Compare commits
2865 Commits
v0.0.1-alp
...
release/v2
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
71d40c8720 | ||
|
|
336f4eb9c2 | ||
|
|
9b3162495c | ||
|
|
61d85ff30e | ||
|
|
2c199c66be | ||
|
|
5875aac92e | ||
|
|
dab51524be | ||
|
|
fb07dfee85 | ||
|
|
7842c7f2d6 | ||
|
|
b385c248b0 | ||
|
|
a0929969ef | ||
|
|
6b3580e16c | ||
|
|
6cd7722539 | ||
|
|
71ea90524b | ||
|
|
9ea0a535ea | ||
|
|
25d2a3cdf1 | ||
|
|
9fa59df798 | ||
|
|
93c0467f91 | ||
|
|
c377fe7651 | ||
|
|
9ed24522bb | ||
|
|
ddcabbf95d | ||
|
|
5c58b45340 | ||
|
|
5690b639cd | ||
|
|
22d0ff8173 | ||
|
|
8e61fe805c | ||
|
|
5356436c94 | ||
|
|
8ca8b92f92 | ||
|
|
7c98f20e11 | ||
|
|
1a8798a5d4 | ||
|
|
926842a216 | ||
|
|
9e11b860ec | ||
|
|
5abf1ee817 | ||
|
|
4e78e80619 | ||
|
|
33be9840f0 | ||
|
|
33fdaee399 | ||
|
|
91660a98d5 | ||
|
|
8d5c4492d8 | ||
|
|
29ad52bb46 | ||
|
|
590b7b7682 | ||
|
|
ea06d9614f | ||
|
|
41ba55634a | ||
|
|
f09616e780 | ||
|
|
a4d7e35cdd | ||
|
|
346e0ea734 | ||
|
|
ce854236cf | ||
|
|
1588663358 | ||
|
|
68fdc0a2b6 | ||
|
|
d335f8f981 | ||
|
|
b4efd15afd | ||
|
|
0e6f9da761 | ||
|
|
02b34f05c8 | ||
|
|
f26800eb85 | ||
|
|
d2cc01169b | ||
|
|
d8924cd8a9 | ||
|
|
25af5d2968 | ||
|
|
3580d4ff85 | ||
|
|
42607aadc3 | ||
|
|
2fe86a4cde | ||
|
|
db0256e0f7 | ||
|
|
224e808c21 | ||
|
|
6ed6b937f8 | ||
|
|
99b940f56f | ||
|
|
66a417a3ee | ||
|
|
761762bdc0 | ||
|
|
bd8ada9e4a | ||
|
|
ba5c7e4fc3 | ||
|
|
903284fe59 | ||
|
|
cf7ee0081c | ||
|
|
e6a1d8156b | ||
|
|
b850f51ef5 | ||
|
|
4e57de4776 | ||
|
|
0a2945e7f1 | ||
|
|
4f9beae49d | ||
|
|
15a49334d8 | ||
|
|
cf5e7c39e0 | ||
|
|
173ee5fcdc | ||
|
|
67968dff7e | ||
|
|
c596c70d42 | ||
|
|
d30c3aef32 | ||
|
|
f7e5101753 | ||
|
|
597b13d1b3 | ||
|
|
2b8385a874 | ||
|
|
ddcc301ab6 | ||
|
|
ab983c678f | ||
|
|
79dfbec910 | ||
|
|
6bf439d4ce | ||
|
|
063c5ee328 | ||
|
|
19137b8e8c | ||
|
|
95aa30ad41 | ||
|
|
55aa96a33a | ||
|
|
5460348450 | ||
|
|
0d1a68ecb4 | ||
|
|
98466220c7 | ||
|
|
6d2dd076dc | ||
|
|
5e07bcb79a | ||
|
|
9c81a74743 | ||
|
|
a3f2b1d829 | ||
|
|
cbdd71e44e | ||
|
|
f01cf5e04c | ||
|
|
bbb3063cb2 | ||
|
|
c0fa6e6939 | ||
|
|
0337362eec | ||
|
|
fb3013cb95 | ||
|
|
833fec3d21 | ||
|
|
007b79c729 | ||
|
|
09f55955e8 | ||
|
|
29c2c72d8f | ||
|
|
ae9b541ce2 | ||
|
|
8d86637d3f | ||
|
|
390ff1bcf7 | ||
|
|
aa65589391 | ||
|
|
9ee23a9086 | ||
|
|
41cdd3dcf7 | ||
|
|
aba5741450 | ||
|
|
cb5eb417c5 | ||
|
|
9f8b8b624b | ||
|
|
8728b07e85 | ||
|
|
e1ffd83b64 | ||
|
|
020a494f3f | ||
|
|
96ed1e1372 | ||
|
|
860682e476 | ||
|
|
2903b4910c | ||
|
|
c07e33eff0 | ||
|
|
a5b1b04915 | ||
|
|
799848c2a0 | ||
|
|
7e6cd34071 | ||
|
|
b8c24f906d | ||
|
|
e678738ded | ||
|
|
9000be6daa | ||
|
|
13ff4afaa4 | ||
|
|
40b9c07641 | ||
|
|
0ce5117715 | ||
|
|
526d154172 | ||
|
|
9e422576b8 | ||
|
|
069bca29d1 | ||
|
|
34ac124b6b | ||
|
|
e475a22435 | ||
|
|
d1ec628d6c | ||
|
|
d13227b277 | ||
|
|
fcb992240e | ||
|
|
cf5eb6a0bc | ||
|
|
2aa38baa35 | ||
|
|
84d046ab2a | ||
|
|
29b08fc306 | ||
|
|
a7153a0ff5 | ||
|
|
bc67308f85 | ||
|
|
6e93a87265 | ||
|
|
6fd1f794f9 | ||
|
|
5942e65b1c | ||
|
|
77d670c224 | ||
|
|
70546e5dfe | ||
|
|
fec7dfefa4 | ||
|
|
9a8944df94 | ||
|
|
ace242fca2 | ||
|
|
96d4034a74 | ||
|
|
2e3624d636 | ||
|
|
cb54bbcd97 | ||
|
|
847e78541a | ||
|
|
ad3eebcf63 | ||
|
|
86df468c3f | ||
|
|
2cf2486a2b | ||
|
|
4d443d614b | ||
|
|
50968ec1a6 | ||
|
|
38ada0b998 | ||
|
|
0b0f9827b9 | ||
|
|
88b5e3f71b | ||
|
|
bc608dc130 | ||
|
|
961c237d33 | ||
|
|
73e2f56ff5 | ||
|
|
a122ceb09b | ||
|
|
b30d7cb3dc | ||
|
|
cd81362781 | ||
|
|
63abf0b840 | ||
|
|
56d265ae11 | ||
|
|
c0c76da4c8 | ||
|
|
3edfff49a2 | ||
|
|
f9be835288 | ||
|
|
86e542e524 | ||
|
|
f28e189cf5 | ||
|
|
2538b6921f | ||
|
|
83525807a2 | ||
|
|
c6a61c1b92 | ||
|
|
0257171cf5 | ||
|
|
f431f9858c | ||
|
|
71e9230789 | ||
|
|
08859f1588 | ||
|
|
d0a255c84a | ||
|
|
ec6f341497 | ||
|
|
811b26275f | ||
|
|
107894eccf | ||
|
|
cb8387cba6 | ||
|
|
6700aac4a4 | ||
|
|
3d1173a2cd | ||
|
|
52c7cca3fc | ||
|
|
9a59a90187 | ||
|
|
08370cb3a6 | ||
|
|
2dce1f23b0 | ||
|
|
a52f5aaa75 | ||
|
|
ef5f7bca64 | ||
|
|
1435c71d9c | ||
|
|
0d2517b96d | ||
|
|
48a1c0f5d4 | ||
|
|
64fb04b77b | ||
|
|
2696a93ee0 | ||
|
|
c350e300f9 | ||
|
|
b74638c25c | ||
|
|
f00fee5328 | ||
|
|
c3aa940c2b | ||
|
|
3fc15c42c4 | ||
|
|
f0c498ff54 | ||
|
|
cecffc0588 | ||
|
|
9293781702 | ||
|
|
97b064be13 | ||
|
|
52acac1a37 | ||
|
|
a296afdd69 | ||
|
|
2e71c718ce | ||
|
|
e44ab85880 | ||
|
|
24452ecd37 | ||
|
|
ccb7d62d95 | ||
|
|
83d2739dc5 | ||
|
|
c0aa1b99b5 | ||
|
|
1260db1bcf | ||
|
|
0625bf8185 | ||
|
|
403ea39825 | ||
|
|
28e1f6e3c7 | ||
|
|
7ee92db427 | ||
|
|
d4cc45f55e | ||
|
|
8240d19fbd | ||
|
|
a158360d7a | ||
|
|
a30f77f8a4 | ||
|
|
8ec9e9ef4d | ||
|
|
dbfb4269cb | ||
|
|
fad7112dd0 | ||
|
|
6afef04a88 | ||
|
|
10f8849e12 | ||
|
|
b55f49b4fe | ||
|
|
883815cd53 | ||
|
|
c9e73edd86 | ||
|
|
2ac2a75c8c | ||
|
|
2e1721ca85 | ||
|
|
91d1e1df48 | ||
|
|
2cfdeeb5a2 | ||
|
|
c9fea671a7 | ||
|
|
dbda8fbdb8 | ||
|
|
e2012a8272 | ||
|
|
c930d58672 | ||
|
|
cdd116dedf | ||
|
|
ad3141dac7 | ||
|
|
ce405b6060 | ||
|
|
53d98c882e | ||
|
|
519cf58d27 | ||
|
|
fdeae99ba5 | ||
|
|
1071f04e93 | ||
|
|
3f6ca549b9 | ||
|
|
a452f15905 | ||
|
|
5fdc8c3e08 | ||
|
|
5a45d2b127 | ||
|
|
0fd8fbe301 | ||
|
|
ec978fc79f | ||
|
|
8c3abb0d8b | ||
|
|
e1fca7f062 | ||
|
|
50829c3217 | ||
|
|
da06854e05 | ||
|
|
865f172e33 | ||
|
|
5607754702 | ||
|
|
17d134766d | ||
|
|
06ed881e37 | ||
|
|
eabd250ed2 | ||
|
|
af153ea0cf | ||
|
|
3f3d68a33a | ||
|
|
c0916edc44 | ||
|
|
34220fd514 | ||
|
|
5b8f673baa | ||
|
|
5b18289808 | ||
|
|
2589c90c25 | ||
|
|
16e0b93bec | ||
|
|
9274e80d71 | ||
|
|
66deeec9f1 | ||
|
|
59ca6548ea | ||
|
|
267d2314e0 | ||
|
|
0b5502963e | ||
|
|
4431aa2dd0 | ||
|
|
26aafa1b6f | ||
|
|
d29f1c062f | ||
|
|
879558fe20 | ||
|
|
940b5c4fb9 | ||
|
|
5ab9c01378 | ||
|
|
db67d2c4df | ||
|
|
47867cd80b | ||
|
|
fe0baa4de9 | ||
|
|
262e6bb543 | ||
|
|
18760acaa8 | ||
|
|
a62404c16f | ||
|
|
44db4e100a | ||
|
|
62d8448b9c | ||
|
|
1cc7682d44 | ||
|
|
6eb3fdf863 | ||
|
|
2e4de673b2 | ||
|
|
a64913f2f0 | ||
|
|
2c7d650d44 | ||
|
|
c05b540518 | ||
|
|
c8bd8d0f26 | ||
|
|
a4cd8095a1 | ||
|
|
79485c99ab | ||
|
|
e29f171844 | ||
|
|
c16cca891f | ||
|
|
68ef3a464e | ||
|
|
a5958b494d | ||
|
|
c88a2f4137 | ||
|
|
349bad9240 | ||
|
|
8c7b534544 | ||
|
|
3028897392 | ||
|
|
b28d80e752 | ||
|
|
76552855bb | ||
|
|
e4d19c84eb | ||
|
|
737d615fbc | ||
|
|
2cac6ce281 | ||
|
|
7490d4d4b8 | ||
|
|
3cb9e7cbee | ||
|
|
7b731f7777 | ||
|
|
7e5cbdaea5 | ||
|
|
6e81e82c8c | ||
|
|
a4e1b80ba7 | ||
|
|
e0131f22dd | ||
|
|
caf55ccb7f | ||
|
|
04afc09d58 | ||
|
|
b67c432bc1 | ||
|
|
a59aaa4dfb | ||
|
|
1302fb17c2 | ||
|
|
2e1e4106fd | ||
|
|
e4df6c9d14 | ||
|
|
bca26ebf0a | ||
|
|
2827171dd8 | ||
|
|
b44a3d36ba | ||
|
|
ea04bc8e47 | ||
|
|
0f7b903ace | ||
|
|
71d59e36cc | ||
|
|
7f99655a2b | ||
|
|
d56844010f | ||
|
|
218a661449 | ||
|
|
873950dc55 | ||
|
|
b445013d25 | ||
|
|
65055c273f | ||
|
|
3c14f8beb0 | ||
|
|
9dd98fb2b2 | ||
|
|
4a871cdf10 | ||
|
|
bb6a7b8f07 | ||
|
|
ae9728685c | ||
|
|
662f0d8cae | ||
|
|
1f5961d2ad | ||
|
|
b263e14fa8 | ||
|
|
1e67d75848 | ||
|
|
f4acc0cfc9 | ||
|
|
e5c9132d1d | ||
|
|
3c330b71aa | ||
|
|
f3f6c373fc | ||
|
|
577d4e71af | ||
|
|
a80325995d | ||
|
|
c093714597 | ||
|
|
fa9d42d7bf | ||
|
|
e93b3d8d75 | ||
|
|
6ea3e5b4da | ||
|
|
ae5294f010 | ||
|
|
8571f9e1f8 | ||
|
|
0cd0bf3b58 | ||
|
|
d62cc90f51 | ||
|
|
3fc5f34344 | ||
|
|
978cc0c5b8 | ||
|
|
4e009a7167 | ||
|
|
176444263c | ||
|
|
87232fd4dd | ||
|
|
0361a08aa0 | ||
|
|
be154d079b | ||
|
|
feccc36415 | ||
|
|
06b8ad2402 | ||
|
|
023a709b6a | ||
|
|
6681cd05a9 | ||
|
|
56807fddf6 | ||
|
|
51504406da | ||
|
|
d28cdd9726 | ||
|
|
c1f120facc | ||
|
|
87f792915a | ||
|
|
9fb5fe3af3 | ||
|
|
0648f56049 | ||
|
|
7da8ffd87f | ||
|
|
79f900b82e | ||
|
|
0394c4d5ef | ||
|
|
693f0c1da1 | ||
|
|
65481c223e | ||
|
|
d2222426f5 | ||
|
|
18924d29a7 | ||
|
|
84a3cdde93 | ||
|
|
e5eb4d4a67 | ||
|
|
60c44c16f5 | ||
|
|
f22222f71d | ||
|
|
287ac6b003 | ||
|
|
5b422bef17 | ||
|
|
1dc3ff6c59 | ||
|
|
ed13067ff2 | ||
|
|
a3151aa10c | ||
|
|
536f4c31ce | ||
|
|
3a8765859d | ||
|
|
369ae5aa71 | ||
|
|
ca2b93ba39 | ||
|
|
8ff8295d0c | ||
|
|
0439154564 | ||
|
|
e7e05f870b | ||
|
|
d54f08e7a9 | ||
|
|
ece3a07567 | ||
|
|
9c37506130 | ||
|
|
58b4ed586a | ||
|
|
c479eb80c6 | ||
|
|
da7af5ab5f | ||
|
|
d1b4851fbe | ||
|
|
a9f53b4f1a | ||
|
|
7327b14a62 | ||
|
|
3d5fc3dc18 | ||
|
|
1d80ff2b09 | ||
|
|
28111d27fb | ||
|
|
ddd377b997 | ||
|
|
e01810037b | ||
|
|
f5563de144 | ||
|
|
8ecaa56461 | ||
|
|
9d38ea6ffc | ||
|
|
f58b82fb4e | ||
|
|
be361a44d5 | ||
|
|
12e065cc43 | ||
|
|
f9e69089ea | ||
|
|
2eced064dd | ||
|
|
7be91884b7 | ||
|
|
b2b610b55e | ||
|
|
21a943e6f9 | ||
|
|
cb1b117d17 | ||
|
|
96f177b101 | ||
|
|
7621418b72 | ||
|
|
7a94a3ac71 | ||
|
|
58b799fa83 | ||
|
|
38635e0ec5 | ||
|
|
d79e49f80b | ||
|
|
5e44b7b1b3 | ||
|
|
131c05d9c7 | ||
|
|
3ac8d54a30 | ||
|
|
c605f9a44f | ||
|
|
eefd47d701 | ||
|
|
0014bc4c43 | ||
|
|
ccf358f0ca | ||
|
|
bd284ab28b | ||
|
|
bed46f6b68 | ||
|
|
fdd3fd1d06 | ||
|
|
e81201b8cb | ||
|
|
2c1085d9ce | ||
|
|
49eb1c5444 | ||
|
|
81dc4adc69 | ||
|
|
8e23989418 | ||
|
|
f532bd2d48 | ||
|
|
da9df03675 | ||
|
|
91965ddfc9 | ||
|
|
0bd78ca80c | ||
|
|
96b96ac78e | ||
|
|
a9a63b8423 | ||
|
|
8abb93e831 | ||
|
|
645f9df4f0 | ||
|
|
6924a16ac7 | ||
|
|
dc2a4c267b | ||
|
|
d5e5a26f5c | ||
|
|
df5ac34c9b | ||
|
|
319dbad795 | ||
|
|
28feb8b1d7 | ||
|
|
f4d898cb92 | ||
|
|
75b5b0fd3c | ||
|
|
6ee3439462 | ||
|
|
4eda5a7ccd | ||
|
|
ad94037516 | ||
|
|
882fb35601 | ||
|
|
48f10a6a20 | ||
|
|
2c35880cbf | ||
|
|
c8af9ced89 | ||
|
|
f89525f8bd | ||
|
|
ad11fbcd00 | ||
|
|
9db661ae63 | ||
|
|
fff5cd50f0 | ||
|
|
b3b50cf503 | ||
|
|
cbebad9586 | ||
|
|
c01023d8f8 | ||
|
|
df610c3cca | ||
|
|
3b7c40bbb3 | ||
|
|
8674f31874 | ||
|
|
b518aad5ac | ||
|
|
12959dec88 | ||
|
|
e381da6a08 | ||
|
|
b004fbfc41 | ||
|
|
8c56ccc5b0 | ||
|
|
c8051eeeed | ||
|
|
5d944b69df | ||
|
|
1fca76c4a8 | ||
|
|
d0e6fcad3f | ||
|
|
d4ba6c4f44 | ||
|
|
35e1b5cbb9 | ||
|
|
f8da3a1b44 | ||
|
|
4ea253220a | ||
|
|
0a5048a56b | ||
|
|
a06652a374 | ||
|
|
86e3991998 | ||
|
|
d9102150cf | ||
|
|
fd08bae1c7 | ||
|
|
4b2af2ede2 | ||
|
|
c6be0b9389 | ||
|
|
6ccdfa074f | ||
|
|
8801029d95 | ||
|
|
5faf6ebadc | ||
|
|
f92d708051 | ||
|
|
76c31c6303 | ||
|
|
cf8ac4dd0e | ||
|
|
879041677c | ||
|
|
cac36365ae | ||
|
|
2c12385344 | ||
|
|
fa217b8775 | ||
|
|
6f7cdde1ba | ||
|
|
da9cc00a56 | ||
|
|
161c90eb8f | ||
|
|
ad5daee004 | ||
|
|
35ea91c111 | ||
|
|
6763490ef6 | ||
|
|
93382f65bb | ||
|
|
190c732c3a | ||
|
|
8bd13edc75 | ||
|
|
98e0774f56 | ||
|
|
c3a44e890d | ||
|
|
a4734d7e30 | ||
|
|
2c267c95e5 | ||
|
|
78f9a6214c | ||
|
|
7ee90a34e5 | ||
|
|
1a6b09afb4 | ||
|
|
c7e158aaa7 | ||
|
|
98c7afd69c | ||
|
|
f3da59e5af | ||
|
|
a17210f387 | ||
|
|
443212d3da | ||
|
|
7a5f60e23f | ||
|
|
7a1d978339 | ||
|
|
6c7ef96354 | ||
|
|
d2e7a37eb4 | ||
|
|
1d8105247a | ||
|
|
6d110cdfb1 | ||
|
|
d015895caa | ||
|
|
64e76a23c6 | ||
|
|
f5006aa239 | ||
|
|
4bd06771ae | ||
|
|
4643f8383e | ||
|
|
b82759b35a | ||
|
|
0343575146 | ||
|
|
e7847b75db | ||
|
|
bb1078d610 | ||
|
|
6f6c097980 | ||
|
|
73692df272 | ||
|
|
138cba6e57 | ||
|
|
2abf932ee4 | ||
|
|
939a75115c | ||
|
|
9f41efb6f7 | ||
|
|
c3d7cad53e | ||
|
|
463f9fbc64 | ||
|
|
4a51b111e6 | ||
|
|
63ebd7fd09 | ||
|
|
c31367909e | ||
|
|
0f0649a674 | ||
|
|
09cbf348a7 | ||
|
|
287bc520b1 | ||
|
|
65a2ceec5c | ||
|
|
516399bf81 | ||
|
|
4ea70765af | ||
|
|
d6372e396b | ||
|
|
7b20ad5dd2 | ||
|
|
3d962136a8 | ||
|
|
f3386505cf | ||
|
|
f4c8da35e8 | ||
|
|
cc3f2c7bde | ||
|
|
80b87729b6 | ||
|
|
2282223592 | ||
|
|
f6c96aea48 | ||
|
|
1fa48bf916 | ||
|
|
d49b77c8d2 | ||
|
|
91132e9c87 | ||
|
|
4680abe951 | ||
|
|
2963708a6c | ||
|
|
1f57cf3d31 | ||
|
|
80611ec70e | ||
|
|
d37bb42995 | ||
|
|
1bf63a94c2 | ||
|
|
cad251444c | ||
|
|
358c6d38b7 | ||
|
|
b8fd46d0df | ||
|
|
6a1ba3c545 | ||
|
|
33a874800b | ||
|
|
f417352370 | ||
|
|
72d90b5692 | ||
|
|
d7dadb4425 | ||
|
|
348408e16e | ||
|
|
04de52044a | ||
|
|
45a00a0170 | ||
|
|
1ac380a7f9 | ||
|
|
2971d34a13 | ||
|
|
90f0d81532 | ||
|
|
d5262404f3 | ||
|
|
03c3cb860a | ||
|
|
a1faa1d965 | ||
|
|
c40d290e46 | ||
|
|
5106a71e6a | ||
|
|
491acf57ad | ||
|
|
0694a9582f | ||
|
|
0c817378cf | ||
|
|
ec2aa13165 | ||
|
|
c921cf0d54 | ||
|
|
11dd0d918c | ||
|
|
467969de0f | ||
|
|
bdc5ae4573 | ||
|
|
1eb4b67013 | ||
|
|
e777947539 | ||
|
|
70b906cae2 | ||
|
|
c57afa1e56 | ||
|
|
73668d19d9 | ||
|
|
82f847e21d | ||
|
|
753b2e6eda | ||
|
|
7b95e90a33 | ||
|
|
7824229d7b | ||
|
|
20557f9f15 | ||
|
|
6430f2b4b0 | ||
|
|
92e136ed54 | ||
|
|
e79b008878 | ||
|
|
43cdea01d6 | ||
|
|
6ddaedb4fc | ||
|
|
b4fef0a6b9 | ||
|
|
735ebd3336 | ||
|
|
a5a9158a24 | ||
|
|
93fdd795da | ||
|
|
18c944d18a | ||
|
|
2c9ef85f6d | ||
|
|
80669d71ef | ||
|
|
b993d17148 | ||
|
|
c454dd481b | ||
|
|
07de9d9ffe | ||
|
|
9f26b09a06 | ||
|
|
ad0f3373b6 | ||
|
|
f880cce4f9 | ||
|
|
8a0fd6ddf9 | ||
|
|
c56f338b12 | ||
|
|
463d241a91 | ||
|
|
db0920ba32 | ||
|
|
16d3180e42 | ||
|
|
81d2ad8245 | ||
|
|
96d1c1b2bd | ||
|
|
545949c67f | ||
|
|
342bb81687 | ||
|
|
60b483569d | ||
|
|
b7a2fb4be0 | ||
|
|
5bdc083ce2 | ||
|
|
787b6953c8 | ||
|
|
40717fa4f4 | ||
|
|
899a1fffca | ||
|
|
02b38ac8e0 | ||
|
|
5dcd599612 | ||
|
|
854ec02823 | ||
|
|
9386b9e0c3 | ||
|
|
f2d749069e | ||
|
|
d4169aa4dd | ||
|
|
c06072d5cf | ||
|
|
7e2d235f53 | ||
|
|
b810aea6cc | ||
|
|
75a879c770 | ||
|
|
d4c5a137a1 | ||
|
|
d4718f6ff4 | ||
|
|
ac9b3d193d | ||
|
|
7c7e76f9f0 | ||
|
|
08401f62b2 | ||
|
|
69e26ca1d9 | ||
|
|
41aac68193 | ||
|
|
fcd38c9395 | ||
|
|
fe4b65972a | ||
|
|
4c576bf599 | ||
|
|
70d30fd52e | ||
|
|
803104578f | ||
|
|
030b6bc77c | ||
|
|
009413affd | ||
|
|
9e76787e9f | ||
|
|
b78bbd5b9d | ||
|
|
3e15e83926 | ||
|
|
1b327e9d4e | ||
|
|
7dd736954b | ||
|
|
6b98590461 | ||
|
|
8049634e4d | ||
|
|
adc7981f22 | ||
|
|
30e5389d02 | ||
|
|
b6a78f42ea | ||
|
|
e4fb8e75f9 | ||
|
|
2f35367a7f | ||
|
|
2d8db4f20d | ||
|
|
12a491f538 | ||
|
|
9503ecafb1 | ||
|
|
e927d39a27 | ||
|
|
ac50aea21f | ||
|
|
c45536723c | ||
|
|
fb1de8c649 | ||
|
|
e1c082e5ac | ||
|
|
1889b64b4e | ||
|
|
0cfdc5d674 | ||
|
|
96afee996a | ||
|
|
da9747a406 | ||
|
|
36d219e05c | ||
|
|
ea2de24ade | ||
|
|
f01911d0e2 | ||
|
|
43eb9327d5 | ||
|
|
ca212ac592 | ||
|
|
fe3e0efcf1 | ||
|
|
ed7a880287 | ||
|
|
e94853f023 | ||
|
|
cbecd8ab56 | ||
|
|
feaab54f70 | ||
|
|
02e12cf871 | ||
|
|
7aeec0a0c4 | ||
|
|
abeea06e72 | ||
|
|
4a55b828b1 | ||
|
|
6b9c0a5e48 | ||
|
|
e060873246 | ||
|
|
143609b9fb | ||
|
|
a22438b7fa | ||
|
|
34321983e7 | ||
|
|
44762933b3 | ||
|
|
2912d1d437 | ||
|
|
4885278691 | ||
|
|
8a7c94180b | ||
|
|
183b9a7ee0 | ||
|
|
0fc582d6fd | ||
|
|
c7a6ed53ca | ||
|
|
547e39d24c | ||
|
|
115b58fe49 | ||
|
|
613e270d00 | ||
|
|
c24e738973 | ||
|
|
e2fb6089c9 | ||
|
|
95eb7aede0 | ||
|
|
3cef177e24 | ||
|
|
c430556498 | ||
|
|
ff9c982df4 | ||
|
|
724c93c23d | ||
|
|
769e20423d | ||
|
|
d12e697769 | ||
|
|
874b05c5da | ||
|
|
1894b90d84 | ||
|
|
cdf5bf3c9e | ||
|
|
5f35bd4e00 | ||
|
|
12504c76d0 | ||
|
|
7346b1a762 | ||
|
|
f7d616d223 | ||
|
|
443e5b5539 | ||
|
|
f6c14c939d | ||
|
|
a602c57e5d | ||
|
|
9ae41899a8 | ||
|
|
cfdd5f0284 | ||
|
|
04b0a0a7ae | ||
|
|
83fcac1868 | ||
|
|
efb0ecb4f9 | ||
|
|
7498d516d4 | ||
|
|
2fe3362c3d | ||
|
|
6473331399 | ||
|
|
6f85363e58 | ||
|
|
02c0d3bd0d | ||
|
|
f1f4cc007a | ||
|
|
7293771766 | ||
|
|
25d065c211 | ||
|
|
bf14f47459 | ||
|
|
8576073b9d | ||
|
|
cbe1331815 | ||
|
|
998b763cf9 | ||
|
|
15e8f106ce | ||
|
|
9aee262054 | ||
|
|
c718336143 | ||
|
|
355ed94852 | ||
|
|
56c5e784fb | ||
|
|
0a30bc1024 | ||
|
|
a55548de07 | ||
|
|
b84e613b5e | ||
|
|
6b9e6cb9a5 | ||
|
|
f24c4034e2 | ||
|
|
797352e4fa | ||
|
|
7d742924f6 | ||
|
|
e19ea796b1 | ||
|
|
bcef28e80b | ||
|
|
4acef9d508 | ||
|
|
8128fc190d | ||
|
|
2ba0c4435e | ||
|
|
b8164717da | ||
|
|
ed88e9dec5 | ||
|
|
5ebb985b10 | ||
|
|
7f5f80286e | ||
|
|
3cd0bc9672 | ||
|
|
95f896e92c | ||
|
|
0b9e3d24ef | ||
|
|
3f0efc9435 | ||
|
|
64205cf523 | ||
|
|
38c62d46c7 | ||
|
|
b1ac3a26f4 | ||
|
|
b795e612f7 | ||
|
|
a1a2286794 | ||
|
|
8c5d83d9fe | ||
|
|
5130a154e4 | ||
|
|
938f2570ef | ||
|
|
97a7b4450f | ||
|
|
46fbc7c71b | ||
|
|
e35da1c890 | ||
|
|
9af6175302 | ||
|
|
e1def4f8ac | ||
|
|
e09078f697 | ||
|
|
7232ff9ea0 | ||
|
|
45876a723c | ||
|
|
1ece35e4c5 | ||
|
|
5dee903374 | ||
|
|
4dd20af7e0 | ||
|
|
b9fbdfc9a4 | ||
|
|
ab00e348a4 | ||
|
|
b5c0ae9d5a | ||
|
|
8e4044eed9 | ||
|
|
7034ef46af | ||
|
|
8dfbe952ae | ||
|
|
f1e9da56dc | ||
|
|
f924c5f76d | ||
|
|
57442e8faa | ||
|
|
95bfd3b3a4 | ||
|
|
2858e83fe1 | ||
|
|
5430152c7f | ||
|
|
3433079121 | ||
|
|
151b84b8fe | ||
|
|
e3e01cb5da | ||
|
|
c4c890d4e9 | ||
|
|
64a473db2e | ||
|
|
cc9bcbaefd | ||
|
|
787d491bd5 | ||
|
|
5c4991299c | ||
|
|
33ac3ef2c6 | ||
|
|
c7504442bd | ||
|
|
1a546a1d82 | ||
|
|
713365a12c | ||
|
|
5d8248d31d | ||
|
|
5346c1cca3 | ||
|
|
baadaa05d2 | ||
|
|
224a1ce941 | ||
|
|
52f1bfed4c | ||
|
|
5c9cbe676d | ||
|
|
e25bb74c05 | ||
|
|
c2f465e246 | ||
|
|
6bbbf16140 | ||
|
|
c5cdb70031 | ||
|
|
2955cd70a8 | ||
|
|
7b4940914c | ||
|
|
30f977a7cb | ||
|
|
e06fa24616 | ||
|
|
20d7d0c78a | ||
|
|
606078c1b3 | ||
|
|
0135eb19d4 | ||
|
|
8b989190c4 | ||
|
|
a85ea59824 | ||
|
|
d012f0f2bc | ||
|
|
7e2b63ea5d | ||
|
|
cb53243fc1 | ||
|
|
5536af9756 | ||
|
|
28087c1d76 | ||
|
|
b80f32ce7d | ||
|
|
8bad59ebde | ||
|
|
b44e4617e0 | ||
|
|
5d99e3d191 | ||
|
|
1807852b6b | ||
|
|
4f4a5c0ba0 | ||
|
|
24188e58ff | ||
|
|
e2be598988 | ||
|
|
9e2a4f329b | ||
|
|
574b86cbca | ||
|
|
4b7042cc46 | ||
|
|
5ae4711f7b | ||
|
|
97a53b1536 | ||
|
|
cc982cf3b1 | ||
|
|
3f652f8b05 | ||
|
|
dcd86dec6e | ||
|
|
0d8194c800 | ||
|
|
150d9d7ae6 | ||
|
|
694f1797d2 | ||
|
|
116be0cfed | ||
|
|
aa2b5ae18d | ||
|
|
e2ccbe2088 | ||
|
|
775891fc88 | ||
|
|
c85954ddef | ||
|
|
dd6db2cbd9 | ||
|
|
5f74c7d294 | ||
|
|
ed87a632b0 | ||
|
|
3edcd16b62 | ||
|
|
b01d3aeecd | ||
|
|
0717c8bdbb | ||
|
|
f1e4561bdd | ||
|
|
efe9a30523 | ||
|
|
e5ede275f8 | ||
|
|
a929d24924 | ||
|
|
368f2d3542 | ||
|
|
139bbbb87c | ||
|
|
51f5d85861 | ||
|
|
7756faec1f | ||
|
|
d9e3e3aa95 | ||
|
|
ff65491bb6 | ||
|
|
8f514d8991 | ||
|
|
2e1000c31a | ||
|
|
c5171a1f2e | ||
|
|
7359e63960 | ||
|
|
307309504b | ||
|
|
1fda202cf9 | ||
|
|
7e634c154f | ||
|
|
3c72e35381 | ||
|
|
7e23430882 | ||
|
|
2c4c3fd749 | ||
|
|
edaf6ca522 | ||
|
|
21f0d5d82c | ||
|
|
059751b3c9 | ||
|
|
05479756d8 | ||
|
|
34e19cb638 | ||
|
|
5312f81c8e | ||
|
|
7f02898539 | ||
|
|
8aabc544f1 | ||
|
|
3b62955e81 | ||
|
|
9c76ba903b | ||
|
|
b4118b73ed | ||
|
|
82a8697f28 | ||
|
|
5b9a1ce5c6 | ||
|
|
32ad462ebe | ||
|
|
1ff8c2806c | ||
|
|
437a7a2852 | ||
|
|
412db70773 | ||
|
|
a1bb6babed | ||
|
|
568c536c3c | ||
|
|
d7129d6b55 | ||
|
|
4a893b13f8 | ||
|
|
8c2983c958 | ||
|
|
a30ffdb176 | ||
|
|
7a306e69ab | ||
|
|
23c4c2f1aa | ||
|
|
aac07f03d8 | ||
|
|
f4418920fb | ||
|
|
7752206152 | ||
|
|
c950f8f817 | ||
|
|
9276345fe7 | ||
|
|
01f910e257 | ||
|
|
de5f00016b | ||
|
|
877729aca3 | ||
|
|
f65d87b191 | ||
|
|
3b1d706b05 | ||
|
|
b0552fa0de | ||
|
|
cbca583f4b | ||
|
|
a0520de7aa | ||
|
|
4602b72778 | ||
|
|
e69a6ed91a | ||
|
|
9d6a037935 | ||
|
|
41df03f600 | ||
|
|
ca92464ef6 | ||
|
|
2e9fd33ce5 | ||
|
|
cf3f729f98 | ||
|
|
8b444283e6 | ||
|
|
4b4e6b1be3 | ||
|
|
d3d271defe | ||
|
|
9bddabf4ff | ||
|
|
959ea6875a | ||
|
|
7b7eb011b0 | ||
|
|
997e6be3a2 | ||
|
|
51af4bbf52 | ||
|
|
e33198e750 | ||
|
|
e3f5a8fee3 | ||
|
|
f8b58f8be9 | ||
|
|
55542a8086 | ||
|
|
70c8c0445c | ||
|
|
29c0bb4ce2 | ||
|
|
b86b195450 | ||
|
|
edf15894f8 | ||
|
|
74878a9aef | ||
|
|
82824b4fc6 | ||
|
|
141d71c39d | ||
|
|
e9d6f271b5 | ||
|
|
8d4dee2aee | ||
|
|
246af92386 | ||
|
|
7c9957a18f | ||
|
|
9e7018383a | ||
|
|
920d6e5404 | ||
|
|
57962347f2 | ||
|
|
6f053c45df | ||
|
|
f154326391 | ||
|
|
776a7fc9c0 | ||
|
|
08412b72bc | ||
|
|
030e166f43 | ||
|
|
d92dfc56b8 | ||
|
|
365d2d102d | ||
|
|
f7853c4ddf | ||
|
|
0a6d5d9267 | ||
|
|
10b761e4e7 | ||
|
|
c6f2b410bc | ||
|
|
306f8f5715 | ||
|
|
f7d9ee90cd | ||
|
|
9376c9a946 | ||
|
|
70fb87bc93 | ||
|
|
63e54f3575 | ||
|
|
1e2a497108 | ||
|
|
5d95a6e750 | ||
|
|
af00610a61 | ||
|
|
809cb79828 | ||
|
|
e44a58cba0 | ||
|
|
10046187a6 | ||
|
|
a402461f9c | ||
|
|
8a6771c9a9 | ||
|
|
7173bd5945 | ||
|
|
8e09ade41c | ||
|
|
6ceb8d8338 | ||
|
|
11296cd94f | ||
|
|
677dca0bc4 | ||
|
|
8e7b957164 | ||
|
|
8f93e2a9d4 | ||
|
|
62755b4b75 | ||
|
|
dcfb745b1f | ||
|
|
f38b83231c | ||
|
|
269f5e2575 | ||
|
|
893596383a | ||
|
|
8c67708829 | ||
|
|
c1528503b6 | ||
|
|
d3c56eb3d3 | ||
|
|
b10eee87ee | ||
|
|
83de469967 | ||
|
|
192978125f | ||
|
|
b4b3551e39 | ||
|
|
7f580e89d0 | ||
|
|
81a087095a | ||
|
|
bcabde3bdb | ||
|
|
c190d80d4a | ||
|
|
11081e8cb2 | ||
|
|
c5890f08ef | ||
|
|
926d8a1c37 | ||
|
|
da6dfd5a1b | ||
|
|
4318152141 | ||
|
|
759145704f | ||
|
|
5cab8f4b11 | ||
|
|
a0ce4b23d2 | ||
|
|
6d88a0c3ac | ||
|
|
db44bcd88e | ||
|
|
585ae5090d | ||
|
|
fe46793c40 | ||
|
|
be146b1cc9 | ||
|
|
e46c7bd519 | ||
|
|
f3d143e5ee | ||
|
|
fc059df8ff | ||
|
|
6c047d1e2a | ||
|
|
f6afe7f0ec | ||
|
|
ca7d2e783f | ||
|
|
0b133ca9f2 | ||
|
|
ede6785e6b | ||
|
|
6d9f39d8ea | ||
|
|
fb637ea955 | ||
|
|
e07558f5b7 | ||
|
|
b75dbf8c70 | ||
|
|
062c1e59a9 | ||
|
|
ba5eea861e | ||
|
|
ff7df54899 | ||
|
|
b75ce95086 | ||
|
|
a86d94745a | ||
|
|
c13de6089a | ||
|
|
3cb748a47e | ||
|
|
3e6e93fab4 | ||
|
|
5832811930 | ||
|
|
6f0ea04ff3 | ||
|
|
26ea167524 | ||
|
|
1393e7a62b | ||
|
|
7e1fd499ca | ||
|
|
309fd86b45 | ||
|
|
e14357f694 | ||
|
|
29f0adc587 | ||
|
|
3ab578747d | ||
|
|
2c3cb1a664 | ||
|
|
99a0c47277 | ||
|
|
c5b2c6709a | ||
|
|
8354ac937c | ||
|
|
aa5ad65286 | ||
|
|
05adb44416 | ||
|
|
adf5a5278f | ||
|
|
bb04ca36b2 | ||
|
|
fc94b1af7a | ||
|
|
d9886035c8 | ||
|
|
0e122863dd | ||
|
|
3089f67946 | ||
|
|
3654e221a9 | ||
|
|
a26dd05c49 | ||
|
|
6c844369be | ||
|
|
a03574f8c3 | ||
|
|
43c6a1531a | ||
|
|
aed7341b34 | ||
|
|
8731f00347 | ||
|
|
75a18b4548 | ||
|
|
716b41e91b | ||
|
|
e72214e266 | ||
|
|
46f9fc194c | ||
|
|
6c5f27be02 | ||
|
|
e96652bdaa | ||
|
|
b7007a35d7 | ||
|
|
e4dc56b59d | ||
|
|
b05059a9c4 | ||
|
|
121783976a | ||
|
|
5a9424d0b1 | ||
|
|
e2a3800664 | ||
|
|
56815a3624 | ||
|
|
ca6e0ff36e | ||
|
|
4c60d1657d | ||
|
|
cdd90cfa75 | ||
|
|
05b053e2e9 | ||
|
|
46c75c1af2 | ||
|
|
80cf5fa729 | ||
|
|
789aa322f1 | ||
|
|
f03c24565f | ||
|
|
b6a95be5d0 | ||
|
|
0f9e8ed3f7 | ||
|
|
50af0ba93c | ||
|
|
923a5882de | ||
|
|
83dc3e6093 | ||
|
|
43edb62f87 | ||
|
|
21e5acc0e0 | ||
|
|
be1ce74dc5 | ||
|
|
31771f3575 | ||
|
|
ffcd7d8059 | ||
|
|
4bc4aa1397 | ||
|
|
04faba95cd | ||
|
|
f712dadab5 | ||
|
|
58b3150ce3 | ||
|
|
e7225db397 | ||
|
|
8ec5492d87 | ||
|
|
c2c64a70c4 | ||
|
|
4621576f40 | ||
|
|
3b609e9b03 | ||
|
|
4f2ebd78be | ||
|
|
88dacebc94 | ||
|
|
92e7d1ad1e | ||
|
|
d5d8c340c8 | ||
|
|
b8a85b809a | ||
|
|
61be0775af | ||
|
|
404ffa5a91 | ||
|
|
f2de7e04b8 | ||
|
|
8b3e3b1dd7 | ||
|
|
81e91ac3f5 | ||
|
|
b9bde94d08 | ||
|
|
37746023c1 | ||
|
|
d3e529b8a4 | ||
|
|
eb69083ef5 | ||
|
|
96aac387c9 | ||
|
|
870f18c621 | ||
|
|
57b33e29f7 | ||
|
|
94b7917679 | ||
|
|
98fa0c4271 | ||
|
|
8282907bce | ||
|
|
323f4f5e5f | ||
|
|
744b3ebd0a | ||
|
|
3fdba35993 | ||
|
|
ebdf9ed379 | ||
|
|
a572274c5c | ||
|
|
6a6bba8669 | ||
|
|
1d1d4bbf4b | ||
|
|
d9bb4c631e | ||
|
|
722962c138 | ||
|
|
c98ff6ae87 | ||
|
|
cbef6a4cad | ||
|
|
f887a2c029 | ||
|
|
078cfe92c2 | ||
|
|
80ef184b60 | ||
|
|
f2475988bd | ||
|
|
45526108e0 | ||
|
|
414c0bbbdc | ||
|
|
6873a710d9 | ||
|
|
8a44006384 | ||
|
|
1b6061066a | ||
|
|
3a8a5982c6 | ||
|
|
ccff578492 | ||
|
|
e2402e3d84 | ||
|
|
f13b1629cf | ||
|
|
72a97bb70a | ||
|
|
67b393ce09 | ||
|
|
48e89b95bb | ||
|
|
2159ed62d0 | ||
|
|
8bb65719cd | ||
|
|
4352915945 | ||
|
|
ebd145f7f7 | ||
|
|
cd52a0eef3 | ||
|
|
69e4a86fe2 | ||
|
|
52d89a2ee1 | ||
|
|
5c60e792d9 | ||
|
|
77c9611784 | ||
|
|
66780bbf54 | ||
|
|
a8932e677e | ||
|
|
e12988a8f9 | ||
|
|
6ee4abe79e | ||
|
|
948e050d60 | ||
|
|
87feb45751 | ||
|
|
77aa81a064 | ||
|
|
a4a1db0915 | ||
|
|
57b9610af7 | ||
|
|
c3384c6499 | ||
|
|
5389859260 | ||
|
|
84c585cf61 | ||
|
|
ca496d393d | ||
|
|
3d4ca831dc | ||
|
|
7ace8de753 | ||
|
|
928d3e2185 | ||
|
|
cbf2b90320 | ||
|
|
69dce73e51 | ||
|
|
75d4f87dec | ||
|
|
4f7d89e825 | ||
|
|
da87e16321 | ||
|
|
f7aa3e7e1b | ||
|
|
deacfd6c03 | ||
|
|
3e8d1ae1d5 | ||
|
|
08f5ca39b0 | ||
|
|
31da363495 | ||
|
|
2ecd99d317 | ||
|
|
59c3d84182 | ||
|
|
641d5378f8 | ||
|
|
08512e5c43 | ||
|
|
8f7f7b23e8 | ||
|
|
2eb6ba5a48 | ||
|
|
03df386f9e | ||
|
|
5e741da69c | ||
|
|
3bea028cc9 | ||
|
|
10475b24c4 | ||
|
|
a5238e867c | ||
|
|
0e747790f9 | ||
|
|
2b4d6150d4 | ||
|
|
e22ad96164 | ||
|
|
f54907e66e | ||
|
|
fb713e9632 | ||
|
|
0b659e3f09 | ||
|
|
4c99117c7c | ||
|
|
83c3e8c2fc | ||
|
|
92277225df | ||
|
|
622ed88a11 | ||
|
|
d9414f25d5 | ||
|
|
5249d17a95 | ||
|
|
25283d357e | ||
|
|
e926321094 | ||
|
|
9c1542c3f3 | ||
|
|
25d06a53bc | ||
|
|
4d904e8216 | ||
|
|
0beab87f5b | ||
|
|
b9ceceada4 | ||
|
|
ac7ccf7b94 | ||
|
|
5aa9ae511f | ||
|
|
dd81ed896b | ||
|
|
e6bbed162d | ||
|
|
3ee8747fdc | ||
|
|
0651064999 | ||
|
|
4661e4519d | ||
|
|
19caeb178f | ||
|
|
d8235ea21b | ||
|
|
5067df179e | ||
|
|
50a1e32da3 | ||
|
|
fb85cafcc5 | ||
|
|
d06a2936cc | ||
|
|
7c77a9723a | ||
|
|
8a3e5790f5 | ||
|
|
dd093a775a | ||
|
|
a096bd2d71 | ||
|
|
2eddcde609 | ||
|
|
1849e1768a | ||
|
|
bbe62d029c | ||
|
|
68a89d3cd4 | ||
|
|
b16f1fc260 | ||
|
|
64f39e160b | ||
|
|
3a76c26822 | ||
|
|
9d9fff5796 | ||
|
|
0a92c61b09 | ||
|
|
546be76f55 | ||
|
|
d770f3f53f | ||
|
|
254cc131ae | ||
|
|
70509ffcb4 | ||
|
|
4cc2326c7f | ||
|
|
0133caaec4 | ||
|
|
7ae4f28920 | ||
|
|
b1eb0270e9 | ||
|
|
03b6de1169 | ||
|
|
9d3f75d111 | ||
|
|
5c41924b2f | ||
|
|
7cf7cf2f1e | ||
|
|
2679731bde | ||
|
|
ad73370cd7 | ||
|
|
18acae57bd | ||
|
|
b427356eca | ||
|
|
2e6ca16a4a | ||
|
|
e98f1142a6 | ||
|
|
06fa8f75c9 | ||
|
|
8cbd4e8172 | ||
|
|
83c7994266 | ||
|
|
43843581b6 | ||
|
|
7e03d64e8a | ||
|
|
c6f4d71187 | ||
|
|
69c3b90fea | ||
|
|
75309b4c93 | ||
|
|
433f13a7ed | ||
|
|
8896a1e73e | ||
|
|
54758b1692 | ||
|
|
375e00c79c | ||
|
|
e2454d91f1 | ||
|
|
6894f6f3bf | ||
|
|
d45501a129 | ||
|
|
def92e14ee | ||
|
|
11708d4189 | ||
|
|
2bc64bf419 | ||
|
|
3a3bdc62c8 | ||
|
|
72294b2a56 | ||
|
|
94940a20ef | ||
|
|
219ff2ef7d | ||
|
|
bc2de741b8 | ||
|
|
5eabd4e898 | ||
|
|
e8d6d5fe5c | ||
|
|
55bd93ff79 | ||
|
|
b34b2d779b | ||
|
|
103ed2be65 | ||
|
|
cc32c1be07 | ||
|
|
a3ba9817a3 | ||
|
|
6d5f1b17ad | ||
|
|
0d5d5fce46 | ||
|
|
375edffd15 | ||
|
|
d1982e64b2 | ||
|
|
cec8b5336c | ||
|
|
8f78263455 | ||
|
|
cb96bca6aa | ||
|
|
c18d0b9217 | ||
|
|
d1970185b9 | ||
|
|
794d3ee2f5 | ||
|
|
daeef98dfb | ||
|
|
4146df1f02 | ||
|
|
78f4dfa48d | ||
|
|
8b68d7d7e2 | ||
|
|
ba1bba17ad | ||
|
|
70f2b5028f | ||
|
|
4f4f0d70a4 | ||
|
|
9607b07e65 | ||
|
|
3570fab0f9 | ||
|
|
dd0f17d7a5 | ||
|
|
2290880389 | ||
|
|
351d287d88 | ||
|
|
eba6706f15 | ||
|
|
7f425efa6b | ||
|
|
d40685ab62 | ||
|
|
f795e3eeb8 | ||
|
|
d3944c0204 | ||
|
|
4086ab15fa | ||
|
|
446a367094 | ||
|
|
bd250c9871 | ||
|
|
91b3788362 | ||
|
|
658dbb9ea8 | ||
|
|
1257b9cbc8 | ||
|
|
0ae39d5a0a | ||
|
|
d8911e0c77 | ||
|
|
1be006a45f | ||
|
|
b95e75ddb4 | ||
|
|
15a5f75fe7 | ||
|
|
b01e27f50f | ||
|
|
b1a9583262 | ||
|
|
dd5e6377f8 | ||
|
|
fcb73554c9 | ||
|
|
5c4b3d1080 | ||
|
|
c98cd10621 | ||
|
|
e4af8ddcc8 | ||
|
|
b5ce02b8cf | ||
|
|
cd42b3fb44 | ||
|
|
6dedb767c3 | ||
|
|
4de3268f3b | ||
|
|
a72ff06d79 | ||
|
|
cf239deb3d | ||
|
|
8735229745 | ||
|
|
3f081ba2d9 | ||
|
|
3f613341cb | ||
|
|
4305b8a77d | ||
|
|
fab91d44c3 | ||
|
|
34484734d8 | ||
|
|
10c58bb007 | ||
|
|
1c1fd62a91 | ||
|
|
637ac1e3fe | ||
|
|
f52387e849 | ||
|
|
9efc4986f9 | ||
|
|
fdc366ec1c | ||
|
|
d455db444c | ||
|
|
17418c9858 | ||
|
|
5da7eb7d0d | ||
|
|
9da977ee7a | ||
|
|
8e4b2ead9b | ||
|
|
fd364828a1 | ||
|
|
afa58d8c08 | ||
|
|
179062876e | ||
|
|
a796f3609f | ||
|
|
b7c6db74d2 | ||
|
|
4f7b040405 | ||
|
|
34ca29830e | ||
|
|
78f1b634fa | ||
|
|
044bc64ad9 | ||
|
|
091f439498 | ||
|
|
a17b0a1ce0 | ||
|
|
354cd5e177 | ||
|
|
4e8f1221f7 | ||
|
|
6b179aa7d9 | ||
|
|
f748114dfa | ||
|
|
5de83f015a | ||
|
|
a6620e478a | ||
|
|
c7fcffdd8e | ||
|
|
160f59a984 | ||
|
|
d38d487c2a | ||
|
|
db28907543 | ||
|
|
c4261399b5 | ||
|
|
b4edb46269 | ||
|
|
a20ed0e630 | ||
|
|
cea869e285 | ||
|
|
e12db14d1e | ||
|
|
296bf3cc6c | ||
|
|
1789aa180d | ||
|
|
bd255800db | ||
|
|
1355962b3c | ||
|
|
bb0114e379 | ||
|
|
f9622a5b9e | ||
|
|
3a74fcd75c | ||
|
|
7265276cc2 | ||
|
|
b98027b528 | ||
|
|
b6ae7d2cdd | ||
|
|
aa887c61c3 | ||
|
|
700cef0989 | ||
|
|
3ed3e553e7 | ||
|
|
d68158ddc9 | ||
|
|
9f83a69242 | ||
|
|
bf69dbd43d | ||
|
|
465ea5ccfd | ||
|
|
92ef39e2ad | ||
|
|
0404790df9 | ||
|
|
f880e93df4 | ||
|
|
4697b1101d | ||
|
|
50ff2accd2 | ||
|
|
c7d876eb8f | ||
|
|
eda392dfcd | ||
|
|
3b91e14f6d | ||
|
|
17e3c57d7e | ||
|
|
1c744a0f97 | ||
|
|
99bdb20aeb | ||
|
|
fbe7050cb8 | ||
|
|
12ea028aa9 | ||
|
|
ea62cb5fc9 | ||
|
|
d27c2164b2 | ||
|
|
ef8f5cb87d | ||
|
|
378a2c2a0e | ||
|
|
2597ad0f73 | ||
|
|
0df34bed59 | ||
|
|
be65cf8052 | ||
|
|
8922753591 | ||
|
|
87e11ed653 | ||
|
|
ab34771b3d | ||
|
|
e733c4f55a | ||
|
|
37b60666c4 | ||
|
|
734d736bdf | ||
|
|
8ca65059f7 | ||
|
|
086f174463 | ||
|
|
48fd70fc09 | ||
|
|
606266e976 | ||
|
|
f7006a8172 | ||
|
|
653dcc8d78 | ||
|
|
8df140c713 | ||
|
|
089af9cc90 | ||
|
|
695fb55b13 | ||
|
|
ec21eedd56 | ||
|
|
5ba3774fd5 | ||
|
|
12a2100fcf | ||
|
|
68074d3543 | ||
|
|
18849e36c7 | ||
|
|
671fe274da | ||
|
|
af1d9102b9 | ||
|
|
9dc10ef7d1 | ||
|
|
86a3cf20e7 | ||
|
|
27a42ecd8e | ||
|
|
ae7a59fbb4 | ||
|
|
598dfc32e8 | ||
|
|
a40d124e23 | ||
|
|
9df3fcab18 | ||
|
|
b6ce969d1b | ||
|
|
6a37649ee6 | ||
|
|
8926095660 | ||
|
|
bd34870334 | ||
|
|
a56ce1f867 | ||
|
|
dab5bbd393 | ||
|
|
15ebfd7eb6 | ||
|
|
5ab8dd2557 | ||
|
|
9164914d16 | ||
|
|
c9e0bc0807 | ||
|
|
61439adf9b | ||
|
|
e4d7450643 | ||
|
|
0fbcfded57 | ||
|
|
fb3a434f95 | ||
|
|
4f66da84d6 | ||
|
|
b67e8aafab | ||
|
|
0b4f1d30a6 | ||
|
|
c494e6bf7e | ||
|
|
b8c57c7901 | ||
|
|
6aed4631e7 | ||
|
|
5df9118365 | ||
|
|
4a4af94d6c | ||
|
|
baa54fb84a | ||
|
|
cb6470f817 | ||
|
|
1a904e138f | ||
|
|
3b482529ff | ||
|
|
67997437db | ||
|
|
a5541eddca | ||
|
|
203157e525 | ||
|
|
655c2261ba | ||
|
|
45e446eb00 | ||
|
|
68abe37648 | ||
|
|
df6a0a3762 | ||
|
|
c35bae577f | ||
|
|
3567941eda | ||
|
|
3c95fe6380 | ||
|
|
d07f0d003c | ||
|
|
86774309db | ||
|
|
427f23e32d | ||
|
|
70cddde16c | ||
|
|
e86789b643 | ||
|
|
f52fec66bd | ||
|
|
f4926d1e45 | ||
|
|
2774c1a5cd | ||
|
|
8274bc0ea3 | ||
|
|
e9531e4d57 | ||
|
|
3a8aad7e5c | ||
|
|
ef079c5b58 | ||
|
|
50332aa2ee | ||
|
|
b47f3a57dc | ||
|
|
9a928744cc | ||
|
|
328d403507 | ||
|
|
76ffd76bd3 | ||
|
|
951589e652 | ||
|
|
7bb0704401 | ||
|
|
3aa45e72e7 | ||
|
|
67691e92e3 | ||
|
|
43388ec67b | ||
|
|
2fe3934491 | ||
|
|
f60ba95b4c | ||
|
|
4ecf541748 | ||
|
|
7994829765 | ||
|
|
ce14951436 | ||
|
|
a5ce8221a3 | ||
|
|
e6344ef18e | ||
|
|
99e60634ad | ||
|
|
6c656b7366 | ||
|
|
fc3a09b5ad | ||
|
|
b1484f2f24 | ||
|
|
7dcf884e38 | ||
|
|
b6d349da8c | ||
|
|
40ce3d50c2 | ||
|
|
68046067c5 | ||
|
|
e3b12a8a24 | ||
|
|
f123b9d3cb | ||
|
|
f4ce89ae26 | ||
|
|
ea451e7e49 | ||
|
|
d434575047 | ||
|
|
e627634184 | ||
|
|
e0dd12505f | ||
|
|
5a67f94380 | ||
|
|
5f9dd7a5a5 | ||
|
|
bce0da2806 | ||
|
|
a58c40f2d7 | ||
|
|
65d5cadf29 | ||
|
|
1ea5d4d2e3 | ||
|
|
719ef3c44c | ||
|
|
f4adfc3029 | ||
|
|
d8d08091cc | ||
|
|
de4b3ef3dc | ||
|
|
7bd6aedb73 | ||
|
|
fffe40fbd4 | ||
|
|
74feda73af | ||
|
|
8b5583930e | ||
|
|
466fdae70e | ||
|
|
054a62fb30 | ||
|
|
c694b570e0 | ||
|
|
4204ec1d43 | ||
|
|
6d4e37ccb2 | ||
|
|
eef06c993e | ||
|
|
58362fbbb9 | ||
|
|
b872e595ae | ||
|
|
18c3f79319 | ||
|
|
8f0cd35d7a | ||
|
|
c8bcf19f32 | ||
|
|
5bee3047ac | ||
|
|
0d2f6bf02d | ||
|
|
7481c6beb0 | ||
|
|
4ece12348b | ||
|
|
e65a5beaae | ||
|
|
ef576128e3 | ||
|
|
7f0bc2ada2 | ||
|
|
96c373d045 | ||
|
|
22648cae3b | ||
|
|
f57ce14754 | ||
|
|
1d3a381389 | ||
|
|
9055e753a9 | ||
|
|
6390812cbb | ||
|
|
fa46f05423 | ||
|
|
6b0ffe0b13 | ||
|
|
e724d90202 | ||
|
|
6129943685 | ||
|
|
d4e37cbda5 | ||
|
|
cccfb3a560 | ||
|
|
d0403038ed | ||
|
|
a5a7d7970f | ||
|
|
62b9377f15 | ||
|
|
ec2c71f9ef | ||
|
|
b54fd2c6b3 | ||
|
|
e5066c3712 | ||
|
|
fd1c038303 | ||
|
|
64e7a857b8 | ||
|
|
7da24932ab | ||
|
|
1a2ea8407b | ||
|
|
32f94bab97 | ||
|
|
dea4a67639 | ||
|
|
236ffd1767 | ||
|
|
1b2ffad2f1 | ||
|
|
4750d0d81c | ||
|
|
63a210a0b2 | ||
|
|
465eaa24d3 | ||
|
|
c23e8c7ee1 | ||
|
|
974f01cb46 | ||
|
|
16fa9b2753 | ||
|
|
9deab1c415 | ||
|
|
7c01eeb115 | ||
|
|
998f0c7d53 | ||
|
|
bd41406aaa | ||
|
|
f17801753d | ||
|
|
92891fd340 | ||
|
|
aa122455f7 | ||
|
|
880e70c19c | ||
|
|
968f249562 | ||
|
|
bb9f476be2 | ||
|
|
276f43fdeb | ||
|
|
150d1c2a5a | ||
|
|
1bf3814701 | ||
|
|
166181c745 | ||
|
|
bfff977d41 | ||
|
|
787d755261 | ||
|
|
acf7173959 | ||
|
|
e6132e36ba | ||
|
|
585b97c462 | ||
|
|
3dfd0bc2e1 | ||
|
|
10ff99542f | ||
|
|
2449030ab8 | ||
|
|
3e85901f40 | ||
|
|
73b1576f81 | ||
|
|
cdb5b7c9a2 | ||
|
|
d9331b0c91 | ||
|
|
b6a8163dd9 | ||
|
|
185252ba48 | ||
|
|
043d37921b | ||
|
|
02fb8d9958 | ||
|
|
cfa6c0a178 | ||
|
|
e8b52bf2fc | ||
|
|
85fbb780bf | ||
|
|
bd9f9bf518 | ||
|
|
077860fff1 | ||
|
|
d29a4ee4d2 | ||
|
|
6d2e34e9b2 | ||
|
|
0b6969537b | ||
|
|
dc6b0d0f0d | ||
|
|
b4dbb178fe | ||
|
|
4cf5290989 | ||
|
|
6ffd2222c2 | ||
|
|
e7725911a7 | ||
|
|
0c1664cd01 | ||
|
|
0239307d8e | ||
|
|
9f10b6be1b | ||
|
|
01f613b39e | ||
|
|
b775d11a70 | ||
|
|
022576697f | ||
|
|
065d0b2c06 | ||
|
|
ed4718205a | ||
|
|
a29d0c536d | ||
|
|
eaeb8ca5c1 | ||
|
|
2092c14aca | ||
|
|
69f38b8c77 | ||
|
|
d2cdd02a57 | ||
|
|
095c8323a1 | ||
|
|
accb4c915e | ||
|
|
242809f61d | ||
|
|
c4907cf6c6 | ||
|
|
a4b9191fa3 | ||
|
|
5fd3d0bd41 | ||
|
|
ba6da23323 | ||
|
|
0328bb14ce | ||
|
|
2b7a0f3fd4 | ||
|
|
527886bea0 | ||
|
|
98078a0c65 | ||
|
|
ca660b7ba5 | ||
|
|
ed93e93b81 | ||
|
|
80419f00db | ||
|
|
01946facb3 | ||
|
|
08c1bd7653 | ||
|
|
ebf9188c6a | ||
|
|
382c6d5885 | ||
|
|
384c60a988 | ||
|
|
0078147587 | ||
|
|
d79bedf2bc | ||
|
|
14b31b321c | ||
|
|
309b9b52f8 | ||
|
|
5d063e7390 | ||
|
|
e7ba9b5624 | ||
|
|
81f6fa598f | ||
|
|
d9eabcdbf7 | ||
|
|
bb3562427b | ||
|
|
8a5bba80bf | ||
|
|
ff2833c4d1 | ||
|
|
45ba845f23 | ||
|
|
771a14fcf6 | ||
|
|
c8ff861d00 | ||
|
|
0f05ce3605 | ||
|
|
38a3f3ba11 | ||
|
|
659a19cd80 | ||
|
|
baaa466c0f | ||
|
|
168c65bb6e | ||
|
|
6003d11156 | ||
|
|
1f16b6d639 | ||
|
|
54bb4b2efd | ||
|
|
f54770c21a | ||
|
|
1244a62deb | ||
|
|
2fe55bcdde | ||
|
|
9943690855 | ||
|
|
89c46a6379 | ||
|
|
a0d4530cc0 | ||
|
|
6db84269af | ||
|
|
2cd3c32ca7 | ||
|
|
9740fecc35 | ||
|
|
433492791b | ||
|
|
7d3c63ad74 | ||
|
|
a6538b117e | ||
|
|
d54e7559a5 | ||
|
|
bb9eca7232 | ||
|
|
b5027d8f3f | ||
|
|
00a134e23f | ||
|
|
aab3452773 | ||
|
|
5903dfc627 | ||
|
|
a5272b2b39 | ||
|
|
771fc20bb2 | ||
|
|
b5f48bee78 | ||
|
|
ff78af5808 | ||
|
|
7eab649abc | ||
|
|
1b5db157b1 | ||
|
|
0fa9aebf7a | ||
|
|
9fb9965ffe | ||
|
|
02c9f29499 | ||
|
|
c6243ad002 | ||
|
|
f4650c7a84 | ||
|
|
6df691598e | ||
|
|
26964b7f88 | ||
|
|
71712ae1c3 | ||
|
|
0b6c979e47 | ||
|
|
cc2cbc2519 | ||
|
|
8043ae961a | ||
|
|
b1d1d30cdb | ||
|
|
28d606cb0e | ||
|
|
e9c5b6e917 | ||
|
|
68f96235fc | ||
|
|
12f22ddeba | ||
|
|
9db5c644a6 | ||
|
|
ef6a1fb09b | ||
|
|
99002f92f4 | ||
|
|
298d6a1a15 | ||
|
|
5a21f50230 | ||
|
|
5263dabd22 | ||
|
|
9b649f6c72 | ||
|
|
b903cd5b68 | ||
|
|
890b5c5202 | ||
|
|
a14e88d04d | ||
|
|
58e09b4c68 | ||
|
|
631201d541 | ||
|
|
0fbeb6d2cd | ||
|
|
11f8e2ffde | ||
|
|
055eb4a61a | ||
|
|
30c1c5c3d3 | ||
|
|
e034ec3207 | ||
|
|
8edc4bd24b | ||
|
|
6e1672f73c | ||
|
|
5e1f6f7317 | ||
|
|
386780ba12 | ||
|
|
e785971ba8 | ||
|
|
daaae07649 | ||
|
|
6cd567dc66 | ||
|
|
a541a7ee85 | ||
|
|
43572bba04 | ||
|
|
2a3a4456c1 | ||
|
|
15f8e6369b | ||
|
|
cfad9a19eb | ||
|
|
e4c3136433 | ||
|
|
73b8a26850 | ||
|
|
aa533b28fb | ||
|
|
9d70e09a57 | ||
|
|
17e18985e6 | ||
|
|
7c39aaf463 | ||
|
|
bae5c125e8 | ||
|
|
1c84fa0d97 | ||
|
|
6f583f9f0e | ||
|
|
217574b75c | ||
|
|
1378530aeb | ||
|
|
0b10ed4d88 | ||
|
|
a2887f5776 | ||
|
|
0f1d27f1e6 | ||
|
|
850ab0942b | ||
|
|
f5ae8f44b4 | ||
|
|
7f98cfd506 | ||
|
|
bc45a79b92 | ||
|
|
5003cf674d | ||
|
|
bc9cbc387c | ||
|
|
60a1e78869 | ||
|
|
37f5587085 | ||
|
|
fa6e3d3706 | ||
|
|
bb8bc875b4 | ||
|
|
b3dca737be | ||
|
|
9094f85487 | ||
|
|
1256bbfbaf | ||
|
|
24fe74f2f6 | ||
|
|
908f501e03 | ||
|
|
35507c7854 | ||
|
|
eb7102ecac | ||
|
|
ade6bfcbca | ||
|
|
fa98403aa8 | ||
|
|
3f0cb1637c | ||
|
|
42011d028e | ||
|
|
307bb0dea1 | ||
|
|
ec2a8347d4 | ||
|
|
e99b1c3ed8 | ||
|
|
99825f2663 | ||
|
|
afffdfbc5c | ||
|
|
cd874acfd5 | ||
|
|
34edbf469e | ||
|
|
d9ed30e436 | ||
|
|
30008de400 | ||
|
|
a5fa731545 | ||
|
|
493ee3c956 | ||
|
|
3dd574ee51 | ||
|
|
5416c19b2e | ||
|
|
2f31d80c7a | ||
|
|
27d1833854 | ||
|
|
84ed716908 | ||
|
|
6c9c9c7578 | ||
|
|
cc7b7b0689 | ||
|
|
5df8e05d1a | ||
|
|
b3b224b0ca | ||
|
|
75ab28ee5d | ||
|
|
aa9ea2b4ab | ||
|
|
1e6be99c36 | ||
|
|
49fb396bf8 | ||
|
|
e055c9ddc1 | ||
|
|
c708e390a7 | ||
|
|
d5ad26c934 | ||
|
|
144b7cd922 | ||
|
|
9e86fbb311 | ||
|
|
b528428d02 | ||
|
|
b3d7730e79 | ||
|
|
f2ba567ca4 | ||
|
|
8342f77087 | ||
|
|
7cade1b98f | ||
|
|
ee4c1fb36c | ||
|
|
dbc4e537fe | ||
|
|
e28990b96c | ||
|
|
408cf92c04 | ||
|
|
425af2e0dc | ||
|
|
22df860eca | ||
|
|
f395044d65 | ||
|
|
afe0ddcd84 | ||
|
|
2c0323684c | ||
|
|
6d5ffdea57 | ||
|
|
648af6e645 | ||
|
|
e1895a4e21 | ||
|
|
d5f45800ae | ||
|
|
51f9d249ff | ||
|
|
6f525356cb | ||
|
|
5008f9064e | ||
|
|
cff96ed7ca | ||
|
|
4e8a600f34 | ||
|
|
4fd5684277 | ||
|
|
06bf469ba7 | ||
|
|
b8a215230c | ||
|
|
2460cfcf1c | ||
|
|
364242c857 | ||
|
|
29e2900f59 | ||
|
|
61e1fb770e | ||
|
|
2d3fcbdea3 | ||
|
|
47e15cee3d | ||
|
|
adeb3e3f42 | ||
|
|
fb1278285b | ||
|
|
e371610849 | ||
|
|
424de63bd1 | ||
|
|
832c925d39 | ||
|
|
378f118d51 | ||
|
|
d651777122 | ||
|
|
65d8ebabb8 | ||
|
|
9195ed9a1b | ||
|
|
5df8f7313c | ||
|
|
25ed6ca0a4 | ||
|
|
9f972995bd | ||
|
|
29c46a9892 | ||
|
|
ef579fe596 | ||
|
|
5b268f62a3 | ||
|
|
1f1c8286a5 | ||
|
|
5401e1ace4 | ||
|
|
69294ef56d | ||
|
|
a685ed8029 | ||
|
|
68d0be3818 | ||
|
|
84e2cb4c1f | ||
|
|
263c664acd | ||
|
|
b12c4c22fb | ||
|
|
9f39fadb9e | ||
|
|
4c29a1ca27 | ||
|
|
f4db124d50 | ||
|
|
8f8c7cccc6 | ||
|
|
e2097c28bd | ||
|
|
871eb444fc | ||
|
|
bc5fbb9fa5 | ||
|
|
3e9749c6b1 | ||
|
|
eaf08fbe90 | ||
|
|
df411cdb88 | ||
|
|
a83c26a864 | ||
|
|
6aa853491c | ||
|
|
3af1d7a5b8 | ||
|
|
c7c57f6717 | ||
|
|
cbb97768d1 | ||
|
|
2bb40d335b | ||
|
|
1b581d6f51 | ||
|
|
c219eb2883 | ||
|
|
65a2c87b5a | ||
|
|
13aa523c37 | ||
|
|
584f0eea58 | ||
|
|
b5ebdb16b2 | ||
|
|
a18f84c27b | ||
|
|
eb86505375 | ||
|
|
984f1c8669 | ||
|
|
c7378edabc | ||
|
|
ac6c6e3a30 | ||
|
|
1bca31f32c | ||
|
|
28d099a6b2 | ||
|
|
6a2b53fbf5 | ||
|
|
7568f301b8 | ||
|
|
6add511447 | ||
|
|
a7586e69fd | ||
|
|
77db369213 | ||
|
|
2eb6a0513e | ||
|
|
38468c72db | ||
|
|
5f759200c6 | ||
|
|
81f68157fa | ||
|
|
0f3e8abf06 | ||
|
|
fcadd5312d | ||
|
|
6e32820910 | ||
|
|
8499269bab | ||
|
|
72122120cb | ||
|
|
2bbcb95f4f | ||
|
|
19982fa4a6 | ||
|
|
41cf38c6a7 | ||
|
|
16e74647eb | ||
|
|
53cdcbc4ee | ||
|
|
eb2535e066 | ||
|
|
f5c29a7a72 | ||
|
|
e243df93f1 | ||
|
|
388642d9dd | ||
|
|
9e1db06936 | ||
|
|
a260403334 | ||
|
|
6396b25886 | ||
|
|
ca480164b7 | ||
|
|
714f9df3cf | ||
|
|
6a7f1e7d48 | ||
|
|
bcdce02b78 | ||
|
|
2f0835b655 | ||
|
|
36bafa23df | ||
|
|
db611549f2 | ||
|
|
5d4cdcc207 | ||
|
|
a3b9c094b6 | ||
|
|
f82174adae | ||
|
|
c7080d2834 | ||
|
|
381127d413 | ||
|
|
f6fa468acb | ||
|
|
9228130f92 | ||
|
|
207c50ceac | ||
|
|
c3255a6e1e | ||
|
|
5e1c93a167 | ||
|
|
43c33a0cc3 | ||
|
|
f5117329e4 | ||
|
|
f7c62d12a5 | ||
|
|
fe5f181706 | ||
|
|
cc09b29a2e | ||
|
|
406601eead | ||
|
|
341d860c51 | ||
|
|
8214bb8e33 | ||
|
|
884e3c678c | ||
|
|
3b249dfe69 | ||
|
|
d236a9af57 | ||
|
|
ad9b0ae067 | ||
|
|
31f166cd02 | ||
|
|
5685ebc3a5 | ||
|
|
46bcf5da33 | ||
|
|
1784d15f36 | ||
|
|
cafce536bb | ||
|
|
d03280a12f | ||
|
|
b30ef523f8 | ||
|
|
a6a303629a | ||
|
|
61e79ef793 | ||
|
|
f632abd8fa | ||
|
|
c3911fe490 | ||
|
|
505701e1c6 | ||
|
|
67643e7487 | ||
|
|
a962c17adb | ||
|
|
479b4b5859 | ||
|
|
57f8cf85ca | ||
|
|
dd2c20b225 | ||
|
|
9da427a515 | ||
|
|
604773e866 | ||
|
|
1331f5260a | ||
|
|
65d0f3569c | ||
|
|
ba522877ec | ||
|
|
4b63ccf140 | ||
|
|
4fcf93306a | ||
|
|
96d8ec2016 | ||
|
|
3697a5e348 | ||
|
|
084c587c0e | ||
|
|
dcb505045e | ||
|
|
0aeb3128ed | ||
|
|
c61cfcbd18 | ||
|
|
eba2dd36e0 | ||
|
|
2a75754561 | ||
|
|
d03944893d | ||
|
|
884c6ebd37 | ||
|
|
331ac3f031 | ||
|
|
ccc84a8367 | ||
|
|
daeb41c31b | ||
|
|
17bda9c110 | ||
|
|
febedaad8f | ||
|
|
d1357dff1f | ||
|
|
102552427f | ||
|
|
f33898265d | ||
|
|
57bdaf939a | ||
|
|
981fed111b | ||
|
|
3a4a2002d4 | ||
|
|
b8d4af5538 | ||
|
|
0646538cef | ||
|
|
70a87247e2 | ||
|
|
61129c6b6a | ||
|
|
c158f95130 | ||
|
|
ad90d37f14 | ||
|
|
73ba754481 | ||
|
|
7dcfbdbb29 | ||
|
|
f453507fcc | ||
|
|
c5465de000 | ||
|
|
352b864636 | ||
|
|
c034befbb5 | ||
|
|
572cdf40fc | ||
|
|
0c0d353e9c | ||
|
|
bcc90afba2 | ||
|
|
a919703011 | ||
|
|
3300a45c39 | ||
|
|
f1cfae8f26 | ||
|
|
62763961be | ||
|
|
f1dab2279d | ||
|
|
ea337cf839 | ||
|
|
27277136f8 | ||
|
|
dd0b807fe4 | ||
|
|
ed09dd57b6 | ||
|
|
58b4c980c1 | ||
|
|
dd5165dcbf | ||
|
|
6da22613fe | ||
|
|
d0926776a5 | ||
|
|
14dc39e8d2 | ||
|
|
f0f2a79384 | ||
|
|
7b6f875920 | ||
|
|
52cec044b8 | ||
|
|
07dd59892f | ||
|
|
ffeaa683c5 | ||
|
|
1301bf7c15 | ||
|
|
69387fd2a4 | ||
|
|
12a0ebe3ba | ||
|
|
3de81827eb | ||
|
|
a7362b60e7 | ||
|
|
5d4bb3a43f | ||
|
|
d02d507812 | ||
|
|
554de7ba6f | ||
|
|
5d9ccc973d | ||
|
|
53ffb8aa00 | ||
|
|
c4da4a81aa | ||
|
|
b824ea8858 | ||
|
|
22e26efec1 | ||
|
|
679490e8f4 | ||
|
|
15f17ed36d | ||
|
|
c8265fb80c | ||
|
|
3883e92631 | ||
|
|
aa9bc4ce8b | ||
|
|
37c14e8088 | ||
|
|
439fbafc01 | ||
|
|
1b8e980519 | ||
|
|
567acb6291 | ||
|
|
996bfe87ff | ||
|
|
3c1793b6c5 | ||
|
|
1a7f253767 | ||
|
|
f188e59b21 | ||
|
|
5ea4e814f5 | ||
|
|
008b3b8408 | ||
|
|
7ae3dee900 | ||
|
|
2395ab6e14 | ||
|
|
8efe053ffa | ||
|
|
612600b88c | ||
|
|
4d7df52dbe | ||
|
|
b6c63a1aa4 | ||
|
|
a4788ce6bb | ||
|
|
0ba6fc1b36 | ||
|
|
0e35c209d9 | ||
|
|
3b9b2cbe9f | ||
|
|
45240bdb71 | ||
|
|
22a5ac7f0f | ||
|
|
d55d185044 | ||
|
|
2bb09697ce | ||
|
|
f316aff2d3 | ||
|
|
433628791b | ||
|
|
4f52b77563 | ||
|
|
52145c045d | ||
|
|
512761080e | ||
|
|
037a5b71fd | ||
|
|
b66bdec61a | ||
|
|
16f52610ab | ||
|
|
b2f018e29b | ||
|
|
1f497cac44 | ||
|
|
4abe69f90a | ||
|
|
75023011d3 | ||
|
|
09f145d880 | ||
|
|
811cd4248f | ||
|
|
a4871724ac | ||
|
|
a7d6446d8f | ||
|
|
635a17ef1e | ||
|
|
6280fbce17 | ||
|
|
daa72e72b0 | ||
|
|
35bb770697 | ||
|
|
9cc5a7d8de | ||
|
|
9b62f01b53 | ||
|
|
a643a82006 | ||
|
|
82b74d8689 | ||
|
|
a5825bb9f5 | ||
|
|
88a890d717 | ||
|
|
be6fab795d | ||
|
|
7a5b9e2991 | ||
|
|
ee1f70841c | ||
|
|
adc3d17eab | ||
|
|
f909d6fde2 | ||
|
|
016a388147 | ||
|
|
aea442e7e1 | ||
|
|
bb013ceb28 | ||
|
|
dd65e9b89d | ||
|
|
12146eda8c | ||
|
|
cd87fbba0d | ||
|
|
c73541f81f | ||
|
|
4618998792 | ||
|
|
0a3b581aa9 | ||
|
|
aaa319b9bf | ||
|
|
25e782177b | ||
|
|
e940fd3d1f | ||
|
|
31d5cb4ad8 | ||
|
|
21576fe459 | ||
|
|
65863a2cb8 | ||
|
|
cdd055bfa6 | ||
|
|
fedf960a5f | ||
|
|
4546fa3270 | ||
|
|
979f3f557c | ||
|
|
48a38a8a5d | ||
|
|
9880b32b0a | ||
|
|
e664ef7a8d | ||
|
|
7cfef379d0 | ||
|
|
093a91c7fc | ||
|
|
94687a047f | ||
|
|
38fdc603ad | ||
|
|
55cecb7f96 | ||
|
|
32e949598e | ||
|
|
6d0c8aff4b | ||
|
|
5eecf03af6 | ||
|
|
76e9884032 | ||
|
|
9867c4baf0 | ||
|
|
2bc05c8cbd | ||
|
|
d15b0107e4 | ||
|
|
c64cb1304d | ||
|
|
c1f209c7a5 | ||
|
|
116ccd6b3b | ||
|
|
b6f30ae3e1 | ||
|
|
5c522ed2e1 | ||
|
|
bc29b80912 | ||
|
|
cfbc17fbf8 | ||
|
|
af0c939302 | ||
|
|
e02538d38d | ||
|
|
001d37567c | ||
|
|
af82ce31a6 | ||
|
|
12ad4908fa | ||
|
|
40ef94ab45 | ||
|
|
8834ab0210 | ||
|
|
128d23720f | ||
|
|
90f4891ca9 | ||
|
|
61ac81c4d9 | ||
|
|
bd05a8173c | ||
|
|
e3d6461a80 | ||
|
|
2bb582f7ed | ||
|
|
2f9a52852f | ||
|
|
137f083b4d | ||
|
|
11f4c54a40 | ||
|
|
c813eaf6d1 | ||
|
|
ffdaa9dfe9 | ||
|
|
182928002b | ||
|
|
7222af2b7e | ||
|
|
034ead5272 | ||
|
|
eca1f19e95 | ||
|
|
ec70c14649 | ||
|
|
65d906a735 | ||
|
|
b981bae1db | ||
|
|
d2df9ccf33 | ||
|
|
5e51f51449 | ||
|
|
2c044a27e4 | ||
|
|
d274a1115e | ||
|
|
bfae2899f3 | ||
|
|
5352a7e13a | ||
|
|
c49f9ef26a | ||
|
|
4a7376c5f5 | ||
|
|
567ce7f987 | ||
|
|
26bc0a8100 | ||
|
|
e7ff319685 | ||
|
|
072138deff | ||
|
|
dd8dc90c1e | ||
|
|
8f1da33375 | ||
|
|
c02fbc2794 | ||
|
|
371db07108 | ||
|
|
99f5dbf16b | ||
|
|
0db06c8962 | ||
|
|
a8e5876b2e | ||
|
|
8273851b73 | ||
|
|
c2967240bb | ||
|
|
282a6270c8 | ||
|
|
1b299fad90 | ||
|
|
aa8dced7ad | ||
|
|
050ba951b0 | ||
|
|
5e47c16099 | ||
|
|
902db4c732 | ||
|
|
86462fbee6 | ||
|
|
48bed79439 | ||
|
|
26b61c2b6b | ||
|
|
3b2253ddc0 | ||
|
|
5ddcb39129 | ||
|
|
59adef5bcc | ||
|
|
875aefc8dd | ||
|
|
0dbc9d213e | ||
|
|
9f4c53e321 | ||
|
|
3c8716f6ac | ||
|
|
1a7f31ae2e | ||
|
|
64ad69acfe | ||
|
|
9f47b55aa9 | ||
|
|
53a1db0703 | ||
|
|
2a789ec705 | ||
|
|
3047b25193 | ||
|
|
f66399cdc0 | ||
|
|
37fb0f632b | ||
|
|
e5dd0c7ff8 | ||
|
|
51392cd54c | ||
|
|
02bcb4ff3c | ||
|
|
d84297a5b5 | ||
|
|
c3876e30a9 | ||
|
|
10711ed780 | ||
|
|
de4e266e33 | ||
|
|
15442969f8 | ||
|
|
bed48ada82 | ||
|
|
a66004f567 | ||
|
|
72a4e3b3b8 | ||
|
|
16761e4fca | ||
|
|
ba34a6d401 | ||
|
|
23912e4091 | ||
|
|
17468cb5f5 | ||
|
|
5ea7aa0a75 | ||
|
|
7792cd6a10 | ||
|
|
237d186207 | ||
|
|
c41487598e | ||
|
|
2c0aa3c3af | ||
|
|
cedb33b2b9 | ||
|
|
06a3aa2c60 | ||
|
|
3fadc94711 | ||
|
|
61d02bf5e4 | ||
|
|
a62976461e | ||
|
|
d7a893acf9 | ||
|
|
0c67e75fb6 | ||
|
|
e6b84c4cfc | ||
|
|
5d2e793386 | ||
|
|
f0517906b7 | ||
|
|
16fa167931 | ||
|
|
b036999b8c | ||
|
|
1911766b7b | ||
|
|
9f7835d818 | ||
|
|
1df45e4857 | ||
|
|
47a1743965 | ||
|
|
d5844bbdaa | ||
|
|
128c87ab33 | ||
|
|
f4adcae79a | ||
|
|
ba4df070cf | ||
|
|
ce4ecfb388 | ||
|
|
e6006e0833 | ||
|
|
d500cc0bd1 | ||
|
|
71995b4f83 | ||
|
|
932c91d022 | ||
|
|
107e7424d1 | ||
|
|
c93181c0ad | ||
|
|
050fca6767 | ||
|
|
71827b4a1a | ||
|
|
1d0315bf5e | ||
|
|
b2b64e7283 | ||
|
|
fe0e2edd37 | ||
|
|
e5bb3d5645 | ||
|
|
b88a99347b | ||
|
|
344a909d19 | ||
|
|
3cbe3aab25 | ||
|
|
9e3a4b1810 | ||
|
|
e855bbaa29 | ||
|
|
78d7dca985 | ||
|
|
9da7ded976 | ||
|
|
427b107d0e | ||
|
|
1cab68e385 | ||
|
|
07e4fa8abd | ||
|
|
77b86c78a4 | ||
|
|
e4c701864a | ||
|
|
0275f28490 | ||
|
|
300c3dd578 | ||
|
|
fb81870803 | ||
|
|
bb6a61a313 | ||
|
|
976d917a57 | ||
|
|
7e13cc2ca8 | ||
|
|
704296df4e | ||
|
|
65244e3b8d | ||
|
|
3cf54a4cce | ||
|
|
031c09d8dc | ||
|
|
5209d9cf75 | ||
|
|
815dad18f4 | ||
|
|
4319382da3 | ||
|
|
5e96cec95b | ||
|
|
071982097a | ||
|
|
56024de6cc | ||
|
|
845d4acd8e | ||
|
|
b0029e9255 | ||
|
|
23bc44a350 | ||
|
|
0bf52f4746 | ||
|
|
345707e6cc | ||
|
|
e2752e4508 | ||
|
|
9916a53761 | ||
|
|
4581c99a81 | ||
|
|
c3fdc41a91 | ||
|
|
edf2f51aa1 | ||
|
|
de944d0095 | ||
|
|
49ffc972f8 | ||
|
|
2d8e5b2420 | ||
|
|
7c48975198 | ||
|
|
9bc250d027 | ||
|
|
41d4e7e15b | ||
|
|
b0d2a38ff6 | ||
|
|
bd4d4d927e | ||
|
|
db17cacbf4 | ||
|
|
0c5961df98 | ||
|
|
0e67b76b57 | ||
|
|
f72b323ab5 | ||
|
|
927c21a60f | ||
|
|
624a9ba8eb | ||
|
|
8509283ac2 | ||
|
|
aa9ba27f40 | ||
|
|
06434464bb | ||
|
|
3e7bfc72a2 | ||
|
|
8dfbc35e60 | ||
|
|
503e5ec950 | ||
|
|
414aeb0ac3 | ||
|
|
55b8544d32 | ||
|
|
2d67ea5f7f | ||
|
|
4eaf72fa3e | ||
|
|
95ef3c1782 | ||
|
|
b3ef410fb7 | ||
|
|
0c55bca218 | ||
|
|
5fd28439dc | ||
|
|
a58c18e992 | ||
|
|
058dfdfcd6 | ||
|
|
637fdac28a | ||
|
|
a8b667780a | ||
|
|
b4f13e10d3 | ||
|
|
d0eb55fb86 | ||
|
|
b041dbd14f | ||
|
|
0ab814fbc4 | ||
|
|
a2144b1759 | ||
|
|
82eb3b5ccf | ||
|
|
7515080c63 | ||
|
|
07015c5172 | ||
|
|
19918cd342 | ||
|
|
16f0ed548e | ||
|
|
0d1600275d | ||
|
|
768f32bd2d | ||
|
|
d86798a7c6 | ||
|
|
7718c6a2a5 | ||
|
|
a0616ac2cb | ||
|
|
23bbe0d52b | ||
|
|
6d9e7758a2 | ||
|
|
f81a80c2da | ||
|
|
ab64619a41 | ||
|
|
18bdd26be8 | ||
|
|
c5f3a674d6 | ||
|
|
f95e17b144 | ||
|
|
4989826124 | ||
|
|
f23a551ae3 | ||
|
|
bd2df01b12 | ||
|
|
880ef303e8 | ||
|
|
b4ed1a0bdc | ||
|
|
7a2eae0699 | ||
|
|
4464252cae | ||
|
|
ca8cf44200 | ||
|
|
4565165579 | ||
|
|
a37be432a9 | ||
|
|
90591e852d | ||
|
|
13f7d44a06 | ||
|
|
7dc8aa66a6 | ||
|
|
6cf28ab718 | ||
|
|
f461c5e8b7 | ||
|
|
9433bdf4ad | ||
|
|
d2d494e079 | ||
|
|
e64b35cde8 | ||
|
|
d32e8c6e98 | ||
|
|
55cee488bc | ||
|
|
65b8942416 | ||
|
|
94cf7c329c | ||
|
|
8eac7d6b4d | ||
|
|
7ebb34de80 | ||
|
|
6ea84906ac | ||
|
|
f7971a871a | ||
|
|
54b35b7c2b | ||
|
|
ca970b4ffb | ||
|
|
8a96e32679 | ||
|
|
fc4d01b3e5 | ||
|
|
b6afc8f6ce | ||
|
|
c481a431be | ||
|
|
0a7b82793e | ||
|
|
3653236bcb | ||
|
|
a2eee72015 | ||
|
|
5672646278 | ||
|
|
c4d3fa7a48 | ||
|
|
32b0267b9f | ||
|
|
a7b41a4b8c | ||
|
|
bfd6d14bf3 | ||
|
|
469de31218 | ||
|
|
2ce9823b3a | ||
|
|
e8b3d09ddf | ||
|
|
f613c01803 | ||
|
|
a5a5908fb5 | ||
|
|
5313a0ed47 | ||
|
|
1c15eebd7c | ||
|
|
f3cab6e177 | ||
|
|
c0623334ee | ||
|
|
d41bd6b6b1 | ||
|
|
c9b4a8eef5 | ||
|
|
3619cb8bd1 | ||
|
|
8e2316ba62 | ||
|
|
495abf42ef | ||
|
|
5372dd633e | ||
|
|
5efa1ebe88 | ||
|
|
07677ed4a7 | ||
|
|
73e5640109 | ||
|
|
bdbded8588 | ||
|
|
e0fbf8920d | ||
|
|
7b2227bfac | ||
|
|
12866ca7ba | ||
|
|
1427b1537e | ||
|
|
6ceb133bb5 | ||
|
|
4ab67aaf90 | ||
|
|
6cce0a3901 | ||
|
|
fa67789350 | ||
|
|
16adeb1373 | ||
|
|
29c1cf1237 | ||
|
|
0e52065893 | ||
|
|
3972c08efc | ||
|
|
1a679ee05d | ||
|
|
b2286055b0 | ||
|
|
249d0d43de | ||
|
|
536630cbcd | ||
|
|
70d0bfce15 | ||
|
|
84e36ed847 | ||
|
|
3d4ff687b5 | ||
|
|
edddf65d0e | ||
|
|
f216273008 | ||
|
|
3295ef4fcf | ||
|
|
4ea0e04852 | ||
|
|
414c0b3a8d | ||
|
|
ff6a1c14be | ||
|
|
0e1a862e34 | ||
|
|
d902c71a6f | ||
|
|
b3f6d5206a | ||
|
|
ff0d80e84f | ||
|
|
cf080330ba | ||
|
|
2373bacb0c | ||
|
|
938edefea1 | ||
|
|
393be92632 | ||
|
|
267440142e | ||
|
|
d11fa476e1 | ||
|
|
bd2994f9ab | ||
|
|
2806feb468 | ||
|
|
8e40069e67 | ||
|
|
24d7d8dcc4 | ||
|
|
34147d7694 | ||
|
|
83bd245bfd | ||
|
|
a02452ccb9 | ||
|
|
a8f72564f4 | ||
|
|
6e7b311696 | ||
|
|
2bda0eb761 | ||
|
|
c2661fb79e | ||
|
|
4e70fd704b | ||
|
|
85d03a9946 | ||
|
|
1c7994a353 | ||
|
|
347c2b6bcc | ||
|
|
19d9953a48 | ||
|
|
7b4e815a8d | ||
|
|
59011c9517 | ||
|
|
39d5c9e525 | ||
|
|
e6d553c8ff | ||
|
|
fecd777d30 | ||
|
|
ce64b1fc09 | ||
|
|
857e442376 | ||
|
|
b0e407bf30 | ||
|
|
cad64ba044 | ||
|
|
85801f18ae | ||
|
|
f93a40a18b | ||
|
|
9b0c44162a | ||
|
|
a66ac1594b | ||
|
|
101e7bbce0 | ||
|
|
0e969bbaad | ||
|
|
621b4c8213 | ||
|
|
8ca6e44de7 | ||
|
|
8ee2c972d3 | ||
|
|
fafcf09570 | ||
|
|
0b14328024 | ||
|
|
2d2b24f589 | ||
|
|
346d8f7583 | ||
|
|
2096532f5d | ||
|
|
4136eb1444 | ||
|
|
67e0acd044 | ||
|
|
cbcdfc5f6c | ||
|
|
288d952686 | ||
|
|
c36e02bba9 | ||
|
|
c121a4c0f5 | ||
|
|
2bac5aabee | ||
|
|
97ff225bc0 | ||
|
|
d5e78b9f80 | ||
|
|
3f98affd5a | ||
|
|
531c2bcf00 | ||
|
|
dd5505918a | ||
|
|
4a30a69eb4 | ||
|
|
38b302e5a5 | ||
|
|
ea010895a0 | ||
|
|
7b88512698 | ||
|
|
1ff24d9285 | ||
|
|
ebf742d272 | ||
|
|
a7b1b04920 | ||
|
|
1218d6abe8 | ||
|
|
f9d546676b | ||
|
|
afef6960b9 | ||
|
|
f6626b8975 | ||
|
|
b1e66f81ab | ||
|
|
9cc018e618 | ||
|
|
797cd9bea2 | ||
|
|
9dbfca3d7a | ||
|
|
f18d1efdcb | ||
|
|
29a9b89224 | ||
|
|
11b5b9808b | ||
|
|
ca1f84d22b | ||
|
|
d6c6c88e6e | ||
|
|
ee33702463 | ||
|
|
8b6995e9ec | ||
|
|
36ba8f0fcb | ||
|
|
bfb560ec50 | ||
|
|
78bb11dcbf | ||
|
|
5c8d00665f | ||
|
|
f4d78cc08e | ||
|
|
2aa395ba12 | ||
|
|
ac862e6822 | ||
|
|
1b55ead16e | ||
|
|
b24727ec22 | ||
|
|
2768926683 | ||
|
|
3f07bd6471 | ||
|
|
2f861f19c0 | ||
|
|
6b397cff73 | ||
|
|
44a3cf86d3 | ||
|
|
dfb0a40293 | ||
|
|
7719dd378b | ||
|
|
c9f8e43681 | ||
|
|
4a7538041d | ||
|
|
dd3b2288e2 | ||
|
|
496abc3a98 | ||
|
|
8b9abfb26e | ||
|
|
330e21e2ba | ||
|
|
e53d0dadbf | ||
|
|
fa56685767 | ||
|
|
2727f4b92d | ||
|
|
0f74f65af8 | ||
|
|
8e03968370 | ||
|
|
969f181f3e | ||
|
|
cc18077192 | ||
|
|
47d07b2326 | ||
|
|
a96bb72fb8 | ||
|
|
75364dd5b4 | ||
|
|
22624ae4d5 | ||
|
|
cb23d3ff3c | ||
|
|
e751bdc8a9 | ||
|
|
2078d048a1 | ||
|
|
22ff25269d | ||
|
|
1ee9a6a39d | ||
|
|
50efd865d9 | ||
|
|
d688d3837f | ||
|
|
6cb438440d | ||
|
|
2c5771d9e8 | ||
|
|
0ce06116e6 | ||
|
|
706bc0fdfe | ||
|
|
0b5b1ba11a | ||
|
|
0ed8ca961e | ||
|
|
31d4b62bf3 | ||
|
|
35d6172d06 | ||
|
|
b5ed8f0183 | ||
|
|
7cb3bb0d4e | ||
|
|
d27d42d9ca | ||
|
|
e2fd6e8f86 | ||
|
|
a8e534a8a4 | ||
|
|
479d7575fa | ||
|
|
4707a3075e | ||
|
|
21a189e0b7 | ||
|
|
ab7ff6551f | ||
|
|
248961d58c | ||
|
|
473e226883 | ||
|
|
2ebb06d330 | ||
|
|
cc88e68c4e | ||
|
|
f8704747d9 | ||
|
|
0c33df883c | ||
|
|
3fbc396bc8 | ||
|
|
17df7a46e2 | ||
|
|
925c1d3d8e | ||
|
|
1976d4cc1b | ||
|
|
d98578f260 | ||
|
|
8d1dddf205 | ||
|
|
2584b6ca5b | ||
|
|
70897cebfe | ||
|
|
0e80cd5c44 | ||
|
|
b979e313b2 | ||
|
|
533cb42d29 | ||
|
|
35a209903e | ||
|
|
824de61579 | ||
|
|
17ca3f8ac2 | ||
|
|
87a299736e | ||
|
|
e86286722a | ||
|
|
c4a0724c8d | ||
|
|
17139f34dd | ||
|
|
1779714b0d | ||
|
|
1ff4495737 | ||
|
|
02c0dc1217 | ||
|
|
fb43c194b9 | ||
|
|
ae94bb56d9 | ||
|
|
123433c4ea | ||
|
|
58619076ea | ||
|
|
a50d1c5784 | ||
|
|
91c8cb197f | ||
|
|
427c60618f | ||
|
|
2d417f200d | ||
|
|
54b11e7b25 | ||
|
|
50d2eb7d57 | ||
|
|
dfb20dd1ca | ||
|
|
4f22016f13 | ||
|
|
430a2d0454 | ||
|
|
db23c8ce9f | ||
|
|
ffd4784916 | ||
|
|
750830c302 | ||
|
|
d245ef9b39 | ||
|
|
c8586d1ef4 | ||
|
|
316cba1cb8 | ||
|
|
13dba62b8d | ||
|
|
c2ff169c08 | ||
|
|
57a1dbfc6d | ||
|
|
efb39d6fc6 | ||
|
|
b784234430 | ||
|
|
aebad92426 | ||
|
|
8e67cfd5c9 | ||
|
|
10cc6d7e08 | ||
|
|
83c236c829 | ||
|
|
b6ab37691f | ||
|
|
c85af78025 | ||
|
|
2c2fc6dd97 | ||
|
|
3620b76139 | ||
|
|
ca5732e586 | ||
|
|
2463d72f3b | ||
|
|
d6f7474200 | ||
|
|
0b2bc7ab3f | ||
|
|
0a4fac61d4 | ||
|
|
797aec5528 | ||
|
|
5f0b95dc59 | ||
|
|
b384c5f14c | ||
|
|
5254dca9d9 | ||
|
|
8534ccbf37 | ||
|
|
9af874d810 | ||
|
|
4e3dee15ce | ||
|
|
aaad618e20 | ||
|
|
10bb50bd82 | ||
|
|
6d2ff6e019 | ||
|
|
670070a879 | ||
|
|
dcec8007d4 | ||
|
|
3abf4a49cd | ||
|
|
38825bf96a | ||
|
|
faa69da28d | ||
|
|
5cf524e2fd | ||
|
|
88802a44e7 | ||
|
|
94498d862d | ||
|
|
9418b24e8f | ||
|
|
b92cbcd7e7 | ||
|
|
9ef2ff92df | ||
|
|
422724bd2d | ||
|
|
6cb7897f25 | ||
|
|
499ba15004 | ||
|
|
b04abe989e | ||
|
|
ea576179f9 | ||
|
|
116d53a978 | ||
|
|
32adbf2ec8 | ||
|
|
c664484fda | ||
|
|
06906eba4c | ||
|
|
d387ebf32d | ||
|
|
f75556f33c | ||
|
|
2cf09e4de6 | ||
|
|
a5a3a9c586 | ||
|
|
746dfbd955 | ||
|
|
b1993d2fb7 | ||
|
|
e8096dec88 | ||
|
|
39eee51ec8 | ||
|
|
7bb3a10795 | ||
|
|
a8cbe4b05f | ||
|
|
fe86da0cde | ||
|
|
4c86a2c191 | ||
|
|
8dc5db17ac | ||
|
|
549c3a190e | ||
|
|
7a68c4ccf3 | ||
|
|
4c684df653 | ||
|
|
bf8831b833 | ||
|
|
394227571f | ||
|
|
bf67577073 | ||
|
|
e180611024 | ||
|
|
43cfc55368 | ||
|
|
c03b7ea15d | ||
|
|
ddfedfb590 | ||
|
|
24418370f1 | ||
|
|
02521b6964 | ||
|
|
16f693148b | ||
|
|
0bf46cb63f | ||
|
|
2e38855396 | ||
|
|
97592a1387 | ||
|
|
c61bf76c80 | ||
|
|
e95b137011 | ||
|
|
ad655183e0 | ||
|
|
789fd34c4a | ||
|
|
87bbbaa475 | ||
|
|
a4ca813cf5 | ||
|
|
e8eef73212 | ||
|
|
512d4a43cb | ||
|
|
b9f7b1d175 | ||
|
|
b7727e2659 | ||
|
|
229d1d8c6e | ||
|
|
c0b18f85aa | ||
|
|
b11b9588f8 | ||
|
|
633d028841 | ||
|
|
a744b304a0 | ||
|
|
e594350307 | ||
|
|
ecf7a1eac1 | ||
|
|
4621afcb31 | ||
|
|
006c949941 | ||
|
|
72e06ab337 | ||
|
|
f4b2a32a23 | ||
|
|
329e21fd78 | ||
|
|
5499d15402 | ||
|
|
d7f8a05612 | ||
|
|
1f99a75049 | ||
|
|
21fd436621 | ||
|
|
ebcbe98684 | ||
|
|
0e437c1105 | ||
|
|
4b18f56f00 | ||
|
|
fd7ab0a7fd | ||
|
|
c3c84d0ea0 | ||
|
|
43b00c5696 | ||
|
|
a9f4536de4 | ||
|
|
892230280c | ||
|
|
0969a0c42a | ||
|
|
185143ecf6 | ||
|
|
6e06f94a91 | ||
|
|
9af0bc31c3 | ||
|
|
6bcbb13bfb | ||
|
|
9a6d48d038 | ||
|
|
0e81f6c3af | ||
|
|
353a2dd92b | ||
|
|
ee749236e1 | ||
|
|
cf45401250 | ||
|
|
15429160c7 | ||
|
|
3ea7f31797 | ||
|
|
dbfa2f9944 | ||
|
|
98cf176c81 | ||
|
|
39b00797d6 | ||
|
|
1df5a36f84 | ||
|
|
1db3bb3d33 | ||
|
|
807848b6bb | ||
|
|
917598acf8 | ||
|
|
b8bddf6a39 | ||
|
|
da95b7559d | ||
|
|
041b475f49 | ||
|
|
c0a8604f90 | ||
|
|
ce80bd521a | ||
|
|
e92615b3a8 | ||
|
|
3d7349ee53 | ||
|
|
0935a637f9 | ||
|
|
c23d40ca71 | ||
|
|
9ffe908c66 | ||
|
|
45003436bf | ||
|
|
5074ff2889 | ||
|
|
c1d7582461 | ||
|
|
186c7d5786 | ||
|
|
7a87d353cb | ||
|
|
badd2a102f | ||
|
|
d0a79c2b4c | ||
|
|
bd781bbcfb | ||
|
|
f3d50e158a | ||
|
|
34ada4113f | ||
|
|
4f43b504f4 | ||
|
|
62e4b03342 | ||
|
|
dca7b0ba91 | ||
|
|
2a61befbfd | ||
|
|
287be26190 | ||
|
|
4992e11383 | ||
|
|
727734850e | ||
|
|
e042d25062 | ||
|
|
ba7a11d0e5 | ||
|
|
ecbcc8b6f1 | ||
|
|
94f320336c | ||
|
|
c27f53b5b1 | ||
|
|
134d819bdf | ||
|
|
dc7c2ce56b | ||
|
|
0cd820e923 | ||
|
|
c047a4476e | ||
|
|
51ca2ee9d8 | ||
|
|
e612a8a496 | ||
|
|
e70d86e843 | ||
|
|
1bc637a43f | ||
|
|
f5b738198f | ||
|
|
34ea89c3be | ||
|
|
d4cbc45e16 | ||
|
|
59ae2f327c | ||
|
|
4ec5b7fc69 | ||
|
|
9e31bbe716 | ||
|
|
65cfa6d347 | ||
|
|
9099ad3d8b | ||
|
|
43876b5ab9 | ||
|
|
6017946144 | ||
|
|
3a8151bcc0 | ||
|
|
2dfe88b82d | ||
|
|
a332e12338 | ||
|
|
25f6291403 | ||
|
|
5807286355 | ||
|
|
445dcf0b6d | ||
|
|
f231107869 | ||
|
|
2cf33b04f9 | ||
|
|
1e7d2e7dce | ||
|
|
186945532f | ||
|
|
c14cabc1c9 | ||
|
|
df755a2a47 | ||
|
|
a828bafa01 | ||
|
|
d668bca087 | ||
|
|
aaa0700155 | ||
|
|
83843bf373 |
84
.github/ISSUE_TEMPLATE/bug_report.yaml
vendored
Normal file
84
.github/ISSUE_TEMPLATE/bug_report.yaml
vendored
Normal file
@@ -0,0 +1,84 @@
|
||||
---
|
||||
name: Bug report
|
||||
description: Create a report to help us improve Flux
|
||||
body:
|
||||
- type: markdown
|
||||
attributes:
|
||||
value: |
|
||||
## Support
|
||||
Find out more about your support options and getting help at: https://fluxcd.io/support/
|
||||
- type: textarea
|
||||
validations:
|
||||
required: true
|
||||
attributes:
|
||||
label: Describe the bug
|
||||
description: A clear description of what the bug is.
|
||||
- type: textarea
|
||||
validations:
|
||||
required: true
|
||||
attributes:
|
||||
label: Steps to reproduce
|
||||
description: |
|
||||
Steps to reproduce the problem.
|
||||
placeholder: |
|
||||
For example:
|
||||
1. Install Flux with the additional image automation controllers
|
||||
2. Run command '...'
|
||||
3. See error
|
||||
- type: textarea
|
||||
validations:
|
||||
required: true
|
||||
attributes:
|
||||
label: Expected behavior
|
||||
description: A brief description of what you expected to happen.
|
||||
- type: textarea
|
||||
attributes:
|
||||
label: Screenshots and recordings
|
||||
description: |
|
||||
If applicable, add screenshots to help explain your problem. You can also record an asciinema session: https://asciinema.org/
|
||||
- type: input
|
||||
validations:
|
||||
required: true
|
||||
attributes:
|
||||
label: OS / Distro
|
||||
description: The OS / distro you are executing `flux` on. If not applicable, write `N/A`.
|
||||
placeholder: e.g. Windows 10, Ubuntu 20.04, Arch Linux, macOS 10.15...
|
||||
- type: input
|
||||
validations:
|
||||
required: true
|
||||
attributes:
|
||||
label: Flux version
|
||||
description: Run `flux version --client`. If not applicable, write `N/A`.
|
||||
placeholder: e.g. v0.20.1
|
||||
- type: textarea
|
||||
validations:
|
||||
required: true
|
||||
attributes:
|
||||
label: Flux check
|
||||
description: Run `flux check`. If not applicable, write `N/A`.
|
||||
placeholder: |
|
||||
For example:
|
||||
► checking prerequisites
|
||||
✔ Kubernetes 1.21.1 >=1.19.0-0
|
||||
► checking controllers
|
||||
✔ all checks passed
|
||||
- type: input
|
||||
attributes:
|
||||
label: Git provider
|
||||
description: If applicable, add the Git provider you are having problems with, e.g. GitHub (Enterprise), GitLab, etc.
|
||||
- type: input
|
||||
attributes:
|
||||
label: Container Registry provider
|
||||
description: If applicable, add the Container Registry provider you are having problems with, e.g. DockerHub, GitHub Packages, Quay.io, etc.
|
||||
- type: textarea
|
||||
attributes:
|
||||
label: Additional context
|
||||
description: Add any other context about the problem here. This can be logs (e.g. output from `flux logs`), environment specific caveats, etc.
|
||||
- type: checkboxes
|
||||
id: terms
|
||||
attributes:
|
||||
label: Code of Conduct
|
||||
description: By submitting this issue, you agree to follow our [Code of Conduct](https://github.com/fluxcd/.github/blob/main/CODE_OF_CONDUCT.md)
|
||||
options:
|
||||
- label: I agree to follow this project's Code of Conduct
|
||||
required: true
|
||||
5
.github/ISSUE_TEMPLATE/config.yml
vendored
Normal file
5
.github/ISSUE_TEMPLATE/config.yml
vendored
Normal file
@@ -0,0 +1,5 @@
|
||||
blank_issues_enabled: true
|
||||
contact_links:
|
||||
- name: Ask a question
|
||||
url: https://github.com/fluxcd/flux2/discussions
|
||||
about: Please ask and answer questions here.
|
||||
6
.github/actions/kustomize/Dockerfile
vendored
6
.github/actions/kustomize/Dockerfile
vendored
@@ -1,6 +0,0 @@
|
||||
FROM giantswarm/tiny-tools
|
||||
|
||||
COPY entrypoint.sh /entrypoint.sh
|
||||
RUN chmod +x /entrypoint.sh
|
||||
|
||||
ENTRYPOINT ["/entrypoint.sh"]
|
||||
9
.github/actions/kustomize/action.yml
vendored
9
.github/actions/kustomize/action.yml
vendored
@@ -1,9 +0,0 @@
|
||||
name: 'kustomize'
|
||||
description: 'A GitHub Action to run kustomize commands'
|
||||
author: 'Stefan Prodan'
|
||||
branding:
|
||||
icon: 'command'
|
||||
color: 'blue'
|
||||
runs:
|
||||
using: 'docker'
|
||||
image: 'Dockerfile'
|
||||
12
.github/actions/kustomize/entrypoint.sh
vendored
12
.github/actions/kustomize/entrypoint.sh
vendored
@@ -1,12 +0,0 @@
|
||||
#!/bin/sh -l
|
||||
|
||||
VERSION=3.5.4
|
||||
curl -sL https://github.com/kubernetes-sigs/kustomize/releases/download/kustomize%2Fv${VERSION}/kustomize_v${VERSION}_linux_amd64.tar.gz | tar xz
|
||||
|
||||
mkdir -p $GITHUB_WORKSPACE/bin
|
||||
cp ./kustomize $GITHUB_WORKSPACE/bin
|
||||
chmod +x $GITHUB_WORKSPACE/bin/kustomize
|
||||
ls -lh $GITHUB_WORKSPACE/bin
|
||||
|
||||
echo "::add-path::$GITHUB_WORKSPACE/bin"
|
||||
echo "::add-path::$RUNNER_WORKSPACE/$(basename $GITHUB_REPOSITORY)/bin"
|
||||
22
.github/aur/flux-bin/.SRCINFO.template
vendored
Normal file
22
.github/aur/flux-bin/.SRCINFO.template
vendored
Normal file
@@ -0,0 +1,22 @@
|
||||
pkgbase = flux-bin
|
||||
pkgdesc = Open and extensible continuous delivery solution for Kubernetes
|
||||
pkgver = ${PKGVER}
|
||||
pkgrel = ${PKGREL}
|
||||
url = https://fluxcd.io/
|
||||
arch = x86_64
|
||||
arch = armv6h
|
||||
arch = armv7h
|
||||
arch = aarch64
|
||||
license = APACHE
|
||||
optdepends = bash-completion: auto-completion for flux in Bash
|
||||
optdepends = zsh-completions: auto-completion for flux in ZSH
|
||||
source_x86_64 = flux-${PKGVER}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${VERSION}/flux_${VERSION}_linux_amd64.tar.gz
|
||||
sha256sums_x86_64 = ${SHA256SUM_AMD64}
|
||||
source_armv6h = flux-${PKGVER}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${VERSION}/flux_${VERSION}_linux_arm.tar.gz
|
||||
sha256sums_armv6h = ${SHA256SUM_ARM}
|
||||
source_armv7h = flux-${PKGVER}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${VERSION}/flux_${VERSION}_linux_arm.tar.gz
|
||||
sha256sums_armv7h = ${SHA256SUM_ARM}
|
||||
source_aarch64 = flux-${PKGVER}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${VERSION}/flux_${VERSION}_linux_arm64.tar.gz
|
||||
sha256sums_aarch64 = ${SHA256SUM_ARM64}
|
||||
|
||||
pkgname = flux-bin
|
||||
1
.github/aur/flux-bin/.gitignore
vendored
Normal file
1
.github/aur/flux-bin/.gitignore
vendored
Normal file
@@ -0,0 +1 @@
|
||||
.pkg
|
||||
46
.github/aur/flux-bin/PKGBUILD.template
vendored
Normal file
46
.github/aur/flux-bin/PKGBUILD.template
vendored
Normal file
@@ -0,0 +1,46 @@
|
||||
# Maintainer: Aurel Canciu <aurelcanciu@gmail.com>
|
||||
# Maintainer: Hidde Beydals <hello@hidde.co>
|
||||
|
||||
pkgname=flux-bin
|
||||
pkgver=${PKGVER}
|
||||
pkgrel=${PKGREL}
|
||||
_srcname=flux
|
||||
_srcver=${VERSION}
|
||||
pkgdesc="Open and extensible continuous delivery solution for Kubernetes"
|
||||
url="https://fluxcd.io/"
|
||||
arch=("x86_64" "armv6h" "armv7h" "aarch64")
|
||||
license=("APACHE")
|
||||
optdepends=('bash-completion: auto-completion for flux in Bash'
|
||||
'zsh-completions: auto-completion for flux in ZSH')
|
||||
source_x86_64=(
|
||||
"${pkgname}-${pkgver}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${_srcver}/flux_${_srcver}_linux_amd64.tar.gz"
|
||||
)
|
||||
source_armv6h=(
|
||||
"${pkgname}-${pkgver}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${_srcver}/flux_${_srcver}_linux_arm.tar.gz"
|
||||
)
|
||||
source_armv7h=(
|
||||
"${pkgname}-${pkgver}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${_srcver}/flux_${_srcver}_linux_arm.tar.gz"
|
||||
)
|
||||
source_aarch64=(
|
||||
"${pkgname}-${pkgver}.tar.gz::https://github.com/fluxcd/flux2/releases/download/v${_srcver}/flux_${_srcver}_linux_arm64.tar.gz"
|
||||
)
|
||||
sha256sums_x86_64=(
|
||||
${SHA256SUM_AMD64}
|
||||
)
|
||||
sha256sums_armv6h=(
|
||||
${SHA256SUM_ARM}
|
||||
)
|
||||
sha256sums_armv7h=(
|
||||
${SHA256SUM_ARM}
|
||||
)
|
||||
sha256sums_aarch64=(
|
||||
${SHA256SUM_ARM64}
|
||||
)
|
||||
|
||||
package() {
|
||||
install -Dm755 ${_srcname} "${pkgdir}/usr/bin/${_srcname}"
|
||||
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion bash | install -Dm644 /dev/stdin "${pkgdir}/usr/share/bash-completion/completions/${_srcname}"
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion fish | install -Dm644 /dev/stdin "${pkgdir}/usr/share/fish/vendor_completions.d/${_srcname}.fish"
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion zsh | install -Dm644 /dev/stdin "${pkgdir}/usr/share/zsh/site-functions/_${_srcname}"
|
||||
}
|
||||
56
.github/aur/flux-bin/publish.sh
vendored
Executable file
56
.github/aur/flux-bin/publish.sh
vendored
Executable file
@@ -0,0 +1,56 @@
|
||||
#!/usr/bin/env bash
|
||||
|
||||
set -e
|
||||
|
||||
WD=$(cd "$( dirname "${BASH_SOURCE[0]}" )" >/dev/null 2>&1 && pwd)
|
||||
PKGNAME=$(basename $WD)
|
||||
ROOT=${WD%/.github/aur/$PKGNAME}
|
||||
|
||||
LOCKFILE=/tmp/aur-$PKGNAME.lock
|
||||
exec 100>$LOCKFILE || exit 0
|
||||
flock -n 100 || exit 0
|
||||
trap "rm -f $LOCKFILE" EXIT
|
||||
|
||||
export VERSION=$1
|
||||
echo "Publishing to AUR as version ${VERSION}"
|
||||
|
||||
cd $WD
|
||||
|
||||
export GIT_SSH_COMMAND="ssh -o UserKnownHostsFile=/dev/null -o StrictHostKeyChecking=no"
|
||||
|
||||
eval $(ssh-agent -s)
|
||||
ssh-add <(echo "$AUR_BOT_SSH_PRIVATE_KEY")
|
||||
|
||||
GITDIR=$(mktemp -d /tmp/aur-$PKGNAME-XXX)
|
||||
trap "rm -rf $GITDIR" EXIT
|
||||
git clone aur@aur.archlinux.org:$PKGNAME $GITDIR 2>&1
|
||||
|
||||
CURRENT_PKGVER=$(cat $GITDIR/.SRCINFO | grep pkgver | awk '{ print $3 }')
|
||||
CURRENT_PKGREL=$(cat $GITDIR/.SRCINFO | grep pkgrel | awk '{ print $3 }')
|
||||
|
||||
# Transform pre-release to AUR compatible version format
|
||||
export PKGVER=${VERSION/-/}
|
||||
|
||||
if [[ "${CURRENT_PKGVER}" == "${PKGVER}" ]]; then
|
||||
export PKGREL=$((CURRENT_PKGREL+1))
|
||||
else
|
||||
export PKGREL=1
|
||||
fi
|
||||
|
||||
export SHA256SUM_ARM=$(sha256sum ${ROOT}/dist/flux_${VERSION}_linux_arm.tar.gz | awk '{ print $1 }')
|
||||
export SHA256SUM_ARM64=$(sha256sum ${ROOT}/dist/flux_${VERSION}_linux_arm64.tar.gz | awk '{ print $1 }')
|
||||
export SHA256SUM_AMD64=$(sha256sum ${ROOT}/dist/flux_${VERSION}_linux_amd64.tar.gz | awk '{ print $1 }')
|
||||
|
||||
envsubst '$VERSION $PKGVER $PKGREL $SHA256SUM_AMD64 $SHA256SUM_ARM $SHA256SUM_ARM64' < .SRCINFO.template > $GITDIR/.SRCINFO
|
||||
envsubst '$VERSION $PKGVER $PKGREL $SHA256SUM_AMD64 $SHA256SUM_ARM $SHA256SUM_ARM64' < PKGBUILD.template > $GITDIR/PKGBUILD
|
||||
|
||||
cd $GITDIR
|
||||
git config user.name "fluxcdbot"
|
||||
git config user.email "fluxcdbot@users.noreply.github.com"
|
||||
git add -A
|
||||
if [ -z "$(git status --porcelain)" ]; then
|
||||
echo "No changes."
|
||||
else
|
||||
git commit -m "Updated to version v${PKGVER} release ${PKGREL}"
|
||||
git push origin master
|
||||
fi
|
||||
18
.github/aur/flux-go/.SRCINFO.template
vendored
Normal file
18
.github/aur/flux-go/.SRCINFO.template
vendored
Normal file
@@ -0,0 +1,18 @@
|
||||
pkgbase = flux-go
|
||||
pkgdesc = Open and extensible continuous delivery solution for Kubernetes
|
||||
pkgver = ${PKGVER}
|
||||
pkgrel = ${PKGREL}
|
||||
url = https://fluxcd.io/
|
||||
arch = x86_64
|
||||
arch = armv6h
|
||||
arch = armv7h
|
||||
arch = aarch64
|
||||
license = APACHE
|
||||
makedepends = go
|
||||
depends = glibc
|
||||
provides = flux-bin
|
||||
conflicts = flux-bin
|
||||
replaces = flux-cli
|
||||
source = flux-go-${PKGVER}.tar.gz::https://github.com/fluxcd/flux2/archive/v${VERSION}.tar.gz
|
||||
|
||||
pkgname = flux-go
|
||||
1
.github/aur/flux-go/.gitignore
vendored
Normal file
1
.github/aur/flux-go/.gitignore
vendored
Normal file
@@ -0,0 +1 @@
|
||||
.pkg
|
||||
59
.github/aur/flux-go/PKGBUILD.template
vendored
Normal file
59
.github/aur/flux-go/PKGBUILD.template
vendored
Normal file
@@ -0,0 +1,59 @@
|
||||
# Maintainer: Aurel Canciu <aurelcanciu@gmail.com>
|
||||
# Maintainer: Hidde Beydals <hello@hidde.co>
|
||||
|
||||
pkgname=flux-go
|
||||
pkgver=${PKGVER}
|
||||
pkgrel=${PKGREL}
|
||||
_srcname=flux
|
||||
_srcver=${VERSION}
|
||||
pkgdesc="Open and extensible continuous delivery solution for Kubernetes"
|
||||
url="https://fluxcd.io/"
|
||||
arch=("x86_64" "armv6h" "armv7h" "aarch64")
|
||||
license=("APACHE")
|
||||
provides=("flux-bin")
|
||||
conflicts=("flux-bin")
|
||||
replaces=("flux-cli")
|
||||
depends=("glibc")
|
||||
makedepends=('go>=1.20', 'kustomize>=5.0')
|
||||
optdepends=('bash-completion: auto-completion for flux in Bash',
|
||||
'zsh-completions: auto-completion for flux in ZSH')
|
||||
source=(
|
||||
"${pkgname}-${pkgver}.tar.gz::https://github.com/fluxcd/flux2/archive/v${_srcver}.tar.gz"
|
||||
)
|
||||
sha256sums=(
|
||||
${SHA256SUM}
|
||||
)
|
||||
|
||||
build() {
|
||||
cd "flux2-${_srcver}"
|
||||
export CGO_LDFLAGS="$LDFLAGS"
|
||||
export CGO_CFLAGS="$CFLAGS"
|
||||
export CGO_CXXFLAGS="$CXXFLAGS"
|
||||
export CGO_CPPFLAGS="$CPPFLAGS"
|
||||
export GOFLAGS="-buildmode=pie -trimpath -mod=readonly -modcacherw"
|
||||
make cmd/flux/.manifests.done
|
||||
go build -ldflags "-linkmode=external -X main.VERSION=${_srcver}" -o ${_srcname} ./cmd/flux
|
||||
}
|
||||
|
||||
check() {
|
||||
cd "flux2-${_srcver}"
|
||||
case $CARCH in
|
||||
aarch64)
|
||||
export ENVTEST_ARCH=arm64
|
||||
;;
|
||||
armv6h|armv7h)
|
||||
export ENVTEST_ARCH=arm
|
||||
;;
|
||||
esac
|
||||
make test
|
||||
}
|
||||
|
||||
package() {
|
||||
cd "flux2-${_srcver}"
|
||||
install -Dm755 ${_srcname} "${pkgdir}/usr/bin/${_srcname}"
|
||||
install -Dm644 LICENSE "${pkgdir}/usr/share/licenses/${pkgname}/LICENSE"
|
||||
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion bash | install -Dm644 /dev/stdin "${pkgdir}/usr/share/bash-completion/completions/${_srcname}"
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion fish | install -Dm644 /dev/stdin "${pkgdir}/usr/share/fish/vendor_completions.d/${_srcname}.fish"
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion zsh | install -Dm644 /dev/stdin "${pkgdir}/usr/share/zsh/site-functions/_${_srcname}"
|
||||
}
|
||||
54
.github/aur/flux-go/publish.sh
vendored
Executable file
54
.github/aur/flux-go/publish.sh
vendored
Executable file
@@ -0,0 +1,54 @@
|
||||
#!/usr/bin/env bash
|
||||
|
||||
set -e
|
||||
|
||||
WD=$(cd "$( dirname "${BASH_SOURCE[0]}" )" >/dev/null 2>&1 && pwd)
|
||||
PKGNAME=$(basename $WD)
|
||||
ROOT=${WD%/.github/aur/$PKGNAME}
|
||||
|
||||
LOCKFILE=/tmp/aur-$PKGNAME.lock
|
||||
exec 100>$LOCKFILE || exit 0
|
||||
flock -n 100 || exit 0
|
||||
trap "rm -f $LOCKFILE" EXIT
|
||||
|
||||
export VERSION=$1
|
||||
echo "Publishing to AUR as version ${VERSION}"
|
||||
|
||||
cd $WD
|
||||
|
||||
export GIT_SSH_COMMAND="ssh -o UserKnownHostsFile=/dev/null -o StrictHostKeyChecking=no"
|
||||
|
||||
eval $(ssh-agent -s)
|
||||
ssh-add <(echo "$AUR_BOT_SSH_PRIVATE_KEY")
|
||||
|
||||
GITDIR=$(mktemp -d /tmp/aur-$PKGNAME-XXX)
|
||||
trap "rm -rf $GITDIR" EXIT
|
||||
git clone aur@aur.archlinux.org:$PKGNAME $GITDIR 2>&1
|
||||
|
||||
CURRENT_PKGVER=$(cat $GITDIR/.SRCINFO | grep pkgver | awk '{ print $3 }')
|
||||
CURRENT_PKGREL=$(cat $GITDIR/.SRCINFO | grep pkgrel | awk '{ print $3 }')
|
||||
|
||||
# Transform pre-release to AUR compatible version format
|
||||
export PKGVER=${VERSION/-/}
|
||||
|
||||
if [[ "${CURRENT_PKGVER}" == "${PKGVER}" ]]; then
|
||||
export PKGREL=$((CURRENT_PKGREL+1))
|
||||
else
|
||||
export PKGREL=1
|
||||
fi
|
||||
|
||||
export SHA256SUM=$(curl -sL https://github.com/fluxcd/flux2/archive/v${VERSION}.tar.gz | sha256sum | awk '{ print $1 }')
|
||||
|
||||
envsubst '$VERSION $PKGVER $PKGREL $SHA256SUM' < .SRCINFO.template > $GITDIR/.SRCINFO
|
||||
envsubst '$VERSION $PKGVER $PKGREL $SHA256SUM' < PKGBUILD.template > $GITDIR/PKGBUILD
|
||||
|
||||
cd $GITDIR
|
||||
git config user.name "fluxcdbot"
|
||||
git config user.email "fluxcdbot@users.noreply.github.com"
|
||||
git add -A
|
||||
if [ -z "$(git status --porcelain)" ]; then
|
||||
echo "No changes."
|
||||
else
|
||||
git commit -m "Updated to version v${PKGVER} release ${PKGREL}"
|
||||
git push origin master
|
||||
fi
|
||||
18
.github/aur/flux-scm/.SRCINFO.template
vendored
Normal file
18
.github/aur/flux-scm/.SRCINFO.template
vendored
Normal file
@@ -0,0 +1,18 @@
|
||||
pkgbase = flux-scm
|
||||
pkgdesc = Open and extensible continuous delivery solution for Kubernetes
|
||||
pkgver = ${PKGVER}
|
||||
pkgrel = ${PKGREL}
|
||||
url = https://fluxcd.io/
|
||||
arch = x86_64
|
||||
arch = armv6h
|
||||
arch = armv7h
|
||||
arch = aarch64
|
||||
license = APACHE
|
||||
makedepends = go
|
||||
depends = glibc
|
||||
provides = flux-bin
|
||||
conflicts = flux-bin
|
||||
source = git+https://github.com/fluxcd/flux2.git
|
||||
md5sums = SKIP
|
||||
|
||||
pkgname = flux-scm
|
||||
1
.github/aur/flux-scm/.gitignore
vendored
Normal file
1
.github/aur/flux-scm/.gitignore
vendored
Normal file
@@ -0,0 +1 @@
|
||||
.pkg
|
||||
60
.github/aur/flux-scm/PKGBUILD.template
vendored
Normal file
60
.github/aur/flux-scm/PKGBUILD.template
vendored
Normal file
@@ -0,0 +1,60 @@
|
||||
# Maintainer: Aurel Canciu <aurelcanciu@gmail.com>
|
||||
# Maintainer: Hidde Beydals <hello@hidde.co>
|
||||
|
||||
pkgname=flux-scm
|
||||
pkgver=${PKGVER}
|
||||
pkgrel=${PKGREL}
|
||||
_srcname=flux
|
||||
pkgdesc="Open and extensible continuous delivery solution for Kubernetes"
|
||||
url="https://fluxcd.io/"
|
||||
arch=("x86_64" "armv6h" "armv7h" "aarch64")
|
||||
license=("APACHE")
|
||||
provides=("flux-bin")
|
||||
conflicts=("flux-bin")
|
||||
depends=("glibc")
|
||||
makedepends=('go>=1.20', 'kustomize>=5.0', 'git')
|
||||
optdepends=('bash-completion: auto-completion for flux in Bash',
|
||||
'zsh-completions: auto-completion for flux in ZSH')
|
||||
source=(
|
||||
"git+https://github.com/fluxcd/flux2.git"
|
||||
)
|
||||
md5sums=('SKIP')
|
||||
|
||||
pkgver() {
|
||||
cd "flux2"
|
||||
printf "r%s.%s" "$(git rev-list --count HEAD)" "$(git rev-parse --short HEAD)"
|
||||
}
|
||||
|
||||
build() {
|
||||
cd "flux2"
|
||||
export CGO_LDFLAGS="$LDFLAGS"
|
||||
export CGO_CFLAGS="$CFLAGS"
|
||||
export CGO_CXXFLAGS="$CXXFLAGS"
|
||||
export CGO_CPPFLAGS="$CPPFLAGS"
|
||||
export GOFLAGS="-buildmode=pie -trimpath -mod=readonly -modcacherw"
|
||||
make cmd/flux/.manifests.done
|
||||
go build -ldflags "-linkmode=external -X main.VERSION=${pkgver}" -o ${_srcname} ./cmd/flux
|
||||
}
|
||||
|
||||
check() {
|
||||
cd "flux2"
|
||||
case $CARCH in
|
||||
aarch64)
|
||||
export ENVTEST_ARCH=arm64
|
||||
;;
|
||||
armv6h|armv7h)
|
||||
export ENVTEST_ARCH=arm
|
||||
;;
|
||||
esac
|
||||
make test
|
||||
}
|
||||
|
||||
package() {
|
||||
cd "flux2"
|
||||
install -Dm755 ${_srcname} "${pkgdir}/usr/bin/${_srcname}"
|
||||
install -Dm644 LICENSE "${pkgdir}/usr/share/licenses/${pkgname}/LICENSE"
|
||||
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion bash | install -Dm644 /dev/stdin "${pkgdir}/usr/share/bash-completion/completions/${_srcname}"
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion fish | install -Dm644 /dev/stdin "${pkgdir}/usr/share/fish/vendor_completions.d/${_srcname}.fish"
|
||||
"${pkgdir}/usr/bin/${_srcname}" completion zsh | install -Dm644 /dev/stdin "${pkgdir}/usr/share/zsh/site-functions/_${_srcname}"
|
||||
}
|
||||
52
.github/aur/flux-scm/publish.sh
vendored
Executable file
52
.github/aur/flux-scm/publish.sh
vendored
Executable file
@@ -0,0 +1,52 @@
|
||||
#!/usr/bin/env bash
|
||||
|
||||
set -e
|
||||
|
||||
WD=$(cd "$( dirname "${BASH_SOURCE[0]}" )" >/dev/null 2>&1 && pwd)
|
||||
PKGNAME=$(basename $WD)
|
||||
ROOT=${WD%/.github/aur/$PKGNAME}
|
||||
|
||||
LOCKFILE=/tmp/aur-$PKGNAME.lock
|
||||
exec 100>$LOCKFILE || exit 0
|
||||
flock -n 100 || exit 0
|
||||
trap "rm -f $LOCKFILE" EXIT
|
||||
|
||||
export VERSION=$1
|
||||
echo "Publishing to AUR as version ${VERSION}"
|
||||
|
||||
cd $WD
|
||||
|
||||
export GIT_SSH_COMMAND="ssh -o UserKnownHostsFile=/dev/null -o StrictHostKeyChecking=no"
|
||||
|
||||
eval $(ssh-agent -s)
|
||||
ssh-add <(echo "$AUR_BOT_SSH_PRIVATE_KEY")
|
||||
|
||||
GITDIR=$(mktemp -d /tmp/aur-$PKGNAME-XXX)
|
||||
trap "rm -rf $GITDIR" EXIT
|
||||
git clone aur@aur.archlinux.org:$PKGNAME $GITDIR 2>&1
|
||||
|
||||
CURRENT_PKGVER=$(cat $GITDIR/.SRCINFO | grep pkgver | awk '{ print $3 }')
|
||||
CURRENT_PKGREL=$(cat $GITDIR/.SRCINFO | grep pkgrel | awk '{ print $3 }')
|
||||
|
||||
# Transform pre-release to AUR compatible version format
|
||||
export PKGVER=${VERSION/-/}
|
||||
|
||||
if [[ "${CURRENT_PKGVER}" == "${PKGVER}" ]]; then
|
||||
export PKGREL=$((CURRENT_PKGREL+1))
|
||||
else
|
||||
export PKGREL=1
|
||||
fi
|
||||
|
||||
envsubst '$PKGVER $PKGREL' < .SRCINFO.template > $GITDIR/.SRCINFO
|
||||
envsubst '$PKGVER $PKGREL' < PKGBUILD.template > $GITDIR/PKGBUILD
|
||||
|
||||
cd $GITDIR
|
||||
git config user.name "fluxcdbot"
|
||||
git config user.email "fluxcdbot@users.noreply.github.com"
|
||||
git add -A
|
||||
if [ -z "$(git status --porcelain)" ]; then
|
||||
echo "No changes."
|
||||
else
|
||||
git commit -m "Updated to version v${PKGVER} release ${PKGREL}"
|
||||
git push origin master
|
||||
fi
|
||||
16
.github/dependabot.yml
vendored
Normal file
16
.github/dependabot.yml
vendored
Normal file
@@ -0,0 +1,16 @@
|
||||
version: 2
|
||||
|
||||
updates:
|
||||
- package-ecosystem: "github-actions"
|
||||
directory: "/"
|
||||
labels: ["area/ci", "dependencies"]
|
||||
groups:
|
||||
# Group all updates together, so that they are all applied in a single PR.
|
||||
# Grouped updates are currently in beta and is subject to change.
|
||||
# xref: https://docs.github.com/en/code-security/dependabot/dependabot-version-updates/configuration-options-for-the-dependabot.yml-file#groups
|
||||
ci:
|
||||
patterns:
|
||||
- "*"
|
||||
schedule:
|
||||
# By default, this will be on a monday.
|
||||
interval: "weekly"
|
||||
5
.github/kind/config.yaml
vendored
Normal file
5
.github/kind/config.yaml
vendored
Normal file
@@ -0,0 +1,5 @@
|
||||
kind: Cluster
|
||||
apiVersion: kind.x-k8s.io/v1alpha4
|
||||
networking:
|
||||
disableDefaultCNI: true # disable kindnet
|
||||
podSubnet: 192.168.0.0/16 # set to Calico's default subnet
|
||||
49
.github/labels.yaml
vendored
Normal file
49
.github/labels.yaml
vendored
Normal file
@@ -0,0 +1,49 @@
|
||||
# Configuration file to declaratively configure labels
|
||||
# Ref: https://github.com/EndBug/label-sync#Config-files
|
||||
|
||||
- name: area/bootstrap
|
||||
description: Bootstrap related issues and pull requests
|
||||
color: '#86efc9'
|
||||
- name: area/install
|
||||
description: Install and uninstall related issues and pull requests
|
||||
color: '#86efc9'
|
||||
- name: area/diff
|
||||
description: Diff related issues and pull requests
|
||||
color: '#BA4192'
|
||||
- name: area/bucket
|
||||
description: Bucket related issues and pull requests
|
||||
color: '#00b140'
|
||||
- name: area/git
|
||||
description: Git related issues and pull requests
|
||||
color: '#863faf'
|
||||
- name: area/oci
|
||||
description: OCI related issues and pull requests
|
||||
color: '#c739ff'
|
||||
- name: area/kustomization
|
||||
description: Kustomization related issues and pull requests
|
||||
color: '#00e54d'
|
||||
- name: area/helm
|
||||
description: Helm related issues and pull requests
|
||||
color: '#1673b6'
|
||||
- name: area/image-automation
|
||||
description: Automated image updates related issues and pull requests
|
||||
color: '#c5def5'
|
||||
- name: area/monitoring
|
||||
description: Monitoring related issues and pull requests
|
||||
color: '#dd75ae'
|
||||
- name: area/multi-tenancy
|
||||
description: Multi-tenancy related issues and pull requests
|
||||
color: '#72CDBD'
|
||||
- name: area/notification
|
||||
description: Notification API related issues and pull requests
|
||||
color: '#434ec1'
|
||||
- name: area/source
|
||||
description: Source API related issues and pull requests
|
||||
color: '#863faf'
|
||||
- name: area/rfc
|
||||
description: Feature request proposals in the RFC format
|
||||
color: '#D621C3'
|
||||
aliases: ['area/RFC']
|
||||
- name: backport:release/v2.0.x
|
||||
description: To be backported to release/v2.0.x
|
||||
color: '#ffd700'
|
||||
80
.github/runners/README.md
vendored
Normal file
80
.github/runners/README.md
vendored
Normal file
@@ -0,0 +1,80 @@
|
||||
# Flux ARM64 GitHub runners
|
||||
|
||||
The Flux ARM64 end-to-end tests run on Equinix Metal instances provisioned with Docker and GitHub self-hosted runners.
|
||||
|
||||
## Current instances
|
||||
|
||||
| Repository | Runner | Instance | Location |
|
||||
|-----------------------------|------------------|------------------------|---------------|
|
||||
| flux2 | equinix-arm-dc-1 | flux-equinix-arm-dc-01 | Washington DC |
|
||||
| flux2 | equinix-arm-dc-2 | flux-equinix-arm-dc-01 | Washington DC |
|
||||
| flux2 | equinix-arm-da-1 | flux-equinix-arm-da-01 | Dallas |
|
||||
| flux2 | equinix-arm-da-2 | flux-equinix-arm-da-01 | Dallas |
|
||||
| source-controller | equinix-arm-dc-1 | flux-equinix-arm-dc-01 | Washington DC |
|
||||
| source-controller | equinix-arm-da-1 | flux-equinix-arm-da-01 | Dallas |
|
||||
| image-automation-controller | equinix-arm-dc-1 | flux-equinix-arm-dc-01 | Washington DC |
|
||||
| image-automation-controller | equinix-arm-da-1 | flux-equinix-arm-da-01 | Dallas |
|
||||
|
||||
Instance spec:
|
||||
- Ampere Altra Q80-30 80-core processor @ 2.8GHz
|
||||
- 2 x 960GB NVME
|
||||
- 256GB RAM
|
||||
- 2 x 25Gbps
|
||||
|
||||
## Instance setup
|
||||
|
||||
In order to add a new runner to the GitHub Actions pool,
|
||||
first create a server on Equinix with the following configuration:
|
||||
- Type: `c3.large.arm64`
|
||||
- OS: `Ubuntu 22.04 LTS`
|
||||
|
||||
### Install prerequisites
|
||||
|
||||
- SSH into a newly created instance
|
||||
```shell
|
||||
ssh root@<instance-public-IP>
|
||||
```
|
||||
|
||||
- Create the ubuntu user
|
||||
```shell
|
||||
adduser ubuntu
|
||||
usermod -aG sudo ubuntu
|
||||
su - ubuntu
|
||||
```
|
||||
|
||||
- Create the prerequisites dir
|
||||
```shell
|
||||
mkdir -p prereq && cd prereq
|
||||
```
|
||||
|
||||
- Download the prerequisites script
|
||||
```shell
|
||||
curl -sL https://raw.githubusercontent.com/fluxcd/flux2/main/.github/runners/prereq.sh > prereq.sh \
|
||||
&& chmod +x ./prereq.sh
|
||||
```
|
||||
|
||||
- Install the prerequisites
|
||||
```shell
|
||||
sudo ./prereq.sh
|
||||
```
|
||||
|
||||
### Install runners
|
||||
|
||||
- Retrieve the GitHub runner token from the repository [settings page](https://github.com/fluxcd/flux2/settings/actions/runners/new?arch=arm64&os=linux)
|
||||
|
||||
- Create two directories `flux2-01`, `flux2-02`
|
||||
|
||||
- In each dir run:
|
||||
```shell
|
||||
curl -sL https://raw.githubusercontent.com/fluxcd/flux2/main/.github/runners/runner-setup.sh > runner-setup.sh \
|
||||
&& chmod +x ./runner-setup.sh
|
||||
|
||||
./runner-setup.sh equinix-arm-<NUMBER> <TOKEN> <REPO>
|
||||
```
|
||||
|
||||
- Reboot the instance
|
||||
```shell
|
||||
sudo reboot
|
||||
```
|
||||
|
||||
- Navigate to the GitHub repository [runners page](https://github.com/fluxcd/flux2/settings/actions/runners) and check the runner status
|
||||
72
.github/runners/prereq.sh
vendored
Executable file
72
.github/runners/prereq.sh
vendored
Executable file
@@ -0,0 +1,72 @@
|
||||
#!/usr/bin/env bash
|
||||
|
||||
# Copyright 2021 The Flux authors. All rights reserved.
|
||||
#
|
||||
# Licensed under the Apache License, Version 2.0 (the "License");
|
||||
# you may not use this file except in compliance with the License.
|
||||
# You may obtain a copy of the License at
|
||||
#
|
||||
# http://www.apache.org/licenses/LICENSE-2.0
|
||||
#
|
||||
# Unless required by applicable law or agreed to in writing, software
|
||||
# distributed under the License is distributed on an "AS IS" BASIS,
|
||||
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
# See the License for the specific language governing permissions and
|
||||
# limitations under the License.
|
||||
|
||||
# This script installs the prerequisites for running Flux end-to-end tests with Docker and GitHub self-hosted runners.
|
||||
|
||||
set -eu
|
||||
|
||||
KIND_VERSION=0.17.0
|
||||
KUBECTL_VERSION=1.24.0
|
||||
KUSTOMIZE_VERSION=4.5.7
|
||||
HELM_VERSION=3.10.1
|
||||
GITHUB_RUNNER_VERSION=2.298.2
|
||||
PACKAGES="apt-transport-https ca-certificates software-properties-common build-essential libssl-dev gnupg lsb-release jq pkg-config"
|
||||
|
||||
# install prerequisites
|
||||
apt-get update \
|
||||
&& apt-get install -y -q ${PACKAGES} \
|
||||
&& apt-get clean \
|
||||
&& rm -rf /var/lib/apt/lists/*
|
||||
|
||||
# fix Kubernetes DNS resolution
|
||||
rm /etc/resolv.conf
|
||||
cat "/run/systemd/resolve/stub-resolv.conf" | sed '/search/d' > /etc/resolv.conf
|
||||
|
||||
# install docker
|
||||
curl -fsSL https://get.docker.com -o get-docker.sh \
|
||||
&& chmod +x get-docker.sh
|
||||
./get-docker.sh
|
||||
systemctl enable docker.service
|
||||
systemctl enable containerd.service
|
||||
usermod -aG docker ubuntu
|
||||
|
||||
# install kind
|
||||
curl -Lo ./kind https://kind.sigs.k8s.io/dl/v${KIND_VERSION}/kind-linux-arm64
|
||||
install -o root -g root -m 0755 kind /usr/local/bin/kind
|
||||
|
||||
# install kubectl
|
||||
curl -LO "https://dl.k8s.io/release/v${KUBECTL_VERSION}/bin/linux/arm64/kubectl"
|
||||
install -o root -g root -m 0755 kubectl /usr/local/bin/kubectl
|
||||
|
||||
# install kustomize
|
||||
curl -Lo ./kustomize.tar.gz https://github.com/kubernetes-sigs/kustomize/releases/download/kustomize%2Fv${KUSTOMIZE_VERSION}/kustomize_v${KUSTOMIZE_VERSION}_linux_arm64.tar.gz \
|
||||
&& tar -zxvf kustomize.tar.gz \
|
||||
&& rm kustomize.tar.gz
|
||||
install -o root -g root -m 0755 kustomize /usr/local/bin/kustomize
|
||||
|
||||
# install helm
|
||||
curl -Lo ./helm.tar.gz https://get.helm.sh/helm-v${HELM_VERSION}-linux-arm64.tar.gz \
|
||||
&& tar -zxvf helm.tar.gz \
|
||||
&& rm helm.tar.gz
|
||||
install -o root -g root -m 0755 linux-arm64/helm /usr/local/bin/helm
|
||||
|
||||
# download runner
|
||||
curl -o actions-runner-linux-arm64.tar.gz -L https://github.com/actions/runner/releases/download/v${GITHUB_RUNNER_VERSION}/actions-runner-linux-arm64-${GITHUB_RUNNER_VERSION}.tar.gz \
|
||||
&& tar xzf actions-runner-linux-arm64.tar.gz \
|
||||
&& rm actions-runner-linux-arm64.tar.gz
|
||||
|
||||
# install runner dependencies
|
||||
./bin/installdependencies.sh
|
||||
37
.github/runners/runner-setup.sh
vendored
Executable file
37
.github/runners/runner-setup.sh
vendored
Executable file
@@ -0,0 +1,37 @@
|
||||
#!/usr/bin/env bash
|
||||
|
||||
# Copyright 2021 The Flux authors. All rights reserved.
|
||||
#
|
||||
# Licensed under the Apache License, Version 2.0 (the "License");
|
||||
# you may not use this file except in compliance with the License.
|
||||
# You may obtain a copy of the License at
|
||||
#
|
||||
# http://www.apache.org/licenses/LICENSE-2.0
|
||||
#
|
||||
# Unless required by applicable law or agreed to in writing, software
|
||||
# distributed under the License is distributed on an "AS IS" BASIS,
|
||||
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
# See the License for the specific language governing permissions and
|
||||
# limitations under the License.
|
||||
|
||||
# This script installs a GitHub self-hosted ARM64 runner for running Flux end-to-end tests.
|
||||
|
||||
set -eu
|
||||
|
||||
RUNNER_NAME=$1
|
||||
REPOSITORY_TOKEN=$2
|
||||
REPOSITORY_URL=${3:-https://github.com/fluxcd/flux2}
|
||||
|
||||
GITHUB_RUNNER_VERSION=2.298.2
|
||||
|
||||
# download runner
|
||||
curl -o actions-runner-linux-arm64.tar.gz -L https://github.com/actions/runner/releases/download/v${GITHUB_RUNNER_VERSION}/actions-runner-linux-arm64-${GITHUB_RUNNER_VERSION}.tar.gz \
|
||||
&& tar xzf actions-runner-linux-arm64.tar.gz \
|
||||
&& rm actions-runner-linux-arm64.tar.gz
|
||||
|
||||
# register runner with GitHub
|
||||
./config.sh --unattended --url ${REPOSITORY_URL} --token ${REPOSITORY_TOKEN} --name ${RUNNER_NAME}
|
||||
|
||||
# start runner
|
||||
sudo ./svc.sh install
|
||||
sudo ./svc.sh start
|
||||
50
.github/workflows/README.md
vendored
Normal file
50
.github/workflows/README.md
vendored
Normal file
@@ -0,0 +1,50 @@
|
||||
# Flux GitHub Workflows
|
||||
|
||||
## End-to-end Testing
|
||||
|
||||
The e2e workflows run a series of tests to ensure that the Flux CLI and
|
||||
the GitOps Toolkit controllers work well all together.
|
||||
The tests are written in Go, Bash, Make and Terraform.
|
||||
|
||||
| Workflow | Jobs | Runner | Role |
|
||||
|--------------------|----------------------|----------------|-----------------------------------------------|
|
||||
| e2e.yaml | e2e-amd64-kubernetes | GitHub Ubuntu | integration testing with Kubernetes Kind<br/> |
|
||||
| e2e-arm64.yaml | e2e-arm64-kubernetes | Equinix Ubuntu | integration testing with Kubernetes Kind<br/> |
|
||||
| e2e-bootstrap.yaml | e2e-boostrap-github | GitHub Ubuntu | integration testing with GitHub API<br/> |
|
||||
| e2e-azure.yaml | e2e-amd64-aks | GitHub Ubuntu | integration testing with Azure API<br/> |
|
||||
| scan.yaml | scan-fossa | GitHub Ubuntu | license scanning<br/> |
|
||||
| scan.yaml | scan-snyk | GitHub Ubuntu | vulnerability scanning<br/> |
|
||||
| scan.yaml | scan-codeql | GitHub Ubuntu | vulnerability scanning<br/> |
|
||||
|
||||
## Components Update
|
||||
|
||||
The components update workflow scans the GitOps Toolkit controller repositories for new releases,
|
||||
amd when it finds a new controller version, the workflow performs the following steps:
|
||||
- Updates the controller API package version in `go.mod`.
|
||||
- Patches the controller CRDs version in the `manifests/crds` overlay.
|
||||
- Patches the controller Deployment version in `manifests/bases` overlay.
|
||||
- Opens a Pull Request against the `main` branch.
|
||||
- Triggers the e2e test suite to run for the opened PR.
|
||||
|
||||
|
||||
| Workflow | Jobs | Runner | Role |
|
||||
|-------------|-------------------|---------------|-----------------------------------------------------|
|
||||
| update.yaml | update-components | GitHub Ubuntu | update the GitOps Toolkit APIs and controllers<br/> |
|
||||
|
||||
## Release
|
||||
|
||||
The release workflow is triggered by a semver Git tag and performs the following steps:
|
||||
- Generates the Flux install manifests (YAML).
|
||||
- Generates the OpenAPI validation schemas for the GitOps Toolkit CRDs (JSON).
|
||||
- Generates a Software Bill of Materials (SPDX JSON).
|
||||
- Builds the Flux CLI binaries and the multi-arch container images.
|
||||
- Pushes the container images to GitHub Container Registry and DockerHub.
|
||||
- Signs the sbom, the binaries checksum and the container images with Cosign and GitHub OIDC.
|
||||
- Uploads the sbom, binaries, checksums and install manifests to GitHub Releases.
|
||||
- Pushes the install manifests as OCI artifacts to GitHub Container Registry and DockerHub.
|
||||
- Signs the OCI artifacts with Cosign and GitHub OIDC.
|
||||
|
||||
| Workflow | Jobs | Runner | Role |
|
||||
|--------------|------------------------|---------------|------------------------------------------------------|
|
||||
| release.yaml | release-flux-cli | GitHub Ubuntu | build, push and sign the CLI release artifacts<br/> |
|
||||
| release.yaml | release-flux-manifests | GitHub Ubuntu | build, push and sign the Flux install manifests<br/> |
|
||||
31
.github/workflows/backport.yaml
vendored
Normal file
31
.github/workflows/backport.yaml
vendored
Normal file
@@ -0,0 +1,31 @@
|
||||
name: backport
|
||||
|
||||
on:
|
||||
pull_request_target:
|
||||
types: [closed, labeled]
|
||||
|
||||
jobs:
|
||||
pull-request:
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
contents: write
|
||||
pull-requests: write
|
||||
if: github.event.pull_request.state == 'closed' && github.event.pull_request.merged && (github.event_name != 'labeled' || startsWith('backport:', github.event.label.name))
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
with:
|
||||
ref: ${{ github.event.pull_request.head.sha }}
|
||||
- name: Create backport PRs
|
||||
uses: korthout/backport-action@bf5fdd624b35f95d5b85991a728bd5744e8c6cf2 # v1.3.1
|
||||
# xref: https://github.com/korthout/backport-action#inputs
|
||||
with:
|
||||
# Use token to allow workflows to be triggered for the created PR
|
||||
github_token: ${{ secrets.BOT_GITHUB_TOKEN }}
|
||||
# Match labels with a pattern `backport:<target-branch>`
|
||||
label_pattern: '^backport:([^ ]+)$'
|
||||
# A bit shorter pull-request title than the default
|
||||
pull_title: '[${target_branch}] ${pull_title}'
|
||||
# Simpler PR description than default
|
||||
pull_description: |-
|
||||
Automated backport to `${target_branch}`, triggered by a label in #${pull_number}.
|
||||
105
.github/workflows/e2e-arm64.yaml
vendored
Normal file
105
.github/workflows/e2e-arm64.yaml
vendored
Normal file
@@ -0,0 +1,105 @@
|
||||
name: e2e-arm64
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches: [ 'main', 'update-components', 'e2e-*', 'release/**' ]
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
e2e-arm64-kubernetes:
|
||||
# Hosted on Equinix
|
||||
# Docs: https://github.com/fluxcd/flux2/tree/main/.github/runners
|
||||
runs-on: [self-hosted, Linux, ARM64, equinix]
|
||||
strategy:
|
||||
matrix:
|
||||
# Keep this list up-to-date with https://endoflife.date/kubernetes
|
||||
# Check which versions are available on DockerHub with 'crane ls kindest/node'
|
||||
KUBERNETES_VERSION: [ 1.25.8, 1.26.3, 1.27.3 ]
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Prepare
|
||||
id: prep
|
||||
run: |
|
||||
ID=${GITHUB_SHA:0:7}-${{ matrix.KUBERNETES_VERSION }}-$(date +%s)
|
||||
echo "CLUSTER=arm64-${ID}" >> $GITHUB_OUTPUT
|
||||
- name: Build
|
||||
run: |
|
||||
make build
|
||||
- name: Setup Kubernetes Kind
|
||||
run: |
|
||||
kind create cluster \
|
||||
--wait 5m \
|
||||
--name ${{ steps.prep.outputs.CLUSTER }} \
|
||||
--kubeconfig=/tmp/${{ steps.prep.outputs.CLUSTER }} \
|
||||
--image=kindest/node:v${{ matrix.KUBERNETES_VERSION }}
|
||||
- name: Run e2e tests
|
||||
run: TEST_KUBECONFIG=/tmp/${{ steps.prep.outputs.CLUSTER }} make e2e
|
||||
- name: Run multi-tenancy tests
|
||||
env:
|
||||
KUBECONFIG: /tmp/${{ steps.prep.outputs.CLUSTER }}
|
||||
run: |
|
||||
./bin/flux install
|
||||
./bin/flux create source git flux-system \
|
||||
--interval=15m \
|
||||
--url=https://github.com/fluxcd/flux2-multi-tenancy \
|
||||
--branch=main \
|
||||
--ignore-paths="./clusters/**/flux-system/"
|
||||
./bin/flux create kustomization flux-system \
|
||||
--interval=15m \
|
||||
--source=flux-system \
|
||||
--path=./clusters/staging
|
||||
kubectl -n flux-system wait kustomization/tenants --for=condition=ready --timeout=5m
|
||||
kubectl -n apps wait kustomization/dev-team --for=condition=ready --timeout=1m
|
||||
kubectl -n apps wait helmrelease/podinfo --for=condition=ready --timeout=1m
|
||||
- name: Run monitoring tests
|
||||
# Keep this test in sync with https://fluxcd.io/flux/guides/monitoring/
|
||||
env:
|
||||
KUBECONFIG: /tmp/${{ steps.prep.outputs.CLUSTER }}
|
||||
run: |
|
||||
./bin/flux create source git flux-monitoring \
|
||||
--interval=30m \
|
||||
--url=https://github.com/fluxcd/flux2 \
|
||||
--branch=${GITHUB_REF#refs/heads/}
|
||||
./bin/flux create kustomization kube-prometheus-stack \
|
||||
--interval=1h \
|
||||
--prune \
|
||||
--source=flux-monitoring \
|
||||
--path="./manifests/monitoring/kube-prometheus-stack" \
|
||||
--health-check-timeout=5m \
|
||||
--wait
|
||||
./bin/flux create kustomization monitoring-config \
|
||||
--depends-on=kube-prometheus-stack \
|
||||
--interval=1h \
|
||||
--prune=true \
|
||||
--source=flux-monitoring \
|
||||
--path="./manifests/monitoring/monitoring-config" \
|
||||
--health-check-timeout=1m \
|
||||
--wait
|
||||
kubectl -n flux-system wait kustomization/kube-prometheus-stack --for=condition=ready --timeout=5m
|
||||
kubectl -n flux-system wait kustomization/monitoring-config --for=condition=ready --timeout=5m
|
||||
kubectl -n monitoring wait helmrelease/kube-prometheus-stack --for=condition=ready --timeout=1m
|
||||
- name: Debug failure
|
||||
if: failure()
|
||||
env:
|
||||
KUBECONFIG: /tmp/${{ steps.prep.outputs.CLUSTER }}
|
||||
run: |
|
||||
kubectl -n flux-system get all
|
||||
kubectl -n flux-system describe po
|
||||
kubectl -n flux-system logs deploy/source-controller
|
||||
kubectl -n flux-system logs deploy/kustomize-controller
|
||||
- name: Cleanup
|
||||
if: always()
|
||||
run: |
|
||||
kind delete cluster --name ${{ steps.prep.outputs.CLUSTER }}
|
||||
rm /tmp/${{ steps.prep.outputs.CLUSTER }}
|
||||
68
.github/workflows/e2e-azure.yaml
vendored
Normal file
68
.github/workflows/e2e-azure.yaml
vendored
Normal file
@@ -0,0 +1,68 @@
|
||||
name: e2e-azure
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
schedule:
|
||||
- cron: '0 6 * * *'
|
||||
push:
|
||||
branches:
|
||||
- main
|
||||
paths:
|
||||
- 'tests/**'
|
||||
- '.github/workflows/e2e-azure.yaml'
|
||||
pull_request:
|
||||
branches:
|
||||
- main
|
||||
paths:
|
||||
- 'tests/**'
|
||||
- '.github/workflows/e2e-azure.yaml'
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
e2e-amd64-aks:
|
||||
runs-on: ubuntu-22.04
|
||||
if: (github.event_name != 'pull_request' || github.event.pull_request.head.repo.full_name == github.repository) && github.actor != 'dependabot[bot]'
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Setup Flux CLI
|
||||
run: |
|
||||
make build
|
||||
mkdir -p $HOME/.local/bin
|
||||
mv ./bin/flux $HOME/.local/bin
|
||||
- name: Setup SOPS
|
||||
run: |
|
||||
wget https://github.com/mozilla/sops/releases/download/v3.7.1/sops-v3.7.1.linux
|
||||
chmod +x sops-v3.7.1.linux
|
||||
mkdir -p $HOME/.local/bin
|
||||
mv sops-v3.7.1.linux $HOME/.local/bin/sops
|
||||
- name: Setup Terraform
|
||||
uses: hashicorp/setup-terraform@633666f66e0061ca3b725c73b2ec20cd13a8fdd1 # v2
|
||||
with:
|
||||
terraform_version: 1.2.8
|
||||
terraform_wrapper: false
|
||||
- name: Setup Azure CLI
|
||||
run: |
|
||||
curl -sL https://aka.ms/InstallAzureCLIDeb | sudo bash
|
||||
- name: Run Azure e2e tests
|
||||
env:
|
||||
ARM_CLIENT_ID: ${{ secrets.ARM_CLIENT_ID }}
|
||||
ARM_CLIENT_SECRET: ${{ secrets.ARM_CLIENT_SECRET }}
|
||||
ARM_SUBSCRIPTION_ID: ${{ secrets.ARM_SUBSCRIPTION_ID }}
|
||||
ARM_TENANT_ID: ${{ secrets.ARM_TENANT_ID }}
|
||||
run: |
|
||||
echo $HOME
|
||||
echo $PATH
|
||||
ls $HOME/.local/bin
|
||||
az login --service-principal -u ${ARM_CLIENT_ID} -p ${ARM_CLIENT_SECRET} -t ${ARM_TENANT_ID}
|
||||
cd ./tests/azure
|
||||
go test -v -coverprofile cover.out -timeout 60m .
|
||||
137
.github/workflows/e2e-bootstrap.yaml
vendored
Normal file
137
.github/workflows/e2e-bootstrap.yaml
vendored
Normal file
@@ -0,0 +1,137 @@
|
||||
name: e2e-bootstrap
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches: [ 'main', 'release/**' ]
|
||||
pull_request:
|
||||
branches: [ 'main', 'release/**' ]
|
||||
paths-ignore: [ 'docs/**', 'rfcs/**' ]
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
e2e-boostrap-github:
|
||||
runs-on: ubuntu-latest
|
||||
if: (github.event_name != 'pull_request' || github.event.pull_request.head.repo.full_name == github.repository) && github.actor != 'dependabot[bot]'
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Setup Kubernetes
|
||||
uses: helm/kind-action@dda0770415bac9fc20092cacbc54aa298604d140 # v1.8.0
|
||||
with:
|
||||
version: v0.20.0
|
||||
cluster_name: kind
|
||||
# The versions below should target the newest Kubernetes version
|
||||
# Keep this up-to-date with https://endoflife.date/kubernetes
|
||||
node_image: kindest/node:v1.27.3@sha256:3966ac761ae0136263ffdb6cfd4db23ef8a83cba8a463690e98317add2c9ba72
|
||||
kubectl_version: v1.27.3
|
||||
- name: Setup Kustomize
|
||||
uses: fluxcd/pkg/actions/kustomize@main
|
||||
- name: Build
|
||||
run: |
|
||||
make cmd/flux/.manifests.done
|
||||
go build -o /tmp/flux ./cmd/flux
|
||||
- name: Set outputs
|
||||
id: vars
|
||||
run: |
|
||||
REPOSITORY_NAME=${{ github.event.repository.name }}
|
||||
BRANCH_NAME=${GITHUB_REF##*/}
|
||||
COMMIT_SHA=$(git rev-parse HEAD)
|
||||
PSEUDO_RAND_SUFFIX=$(echo "${BRANCH_NAME}-${COMMIT_SHA}" | shasum | awk '{print $1}')
|
||||
TEST_REPO_NAME="${REPOSITORY_NAME}-${PSEUDO_RAND_SUFFIX}"
|
||||
echo "test_repo_name=$TEST_REPO_NAME" >> $GITHUB_OUTPUT
|
||||
- name: bootstrap init
|
||||
run: |
|
||||
/tmp/flux bootstrap github --manifests ./manifests/install/ \
|
||||
--owner=fluxcd-testing \
|
||||
--repository=${{ steps.vars.outputs.test_repo_name }} \
|
||||
--branch=main \
|
||||
--path=test-cluster \
|
||||
--team=team-z
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITPROVIDER_BOT_TOKEN }}
|
||||
- name: bootstrap no-op
|
||||
run: |
|
||||
/tmp/flux bootstrap github --manifests ./manifests/install/ \
|
||||
--owner=fluxcd-testing \
|
||||
--repository=${{ steps.vars.outputs.test_repo_name }} \
|
||||
--branch=main \
|
||||
--path=test-cluster \
|
||||
--team=team-z
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITPROVIDER_BOT_TOKEN }}
|
||||
- name: bootstrap customize
|
||||
run: |
|
||||
make setup-bootstrap-patch
|
||||
/tmp/flux bootstrap github --manifests ./manifests/install/ \
|
||||
--owner=fluxcd-testing \
|
||||
--repository=${{ steps.vars.outputs.test_repo_name }} \
|
||||
--branch=main \
|
||||
--path=test-cluster \
|
||||
--team=team-z
|
||||
if [ $(kubectl get deployments.apps source-controller -o jsonpath='{.spec.template.spec.securityContext.runAsUser}') != "10000" ]; then
|
||||
echo "Bootstrap not customized as controller is not running as user 10000" && exit 1
|
||||
fi
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITPROVIDER_BOT_TOKEN }}
|
||||
GITHUB_REPO_NAME: ${{ steps.vars.outputs.test_repo_name }}
|
||||
GITHUB_ORG_NAME: fluxcd-testing
|
||||
- name: uninstall
|
||||
run: |
|
||||
/tmp/flux uninstall -s --keep-namespace
|
||||
kubectl delete ns flux-system --timeout=10m --wait=true
|
||||
- name: test image automation
|
||||
run: |
|
||||
make setup-image-automation
|
||||
/tmp/flux bootstrap github --manifests ./manifests/install/ \
|
||||
--owner=fluxcd-testing \
|
||||
--repository=${{ steps.vars.outputs.test_repo_name }} \
|
||||
--branch=main \
|
||||
--path=test-cluster \
|
||||
--read-write-key
|
||||
/tmp/flux reconcile image repository podinfo
|
||||
/tmp/flux get images all
|
||||
|
||||
retries=10
|
||||
count=0
|
||||
ok=false
|
||||
until ${ok}; do
|
||||
/tmp/flux get image update flux-system | grep 'commit' && ok=true || ok=false
|
||||
count=$(($count + 1))
|
||||
if [[ ${count} -eq ${retries} ]]; then
|
||||
echo "No more retries left"
|
||||
exit 1
|
||||
fi
|
||||
sleep 6
|
||||
/tmp/flux reconcile image update flux-system
|
||||
done
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITPROVIDER_BOT_TOKEN }}
|
||||
GITHUB_REPO_NAME: ${{ steps.vars.outputs.test_repo_name }}
|
||||
GITHUB_ORG_NAME: fluxcd-testing
|
||||
- name: delete repository
|
||||
if: ${{ always() }}
|
||||
run: |
|
||||
curl \
|
||||
-X DELETE \
|
||||
-H "Accept: application/vnd.github.v3+json" \
|
||||
-H "Authorization: token ${GITHUB_TOKEN}" \
|
||||
--fail --silent \
|
||||
https://api.github.com/repos/fluxcd-testing/${{ steps.vars.outputs.test_repo_name }}
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITPROVIDER_BOT_TOKEN }}
|
||||
- name: Debug failure
|
||||
if: failure()
|
||||
run: |
|
||||
kubectl -n flux-system get all
|
||||
kubectl -n flux-system logs deploy/source-controller
|
||||
kubectl -n flux-system logs deploy/kustomize-controller
|
||||
252
.github/workflows/e2e.yaml
vendored
252
.github/workflows/e2e.yaml
vendored
@@ -1,104 +1,244 @@
|
||||
name: e2e
|
||||
|
||||
on:
|
||||
pull_request:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches:
|
||||
- master
|
||||
branches: [ 'main', 'release/**' ]
|
||||
pull_request:
|
||||
branches: [ 'main', 'release/**' ]
|
||||
paths-ignore: [ 'docs/**', 'rfcs/**' ]
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
kind:
|
||||
e2e-amd64-kubernetes:
|
||||
runs-on: ubuntu-latest
|
||||
services:
|
||||
registry:
|
||||
image: registry:2
|
||||
ports:
|
||||
- 5000:5000
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v2
|
||||
- name: Restore Go cache
|
||||
uses: actions/cache@v1
|
||||
with:
|
||||
path: ~/go/pkg/mod
|
||||
key: ${{ runner.os }}-go-${{ hashFiles('**/go.sum') }}
|
||||
restore-keys: |
|
||||
${{ runner.os }}-go-
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@v2-beta
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.14.x
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Setup Kubernetes
|
||||
uses: engineerd/setup-kind@v0.3.0
|
||||
uses: helm/kind-action@dda0770415bac9fc20092cacbc54aa298604d140 # v1.8.0
|
||||
with:
|
||||
version: v0.20.0
|
||||
cluster_name: kind
|
||||
config: .github/kind/config.yaml # disable KIND-net
|
||||
# The versions below should target the newest Kubernetes version
|
||||
# Keep this up-to-date with https://endoflife.date/kubernetes
|
||||
node_image: kindest/node:v1.27.3@sha256:3966ac761ae0136263ffdb6cfd4db23ef8a83cba8a463690e98317add2c9ba72
|
||||
kubectl_version: v1.27.3
|
||||
- name: Setup Calico for network policy
|
||||
run: |
|
||||
kubectl apply -f https://docs.projectcalico.org/v3.25/manifests/calico.yaml
|
||||
kubectl -n kube-system set env daemonset/calico-node FELIX_IGNORELOOSERPF=true
|
||||
- name: Setup Kustomize
|
||||
uses: ./.github/actions/kustomize
|
||||
- name: Run test
|
||||
uses: fluxcd/pkg/actions/kustomize@main
|
||||
- name: Run tests
|
||||
run: make test
|
||||
- name: Run e2e tests
|
||||
run: TEST_KUBECONFIG=$HOME/.kube/config make e2e
|
||||
- name: Check if working tree is dirty
|
||||
run: |
|
||||
if [[ $(git diff --stat) != '' ]]; then
|
||||
git diff
|
||||
echo 'run make test and commit changes'
|
||||
exit 1
|
||||
fi
|
||||
- name: Build
|
||||
run: sudo go build -o ./bin/tk ./cmd/tk
|
||||
- name: tk check --pre
|
||||
run: |
|
||||
./bin/tk check --pre
|
||||
- name: tk install --version
|
||||
go build -o /tmp/flux ./cmd/flux
|
||||
- name: flux check --pre
|
||||
run: |
|
||||
./bin/tk install --version=master --namespace=test --verbose
|
||||
- name: tk uninstall
|
||||
/tmp/flux check --pre
|
||||
- name: flux install --manifests
|
||||
run: |
|
||||
./bin/tk uninstall --namespace=test --crds --silent
|
||||
- name: tk install --manifests
|
||||
/tmp/flux install --manifests ./manifests/install/
|
||||
- name: flux create secret
|
||||
run: |
|
||||
./bin/tk install --manifests ./manifests/install/ --version=""
|
||||
- name: tk create source git
|
||||
/tmp/flux create secret git git-ssh-test \
|
||||
--url ssh://git@github.com/stefanprodan/podinfo
|
||||
/tmp/flux create secret git git-https-test \
|
||||
--url https://github.com/stefanprodan/podinfo \
|
||||
--username=test --password=test
|
||||
/tmp/flux create secret helm helm-test \
|
||||
--username=test --password=test
|
||||
- name: flux create source git
|
||||
run: |
|
||||
./bin/tk create source git podinfo \
|
||||
/tmp/flux create source git podinfo \
|
||||
--url https://github.com/stefanprodan/podinfo \
|
||||
--tag-semver=">=3.2.3"
|
||||
- name: tk get sources git
|
||||
--tag-semver=">=6.3.5"
|
||||
- name: flux create source git export apply
|
||||
run: |
|
||||
./bin/tk get sources git
|
||||
- name: tk create kustomization
|
||||
/tmp/flux create source git podinfo-export \
|
||||
--url https://github.com/stefanprodan/podinfo \
|
||||
--tag-semver=">=6.3.5" \
|
||||
--export | kubectl apply -f -
|
||||
/tmp/flux delete source git podinfo-export --silent
|
||||
- name: flux get sources git
|
||||
run: |
|
||||
./bin/tk create kustomization podinfo \
|
||||
/tmp/flux get sources git
|
||||
- name: flux get sources git --all-namespaces
|
||||
run: |
|
||||
/tmp/flux get sources git --all-namespaces
|
||||
- name: flux create kustomization
|
||||
run: |
|
||||
/tmp/flux create kustomization podinfo \
|
||||
--source=podinfo \
|
||||
--path="./deploy/overlays/dev" \
|
||||
--prune=true \
|
||||
--interval=5m \
|
||||
--validate=client \
|
||||
--health-check="Deployment/frontend.dev" \
|
||||
--health-check="Deployment/backend.dev" \
|
||||
--health-check-timeout=3m
|
||||
- name: tk sync kustomization --with-source
|
||||
- name: flux trace
|
||||
run: |
|
||||
./bin/tk sync kustomization podinfo --with-source
|
||||
- name: tk get kustomizations
|
||||
/tmp/flux trace frontend \
|
||||
--kind=deployment \
|
||||
--api-version=apps/v1 \
|
||||
--namespace=dev
|
||||
- name: flux reconcile kustomization --with-source
|
||||
run: |
|
||||
./bin/tk get kustomizations
|
||||
- name: tk suspend kustomization
|
||||
/tmp/flux reconcile kustomization podinfo --with-source
|
||||
- name: flux get kustomizations
|
||||
run: |
|
||||
./bin/tk suspend kustomization podinfo
|
||||
- name: tk resume kustomization
|
||||
/tmp/flux get kustomizations
|
||||
- name: flux get kustomizations --all-namespaces
|
||||
run: |
|
||||
./bin/tk resume kustomization podinfo
|
||||
- name: tk export
|
||||
/tmp/flux get kustomizations --all-namespaces
|
||||
- name: flux suspend kustomization
|
||||
run: |
|
||||
./bin/tk export source git --all
|
||||
./bin/tk export kustomization --all
|
||||
- name: tk delete kustomization
|
||||
/tmp/flux suspend kustomization podinfo
|
||||
- name: flux resume kustomization
|
||||
run: |
|
||||
./bin/tk delete kustomization podinfo --silent
|
||||
- name: tk delete source git
|
||||
/tmp/flux resume kustomization podinfo
|
||||
- name: flux export
|
||||
run: |
|
||||
./bin/tk delete source git podinfo --silent
|
||||
- name: tk check
|
||||
/tmp/flux export source git --all
|
||||
/tmp/flux export kustomization --all
|
||||
- name: flux delete kustomization
|
||||
run: |
|
||||
./bin/tk check
|
||||
/tmp/flux delete kustomization podinfo --silent
|
||||
- name: flux create source helm
|
||||
run: |
|
||||
/tmp/flux create source helm podinfo \
|
||||
--url https://stefanprodan.github.io/podinfo
|
||||
- name: flux create helmrelease --source=HelmRepository/podinfo
|
||||
run: |
|
||||
/tmp/flux create hr podinfo-helm \
|
||||
--target-namespace=default \
|
||||
--source=HelmRepository/podinfo.flux-system \
|
||||
--chart=podinfo \
|
||||
--chart-version=">6.0.0 <7.0.0"
|
||||
- name: flux create helmrelease --source=GitRepository/podinfo
|
||||
run: |
|
||||
/tmp/flux create hr podinfo-git \
|
||||
--target-namespace=default \
|
||||
--source=GitRepository/podinfo \
|
||||
--chart=./charts/podinfo
|
||||
- name: flux reconcile helmrelease --with-source
|
||||
run: |
|
||||
/tmp/flux reconcile helmrelease podinfo-git --with-source
|
||||
- name: flux get helmreleases
|
||||
run: |
|
||||
/tmp/flux get helmreleases
|
||||
- name: flux get helmreleases --all-namespaces
|
||||
run: |
|
||||
/tmp/flux get helmreleases --all-namespaces
|
||||
- name: flux export helmrelease
|
||||
run: |
|
||||
/tmp/flux export hr --all
|
||||
- name: flux delete helmrelease podinfo-helm
|
||||
run: |
|
||||
/tmp/flux delete hr podinfo-helm --silent
|
||||
- name: flux delete helmrelease podinfo-git
|
||||
run: |
|
||||
/tmp/flux delete hr podinfo-git --silent
|
||||
- name: flux delete source helm
|
||||
run: |
|
||||
/tmp/flux delete source helm podinfo --silent
|
||||
- name: flux delete source git
|
||||
run: |
|
||||
/tmp/flux delete source git podinfo --silent
|
||||
- name: flux oci artifacts
|
||||
run: |
|
||||
/tmp/flux push artifact oci://localhost:5000/fluxcd/flux:${{ github.sha }} \
|
||||
--path="./manifests" \
|
||||
--source="${{ github.repositoryUrl }}" \
|
||||
--revision="${{ github.ref }}@sha1:${{ github.sha }}"
|
||||
/tmp/flux tag artifact oci://localhost:5000/fluxcd/flux:${{ github.sha }} \
|
||||
--tag latest
|
||||
/tmp/flux list artifacts oci://localhost:5000/fluxcd/flux
|
||||
- name: flux oci repositories
|
||||
run: |
|
||||
/tmp/flux create source oci podinfo-oci \
|
||||
--url oci://ghcr.io/stefanprodan/manifests/podinfo \
|
||||
--tag-semver 6.3.x \
|
||||
--interval 10m
|
||||
/tmp/flux create kustomization podinfo-oci \
|
||||
--source=OCIRepository/podinfo-oci \
|
||||
--path="./" \
|
||||
--prune=true \
|
||||
--interval=5m \
|
||||
--target-namespace=default \
|
||||
--wait=true \
|
||||
--health-check-timeout=3m
|
||||
/tmp/flux reconcile source oci podinfo-oci
|
||||
/tmp/flux suspend source oci podinfo-oci
|
||||
/tmp/flux get sources oci
|
||||
/tmp/flux resume source oci podinfo-oci
|
||||
/tmp/flux export source oci podinfo-oci
|
||||
/tmp/flux delete ks podinfo-oci --silent
|
||||
/tmp/flux delete source oci podinfo-oci --silent
|
||||
- name: flux create tenant
|
||||
run: |
|
||||
/tmp/flux create tenant dev-team --with-namespace=apps
|
||||
/tmp/flux -n apps create source helm podinfo \
|
||||
--url https://stefanprodan.github.io/podinfo
|
||||
/tmp/flux -n apps create hr podinfo-helm \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo \
|
||||
--chart-version="6.3.x" \
|
||||
--service-account=dev-team
|
||||
- name: flux2-kustomize-helm-example
|
||||
run: |
|
||||
/tmp/flux create source git flux-system \
|
||||
--url=https://github.com/fluxcd/flux2-kustomize-helm-example \
|
||||
--branch=main \
|
||||
--ignore-paths="./clusters/**/flux-system/" \
|
||||
--recurse-submodules
|
||||
/tmp/flux create kustomization flux-system \
|
||||
--source=flux-system \
|
||||
--path=./clusters/staging
|
||||
kubectl -n flux-system wait kustomization/infra-controllers --for=condition=ready --timeout=5m
|
||||
kubectl -n flux-system wait kustomization/apps --for=condition=ready --timeout=5m
|
||||
kubectl -n podinfo wait helmrelease/podinfo --for=condition=ready --timeout=5m
|
||||
- name: flux tree
|
||||
run: |
|
||||
/tmp/flux tree kustomization flux-system | grep Service/podinfo
|
||||
- name: flux check
|
||||
run: |
|
||||
/tmp/flux check
|
||||
- name: flux uninstall
|
||||
run: |
|
||||
/tmp/flux uninstall --silent
|
||||
- name: Debug failure
|
||||
if: failure()
|
||||
run: |
|
||||
kubectl version --client --short
|
||||
kustomize version --short
|
||||
kubectl -n gitops-system get all
|
||||
kubectl -n gitops-system get kustomizations -oyaml
|
||||
kubectl -n gitops-system logs deploy/source-controller
|
||||
kubectl -n gitops-system logs deploy/kustomize-controller
|
||||
kubectl -n flux-system get all
|
||||
kubectl -n flux-system describe pods
|
||||
kubectl -n flux-system get kustomizations -oyaml
|
||||
kubectl -n flux-system logs deploy/source-controller
|
||||
kubectl -n flux-system logs deploy/kustomize-controller
|
||||
|
||||
39
.github/workflows/ossf.yaml
vendored
Normal file
39
.github/workflows/ossf.yaml
vendored
Normal file
@@ -0,0 +1,39 @@
|
||||
name: ossf
|
||||
on:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches:
|
||||
- main
|
||||
schedule:
|
||||
# Weekly on Saturdays.
|
||||
- cron: '30 1 * * 6'
|
||||
|
||||
permissions: read-all
|
||||
|
||||
jobs:
|
||||
scorecard:
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
security-events: write
|
||||
id-token: write
|
||||
actions: read
|
||||
contents: read
|
||||
steps:
|
||||
- uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Run analysis
|
||||
uses: ossf/scorecard-action@08b4669551908b1024bb425080c797723083c031 # v2.2.0
|
||||
with:
|
||||
results_file: results.sarif
|
||||
results_format: sarif
|
||||
repo_token: ${{ secrets.GITHUB_TOKEN }}
|
||||
publish_results: true
|
||||
- name: Upload artifact
|
||||
uses: actions/upload-artifact@0b7f8abb1508181956e8e162db84b466c27e18ce # v3.1.2
|
||||
with:
|
||||
name: SARIF file
|
||||
path: results.sarif
|
||||
retention-days: 5
|
||||
- name: Upload SARIF results
|
||||
uses: github/codeql-action/upload-sarif@cdcdbb579706841c47f7063dda365e292e5cad7a # v2.13.4
|
||||
with:
|
||||
sarif_file: results.sarif
|
||||
203
.github/workflows/release.yaml
vendored
203
.github/workflows/release.yaml
vendored
@@ -2,33 +2,210 @@ name: release
|
||||
|
||||
on:
|
||||
push:
|
||||
tags:
|
||||
- '*'
|
||||
tags: [ 'v*' ]
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
goreleaser:
|
||||
release-flux-cli:
|
||||
outputs:
|
||||
hashes: ${{ steps.slsa.outputs.hashes }}
|
||||
image_url: ${{ steps.slsa.outputs.image_url }}
|
||||
image_digest: ${{ steps.slsa.outputs.image_digest }}
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
contents: write # needed to write releases
|
||||
id-token: write # needed for keyless signing
|
||||
packages: write # needed for ghcr access
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v2
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Unshallow
|
||||
run: git fetch --prune --unshallow
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@v2-beta
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.14.x
|
||||
go-version: 1.20.x
|
||||
cache: false
|
||||
- name: Setup QEMU
|
||||
uses: docker/setup-qemu-action@2b82ce82d56a2a04d2637cd93a637ae1b359c0a7 # v2.2.0
|
||||
- name: Setup Docker Buildx
|
||||
id: buildx
|
||||
uses: docker/setup-buildx-action@4c0219f9ac95b02789c1075625400b2acbff50b1 # v2.9.1
|
||||
- name: Setup Syft
|
||||
uses: anchore/sbom-action/download-syft@78fc58e266e87a38d4194b2137a3d4e9bcaf7ca1 # v0.14.3
|
||||
- name: Setup Cosign
|
||||
uses: sigstore/cosign-installer@6e04d228eb30da1757ee4e1dd75a0ec73a653e06 # v3.1.1
|
||||
- name: Setup Kustomize
|
||||
uses: fluxcd/pkg/actions/kustomize@main
|
||||
- name: Login to GitHub Container Registry
|
||||
uses: docker/login-action@465a07811f14bebb1938fbed4728c6a1ff8901fc # v2.2.0
|
||||
with:
|
||||
registry: ghcr.io
|
||||
username: fluxcdbot
|
||||
password: ${{ secrets.GHCR_TOKEN }}
|
||||
- name: Login to Docker Hub
|
||||
uses: docker/login-action@465a07811f14bebb1938fbed4728c6a1ff8901fc # v2.2.0
|
||||
with:
|
||||
username: fluxcdbot
|
||||
password: ${{ secrets.DOCKER_FLUXCD_PASSWORD }}
|
||||
- name: Generate manifests
|
||||
run: |
|
||||
make cmd/flux/.manifests.done
|
||||
./manifests/scripts/bundle.sh "" ./output manifests.tar.gz
|
||||
kustomize build ./manifests/install > ./output/install.yaml
|
||||
- name: Build CRDs
|
||||
run: |
|
||||
kustomize build manifests/crds > all-crds.yaml
|
||||
- name: Generate OpenAPI JSON schemas from CRDs
|
||||
uses: fluxcd/pkg/actions/crdjsonschema@main
|
||||
with:
|
||||
crd: all-crds.yaml
|
||||
output: schemas
|
||||
- name: Archive the OpenAPI JSON schemas
|
||||
run: |
|
||||
tar -czvf ./output/crd-schemas.tar.gz -C schemas .
|
||||
- name: Download release notes utility
|
||||
env:
|
||||
GH_REL_URL: https://github.com/buchanae/github-release-notes/releases/download/0.2.0/github-release-notes-linux-amd64-0.2.0.tar.gz
|
||||
run: cd /tmp && curl -sSL ${GH_REL_URL} | tar xz && sudo mv github-release-notes /usr/local/bin/
|
||||
- name: Generate release notes
|
||||
run: |
|
||||
echo 'CHANGELOG' > /tmp/release.txt
|
||||
github-release-notes -org fluxcd -repo toolkit >> /tmp/release.txt
|
||||
- name: Run GoReleaser
|
||||
uses: goreleaser/goreleaser-action@v1
|
||||
with:
|
||||
version: latest
|
||||
args: release --release-notes=/tmp/release.txt
|
||||
NOTES="./output/notes.md"
|
||||
echo '## CLI Changelog' > ${NOTES}
|
||||
github-release-notes -org fluxcd -repo flux2 -since-latest-release -include-author >> ${NOTES}
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
|
||||
- name: Run GoReleaser
|
||||
id: run-goreleaser
|
||||
uses: goreleaser/goreleaser-action@336e29918d653399e599bfca99fadc1d7ffbc9f7 # v4.3.0
|
||||
with:
|
||||
version: latest
|
||||
args: release --release-notes=output/notes.md --skip-validate
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
|
||||
HOMEBREW_TAP_GITHUB_TOKEN: ${{ secrets.BOT_GITHUB_TOKEN }}
|
||||
AUR_BOT_SSH_PRIVATE_KEY: ${{ secrets.AUR_BOT_SSH_PRIVATE_KEY }}
|
||||
- name: Generate SLSA metadata
|
||||
id: slsa
|
||||
env:
|
||||
ARTIFACTS: "${{ steps.run-goreleaser.outputs.artifacts }}"
|
||||
run: |
|
||||
set -euo pipefail
|
||||
|
||||
hashes=$(echo -E $ARTIFACTS | jq --raw-output '.[] | {name, "digest": (.extra.Digest // .extra.Checksum)} | select(.digest) | {digest} + {name} | join(" ") | sub("^sha256:";"")' | base64 -w0)
|
||||
echo "hashes=$hashes" >> $GITHUB_OUTPUT
|
||||
|
||||
image_url=fluxcd/flux-cli:$GITHUB_REF_NAME
|
||||
echo "image_url=$image_url" >> $GITHUB_OUTPUT
|
||||
|
||||
image_digest=$(docker buildx imagetools inspect ${image_url} --format '{{json .}}' | jq -r .manifest.digest)
|
||||
echo "image_digest=$image_digest" >> $GITHUB_OUTPUT
|
||||
|
||||
release-flux-manifests:
|
||||
runs-on: ubuntu-latest
|
||||
needs: release-flux-cli
|
||||
permissions:
|
||||
id-token: write
|
||||
packages: write
|
||||
steps:
|
||||
- uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Kustomize
|
||||
uses: fluxcd/pkg/actions/kustomize@main
|
||||
- name: Setup Flux CLI
|
||||
uses: ./action/
|
||||
- name: Prepare
|
||||
id: prep
|
||||
run: |
|
||||
VERSION=$(flux version --client | awk '{ print $NF }')
|
||||
echo "version=${VERSION}" >> $GITHUB_OUTPUT
|
||||
- name: Login to GHCR
|
||||
uses: docker/login-action@465a07811f14bebb1938fbed4728c6a1ff8901fc # v2.2.0
|
||||
with:
|
||||
registry: ghcr.io
|
||||
username: fluxcdbot
|
||||
password: ${{ secrets.GHCR_TOKEN }}
|
||||
- name: Login to DockerHub
|
||||
uses: docker/login-action@465a07811f14bebb1938fbed4728c6a1ff8901fc # v2.2.0
|
||||
with:
|
||||
username: fluxcdbot
|
||||
password: ${{ secrets.DOCKER_FLUXCD_PASSWORD }}
|
||||
- name: Push manifests to GHCR
|
||||
run: |
|
||||
mkdir -p ./ghcr.io/flux-system
|
||||
flux install --registry=ghcr.io/fluxcd \
|
||||
--components-extra=image-reflector-controller,image-automation-controller \
|
||||
--export > ./ghcr.io/flux-system/gotk-components.yaml
|
||||
|
||||
cd ./ghcr.io && flux push artifact \
|
||||
oci://ghcr.io/fluxcd/flux-manifests:${{ steps.prep.outputs.version }} \
|
||||
--path="./flux-system" \
|
||||
--source=${{ github.repositoryUrl }} \
|
||||
--revision="${{ github.ref_name }}@sha1:${{ github.sha }}"
|
||||
- name: Push manifests to DockerHub
|
||||
run: |
|
||||
mkdir -p ./docker.io/flux-system
|
||||
flux install --registry=docker.io/fluxcd \
|
||||
--components-extra=image-reflector-controller,image-automation-controller \
|
||||
--export > ./docker.io/flux-system/gotk-components.yaml
|
||||
|
||||
cd ./docker.io && flux push artifact \
|
||||
oci://docker.io/fluxcd/flux-manifests:${{ steps.prep.outputs.version }} \
|
||||
--path="./flux-system" \
|
||||
--source=${{ github.repositoryUrl }} \
|
||||
--revision="${{ github.ref_name }}@sha1:${{ github.sha }}"
|
||||
- uses: sigstore/cosign-installer@6e04d228eb30da1757ee4e1dd75a0ec73a653e06 # v3.1.1
|
||||
- name: Sign manifests
|
||||
env:
|
||||
COSIGN_EXPERIMENTAL: 1
|
||||
run: |
|
||||
cosign sign --yes ghcr.io/fluxcd/flux-manifests:${{ steps.prep.outputs.version }}
|
||||
cosign sign --yes docker.io/fluxcd/flux-manifests:${{ steps.prep.outputs.version }}
|
||||
- name: Tag manifests
|
||||
run: |
|
||||
flux tag artifact oci://ghcr.io/fluxcd/flux-manifests:${{ steps.prep.outputs.version }} \
|
||||
--tag latest
|
||||
|
||||
flux tag artifact oci://docker.io/fluxcd/flux-manifests:${{ steps.prep.outputs.version }} \
|
||||
--tag latest
|
||||
|
||||
release-provenance:
|
||||
needs: [release-flux-cli]
|
||||
permissions:
|
||||
actions: read # for detecting the Github Actions environment.
|
||||
id-token: write # for creating OIDC tokens for signing.
|
||||
contents: write # for uploading attestations to GitHub releases.
|
||||
uses: slsa-framework/slsa-github-generator/.github/workflows/generator_generic_slsa3.yml@v1.7.0
|
||||
with:
|
||||
provenance-name: "provenance.intoto.jsonl"
|
||||
base64-subjects: "${{ needs.release-flux-cli.outputs.hashes }}"
|
||||
upload-assets: true
|
||||
|
||||
dockerhub-provenance:
|
||||
needs: [release-flux-cli]
|
||||
permissions:
|
||||
actions: read # for detecting the Github Actions environment.
|
||||
id-token: write # for creating OIDC tokens for signing.
|
||||
packages: write # for uploading attestations.
|
||||
uses: slsa-framework/slsa-github-generator/.github/workflows/generator_container_slsa3.yml@v1.7.0
|
||||
with:
|
||||
image: ${{ needs.release-flux-cli.outputs.image_url }}
|
||||
digest: ${{ needs.release-flux-cli.outputs.image_digest }}
|
||||
registry-username: fluxcdbot
|
||||
secrets:
|
||||
registry-password: ${{ secrets.DOCKER_FLUXCD_PASSWORD }}
|
||||
|
||||
ghcr-provenance:
|
||||
needs: [release-flux-cli]
|
||||
permissions:
|
||||
actions: read # for detecting the Github Actions environment.
|
||||
id-token: write # for creating OIDC tokens for signing.
|
||||
packages: write # for uploading attestations.
|
||||
uses: slsa-framework/slsa-github-generator/.github/workflows/generator_container_slsa3.yml@v1.7.0
|
||||
with:
|
||||
image: ghcr.io/${{ needs.release-flux-cli.outputs.image_url }}
|
||||
digest: ${{ needs.release-flux-cli.outputs.image_digest }}
|
||||
registry-username: fluxcdbot
|
||||
secrets:
|
||||
registry-password: ${{ secrets.GHCR_TOKEN }}
|
||||
|
||||
82
.github/workflows/scan.yaml
vendored
Normal file
82
.github/workflows/scan.yaml
vendored
Normal file
@@ -0,0 +1,82 @@
|
||||
name: scan
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches: [ 'main', 'release/**' ]
|
||||
pull_request:
|
||||
branches: [ 'main', 'release/**' ]
|
||||
schedule:
|
||||
- cron: '18 10 * * 3'
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
scan-fossa:
|
||||
runs-on: ubuntu-latest
|
||||
if: github.actor != 'dependabot[bot]'
|
||||
steps:
|
||||
- uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Run FOSSA scan and upload build data
|
||||
uses: fossa-contrib/fossa-action@6728dc6fe9a068c648d080c33829ffbe56565023 # v2.0.0
|
||||
with:
|
||||
# FOSSA Push-Only API Token
|
||||
fossa-api-key: 5ee8bf422db1471e0bcf2bcb289185de
|
||||
github-token: ${{ github.token }}
|
||||
|
||||
scan-snyk:
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
security-events: write
|
||||
if: (github.event_name != 'pull_request' || github.event.pull_request.head.repo.full_name == github.repository) && github.actor != 'dependabot[bot]'
|
||||
steps:
|
||||
- uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Kustomize
|
||||
uses: fluxcd/pkg/actions/kustomize@main
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Download modules and build manifests
|
||||
run: |
|
||||
make tidy
|
||||
make cmd/flux/.manifests.done
|
||||
- uses: snyk/actions/setup@b98d498629f1c368650224d6d212bf7dfa89e4bf
|
||||
- name: Run Snyk to check for vulnerabilities
|
||||
continue-on-error: true
|
||||
run: |
|
||||
snyk test --sarif-file-output=snyk.sarif
|
||||
env:
|
||||
SNYK_TOKEN: ${{ secrets.SNYK_TOKEN }}
|
||||
- name: Upload result to GitHub Code Scanning
|
||||
uses: github/codeql-action/upload-sarif@cdcdbb579706841c47f7063dda365e292e5cad7a # v2.13.4
|
||||
with:
|
||||
sarif_file: snyk.sarif
|
||||
|
||||
scan-codeql:
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
security-events: write
|
||||
if: github.actor != 'dependabot[bot]'
|
||||
steps:
|
||||
- name: Checkout repository
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Initialize CodeQL
|
||||
uses: github/codeql-action/init@cdcdbb579706841c47f7063dda365e292e5cad7a # v2.13.4
|
||||
with:
|
||||
languages: go
|
||||
- name: Autobuild
|
||||
uses: github/codeql-action/autobuild@cdcdbb579706841c47f7063dda365e292e5cad7a # v2.13.4
|
||||
- name: Perform CodeQL Analysis
|
||||
uses: github/codeql-action/analyze@cdcdbb579706841c47f7063dda365e292e5cad7a # v2.13.4
|
||||
28
.github/workflows/sync-labels.yaml
vendored
Normal file
28
.github/workflows/sync-labels.yaml
vendored
Normal file
@@ -0,0 +1,28 @@
|
||||
name: sync-labels
|
||||
on:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches:
|
||||
- main
|
||||
paths:
|
||||
- .github/labels.yaml
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
labels:
|
||||
name: Run sync
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
issues: write
|
||||
steps:
|
||||
- uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- uses: EndBug/label-sync@da00f2c11fdb78e4fae44adac2fdd713778ea3e8 # v2.3.2
|
||||
with:
|
||||
# Configuration file
|
||||
config-file: |
|
||||
https://raw.githubusercontent.com/fluxcd/community/main/.github/standard-labels.yaml
|
||||
.github/labels.yaml
|
||||
# Strictly declarative
|
||||
delete-other-labels: true
|
||||
108
.github/workflows/update.yaml
vendored
Normal file
108
.github/workflows/update.yaml
vendored
Normal file
@@ -0,0 +1,108 @@
|
||||
name: update
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
schedule:
|
||||
- cron: "0 * * * *"
|
||||
push:
|
||||
branches: [main]
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
update-components:
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
contents: write
|
||||
pull-requests: write
|
||||
steps:
|
||||
- name: Check out code
|
||||
uses: actions/checkout@c85c95e3d7251135ab7dc9ce3241c5835cc595a9 # v3.5.3
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@fac708d6674e30b6ba41289acaab6d4b75aa0753 # v4.0.1
|
||||
with:
|
||||
go-version: 1.20.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Update component versions
|
||||
id: update
|
||||
run: |
|
||||
PR_BODY=$(mktemp)
|
||||
|
||||
bump_version() {
|
||||
local LATEST_VERSION=$(curl -s https://api.github.com/repos/fluxcd/$1/releases | jq -r 'sort_by(.published_at) | .[-1] | .tag_name')
|
||||
local CTRL_VERSION=$(sed -n "s/.*$1\/releases\/download\/\(.*\)\/.*/\1/p;n" manifests/bases/$1/kustomization.yaml)
|
||||
local CRD_VERSION=$(sed -n "s/.*$1\/releases\/download\/\(.*\)\/.*/\1/p" manifests/crds/kustomization.yaml)
|
||||
local MOD_VERSION=$(go list -m -f '{{ .Version }}' "github.com/fluxcd/$1/api")
|
||||
|
||||
local changed=false
|
||||
|
||||
if [[ "${CTRL_VERSION}" != "${LATEST_VERSION}" ]]; then
|
||||
sed -i "s/\($1\/releases\/download\/\)v.*\(\/.*\)/\1${LATEST_VERSION}\2/g" "manifests/bases/$1/kustomization.yaml"
|
||||
changed=true
|
||||
fi
|
||||
|
||||
if [[ "${CRD_VERSION}" != "${LATEST_VERSION}" ]]; then
|
||||
sed -i "s/\($1\/releases\/download\/\)v.*\(\/.*\)/\1${LATEST_VERSION}\2/g" "manifests/crds/kustomization.yaml"
|
||||
changed=true
|
||||
fi
|
||||
|
||||
if [[ "${MOD_VERSION}" != "${LATEST_VERSION}" ]]; then
|
||||
go mod edit -require="github.com/fluxcd/$1/api@${LATEST_VERSION}"
|
||||
make tidy
|
||||
changed=true
|
||||
fi
|
||||
|
||||
if [[ "$changed" == true ]]; then
|
||||
echo "- $1 to ${LATEST_VERSION}" >> $PR_BODY
|
||||
echo " https://github.com/fluxcd/$1/blob/${LATEST_VERSION}/CHANGELOG.md" >> $PR_BODY
|
||||
fi
|
||||
}
|
||||
|
||||
{
|
||||
# bump controller versions
|
||||
bump_version helm-controller
|
||||
bump_version kustomize-controller
|
||||
bump_version source-controller
|
||||
bump_version notification-controller
|
||||
bump_version image-reflector-controller
|
||||
bump_version image-automation-controller
|
||||
|
||||
# diff change
|
||||
git diff
|
||||
|
||||
# export PR_BODY for PR and commit
|
||||
# NB: this may look strange but it is the way it should be done to
|
||||
# maintain our precious newlines
|
||||
# Ref: https://github.com/github/docs/issues/21529
|
||||
echo 'pr_body<<EOF' >> $GITHUB_OUTPUT
|
||||
cat $PR_BODY >> $GITHUB_OUTPUT
|
||||
echo 'EOF' >> $GITHUB_OUTPUT
|
||||
}
|
||||
|
||||
- name: Create Pull Request
|
||||
id: cpr
|
||||
uses: peter-evans/create-pull-request@153407881ec5c347639a548ade7d8ad1d6740e38 # v5.0.2
|
||||
with:
|
||||
token: ${{ secrets.BOT_GITHUB_TOKEN }}
|
||||
commit-message: |
|
||||
Update toolkit components
|
||||
|
||||
${{ steps.update.outputs.pr_body }}
|
||||
committer: GitHub <noreply@github.com>
|
||||
author: fluxcdbot <fluxcdbot@users.noreply.github.com>
|
||||
signoff: true
|
||||
branch: update-components
|
||||
title: Update toolkit components
|
||||
body: |
|
||||
${{ steps.update.outputs.pr_body }}
|
||||
labels: |
|
||||
dependencies
|
||||
reviewers: ${{ secrets.ASSIGNEES }}
|
||||
|
||||
- name: Check output
|
||||
run: |
|
||||
echo "Pull Request Number - ${{ steps.cpr.outputs.pull-request-number }}"
|
||||
echo "Pull Request URL - ${{ steps.cpr.outputs.pull-request-url }}"
|
||||
12
.gitignore
vendored
12
.gitignore
vendored
@@ -11,6 +11,16 @@
|
||||
# Output of the go coverage tool, specifically when used with LiteIDE
|
||||
*.out
|
||||
|
||||
# Release
|
||||
dist/
|
||||
|
||||
# Dependency directories (remove the comment below to include it)
|
||||
# vendor/
|
||||
bin/
|
||||
bin/
|
||||
output/
|
||||
cmd/flux/manifests/
|
||||
cmd/flux/.manifests.done
|
||||
testbin/
|
||||
|
||||
# Docs
|
||||
site/
|
||||
|
||||
171
.goreleaser.yml
171
.goreleaser.yml
@@ -1,14 +1,175 @@
|
||||
project_name: flux
|
||||
builds:
|
||||
- main: ./cmd/tk
|
||||
binary: tk
|
||||
- <<: &build_defaults
|
||||
binary: flux
|
||||
main: ./cmd/flux
|
||||
ldflags:
|
||||
- -s -w -X main.VERSION={{ .Version }}
|
||||
env:
|
||||
- CGO_ENABLED=0
|
||||
id: linux
|
||||
goos:
|
||||
- darwin
|
||||
- linux
|
||||
goarch:
|
||||
- amd64
|
||||
env:
|
||||
- CGO_ENABLED=0
|
||||
- arm64
|
||||
- arm
|
||||
goarm:
|
||||
- 7
|
||||
- <<: *build_defaults
|
||||
id: darwin
|
||||
goos:
|
||||
- darwin
|
||||
goarch:
|
||||
- amd64
|
||||
- arm64
|
||||
- <<: *build_defaults
|
||||
id: windows
|
||||
goos:
|
||||
- windows
|
||||
archives:
|
||||
- name_template: "{{ .Binary }}_{{ .Version }}_{{ .Os }}_{{ .Arch }}"
|
||||
id: nix
|
||||
builds: [linux, darwin]
|
||||
format: tar.gz
|
||||
files:
|
||||
- none*
|
||||
- name_template: "{{ .Binary }}_{{ .Version }}_{{ .Os }}_{{ .Arch }}"
|
||||
id: windows
|
||||
builds: [windows]
|
||||
format: zip
|
||||
files:
|
||||
- none*
|
||||
source:
|
||||
enabled: true
|
||||
name_template: '{{ .ProjectName }}_{{ .Version }}_source_code'
|
||||
sboms:
|
||||
- id: source
|
||||
artifacts: source
|
||||
documents:
|
||||
- "{{ .ProjectName }}_{{ .Version }}_sbom.spdx.json"
|
||||
release:
|
||||
extra_files:
|
||||
- glob: output/crd-schemas.tar.gz
|
||||
- glob: output/manifests.tar.gz
|
||||
- glob: output/install.yaml
|
||||
checksum:
|
||||
extra_files:
|
||||
- glob: output/crd-schemas.tar.gz
|
||||
- glob: output/manifests.tar.gz
|
||||
- glob: output/install.yaml
|
||||
signs:
|
||||
- cmd: cosign
|
||||
env:
|
||||
- COSIGN_EXPERIMENTAL=1
|
||||
certificate: '${artifact}.pem'
|
||||
args:
|
||||
- sign-blob
|
||||
- "--yes"
|
||||
- '--output-certificate=${certificate}'
|
||||
- '--output-signature=${signature}'
|
||||
- '${artifact}'
|
||||
artifacts: checksum
|
||||
output: true
|
||||
brews:
|
||||
- name: flux
|
||||
tap:
|
||||
owner: fluxcd
|
||||
name: homebrew-tap
|
||||
token: "{{ .Env.HOMEBREW_TAP_GITHUB_TOKEN }}"
|
||||
folder: Formula
|
||||
homepage: "https://fluxcd.io/"
|
||||
description: "Flux CLI"
|
||||
install: |
|
||||
bin.install "flux"
|
||||
|
||||
generate_completions_from_executable(bin/"flux", "completion")
|
||||
test: |
|
||||
system "#{bin}/flux --version"
|
||||
publishers:
|
||||
- name: aur-pkg-bin
|
||||
env:
|
||||
- AUR_BOT_SSH_PRIVATE_KEY={{ .Env.AUR_BOT_SSH_PRIVATE_KEY }}
|
||||
cmd: |
|
||||
.github/aur/flux-bin/publish.sh {{ .Version }}
|
||||
- name: aur-pkg-scm
|
||||
env:
|
||||
- AUR_BOT_SSH_PRIVATE_KEY={{ .Env.AUR_BOT_SSH_PRIVATE_KEY }}
|
||||
cmd: |
|
||||
.github/aur/flux-scm/publish.sh {{ .Version }}
|
||||
- name: aur-pkg-go
|
||||
env:
|
||||
- AUR_BOT_SSH_PRIVATE_KEY={{ .Env.AUR_BOT_SSH_PRIVATE_KEY }}
|
||||
cmd: |
|
||||
.github/aur/flux-go/publish.sh {{ .Version }}
|
||||
dockers:
|
||||
- image_templates:
|
||||
- 'fluxcd/flux-cli:{{ .Tag }}-amd64'
|
||||
- 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}-amd64'
|
||||
dockerfile: Dockerfile
|
||||
use: buildx
|
||||
goos: linux
|
||||
goarch: amd64
|
||||
build_flag_templates:
|
||||
- "--pull"
|
||||
- "--build-arg=ARCH=linux/amd64"
|
||||
- "--label=org.opencontainers.image.created={{ .Date }}"
|
||||
- "--label=org.opencontainers.image.name={{ .ProjectName }}"
|
||||
- "--label=org.opencontainers.image.revision={{ .FullCommit }}"
|
||||
- "--label=org.opencontainers.image.version={{ .Version }}"
|
||||
- "--label=org.opencontainers.image.source={{ .GitURL }}"
|
||||
- "--platform=linux/amd64"
|
||||
- image_templates:
|
||||
- 'fluxcd/flux-cli:{{ .Tag }}-arm64'
|
||||
- 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}-arm64'
|
||||
dockerfile: Dockerfile
|
||||
use: buildx
|
||||
goos: linux
|
||||
goarch: arm64
|
||||
build_flag_templates:
|
||||
- "--pull"
|
||||
- "--build-arg=ARCH=linux/arm64"
|
||||
- "--label=org.opencontainers.image.created={{ .Date }}"
|
||||
- "--label=org.opencontainers.image.name={{ .ProjectName }}"
|
||||
- "--label=org.opencontainers.image.revision={{ .FullCommit }}"
|
||||
- "--label=org.opencontainers.image.version={{ .Version }}"
|
||||
- "--label=org.opencontainers.image.source={{ .GitURL }}"
|
||||
- "--platform=linux/arm64"
|
||||
- image_templates:
|
||||
- 'fluxcd/flux-cli:{{ .Tag }}-arm'
|
||||
- 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}-arm'
|
||||
dockerfile: Dockerfile
|
||||
use: buildx
|
||||
goos: linux
|
||||
goarch: arm
|
||||
goarm: 7
|
||||
build_flag_templates:
|
||||
- "--pull"
|
||||
- "--build-arg=ARCH=linux/arm"
|
||||
- "--label=org.opencontainers.image.created={{ .Date }}"
|
||||
- "--label=org.opencontainers.image.name={{ .ProjectName }}"
|
||||
- "--label=org.opencontainers.image.revision={{ .FullCommit }}"
|
||||
- "--label=org.opencontainers.image.version={{ .Version }}"
|
||||
- "--label=org.opencontainers.image.source={{ .GitURL }}"
|
||||
- "--platform=linux/arm/v7"
|
||||
docker_manifests:
|
||||
- name_template: 'fluxcd/flux-cli:{{ .Tag }}'
|
||||
image_templates:
|
||||
- 'fluxcd/flux-cli:{{ .Tag }}-amd64'
|
||||
- 'fluxcd/flux-cli:{{ .Tag }}-arm64'
|
||||
- 'fluxcd/flux-cli:{{ .Tag }}-arm'
|
||||
- name_template: 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}'
|
||||
image_templates:
|
||||
- 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}-amd64'
|
||||
- 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}-arm64'
|
||||
- 'ghcr.io/fluxcd/flux-cli:{{ .Tag }}-arm'
|
||||
docker_signs:
|
||||
- cmd: cosign
|
||||
env:
|
||||
- COSIGN_EXPERIMENTAL=1
|
||||
args:
|
||||
- sign
|
||||
- "--yes"
|
||||
- '${artifact}'
|
||||
artifacts: all
|
||||
output: true
|
||||
|
||||
120
CONTRIBUTING.md
120
CONTRIBUTING.md
@@ -1,8 +1,9 @@
|
||||
# Contributing
|
||||
|
||||
FluxCD toolkit is [Apache 2.0 licensed](LICENSE) and accepts contributions
|
||||
via GitHub pull requests. This document outlines some of the conventions on
|
||||
to make it easier to get your contribution accepted.
|
||||
Flux is [Apache 2.0 licensed](https://github.com/fluxcd/flux2/blob/main/LICENSE) and
|
||||
accepts contributions via GitHub pull requests. This document outlines
|
||||
some of the conventions on to make it easier to get your contribution
|
||||
accepted.
|
||||
|
||||
We gratefully welcome improvements to issues and documentation as well as to
|
||||
code.
|
||||
@@ -12,30 +13,115 @@ code.
|
||||
By contributing to this project you agree to the Developer Certificate of
|
||||
Origin (DCO). This document was created by the Linux Kernel community and is a
|
||||
simple statement that you, as a contributor, have the legal right to make the
|
||||
contribution. No action from you is required, but it's a good idea to see the
|
||||
[DCO](DCO) file for details before you start contributing code to FluxCD
|
||||
toolkit.
|
||||
contribution.
|
||||
|
||||
We require all commits to be signed. By signing off with your signature, you
|
||||
certify that you wrote the patch or otherwise have the right to contribute the
|
||||
material by the rules of the [DCO](DCO):
|
||||
|
||||
`Signed-off-by: Jane Doe <jane.doe@example.com>`
|
||||
|
||||
The signature must contain your real name
|
||||
(sorry, no pseudonyms or anonymous contributions)
|
||||
If your `user.name` and `user.email` are configured in your Git config,
|
||||
you can sign your commit automatically with `git commit -s`.
|
||||
|
||||
## Communications
|
||||
|
||||
The project uses Slack: To join the conversation, simply join the
|
||||
[CNCF](https://slack.cncf.io/) Slack workspace and use the
|
||||
[#flux](https://cloud-native.slack.com/messages/flux/) channel.
|
||||
For realtime communications we use Slack: To join the conversation, simply
|
||||
join the [CNCF](https://slack.cncf.io/) Slack workspace and use the
|
||||
[#flux-contributors](https://cloud-native.slack.com/messages/flux-contributors/) channel.
|
||||
|
||||
The developers use a mailing list to discuss development as well.
|
||||
Simply subscribe to [flux-dev on cncf.io](https://lists.cncf.io/g/cncf-flux-dev)
|
||||
to join the conversation (this will also add an invitation to your
|
||||
Google calendar for our [Flux
|
||||
meeting](https://docs.google.com/document/d/1l_M0om0qUEN_NNiGgpqJ2tvsF2iioHkaARDeh6b70B0/edit#)).
|
||||
To discuss ideas and specifications we use [Github
|
||||
Discussions](https://github.com/fluxcd/flux2/discussions).
|
||||
|
||||
### How to run the test suite
|
||||
For announcements we use a mailing list as well. Simply subscribe to
|
||||
[flux-dev on cncf.io](https://lists.cncf.io/g/cncf-flux-dev)
|
||||
to join the conversation (there you can also add calendar invites
|
||||
to your Google calendar for our [Flux
|
||||
meeting](https://docs.google.com/document/d/1l_M0om0qUEN_NNiGgpqJ2tvsF2iioHkaARDeh6b70B0/view)).
|
||||
|
||||
You can run the unit tests by simply doing
|
||||
## Understanding Flux and the GitOps Toolkit
|
||||
|
||||
If you are entirely new to Flux and the GitOps Toolkit,
|
||||
you might want to take a look at the [introductory talk and demo](https://www.youtube.com/watch?v=qQBtSkgl7tI).
|
||||
|
||||
This project is composed of:
|
||||
|
||||
- [flux2](https://github.com/fluxcd/flux2): The Flux CLI
|
||||
- [source-manager](https://github.com/fluxcd/source-controller): Kubernetes operator for managing sources (Git and Helm repositories, S3-compatible Buckets)
|
||||
- [kustomize-controller](https://github.com/fluxcd/kustomize-controller): Kubernetes operator for building GitOps pipelines with Kustomize
|
||||
- [helm-controller](https://github.com/fluxcd/helm-controller): Kubernetes operator for building GitOps pipelines with Helm
|
||||
- [notification-controller](https://github.com/fluxcd/notification-controller): Kubernetes operator for handling inbound and outbound events
|
||||
- [image-reflector-controller](https://github.com/fluxcd/image-reflector-controller): Kubernetes operator for scanning container registries
|
||||
- [image-automation-controller](https://github.com/fluxcd/image-automation-controller): Kubernetes operator for patches container image tags in Git
|
||||
|
||||
### Understanding the code
|
||||
|
||||
To get started with developing controllers, you might want to review
|
||||
[our guide](https://fluxcd.io/flux/gitops-toolkit/source-watcher/) which
|
||||
walks you through writing a short and concise controller that watches out
|
||||
for source changes.
|
||||
|
||||
## How to run the test suite
|
||||
|
||||
Prerequisites:
|
||||
|
||||
* go >= 1.20
|
||||
* kubectl >= 1.24
|
||||
* kustomize >= 5.0
|
||||
* coreutils (on Mac OS)
|
||||
|
||||
Install the [controller-runtime/envtest](https://github.com/kubernetes-sigs/controller-runtime/tree/master/tools/setup-envtest) binaries with:
|
||||
|
||||
```bash
|
||||
make install-envtest
|
||||
```
|
||||
|
||||
Then you can run the unit tests with:
|
||||
|
||||
```bash
|
||||
make test
|
||||
```
|
||||
|
||||
After [installing Kubernetes kind](https://kind.sigs.k8s.io/docs/user/quick-start#installation) on your machine,
|
||||
create a cluster for testing with:
|
||||
|
||||
```bash
|
||||
make setup-kind
|
||||
```
|
||||
|
||||
Then you can run the end-to-end tests with:
|
||||
|
||||
```bash
|
||||
make e2e
|
||||
```
|
||||
|
||||
When the output of the Flux CLI changes, to automatically update the golden
|
||||
files used in the test, pass `-update` flag to the test as:
|
||||
|
||||
```bash
|
||||
make e2e TEST_ARGS="-update"
|
||||
```
|
||||
|
||||
Since not all packages use golden files for testing, `-update` argument must be
|
||||
passed only for the packages that use golden files. Use the variables
|
||||
`TEST_PKG_PATH` for unit tests and `E2E_TEST_PKG_PATH` for e2e tests, to set the
|
||||
path of the target test package:
|
||||
|
||||
```bash
|
||||
# Unit test
|
||||
make test TEST_PKG_PATH="./cmd/flux" TEST_ARGS="-update"
|
||||
# e2e test
|
||||
make e2e E2E_TEST_PKG_PATH="./cmd/flux" TEST_ARGS="-update"
|
||||
```
|
||||
|
||||
Teardown the e2e environment with:
|
||||
|
||||
```bash
|
||||
make cleanup-kind
|
||||
```
|
||||
|
||||
## Acceptance policy
|
||||
|
||||
These things will make a PR more likely to be accepted:
|
||||
@@ -57,7 +143,7 @@ get asked to resubmit the PR or divide the changes into more than one PR.
|
||||
|
||||
### Format of the Commit Message
|
||||
|
||||
For Source Controller we prefer the following rules for good commit messages:
|
||||
For the GitOps Toolkit controllers we prefer the following rules for good commit messages:
|
||||
|
||||
- Limit the subject to 50 characters and write as the continuation
|
||||
of the sentence "If applied, this commit will ..."
|
||||
|
||||
20
Dockerfile
Normal file
20
Dockerfile
Normal file
@@ -0,0 +1,20 @@
|
||||
FROM alpine:3.18 as builder
|
||||
|
||||
RUN apk add --no-cache ca-certificates curl
|
||||
|
||||
ARG ARCH=linux/amd64
|
||||
ARG KUBECTL_VER=1.27.3
|
||||
|
||||
RUN curl -sL https://storage.googleapis.com/kubernetes-release/release/v${KUBECTL_VER}/bin/${ARCH}/kubectl \
|
||||
-o /usr/local/bin/kubectl && chmod +x /usr/local/bin/kubectl && \
|
||||
kubectl version --client=true
|
||||
|
||||
FROM alpine:3.18 as flux-cli
|
||||
|
||||
RUN apk add --no-cache ca-certificates
|
||||
|
||||
COPY --from=builder /usr/local/bin/kubectl /usr/local/bin/
|
||||
COPY --chmod=755 flux /usr/local/bin/
|
||||
|
||||
USER 65534:65534
|
||||
ENTRYPOINT [ "flux" ]
|
||||
@@ -2,7 +2,7 @@ The maintainers are generally available in Slack at
|
||||
https://cloud-native.slack.com in #flux (https://cloud-native.slack.com/messages/CLAJ40HV3)
|
||||
(obtain an invitation at https://slack.cncf.io/).
|
||||
|
||||
In alphabetical order:
|
||||
The Flux2 maintainers team is identical with the core maintainers of the project
|
||||
as listed in
|
||||
|
||||
Hidde Beydals, Weaveworks <hidde@weave.works> (github: @hiddeco, slack: hidde)
|
||||
Stefan Prodan, Weaveworks <stefan@weave.works> (github: @stefanprodan, slack: stefanprodan)
|
||||
https://github.com/fluxcd/community/blob/main/CORE-MAINTAINERS
|
||||
|
||||
94
Makefile
94
Makefile
@@ -1,9 +1,24 @@
|
||||
VERSION?=$(shell grep 'VERSION' cmd/tk/main.go | awk '{ print $$4 }' | tr -d '"')
|
||||
VERSION?=$(shell grep 'VERSION' cmd/flux/main.go | awk '{ print $$4 }' | head -n 1 | tr -d '"')
|
||||
DEV_VERSION?=0.0.0-$(shell git rev-parse --abbrev-ref HEAD)-$(shell git rev-parse --short HEAD)-$(shell date +%s)
|
||||
EMBEDDED_MANIFESTS_TARGET=cmd/flux/.manifests.done
|
||||
TEST_KUBECONFIG?=/tmp/flux-e2e-test-kubeconfig
|
||||
# Architecture to use envtest with
|
||||
ENVTEST_ARCH ?= amd64
|
||||
|
||||
# Get the currently used golang install path (in GOPATH/bin, unless GOBIN is set)
|
||||
ifeq (,$(shell go env GOBIN))
|
||||
GOBIN=$(shell go env GOPATH)/bin
|
||||
else
|
||||
GOBIN=$(shell go env GOBIN)
|
||||
endif
|
||||
|
||||
rwildcard=$(foreach d,$(wildcard $(addsuffix *,$(1))),$(call rwildcard,$(d)/,$(2)) $(filter $(subst *,%,$(2)),$(d)))
|
||||
|
||||
all: test build
|
||||
|
||||
tidy:
|
||||
go mod tidy
|
||||
go mod tidy -compat=1.20
|
||||
cd tests/azure && go mod tidy -compat=1.20
|
||||
|
||||
fmt:
|
||||
go fmt ./...
|
||||
@@ -11,18 +26,73 @@ fmt:
|
||||
vet:
|
||||
go vet ./...
|
||||
|
||||
test: tidy fmt vet
|
||||
go test ./... -coverprofile cover.out
|
||||
setup-kind:
|
||||
kind create cluster --name=flux-e2e-test --kubeconfig=$(TEST_KUBECONFIG) --config=.github/kind/config.yaml
|
||||
kubectl --kubeconfig=$(TEST_KUBECONFIG) apply -f https://docs.projectcalico.org/v3.16/manifests/calico.yaml
|
||||
kubectl --kubeconfig=$(TEST_KUBECONFIG) -n kube-system set env daemonset/calico-node FELIX_IGNORELOOSERPF=true
|
||||
|
||||
build:
|
||||
CGO_ENABLED=0 go build -o ./bin/tk ./cmd/tk
|
||||
cleanup-kind:
|
||||
kind delete cluster --name=flux-e2e-test
|
||||
rm $(TEST_KUBECONFIG)
|
||||
|
||||
KUBEBUILDER_ASSETS?="$(shell $(ENVTEST) --arch=$(ENVTEST_ARCH) use -i $(ENVTEST_KUBERNETES_VERSION) --bin-dir=$(ENVTEST_ASSETS_DIR) -p path)"
|
||||
TEST_PKG_PATH="./..."
|
||||
test: $(EMBEDDED_MANIFESTS_TARGET) tidy fmt vet install-envtest
|
||||
KUBEBUILDER_ASSETS="$(KUBEBUILDER_ASSETS)" go test $(TEST_PKG_PATH) -coverprofile cover.out --tags=unit $(TEST_ARGS)
|
||||
|
||||
E2E_TEST_PKG_PATH="./cmd/flux/..."
|
||||
e2e: $(EMBEDDED_MANIFESTS_TARGET) tidy fmt vet
|
||||
TEST_KUBECONFIG=$(TEST_KUBECONFIG) go test $(E2E_TEST_PKG_PATH) -coverprofile e2e.cover.out --tags=e2e -v -failfast $(TEST_ARGS)
|
||||
|
||||
test-with-kind: install-envtest
|
||||
make setup-kind
|
||||
make e2e
|
||||
make cleanup-kind
|
||||
|
||||
$(EMBEDDED_MANIFESTS_TARGET): $(call rwildcard,manifests/,*.yaml *.json)
|
||||
./manifests/scripts/bundle.sh
|
||||
touch $@
|
||||
|
||||
build: $(EMBEDDED_MANIFESTS_TARGET)
|
||||
CGO_ENABLED=0 go build -ldflags="-s -w -X main.VERSION=$(VERSION)" -o ./bin/flux ./cmd/flux
|
||||
|
||||
build-dev: $(EMBEDDED_MANIFESTS_TARGET)
|
||||
CGO_ENABLED=0 go build -ldflags="-s -w -X main.VERSION=$(DEV_VERSION)" -o ./bin/flux ./cmd/flux
|
||||
|
||||
.PHONY: install
|
||||
install:
|
||||
go install cmd/tk
|
||||
|
||||
.PHONY: docs
|
||||
docs:
|
||||
mkdir -p ./docs/cmd && go run ./cmd/tk/ docgen
|
||||
CGO_ENABLED=0 go install ./cmd/flux
|
||||
|
||||
install-dev:
|
||||
CGO_ENABLED=0 go build -o /usr/local/bin ./cmd/tk
|
||||
CGO_ENABLED=0 go build -o /usr/local/bin ./cmd/flux
|
||||
|
||||
setup-bootstrap-patch:
|
||||
go run ./tests/bootstrap/main.go
|
||||
|
||||
setup-image-automation:
|
||||
cd tests/image-automation && go run main.go
|
||||
|
||||
ENVTEST_ASSETS_DIR=$(shell pwd)/testbin
|
||||
ENVTEST_KUBERNETES_VERSION?=latest
|
||||
install-envtest: setup-envtest
|
||||
mkdir -p ${ENVTEST_ASSETS_DIR}
|
||||
$(ENVTEST) use $(ENVTEST_KUBERNETES_VERSION) --arch=$(ENVTEST_ARCH) --bin-dir=$(ENVTEST_ASSETS_DIR)
|
||||
|
||||
ENVTEST = $(shell pwd)/bin/setup-envtest
|
||||
.PHONY: envtest
|
||||
setup-envtest: ## Download envtest-setup locally if necessary.
|
||||
$(call go-install-tool,$(ENVTEST),sigs.k8s.io/controller-runtime/tools/setup-envtest@latest)
|
||||
|
||||
# go-install-tool will 'go install' any package $2 and install it to $1.
|
||||
PROJECT_DIR := $(shell dirname $(abspath $(lastword $(MAKEFILE_LIST))))
|
||||
define go-install-tool
|
||||
@[ -f $(1) ] || { \
|
||||
set -e ;\
|
||||
TMP_DIR=$$(mktemp -d) ;\
|
||||
cd $$TMP_DIR ;\
|
||||
go mod init tmp ;\
|
||||
echo "Downloading $(2)" ;\
|
||||
GOBIN=$(PROJECT_DIR)/bin go install $(2) ;\
|
||||
rm -rf $$TMP_DIR ;\
|
||||
}
|
||||
endef
|
||||
|
||||
107
README.md
107
README.md
@@ -1,17 +1,100 @@
|
||||
# toolkit
|
||||
# Flux version 2
|
||||
|
||||
[](https://github.com/fluxcd/toolkit/actions)
|
||||
[](https://goreportcard.com/report/github.com/fluxcd/toolkit)
|
||||
[](https://github.com/fluxcd/toolkit/blob/master/LICENSE)
|
||||
[](https://github.com/fluxcd/toolkit/releases)
|
||||
[](https://github.com/fluxcd/flux2/releases)
|
||||
[](https://bestpractices.coreinfrastructure.org/projects/4782)
|
||||
[](https://api.securityscorecards.dev/projects/github.com/fluxcd/flux2)
|
||||
[](https://app.fossa.com/projects/custom%2B162%2Fgithub.com%2Ffluxcd%2Fflux2?ref=badge_shield)
|
||||
[](https://artifacthub.io/packages/helm/fluxcd-community/flux2)
|
||||
|
||||
Experimental toolkit for assembling CD pipelines the GitOps way.
|
||||
Flux is a tool for keeping Kubernetes clusters in sync with sources of
|
||||
configuration (like Git repositories and OCI artifacts),
|
||||
and automating updates to configuration when there is new code to deploy.
|
||||
|
||||

|
||||
Flux version 2 ("v2") is built from the ground up to use Kubernetes'
|
||||
API extension system, and to integrate with Prometheus and other core
|
||||
components of the Kubernetes ecosystem. In version 2, Flux supports
|
||||
multi-tenancy and support for syncing an arbitrary number of Git
|
||||
repositories, among other long-requested features.
|
||||
|
||||
Components:
|
||||
* [Toolkit CLI](docs/cmd/tk.md)
|
||||
* [Source Controller](https://github.com/fluxcd/source-controller)
|
||||
* [Kustomize Controller](https://github.com/fluxcd/kustomize-controller)
|
||||
Flux v2 is constructed with the [GitOps Toolkit](#gitops-toolkit), a
|
||||
set of composable APIs and specialized tools for building Continuous
|
||||
Delivery on top of Kubernetes.
|
||||
|
||||
To install the toolkit CLI, follow the [instructions](install/README.md).
|
||||
Flux is a Cloud Native Computing Foundation ([CNCF](https://www.cncf.io/)) project, used in
|
||||
production by various [organisations](https://fluxcd.io/adopters) and [cloud providers](https://fluxcd.io/ecosystem).
|
||||
|
||||
## Quickstart and documentation
|
||||
|
||||
To get started check out this [guide](https://fluxcd.io/flux/get-started/)
|
||||
on how to bootstrap Flux on Kubernetes and deploy a sample application in a GitOps manner.
|
||||
|
||||
For more comprehensive documentation, see the following guides:
|
||||
- [Ways of structuring your repositories](https://fluxcd.io/flux/guides/repository-structure/)
|
||||
- [Manage Helm Releases](https://fluxcd.io/flux/guides/helmreleases/)
|
||||
- [Automate image updates to Git](https://fluxcd.io/flux/guides/image-update/)
|
||||
- [Manage Kubernetes secrets with Mozilla SOPS](https://fluxcd.io/flux/guides/mozilla-sops/)
|
||||
|
||||
If you need help, please refer to our **[Support page](https://fluxcd.io/support/)**.
|
||||
|
||||
## GitOps Toolkit
|
||||
|
||||
The GitOps Toolkit is the set of APIs and controllers that make up the
|
||||
runtime for Flux v2. The APIs comprise Kubernetes custom resources,
|
||||
which can be created and updated by a cluster user, or by other
|
||||
automation tooling.
|
||||
|
||||
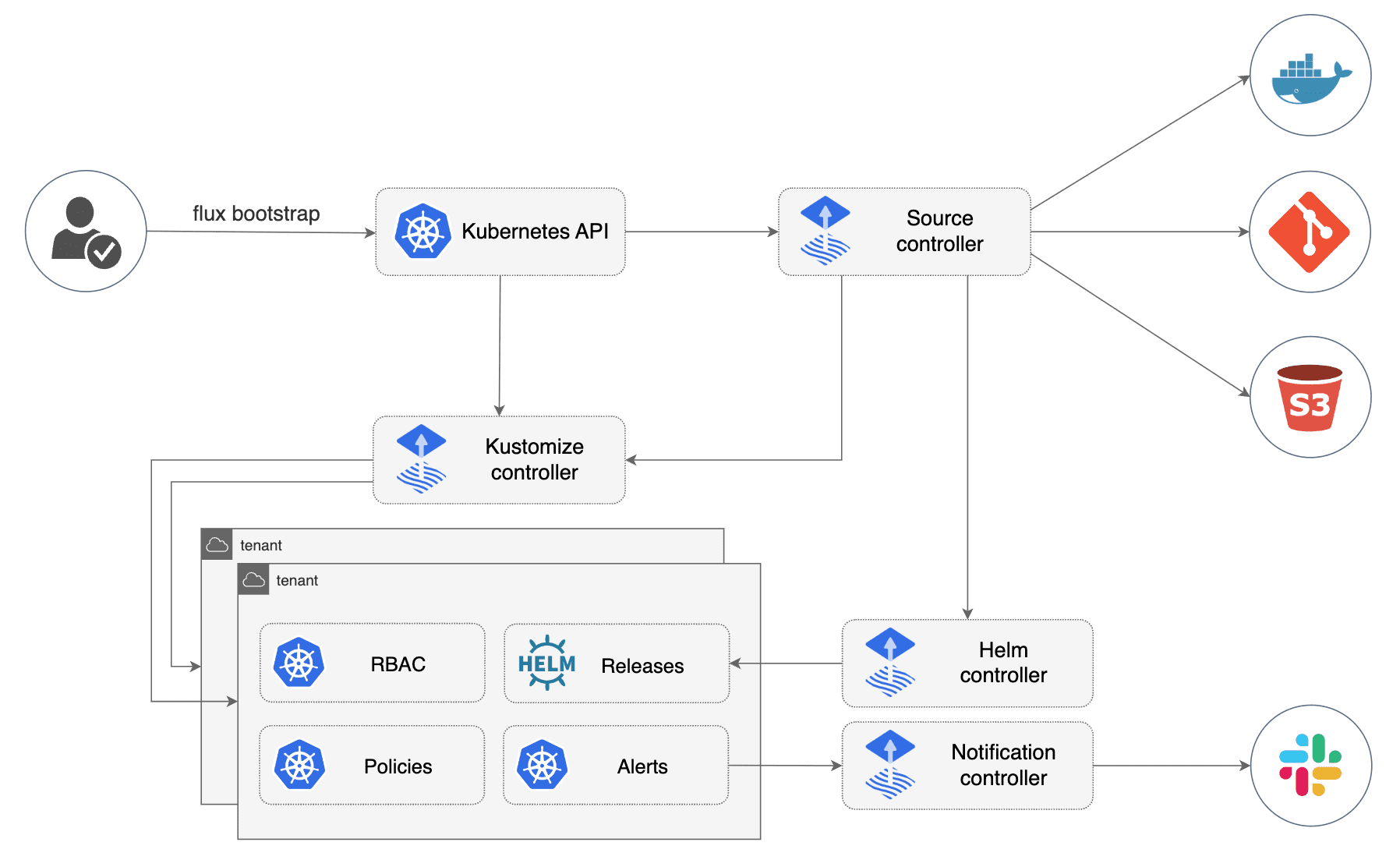
|
||||
|
||||
You can use the toolkit to extend Flux, or to build your own systems
|
||||
for continuous delivery -- see [the developer
|
||||
guides](https://fluxcd.io/flux/gitops-toolkit/source-watcher/).
|
||||
|
||||
### Components
|
||||
|
||||
- [Source Controller](https://fluxcd.io/flux/components/source/)
|
||||
- [GitRepository CRD](https://fluxcd.io/flux/components/source/gitrepositories/)
|
||||
- [OCIRepository CRD](https://fluxcd.io/flux/components/source/ocirepositories/)
|
||||
- [HelmRepository CRD](https://fluxcd.io/flux/components/source/helmrepositories/)
|
||||
- [HelmChart CRD](https://fluxcd.io/flux/components/source/helmcharts/)
|
||||
- [Bucket CRD](https://fluxcd.io/flux/components/source/buckets/)
|
||||
- [Kustomize Controller](https://fluxcd.io/flux/components/kustomize/)
|
||||
- [Kustomization CRD](https://fluxcd.io/flux/components/kustomize/kustomization/)
|
||||
- [Helm Controller](https://fluxcd.io/flux/components/helm/)
|
||||
- [HelmRelease CRD](https://fluxcd.io/flux/components/helm/helmreleases/)
|
||||
- [Notification Controller](https://fluxcd.io/flux/components/notification/)
|
||||
- [Provider CRD](https://fluxcd.io/flux/components/notification/provider/)
|
||||
- [Alert CRD](https://fluxcd.io/flux/components/notification/alert/)
|
||||
- [Receiver CRD](https://fluxcd.io/flux/components/notification/receiver/)
|
||||
- [Image Automation Controllers](https://fluxcd.io/flux/components/image/)
|
||||
- [ImageRepository CRD](https://fluxcd.io/flux/components/image/imagerepositories/)
|
||||
- [ImagePolicy CRD](https://fluxcd.io/flux/components/image/imagepolicies/)
|
||||
- [ImageUpdateAutomation CRD](https://fluxcd.io/flux/components/image/imageupdateautomations/)
|
||||
|
||||
## Community
|
||||
|
||||
Need help or want to contribute? Please see the links below. The Flux project is always looking for
|
||||
new contributors and there are a multitude of ways to get involved.
|
||||
|
||||
- Getting Started?
|
||||
- Look at our [Get Started guide](https://fluxcd.io/flux/get-started/) and give us feedback
|
||||
- Need help?
|
||||
- First: Ask questions on our [GH Discussions page](https://github.com/fluxcd/flux2/discussions).
|
||||
- Second: Talk to us in the #flux channel on [CNCF Slack](https://slack.cncf.io/).
|
||||
- Please follow our [Support Guidelines](https://fluxcd.io/support/)
|
||||
(in short: be nice, be respectful of volunteers' time, understand that maintainers and
|
||||
contributors cannot respond to all DMs, and keep discussions in the public #flux channel as much as possible).
|
||||
- Have feature proposals or want to contribute?
|
||||
- Propose features on our [GitHub Discussions page](https://github.com/fluxcd/flux2/discussions).
|
||||
- Join our upcoming dev meetings ([meeting access and agenda](https://docs.google.com/document/d/1l_M0om0qUEN_NNiGgpqJ2tvsF2iioHkaARDeh6b70B0/view)).
|
||||
- [Join the flux-dev mailing list](https://lists.cncf.io/g/cncf-flux-dev).
|
||||
- Check out [how to contribute](CONTRIBUTING.md) to the project.
|
||||
- Check out the [project roadmap](https://fluxcd.io/roadmap/).
|
||||
|
||||
### Events
|
||||
|
||||
Check out our **[events calendar](https://fluxcd.io/#calendar)**,
|
||||
both with upcoming talks, events and meetings you can attend.
|
||||
Or view the **[resources section](https://fluxcd.io/resources)**
|
||||
with past events videos you can watch.
|
||||
|
||||
We look forward to seeing you with us!
|
||||
|
||||
216
action/README.md
Normal file
216
action/README.md
Normal file
@@ -0,0 +1,216 @@
|
||||
# Flux GitHub Action
|
||||
|
||||
Usage:
|
||||
|
||||
```yaml
|
||||
steps:
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
- name: Run Flux commands
|
||||
run: flux -v
|
||||
```
|
||||
|
||||
The latest stable version of the `flux` binary is downloaded from
|
||||
GitHub [releases](https://github.com/fluxcd/flux2/releases)
|
||||
and placed at `/usr/local/bin/flux`.
|
||||
|
||||
Note that this action can only be used on GitHub **Linux** runners.
|
||||
You can change the arch (defaults to `amd64`) with:
|
||||
|
||||
```yaml
|
||||
steps:
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
with:
|
||||
arch: arm64 # can be amd64, arm64 or arm
|
||||
```
|
||||
|
||||
You can download a specific version with:
|
||||
|
||||
```yaml
|
||||
steps:
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
with:
|
||||
version: 0.32.0
|
||||
```
|
||||
|
||||
You can also authenticate against the GitHub API using GitHub Actions' `GITHUB_TOKEN` secret.
|
||||
|
||||
For more information, please [read about the GitHub token secret](https://docs.github.com/en/actions/security-guides/automatic-token-authentication#about-the-github_token-secret).
|
||||
|
||||
```yaml
|
||||
steps:
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
with:
|
||||
token: ${{ secrets.GITHUB_TOKEN }}
|
||||
```
|
||||
|
||||
This is useful if you are seeing failures on shared runners, those failures are usually API limits being hit.
|
||||
|
||||
### Automate Flux updates
|
||||
|
||||
Example workflow for updating Flux's components generated with `flux bootstrap --path=clusters/production`:
|
||||
|
||||
```yaml
|
||||
name: update-flux
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
schedule:
|
||||
- cron: "0 * * * *"
|
||||
|
||||
permissions:
|
||||
contents: write
|
||||
pull-requests: write
|
||||
|
||||
jobs:
|
||||
components:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: Check out code
|
||||
uses: actions/checkout@v3
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
- name: Check for updates
|
||||
id: update
|
||||
run: |
|
||||
flux install \
|
||||
--export > ./clusters/production/flux-system/gotk-components.yaml
|
||||
|
||||
VERSION="$(flux -v)"
|
||||
echo "flux_version=$VERSION" >> $GITHUB_OUTPUT
|
||||
- name: Create Pull Request
|
||||
uses: peter-evans/create-pull-request@v4
|
||||
with:
|
||||
token: ${{ secrets.GITHUB_TOKEN }}
|
||||
branch: update-flux
|
||||
commit-message: Update to ${{ steps.update.outputs.flux_version }}
|
||||
title: Update to ${{ steps.update.outputs.flux_version }}
|
||||
body: |
|
||||
${{ steps.update.outputs.flux_version }}
|
||||
```
|
||||
|
||||
### Push Kubernetes manifests to container registries
|
||||
|
||||
Example workflow for publishing Kubernetes manifests bundled as OCI artifacts to GitHub Container Registry:
|
||||
|
||||
```yaml
|
||||
name: push-artifact-staging
|
||||
|
||||
on:
|
||||
push:
|
||||
branches:
|
||||
- 'main'
|
||||
|
||||
permissions:
|
||||
packages: write # needed for ghcr.io access
|
||||
|
||||
env:
|
||||
OCI_REPO: "oci://ghcr.io/my-org/manifests/${{ github.event.repository.name }}"
|
||||
|
||||
jobs:
|
||||
kubernetes:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v3
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
- name: Login to GHCR
|
||||
uses: docker/login-action@v2
|
||||
with:
|
||||
registry: ghcr.io
|
||||
username: ${{ github.actor }}
|
||||
password: ${{ secrets.GITHUB_TOKEN }}
|
||||
- name: Generate manifests
|
||||
run: |
|
||||
kustomize build ./manifests/staging > ./deploy/app.yaml
|
||||
- name: Push manifests
|
||||
run: |
|
||||
flux push artifact $OCI_REPO:$(git rev-parse --short HEAD) \
|
||||
--path="./deploy" \
|
||||
--source="$(git config --get remote.origin.url)" \
|
||||
--revision="$(git branch --show-current)@sha1:$(git rev-parse HEAD)"
|
||||
- name: Deploy manifests to staging
|
||||
run: |
|
||||
flux tag artifact $OCI_REPO:$(git rev-parse --short HEAD) --tag staging
|
||||
```
|
||||
|
||||
### Push and sign Kubernetes manifests to container registries
|
||||
|
||||
Example workflow for publishing Kubernetes manifests bundled as OCI artifacts
|
||||
which are signed with Cosign and GitHub OIDC:
|
||||
|
||||
```yaml
|
||||
name: push-sign-artifact
|
||||
|
||||
on:
|
||||
push:
|
||||
branches:
|
||||
- 'main'
|
||||
|
||||
permissions:
|
||||
packages: write # needed for ghcr.io access
|
||||
id-token: write # needed for keyless signing
|
||||
|
||||
env:
|
||||
OCI_REPO: "oci://ghcr.io/my-org/manifests/${{ github.event.repository.name }}"
|
||||
|
||||
jobs:
|
||||
kubernetes:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v3
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
- name: Setup Cosign
|
||||
uses: sigstore/cosign-installer@main
|
||||
- name: Login to GHCR
|
||||
uses: docker/login-action@v2
|
||||
with:
|
||||
registry: ghcr.io
|
||||
username: ${{ github.actor }}
|
||||
password: ${{ secrets.GITHUB_TOKEN }}
|
||||
- name: Push and sign manifests
|
||||
run: |
|
||||
digest_url=$(flux push artifact \
|
||||
$OCI_REPO:$(git rev-parse --short HEAD) \
|
||||
--path="./manifests" \
|
||||
--source="$(git config --get remote.origin.url)" \
|
||||
--revision="$(git branch --show-current)@sha1:$(git rev-parse HEAD)" |\
|
||||
jq -r '. | .repository + "@" + .digest')
|
||||
|
||||
cosign sign $digest_url
|
||||
```
|
||||
|
||||
### End-to-end testing
|
||||
|
||||
Example workflow for running Flux in Kubernetes Kind:
|
||||
|
||||
```yaml
|
||||
name: e2e
|
||||
|
||||
on:
|
||||
push:
|
||||
branches:
|
||||
- '*'
|
||||
|
||||
jobs:
|
||||
kubernetes:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v3
|
||||
- name: Setup Flux CLI
|
||||
uses: fluxcd/flux2/action@main
|
||||
- name: Setup Kubernetes Kind
|
||||
uses: engineerd/setup-kind@v0.5.0
|
||||
- name: Install Flux in Kubernetes Kind
|
||||
run: flux install
|
||||
```
|
||||
|
||||
A complete e2e testing workflow is available here
|
||||
[flux2-kustomize-helm-example](https://github.com/fluxcd/flux2-kustomize-helm-example/blob/main/.github/workflows/e2e.yaml)
|
||||
64
action/action.yml
Normal file
64
action/action.yml
Normal file
@@ -0,0 +1,64 @@
|
||||
name: Setup Flux CLI
|
||||
description: A GitHub Action for running Flux commands
|
||||
author: Stefan Prodan
|
||||
branding:
|
||||
color: blue
|
||||
icon: command
|
||||
inputs:
|
||||
version:
|
||||
description: "Flux version e.g. 0.8.0 (defaults to latest stable release)"
|
||||
required: false
|
||||
arch:
|
||||
description: "arch can be amd64, arm64 or arm"
|
||||
required: true
|
||||
default: "amd64"
|
||||
bindir:
|
||||
description: "Optional location of the Flux binary. Will not use sudo if set. Updates System Path."
|
||||
required: false
|
||||
token:
|
||||
description: "GitHub Token used to authentication against the API (generally only needed to prevent quota limit errors)"
|
||||
required: false
|
||||
runs:
|
||||
using: composite
|
||||
steps:
|
||||
- name: "Download flux binary to tmp"
|
||||
shell: bash
|
||||
run: |
|
||||
ARCH=${{ inputs.arch }}
|
||||
VERSION=${{ inputs.version }}
|
||||
TOKEN=${{ inputs.token }}
|
||||
|
||||
if [ -z "${VERSION}" ]; then
|
||||
if [ -n "${TOKEN}" ]; then
|
||||
VERSION_SLUG=$(curl https://api.github.com/repos/fluxcd/flux2/releases/latest --silent --location --header "Authorization: token ${TOKEN}" | grep tag_name)
|
||||
else
|
||||
# With no GITHUB_TOKEN you will experience occasional failures due to rate limiting
|
||||
# Ref: https://github.com/fluxcd/flux2/issues/3509#issuecomment-1400820992
|
||||
VERSION_SLUG=$(curl https://api.github.com/repos/fluxcd/flux2/releases/latest --silent --location | grep tag_name)
|
||||
fi
|
||||
|
||||
VERSION=$(echo "${VERSION_SLUG}" | sed -E 's/.*"([^"]+)".*/\1/' | cut -c 2-)
|
||||
fi
|
||||
|
||||
BIN_URL="https://github.com/fluxcd/flux2/releases/download/v${VERSION}/flux_${VERSION}_linux_${ARCH}.tar.gz"
|
||||
curl --silent --fail --location "${BIN_URL}" --output /tmp/flux.tar.gz
|
||||
mkdir -p /tmp/flux
|
||||
tar -C /tmp/flux/ -zxvf /tmp/flux.tar.gz
|
||||
- name: "Copy Flux binary to execute location"
|
||||
shell: bash
|
||||
run: |
|
||||
BINDIR=${{ inputs.bindir }}
|
||||
if [ -z "${BINDIR}" ]; then
|
||||
sudo cp /tmp/flux/flux /usr/local/bin
|
||||
else
|
||||
cp /tmp/flux/flux "${BINDIR}"
|
||||
echo "${BINDIR}" >> $GITHUB_PATH
|
||||
fi
|
||||
- name: "Cleanup tmp"
|
||||
shell: bash
|
||||
run: |
|
||||
rm -rf /tmp/flux/ /tmp/flux.tar.gz
|
||||
- name: "Verify correct installation of binary"
|
||||
shell: bash
|
||||
run: |
|
||||
flux -v
|
||||
57
cmd/flux/alert.go
Normal file
57
cmd/flux/alert.go
Normal file
@@ -0,0 +1,57 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
// notificationv1.Alert
|
||||
|
||||
var alertType = apiType{
|
||||
kind: notificationv1.AlertKind,
|
||||
humanKind: "alert",
|
||||
groupVersion: notificationv1.GroupVersion,
|
||||
}
|
||||
|
||||
type alertAdapter struct {
|
||||
*notificationv1.Alert
|
||||
}
|
||||
|
||||
func (a alertAdapter) asClientObject() client.Object {
|
||||
return a.Alert
|
||||
}
|
||||
|
||||
func (a alertAdapter) deepCopyClientObject() client.Object {
|
||||
return a.Alert.DeepCopy()
|
||||
}
|
||||
|
||||
// notificationv1.Alert
|
||||
|
||||
type alertListAdapter struct {
|
||||
*notificationv1.AlertList
|
||||
}
|
||||
|
||||
func (a alertListAdapter) asClientList() client.ObjectList {
|
||||
return a.AlertList
|
||||
}
|
||||
|
||||
func (a alertListAdapter) len() int {
|
||||
return len(a.AlertList.Items)
|
||||
}
|
||||
57
cmd/flux/alert_provider.go
Normal file
57
cmd/flux/alert_provider.go
Normal file
@@ -0,0 +1,57 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
// notificationv1.Provider
|
||||
|
||||
var alertProviderType = apiType{
|
||||
kind: notificationv1.ProviderKind,
|
||||
humanKind: "alert provider",
|
||||
groupVersion: notificationv1.GroupVersion,
|
||||
}
|
||||
|
||||
type alertProviderAdapter struct {
|
||||
*notificationv1.Provider
|
||||
}
|
||||
|
||||
func (a alertProviderAdapter) asClientObject() client.Object {
|
||||
return a.Provider
|
||||
}
|
||||
|
||||
func (a alertProviderAdapter) deepCopyClientObject() client.Object {
|
||||
return a.Provider.DeepCopy()
|
||||
}
|
||||
|
||||
// notificationv1.Provider
|
||||
|
||||
type alertProviderListAdapter struct {
|
||||
*notificationv1.ProviderList
|
||||
}
|
||||
|
||||
func (a alertProviderListAdapter) asClientList() client.ObjectList {
|
||||
return a.ProviderList
|
||||
}
|
||||
|
||||
func (a alertProviderListAdapter) len() int {
|
||||
return len(a.ProviderList.Items)
|
||||
}
|
||||
190
cmd/flux/bootstrap.go
Normal file
190
cmd/flux/bootstrap.go
Normal file
@@ -0,0 +1,190 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"crypto/elliptic"
|
||||
"fmt"
|
||||
"strings"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
)
|
||||
|
||||
var bootstrapCmd = &cobra.Command{
|
||||
Use: "bootstrap",
|
||||
Short: "Deploy Flux on a cluster the GitOps way.",
|
||||
Long: `The bootstrap sub-commands push the Flux manifests to a Git repository
|
||||
and deploy Flux on the cluster.`,
|
||||
}
|
||||
|
||||
type bootstrapFlags struct {
|
||||
version string
|
||||
logLevel flags.LogLevel
|
||||
|
||||
branch string
|
||||
recurseSubmodules bool
|
||||
manifestsPath string
|
||||
|
||||
defaultComponents []string
|
||||
extraComponents []string
|
||||
requiredComponents []string
|
||||
|
||||
registry string
|
||||
imagePullSecret string
|
||||
|
||||
secretName string
|
||||
tokenAuth bool
|
||||
keyAlgorithm flags.PublicKeyAlgorithm
|
||||
keyRSABits flags.RSAKeyBits
|
||||
keyECDSACurve flags.ECDSACurve
|
||||
sshHostname string
|
||||
caFile string
|
||||
privateKeyFile string
|
||||
|
||||
watchAllNamespaces bool
|
||||
networkPolicy bool
|
||||
clusterDomain string
|
||||
tolerationKeys []string
|
||||
|
||||
authorName string
|
||||
authorEmail string
|
||||
|
||||
gpgKeyRingPath string
|
||||
gpgPassphrase string
|
||||
gpgKeyID string
|
||||
|
||||
commitMessageAppendix string
|
||||
}
|
||||
|
||||
const (
|
||||
bootstrapDefaultBranch = "main"
|
||||
)
|
||||
|
||||
var bootstrapArgs = NewBootstrapFlags()
|
||||
|
||||
func init() {
|
||||
bootstrapCmd.PersistentFlags().StringVarP(&bootstrapArgs.version, "version", "v", "",
|
||||
"toolkit version, when specified the manifests are downloaded from https://github.com/fluxcd/flux2/releases")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringSliceVar(&bootstrapArgs.defaultComponents, "components", rootArgs.defaults.Components,
|
||||
"list of components, accepts comma-separated values")
|
||||
bootstrapCmd.PersistentFlags().StringSliceVar(&bootstrapArgs.extraComponents, "components-extra", nil,
|
||||
"list of components in addition to those supplied or defaulted, accepts values such as 'image-reflector-controller,image-automation-controller'")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.registry, "registry", "ghcr.io/fluxcd",
|
||||
"container registry where the Flux controller images are published")
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.imagePullSecret, "image-pull-secret", "",
|
||||
"Kubernetes secret name used for pulling the controller images from a private registry")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.branch, "branch", bootstrapDefaultBranch, "Git branch")
|
||||
bootstrapCmd.PersistentFlags().BoolVar(&bootstrapArgs.recurseSubmodules, "recurse-submodules", false,
|
||||
"when enabled, configures the GitRepository source to initialize and include Git submodules in the artifact it produces")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.manifestsPath, "manifests", "", "path to the manifest directory")
|
||||
|
||||
bootstrapCmd.PersistentFlags().BoolVar(&bootstrapArgs.watchAllNamespaces, "watch-all-namespaces", true,
|
||||
"watch for custom resources in all namespaces, if set to false it will only watch the namespace where the Flux controllers are installed")
|
||||
bootstrapCmd.PersistentFlags().BoolVar(&bootstrapArgs.networkPolicy, "network-policy", true,
|
||||
"setup Kubernetes network policies to deny ingress access to the Flux controllers from other namespaces")
|
||||
bootstrapCmd.PersistentFlags().BoolVar(&bootstrapArgs.tokenAuth, "token-auth", false,
|
||||
"when enabled, the personal access token will be used instead of the SSH deploy key")
|
||||
bootstrapCmd.PersistentFlags().Var(&bootstrapArgs.logLevel, "log-level", bootstrapArgs.logLevel.Description())
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.clusterDomain, "cluster-domain", rootArgs.defaults.ClusterDomain, "internal cluster domain")
|
||||
bootstrapCmd.PersistentFlags().StringSliceVar(&bootstrapArgs.tolerationKeys, "toleration-keys", nil,
|
||||
"list of toleration keys used to schedule the controller pods onto nodes with matching taints")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.secretName, "secret-name", rootArgs.defaults.Namespace, "name of the secret the sync credentials can be found in or stored to")
|
||||
bootstrapCmd.PersistentFlags().Var(&bootstrapArgs.keyAlgorithm, "ssh-key-algorithm", bootstrapArgs.keyAlgorithm.Description())
|
||||
bootstrapCmd.PersistentFlags().Var(&bootstrapArgs.keyRSABits, "ssh-rsa-bits", bootstrapArgs.keyRSABits.Description())
|
||||
bootstrapCmd.PersistentFlags().Var(&bootstrapArgs.keyECDSACurve, "ssh-ecdsa-curve", bootstrapArgs.keyECDSACurve.Description())
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.sshHostname, "ssh-hostname", "", "SSH hostname, to be used when the SSH host differs from the HTTPS one")
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.caFile, "ca-file", "", "path to TLS CA file used for validating self-signed certificates")
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.privateKeyFile, "private-key-file", "", "path to a private key file used for authenticating to the Git SSH server")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.authorName, "author-name", "Flux", "author name for Git commits")
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.authorEmail, "author-email", "", "author email for Git commits")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.gpgKeyRingPath, "gpg-key-ring", "", "path to GPG key ring for signing commits")
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.gpgPassphrase, "gpg-passphrase", "", "passphrase for decrypting GPG private key")
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.gpgKeyID, "gpg-key-id", "", "key id for selecting a particular key")
|
||||
|
||||
bootstrapCmd.PersistentFlags().StringVar(&bootstrapArgs.commitMessageAppendix, "commit-message-appendix", "", "string to add to the commit messages, e.g. '[ci skip]'")
|
||||
|
||||
bootstrapCmd.PersistentFlags().MarkHidden("manifests")
|
||||
|
||||
rootCmd.AddCommand(bootstrapCmd)
|
||||
}
|
||||
|
||||
func NewBootstrapFlags() bootstrapFlags {
|
||||
return bootstrapFlags{
|
||||
logLevel: flags.LogLevel(rootArgs.defaults.LogLevel),
|
||||
requiredComponents: []string{"source-controller", "kustomize-controller"},
|
||||
keyAlgorithm: flags.PublicKeyAlgorithm(sourcesecret.ECDSAPrivateKeyAlgorithm),
|
||||
keyRSABits: 2048,
|
||||
keyECDSACurve: flags.ECDSACurve{Curve: elliptic.P384()},
|
||||
}
|
||||
}
|
||||
|
||||
func bootstrapComponents() []string {
|
||||
return append(bootstrapArgs.defaultComponents, bootstrapArgs.extraComponents...)
|
||||
}
|
||||
|
||||
func buildEmbeddedManifestBase() (string, error) {
|
||||
if !isEmbeddedVersion(bootstrapArgs.version) {
|
||||
return "", nil
|
||||
}
|
||||
tmpBaseDir, err := manifestgen.MkdirTempAbs("", "flux-manifests-")
|
||||
if err != nil {
|
||||
return "", err
|
||||
}
|
||||
if err := writeEmbeddedManifests(tmpBaseDir); err != nil {
|
||||
return "", err
|
||||
}
|
||||
return tmpBaseDir, nil
|
||||
}
|
||||
|
||||
func bootstrapValidate() error {
|
||||
components := bootstrapComponents()
|
||||
for _, component := range bootstrapArgs.requiredComponents {
|
||||
if !utils.ContainsItemString(components, component) {
|
||||
return fmt.Errorf("component %s is required", component)
|
||||
}
|
||||
}
|
||||
|
||||
if err := utils.ValidateComponents(components); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func mapTeamSlice(s []string, defaultPermission string) map[string]string {
|
||||
m := make(map[string]string, len(s))
|
||||
for _, v := range s {
|
||||
m[v] = defaultPermission
|
||||
if s := strings.Split(v, ":"); len(s) == 2 {
|
||||
m[s[0]] = s[1]
|
||||
}
|
||||
}
|
||||
|
||||
return m
|
||||
}
|
||||
290
cmd/flux/bootstrap_bitbucket_server.go
Normal file
290
cmd/flux/bootstrap_bitbucket_server.go
Normal file
@@ -0,0 +1,290 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"os"
|
||||
"time"
|
||||
|
||||
"github.com/fluxcd/pkg/git"
|
||||
"github.com/fluxcd/pkg/git/gogit"
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap/provider"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/install"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sync"
|
||||
)
|
||||
|
||||
var bootstrapBServerCmd = &cobra.Command{
|
||||
Use: "bitbucket-server",
|
||||
Short: "Deploy Flux on a cluster connected to a Bitbucket Server repository",
|
||||
Long: `The bootstrap bitbucket-server command creates the Bitbucket Server repository if it doesn't exists and
|
||||
commits the Flux manifests to the master branch.
|
||||
Then it configures the target cluster to synchronize with the repository.
|
||||
If the Flux components are present on the cluster,
|
||||
the bootstrap command will perform an upgrade if needed.`,
|
||||
Example: ` # Create a Bitbucket Server API token and export it as an env var
|
||||
export BITBUCKET_TOKEN=<my-token>
|
||||
|
||||
# Run bootstrap for a private repository using HTTPS token authentication
|
||||
flux bootstrap bitbucket-server --owner=<project> --username=<user> --repository=<repository name> --hostname=<domain> --token-auth --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a private repository using SSH authentication
|
||||
flux bootstrap bitbucket-server --owner=<project> --username=<user> --repository=<repository name> --hostname=<domain> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a public repository on a personal account
|
||||
flux bootstrap bitbucket-server --owner=<user> --repository=<repository name> --private=false --personal --hostname=<domain> --token-auth --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a an existing repository with a branch named main
|
||||
flux bootstrap bitbucket-server --owner=<project> --username=<user> --repository=<repository name> --branch=main --hostname=<domain> --token-auth --path=clusters/my-cluster`,
|
||||
RunE: bootstrapBServerCmdRun,
|
||||
}
|
||||
|
||||
const (
|
||||
bServerDefaultPermission = "push"
|
||||
bServerTokenEnvVar = "BITBUCKET_TOKEN"
|
||||
)
|
||||
|
||||
type bServerFlags struct {
|
||||
owner string
|
||||
repository string
|
||||
interval time.Duration
|
||||
personal bool
|
||||
username string
|
||||
private bool
|
||||
hostname string
|
||||
path flags.SafeRelativePath
|
||||
teams []string
|
||||
readWriteKey bool
|
||||
reconcile bool
|
||||
}
|
||||
|
||||
var bServerArgs bServerFlags
|
||||
|
||||
func init() {
|
||||
bootstrapBServerCmd.Flags().StringVar(&bServerArgs.owner, "owner", "", "Bitbucket Server user or project name")
|
||||
bootstrapBServerCmd.Flags().StringVar(&bServerArgs.repository, "repository", "", "Bitbucket Server repository name")
|
||||
bootstrapBServerCmd.Flags().StringSliceVar(&bServerArgs.teams, "group", []string{}, "Bitbucket Server groups to be given write access (also accepts comma-separated values)")
|
||||
bootstrapBServerCmd.Flags().BoolVar(&bServerArgs.personal, "personal", false, "if true, the owner is assumed to be a Bitbucket Server user; otherwise a group")
|
||||
bootstrapBServerCmd.Flags().StringVarP(&bServerArgs.username, "username", "u", "git", "authentication username")
|
||||
bootstrapBServerCmd.Flags().BoolVar(&bServerArgs.private, "private", true, "if true, the repository is setup or configured as private")
|
||||
bootstrapBServerCmd.Flags().DurationVar(&bServerArgs.interval, "interval", time.Minute, "sync interval")
|
||||
bootstrapBServerCmd.Flags().StringVar(&bServerArgs.hostname, "hostname", "", "Bitbucket Server hostname")
|
||||
bootstrapBServerCmd.Flags().Var(&bServerArgs.path, "path", "path relative to the repository root, when specified the cluster sync will be scoped to this path")
|
||||
bootstrapBServerCmd.Flags().BoolVar(&bServerArgs.readWriteKey, "read-write-key", false, "if true, the deploy key is configured with read/write permissions")
|
||||
bootstrapBServerCmd.Flags().BoolVar(&bServerArgs.reconcile, "reconcile", false, "if true, the configured options are also reconciled if the repository already exists")
|
||||
|
||||
bootstrapCmd.AddCommand(bootstrapBServerCmd)
|
||||
}
|
||||
|
||||
func bootstrapBServerCmdRun(cmd *cobra.Command, args []string) error {
|
||||
bitbucketToken := os.Getenv(bServerTokenEnvVar)
|
||||
if bitbucketToken == "" {
|
||||
var err error
|
||||
bitbucketToken, err = readPasswordFromStdin("Please enter your Bitbucket personal access token (PAT): ")
|
||||
if err != nil {
|
||||
return fmt.Errorf("could not read token: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
if bServerArgs.hostname == "" {
|
||||
return fmt.Errorf("invalid hostname %q", bServerArgs.hostname)
|
||||
}
|
||||
|
||||
if err := bootstrapValidate(); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Manifest base
|
||||
if ver, err := getVersion(bootstrapArgs.version); err != nil {
|
||||
return err
|
||||
} else {
|
||||
bootstrapArgs.version = ver
|
||||
}
|
||||
manifestsBase, err := buildEmbeddedManifestBase()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(manifestsBase)
|
||||
|
||||
user := bServerArgs.username
|
||||
if bServerArgs.personal {
|
||||
user = bServerArgs.owner
|
||||
}
|
||||
|
||||
var caBundle []byte
|
||||
if bootstrapArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(bootstrapArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
// Build Bitbucket Server provider
|
||||
providerCfg := provider.Config{
|
||||
Provider: provider.GitProviderStash,
|
||||
Hostname: bServerArgs.hostname,
|
||||
Username: user,
|
||||
Token: bitbucketToken,
|
||||
CaBundle: caBundle,
|
||||
}
|
||||
|
||||
providerClient, err := provider.BuildGitProvider(providerCfg)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Lazy go-git repository
|
||||
tmpDir, err := manifestgen.MkdirTempAbs("", "flux-bootstrap-")
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create temporary working dir: %w", err)
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
clientOpts := []gogit.ClientOption{gogit.WithDiskStorage(), gogit.WithFallbackToDefaultKnownHosts()}
|
||||
gitClient, err := gogit.NewClient(tmpDir, &git.AuthOptions{
|
||||
Transport: git.HTTPS,
|
||||
Username: user,
|
||||
Password: bitbucketToken,
|
||||
CAFile: caBundle,
|
||||
}, clientOpts...)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create a Git client: %w", err)
|
||||
}
|
||||
|
||||
// Install manifest config
|
||||
installOptions := install.Options{
|
||||
BaseURL: rootArgs.defaults.BaseURL,
|
||||
Version: bootstrapArgs.version,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Components: bootstrapComponents(),
|
||||
Registry: bootstrapArgs.registry,
|
||||
ImagePullSecret: bootstrapArgs.imagePullSecret,
|
||||
WatchAllNamespaces: bootstrapArgs.watchAllNamespaces,
|
||||
NetworkPolicy: bootstrapArgs.networkPolicy,
|
||||
LogLevel: bootstrapArgs.logLevel.String(),
|
||||
NotificationController: rootArgs.defaults.NotificationController,
|
||||
ManifestFile: rootArgs.defaults.ManifestFile,
|
||||
Timeout: rootArgs.timeout,
|
||||
TargetPath: bServerArgs.path.ToSlash(),
|
||||
ClusterDomain: bootstrapArgs.clusterDomain,
|
||||
TolerationKeys: bootstrapArgs.tolerationKeys,
|
||||
}
|
||||
if customBaseURL := bootstrapArgs.manifestsPath; customBaseURL != "" {
|
||||
installOptions.BaseURL = customBaseURL
|
||||
}
|
||||
|
||||
// Source generation and secret config
|
||||
secretOpts := sourcesecret.Options{
|
||||
Name: bootstrapArgs.secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
TargetPath: bServerArgs.path.String(),
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
if bootstrapArgs.tokenAuth {
|
||||
if bServerArgs.personal {
|
||||
secretOpts.Username = bServerArgs.owner
|
||||
} else {
|
||||
secretOpts.Username = bServerArgs.username
|
||||
}
|
||||
secretOpts.Password = bitbucketToken
|
||||
secretOpts.CAFile = caBundle
|
||||
} else {
|
||||
keypair, err := sourcesecret.LoadKeyPairFromPath(bootstrapArgs.privateKeyFile, gitArgs.password)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
secretOpts.Keypair = keypair
|
||||
secretOpts.PrivateKeyAlgorithm = sourcesecret.PrivateKeyAlgorithm(bootstrapArgs.keyAlgorithm)
|
||||
secretOpts.RSAKeyBits = int(bootstrapArgs.keyRSABits)
|
||||
secretOpts.ECDSACurve = bootstrapArgs.keyECDSACurve.Curve
|
||||
|
||||
secretOpts.SSHHostname = bServerArgs.hostname
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
secretOpts.SSHHostname = bootstrapArgs.sshHostname
|
||||
}
|
||||
}
|
||||
|
||||
// Sync manifest config
|
||||
syncOpts := sync.Options{
|
||||
Interval: bServerArgs.interval,
|
||||
Name: *kubeconfigArgs.Namespace,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Branch: bootstrapArgs.branch,
|
||||
Secret: bootstrapArgs.secretName,
|
||||
TargetPath: bServerArgs.path.ToSlash(),
|
||||
ManifestFile: sync.MakeDefaultOptions().ManifestFile,
|
||||
RecurseSubmodules: bootstrapArgs.recurseSubmodules,
|
||||
}
|
||||
|
||||
entityList, err := bootstrap.LoadEntityListFromPath(bootstrapArgs.gpgKeyRingPath)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Bootstrap config
|
||||
|
||||
bootstrapOpts := []bootstrap.GitProviderOption{
|
||||
bootstrap.WithProviderRepository(bServerArgs.owner, bServerArgs.repository, bServerArgs.personal),
|
||||
bootstrap.WithBranch(bootstrapArgs.branch),
|
||||
bootstrap.WithBootstrapTransportType("https"),
|
||||
bootstrap.WithSignature(bootstrapArgs.authorName, bootstrapArgs.authorEmail),
|
||||
bootstrap.WithCommitMessageAppendix(bootstrapArgs.commitMessageAppendix),
|
||||
bootstrap.WithProviderTeamPermissions(mapTeamSlice(bServerArgs.teams, bServerDefaultPermission)),
|
||||
bootstrap.WithReadWriteKeyPermissions(bServerArgs.readWriteKey),
|
||||
bootstrap.WithKubeconfig(kubeconfigArgs, kubeclientOptions),
|
||||
bootstrap.WithLogger(logger),
|
||||
bootstrap.WithGitCommitSigning(entityList, bootstrapArgs.gpgPassphrase, bootstrapArgs.gpgKeyID),
|
||||
}
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithSSHHostname(bootstrapArgs.sshHostname))
|
||||
}
|
||||
if bootstrapArgs.tokenAuth {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithSyncTransportType("https"))
|
||||
}
|
||||
if !bServerArgs.private {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithProviderRepositoryConfig("", "", "public"))
|
||||
}
|
||||
if bServerArgs.reconcile {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithReconcile())
|
||||
}
|
||||
|
||||
// Setup bootstrapper with constructed configs
|
||||
b, err := bootstrap.NewGitProviderBootstrapper(gitClient, providerClient, kubeClient, bootstrapOpts...)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Run
|
||||
return bootstrap.Run(ctx, b, manifestsBase, installOptions, secretOpts, syncOpts, rootArgs.pollInterval, rootArgs.timeout)
|
||||
}
|
||||
369
cmd/flux/bootstrap_git.go
Normal file
369
cmd/flux/bootstrap_git.go
Normal file
@@ -0,0 +1,369 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"net/url"
|
||||
"os"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/manifoldco/promptui"
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/install"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sync"
|
||||
"github.com/fluxcd/pkg/git"
|
||||
"github.com/fluxcd/pkg/git/gogit"
|
||||
)
|
||||
|
||||
var bootstrapGitCmd = &cobra.Command{
|
||||
Use: "git",
|
||||
Short: "Deploy Flux on a cluster connected to a Git repository",
|
||||
Long: `The bootstrap git command commits the Flux manifests to the
|
||||
branch of a Git repository. And then it configures the target cluster to synchronize with
|
||||
that repository. If the Flux components are present on the cluster, the bootstrap
|
||||
command will perform an upgrade if needed.`,
|
||||
Example: ` # Run bootstrap for a Git repository and authenticate with your SSH agent
|
||||
flux bootstrap git --url=ssh://git@example.com/repository.git --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a Git repository and authenticate using a password
|
||||
flux bootstrap git --url=https://example.com/repository.git --password=<password> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a Git repository and authenticate using a password from environment variable
|
||||
GIT_PASSWORD=<password> && flux bootstrap git --url=https://example.com/repository.git --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a Git repository with a passwordless private key
|
||||
flux bootstrap git --url=ssh://git@example.com/repository.git --private-key-file=<path/to/private.key> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a Git repository with a private key and password
|
||||
flux bootstrap git --url=ssh://git@example.com/repository.git --private-key-file=<path/to/private.key> --password=<password> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a Git repository on AWS CodeCommit
|
||||
flux bootstrap git --url=ssh://<SSH-Key-ID>@git-codecommit.<region>.amazonaws.com/v1/repos/<repository> --private-key-file=<path/to/private.key> --password=<SSH-passphrase> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a Git repository on Azure Devops
|
||||
flux bootstrap git --url=ssh://git@ssh.dev.azure.com/v3/<org>/<project>/<repository> --ssh-key-algorithm=rsa --ssh-rsa-bits=4096 --path=clusters/my-cluster
|
||||
`,
|
||||
RunE: bootstrapGitCmdRun,
|
||||
}
|
||||
|
||||
type gitFlags struct {
|
||||
url string
|
||||
interval time.Duration
|
||||
path flags.SafeRelativePath
|
||||
username string
|
||||
password string
|
||||
silent bool
|
||||
insecureHttpAllowed bool
|
||||
}
|
||||
|
||||
const (
|
||||
gitPasswordEnvVar = "GIT_PASSWORD"
|
||||
)
|
||||
|
||||
var gitArgs gitFlags
|
||||
|
||||
func init() {
|
||||
bootstrapGitCmd.Flags().StringVar(&gitArgs.url, "url", "", "Git repository URL")
|
||||
bootstrapGitCmd.Flags().DurationVar(&gitArgs.interval, "interval", time.Minute, "sync interval")
|
||||
bootstrapGitCmd.Flags().Var(&gitArgs.path, "path", "path relative to the repository root, when specified the cluster sync will be scoped to this path")
|
||||
bootstrapGitCmd.Flags().StringVarP(&gitArgs.username, "username", "u", "git", "basic authentication username")
|
||||
bootstrapGitCmd.Flags().StringVarP(&gitArgs.password, "password", "p", "", "basic authentication password")
|
||||
bootstrapGitCmd.Flags().BoolVarP(&gitArgs.silent, "silent", "s", false, "assumes the deploy key is already setup, skips confirmation")
|
||||
bootstrapGitCmd.Flags().BoolVar(&gitArgs.insecureHttpAllowed, "allow-insecure-http", false, "allows insecure HTTP connections")
|
||||
|
||||
bootstrapCmd.AddCommand(bootstrapGitCmd)
|
||||
}
|
||||
|
||||
func bootstrapGitCmdRun(cmd *cobra.Command, args []string) error {
|
||||
gitPassword := os.Getenv(gitPasswordEnvVar)
|
||||
if gitPassword != "" && gitArgs.password == "" {
|
||||
gitArgs.password = gitPassword
|
||||
}
|
||||
if bootstrapArgs.tokenAuth && gitArgs.password == "" {
|
||||
var err error
|
||||
gitPassword, err = readPasswordFromStdin("Please enter your Git repository password: ")
|
||||
if err != nil {
|
||||
return fmt.Errorf("could not read token: %w", err)
|
||||
}
|
||||
gitArgs.password = gitPassword
|
||||
}
|
||||
|
||||
if err := bootstrapValidate(); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
repositoryURL, err := url.Parse(gitArgs.url)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if strings.Contains(repositoryURL.Hostname(), "git-codecommit") && strings.Contains(repositoryURL.Hostname(), "amazonaws.com") {
|
||||
if repositoryURL.Scheme == string(git.SSH) {
|
||||
if repositoryURL.User == nil {
|
||||
return fmt.Errorf("invalid AWS CodeCommit url: ssh username should be specified in the url")
|
||||
}
|
||||
if repositoryURL.User.Username() == git.DefaultPublicKeyAuthUser {
|
||||
return fmt.Errorf("invalid AWS CodeCommit url: ssh username should be the SSH key ID for the provided private key")
|
||||
}
|
||||
if bootstrapArgs.privateKeyFile == "" {
|
||||
return fmt.Errorf("private key file is required for bootstrapping against AWS CodeCommit using ssh")
|
||||
}
|
||||
}
|
||||
if repositoryURL.Scheme == string(git.HTTPS) && !bootstrapArgs.tokenAuth {
|
||||
return fmt.Errorf("--token-auth=true must be specified for using an HTTPS AWS CodeCommit url")
|
||||
}
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Manifest base
|
||||
if ver, err := getVersion(bootstrapArgs.version); err != nil {
|
||||
return err
|
||||
} else {
|
||||
bootstrapArgs.version = ver
|
||||
}
|
||||
manifestsBase, err := buildEmbeddedManifestBase()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(manifestsBase)
|
||||
|
||||
// Lazy go-git repository
|
||||
tmpDir, err := manifestgen.MkdirTempAbs("", "flux-bootstrap-")
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create temporary working dir: %w", err)
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
var caBundle []byte
|
||||
if bootstrapArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(bootstrapArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
authOpts, err := getAuthOpts(repositoryURL, caBundle)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create authentication options for %s: %w", repositoryURL.String(), err)
|
||||
}
|
||||
|
||||
clientOpts := []gogit.ClientOption{gogit.WithDiskStorage(), gogit.WithFallbackToDefaultKnownHosts()}
|
||||
if gitArgs.insecureHttpAllowed {
|
||||
clientOpts = append(clientOpts, gogit.WithInsecureCredentialsOverHTTP())
|
||||
}
|
||||
gitClient, err := gogit.NewClient(tmpDir, authOpts, clientOpts...)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create a Git client: %w", err)
|
||||
}
|
||||
|
||||
// Install manifest config
|
||||
installOptions := install.Options{
|
||||
BaseURL: rootArgs.defaults.BaseURL,
|
||||
Version: bootstrapArgs.version,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Components: bootstrapComponents(),
|
||||
Registry: bootstrapArgs.registry,
|
||||
ImagePullSecret: bootstrapArgs.imagePullSecret,
|
||||
WatchAllNamespaces: bootstrapArgs.watchAllNamespaces,
|
||||
NetworkPolicy: bootstrapArgs.networkPolicy,
|
||||
LogLevel: bootstrapArgs.logLevel.String(),
|
||||
NotificationController: rootArgs.defaults.NotificationController,
|
||||
ManifestFile: rootArgs.defaults.ManifestFile,
|
||||
Timeout: rootArgs.timeout,
|
||||
TargetPath: gitArgs.path.ToSlash(),
|
||||
ClusterDomain: bootstrapArgs.clusterDomain,
|
||||
TolerationKeys: bootstrapArgs.tolerationKeys,
|
||||
}
|
||||
if customBaseURL := bootstrapArgs.manifestsPath; customBaseURL != "" {
|
||||
installOptions.BaseURL = customBaseURL
|
||||
}
|
||||
|
||||
// Source generation and secret config
|
||||
secretOpts := sourcesecret.Options{
|
||||
Name: bootstrapArgs.secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
TargetPath: gitArgs.path.String(),
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
if bootstrapArgs.tokenAuth {
|
||||
secretOpts.Username = gitArgs.username
|
||||
secretOpts.Password = gitArgs.password
|
||||
secretOpts.CAFile = caBundle
|
||||
|
||||
// Remove port of the given host when not syncing over HTTP/S to not assume port for protocol
|
||||
// This _might_ be overwritten later on by e.g. --ssh-hostname
|
||||
if repositoryURL.Scheme != "https" && repositoryURL.Scheme != "http" {
|
||||
repositoryURL.Host = repositoryURL.Hostname()
|
||||
}
|
||||
|
||||
// Configure repository URL to match auth config for sync.
|
||||
repositoryURL.User = nil
|
||||
if !gitArgs.insecureHttpAllowed {
|
||||
repositoryURL.Scheme = "https"
|
||||
}
|
||||
} else {
|
||||
secretOpts.PrivateKeyAlgorithm = sourcesecret.PrivateKeyAlgorithm(bootstrapArgs.keyAlgorithm)
|
||||
secretOpts.Password = gitArgs.password
|
||||
secretOpts.RSAKeyBits = int(bootstrapArgs.keyRSABits)
|
||||
secretOpts.ECDSACurve = bootstrapArgs.keyECDSACurve.Curve
|
||||
|
||||
// Configure repository URL to match auth config for sync
|
||||
|
||||
// Override existing user when user is not already set
|
||||
// or when a username was passed in
|
||||
if repositoryURL.User == nil || gitArgs.username != "git" {
|
||||
repositoryURL.User = url.User(gitArgs.username)
|
||||
}
|
||||
|
||||
repositoryURL.Scheme = "ssh"
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
repositoryURL.Host = bootstrapArgs.sshHostname
|
||||
}
|
||||
|
||||
keypair, err := sourcesecret.LoadKeyPairFromPath(bootstrapArgs.privateKeyFile, gitArgs.password)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
secretOpts.Keypair = keypair
|
||||
|
||||
// Configure last as it depends on the config above.
|
||||
secretOpts.SSHHostname = repositoryURL.Host
|
||||
}
|
||||
|
||||
// Sync manifest config
|
||||
syncOpts := sync.Options{
|
||||
Interval: gitArgs.interval,
|
||||
Name: *kubeconfigArgs.Namespace,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
URL: repositoryURL.String(),
|
||||
Branch: bootstrapArgs.branch,
|
||||
Secret: bootstrapArgs.secretName,
|
||||
TargetPath: gitArgs.path.ToSlash(),
|
||||
ManifestFile: sync.MakeDefaultOptions().ManifestFile,
|
||||
RecurseSubmodules: bootstrapArgs.recurseSubmodules,
|
||||
}
|
||||
|
||||
entityList, err := bootstrap.LoadEntityListFromPath(bootstrapArgs.gpgKeyRingPath)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Bootstrap config
|
||||
bootstrapOpts := []bootstrap.GitOption{
|
||||
bootstrap.WithRepositoryURL(gitArgs.url),
|
||||
bootstrap.WithBranch(bootstrapArgs.branch),
|
||||
bootstrap.WithSignature(bootstrapArgs.authorName, bootstrapArgs.authorEmail),
|
||||
bootstrap.WithCommitMessageAppendix(bootstrapArgs.commitMessageAppendix),
|
||||
bootstrap.WithKubeconfig(kubeconfigArgs, kubeclientOptions),
|
||||
bootstrap.WithPostGenerateSecretFunc(promptPublicKey),
|
||||
bootstrap.WithLogger(logger),
|
||||
bootstrap.WithGitCommitSigning(entityList, bootstrapArgs.gpgPassphrase, bootstrapArgs.gpgKeyID),
|
||||
}
|
||||
|
||||
// Setup bootstrapper with constructed configs
|
||||
b, err := bootstrap.NewPlainGitProvider(gitClient, kubeClient, bootstrapOpts...)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Run
|
||||
return bootstrap.Run(ctx, b, manifestsBase, installOptions, secretOpts, syncOpts, rootArgs.pollInterval, rootArgs.timeout)
|
||||
}
|
||||
|
||||
// getAuthOpts retruns a AuthOptions based on the scheme
|
||||
// of the given URL and the configured flags. If the protocol equals
|
||||
// "ssh" but no private key is configured, authentication using the local
|
||||
// SSH-agent is attempted.
|
||||
func getAuthOpts(u *url.URL, caBundle []byte) (*git.AuthOptions, error) {
|
||||
switch u.Scheme {
|
||||
case "http":
|
||||
if !gitArgs.insecureHttpAllowed {
|
||||
return nil, fmt.Errorf("scheme http is insecure, pass --allow-insecure-http=true to allow it")
|
||||
}
|
||||
return &git.AuthOptions{
|
||||
Transport: git.HTTP,
|
||||
Username: gitArgs.username,
|
||||
Password: gitArgs.password,
|
||||
}, nil
|
||||
case "https":
|
||||
return &git.AuthOptions{
|
||||
Transport: git.HTTPS,
|
||||
Username: gitArgs.username,
|
||||
Password: gitArgs.password,
|
||||
CAFile: caBundle,
|
||||
}, nil
|
||||
case "ssh":
|
||||
authOpts := &git.AuthOptions{
|
||||
Transport: git.SSH,
|
||||
Username: u.User.Username(),
|
||||
Password: gitArgs.password,
|
||||
}
|
||||
if bootstrapArgs.privateKeyFile != "" {
|
||||
pk, err := os.ReadFile(bootstrapArgs.privateKeyFile)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
kh, err := sourcesecret.ScanHostKey(u.Host)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
authOpts.Identity = pk
|
||||
authOpts.KnownHosts = kh
|
||||
}
|
||||
return authOpts, nil
|
||||
default:
|
||||
return nil, fmt.Errorf("scheme %q is not supported", u.Scheme)
|
||||
}
|
||||
}
|
||||
|
||||
func promptPublicKey(ctx context.Context, secret corev1.Secret, _ sourcesecret.Options) error {
|
||||
ppk, ok := secret.StringData[sourcesecret.PublicKeySecretKey]
|
||||
if !ok {
|
||||
return nil
|
||||
}
|
||||
|
||||
logger.Successf("public key: %s", strings.TrimSpace(ppk))
|
||||
|
||||
if !gitArgs.silent {
|
||||
prompt := promptui.Prompt{
|
||||
Label: "Please give the key access to your repository",
|
||||
IsConfirm: true,
|
||||
}
|
||||
_, err := prompt.Run()
|
||||
if err != nil {
|
||||
return fmt.Errorf("aborting")
|
||||
}
|
||||
}
|
||||
return nil
|
||||
}
|
||||
275
cmd/flux/bootstrap_github.go
Normal file
275
cmd/flux/bootstrap_github.go
Normal file
@@ -0,0 +1,275 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"os"
|
||||
"time"
|
||||
|
||||
"github.com/fluxcd/pkg/git"
|
||||
"github.com/fluxcd/pkg/git/gogit"
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap/provider"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/install"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sync"
|
||||
)
|
||||
|
||||
var bootstrapGitHubCmd = &cobra.Command{
|
||||
Use: "github",
|
||||
Short: "Deploy Flux on a cluster connected to a GitHub repository",
|
||||
Long: `The bootstrap github command creates the GitHub repository if it doesn't exists and
|
||||
commits the Flux manifests to the specified branch.
|
||||
Then it configures the target cluster to synchronize with that repository.
|
||||
If the Flux components are present on the cluster,
|
||||
the bootstrap command will perform an upgrade if needed.`,
|
||||
Example: ` # Create a GitHub personal access token and export it as an env var
|
||||
export GITHUB_TOKEN=<my-token>
|
||||
|
||||
# Run bootstrap for a private repository owned by a GitHub organization
|
||||
flux bootstrap github --owner=<organization> --repository=<repository name> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a private repository and assign organization teams to it
|
||||
flux bootstrap github --owner=<organization> --repository=<repository name> --team=<team1 slug> --team=<team2 slug> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a private repository and assign organization teams with their access level(e.g maintain, admin) to it
|
||||
flux bootstrap github --owner=<organization> --repository=<repository name> --team=<team1 slug>:<access-level> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a public repository on a personal account
|
||||
flux bootstrap github --owner=<user> --repository=<repository name> --private=false --personal=true --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a private repository hosted on GitHub Enterprise using SSH auth
|
||||
flux bootstrap github --owner=<organization> --repository=<repository name> --hostname=<domain> --ssh-hostname=<domain> --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for a private repository hosted on GitHub Enterprise using HTTPS auth
|
||||
flux bootstrap github --owner=<organization> --repository=<repository name> --hostname=<domain> --token-auth --path=clusters/my-cluster
|
||||
|
||||
# Run bootstrap for an existing repository with a branch named main
|
||||
flux bootstrap github --owner=<organization> --repository=<repository name> --branch=main --path=clusters/my-cluster`,
|
||||
RunE: bootstrapGitHubCmdRun,
|
||||
}
|
||||
|
||||
type githubFlags struct {
|
||||
owner string
|
||||
repository string
|
||||
interval time.Duration
|
||||
personal bool
|
||||
private bool
|
||||
hostname string
|
||||
path flags.SafeRelativePath
|
||||
teams []string
|
||||
readWriteKey bool
|
||||
reconcile bool
|
||||
}
|
||||
|
||||
const (
|
||||
ghDefaultPermission = "maintain"
|
||||
ghDefaultDomain = "github.com"
|
||||
ghTokenEnvVar = "GITHUB_TOKEN"
|
||||
)
|
||||
|
||||
var githubArgs githubFlags
|
||||
|
||||
func init() {
|
||||
bootstrapGitHubCmd.Flags().StringVar(&githubArgs.owner, "owner", "", "GitHub user or organization name")
|
||||
bootstrapGitHubCmd.Flags().StringVar(&githubArgs.repository, "repository", "", "GitHub repository name")
|
||||
bootstrapGitHubCmd.Flags().StringSliceVar(&githubArgs.teams, "team", []string{}, "GitHub team and the access to be given to it(team:maintain). Defaults to maintainer access if no access level is specified (also accepts comma-separated values)")
|
||||
bootstrapGitHubCmd.Flags().BoolVar(&githubArgs.personal, "personal", false, "if true, the owner is assumed to be a GitHub user; otherwise an org")
|
||||
bootstrapGitHubCmd.Flags().BoolVar(&githubArgs.private, "private", true, "if true, the repository is setup or configured as private")
|
||||
bootstrapGitHubCmd.Flags().DurationVar(&githubArgs.interval, "interval", time.Minute, "sync interval")
|
||||
bootstrapGitHubCmd.Flags().StringVar(&githubArgs.hostname, "hostname", ghDefaultDomain, "GitHub hostname")
|
||||
bootstrapGitHubCmd.Flags().Var(&githubArgs.path, "path", "path relative to the repository root, when specified the cluster sync will be scoped to this path")
|
||||
bootstrapGitHubCmd.Flags().BoolVar(&githubArgs.readWriteKey, "read-write-key", false, "if true, the deploy key is configured with read/write permissions")
|
||||
bootstrapGitHubCmd.Flags().BoolVar(&githubArgs.reconcile, "reconcile", false, "if true, the configured options are also reconciled if the repository already exists")
|
||||
|
||||
bootstrapCmd.AddCommand(bootstrapGitHubCmd)
|
||||
}
|
||||
|
||||
func bootstrapGitHubCmdRun(cmd *cobra.Command, args []string) error {
|
||||
ghToken := os.Getenv(ghTokenEnvVar)
|
||||
if ghToken == "" {
|
||||
var err error
|
||||
ghToken, err = readPasswordFromStdin("Please enter your GitHub personal access token (PAT): ")
|
||||
if err != nil {
|
||||
return fmt.Errorf("could not read token: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
if err := bootstrapValidate(); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Manifest base
|
||||
if ver, err := getVersion(bootstrapArgs.version); err != nil {
|
||||
return err
|
||||
} else {
|
||||
bootstrapArgs.version = ver
|
||||
}
|
||||
manifestsBase, err := buildEmbeddedManifestBase()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(manifestsBase)
|
||||
|
||||
var caBundle []byte
|
||||
if bootstrapArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(bootstrapArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
// Build GitHub provider
|
||||
providerCfg := provider.Config{
|
||||
Provider: provider.GitProviderGitHub,
|
||||
Hostname: githubArgs.hostname,
|
||||
Token: ghToken,
|
||||
CaBundle: caBundle,
|
||||
}
|
||||
providerClient, err := provider.BuildGitProvider(providerCfg)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
tmpDir, err := manifestgen.MkdirTempAbs("", "flux-bootstrap-")
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create temporary working dir: %w", err)
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
clientOpts := []gogit.ClientOption{gogit.WithDiskStorage(), gogit.WithFallbackToDefaultKnownHosts()}
|
||||
gitClient, err := gogit.NewClient(tmpDir, &git.AuthOptions{
|
||||
Transport: git.HTTPS,
|
||||
Username: githubArgs.owner,
|
||||
Password: ghToken,
|
||||
CAFile: caBundle,
|
||||
}, clientOpts...)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create a Git client: %w", err)
|
||||
}
|
||||
|
||||
// Install manifest config
|
||||
installOptions := install.Options{
|
||||
BaseURL: rootArgs.defaults.BaseURL,
|
||||
Version: bootstrapArgs.version,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Components: bootstrapComponents(),
|
||||
Registry: bootstrapArgs.registry,
|
||||
ImagePullSecret: bootstrapArgs.imagePullSecret,
|
||||
WatchAllNamespaces: bootstrapArgs.watchAllNamespaces,
|
||||
NetworkPolicy: bootstrapArgs.networkPolicy,
|
||||
LogLevel: bootstrapArgs.logLevel.String(),
|
||||
NotificationController: rootArgs.defaults.NotificationController,
|
||||
ManifestFile: rootArgs.defaults.ManifestFile,
|
||||
Timeout: rootArgs.timeout,
|
||||
TargetPath: githubArgs.path.ToSlash(),
|
||||
ClusterDomain: bootstrapArgs.clusterDomain,
|
||||
TolerationKeys: bootstrapArgs.tolerationKeys,
|
||||
}
|
||||
if customBaseURL := bootstrapArgs.manifestsPath; customBaseURL != "" {
|
||||
installOptions.BaseURL = customBaseURL
|
||||
}
|
||||
|
||||
// Source generation and secret config
|
||||
secretOpts := sourcesecret.Options{
|
||||
Name: bootstrapArgs.secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
TargetPath: githubArgs.path.ToSlash(),
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
if bootstrapArgs.tokenAuth {
|
||||
secretOpts.Username = "git"
|
||||
secretOpts.Password = ghToken
|
||||
secretOpts.CAFile = caBundle
|
||||
} else {
|
||||
secretOpts.PrivateKeyAlgorithm = sourcesecret.PrivateKeyAlgorithm(bootstrapArgs.keyAlgorithm)
|
||||
secretOpts.RSAKeyBits = int(bootstrapArgs.keyRSABits)
|
||||
secretOpts.ECDSACurve = bootstrapArgs.keyECDSACurve.Curve
|
||||
|
||||
secretOpts.SSHHostname = githubArgs.hostname
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
secretOpts.SSHHostname = bootstrapArgs.sshHostname
|
||||
}
|
||||
}
|
||||
|
||||
// Sync manifest config
|
||||
syncOpts := sync.Options{
|
||||
Interval: githubArgs.interval,
|
||||
Name: *kubeconfigArgs.Namespace,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Branch: bootstrapArgs.branch,
|
||||
Secret: bootstrapArgs.secretName,
|
||||
TargetPath: githubArgs.path.ToSlash(),
|
||||
ManifestFile: sync.MakeDefaultOptions().ManifestFile,
|
||||
RecurseSubmodules: bootstrapArgs.recurseSubmodules,
|
||||
}
|
||||
|
||||
entityList, err := bootstrap.LoadEntityListFromPath(bootstrapArgs.gpgKeyRingPath)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Bootstrap config
|
||||
bootstrapOpts := []bootstrap.GitProviderOption{
|
||||
bootstrap.WithProviderRepository(githubArgs.owner, githubArgs.repository, githubArgs.personal),
|
||||
bootstrap.WithBranch(bootstrapArgs.branch),
|
||||
bootstrap.WithBootstrapTransportType("https"),
|
||||
bootstrap.WithSignature(bootstrapArgs.authorName, bootstrapArgs.authorEmail),
|
||||
bootstrap.WithCommitMessageAppendix(bootstrapArgs.commitMessageAppendix),
|
||||
bootstrap.WithProviderTeamPermissions(mapTeamSlice(githubArgs.teams, ghDefaultPermission)),
|
||||
bootstrap.WithReadWriteKeyPermissions(githubArgs.readWriteKey),
|
||||
bootstrap.WithKubeconfig(kubeconfigArgs, kubeclientOptions),
|
||||
bootstrap.WithLogger(logger),
|
||||
bootstrap.WithGitCommitSigning(entityList, bootstrapArgs.gpgPassphrase, bootstrapArgs.gpgKeyID),
|
||||
}
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithSSHHostname(bootstrapArgs.sshHostname))
|
||||
}
|
||||
if bootstrapArgs.tokenAuth {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithSyncTransportType("https"))
|
||||
}
|
||||
if !githubArgs.private {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithProviderRepositoryConfig("", "", "public"))
|
||||
}
|
||||
if githubArgs.reconcile {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithReconcile())
|
||||
}
|
||||
|
||||
// Setup bootstrapper with constructed configs
|
||||
b, err := bootstrap.NewGitProviderBootstrapper(gitClient, providerClient, kubeClient, bootstrapOpts...)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Run
|
||||
return bootstrap.Run(ctx, b, manifestsBase, installOptions, secretOpts, syncOpts, rootArgs.pollInterval, rootArgs.timeout)
|
||||
}
|
||||
311
cmd/flux/bootstrap_gitlab.go
Normal file
311
cmd/flux/bootstrap_gitlab.go
Normal file
@@ -0,0 +1,311 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"os"
|
||||
"regexp"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/fluxcd/pkg/git"
|
||||
"github.com/fluxcd/pkg/git/gogit"
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap"
|
||||
"github.com/fluxcd/flux2/v2/pkg/bootstrap/provider"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/install"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sync"
|
||||
)
|
||||
|
||||
var bootstrapGitLabCmd = &cobra.Command{
|
||||
Use: "gitlab",
|
||||
Short: "Deploy Flux on a cluster connected to a GitLab repository",
|
||||
Long: `The bootstrap gitlab command creates the GitLab repository if it doesn't exists and
|
||||
commits the Flux manifests to the specified branch.
|
||||
Then it configures the target cluster to synchronize with that repository.
|
||||
If the Flux components are present on the cluster,
|
||||
the bootstrap command will perform an upgrade if needed.`,
|
||||
Example: ` # Create a GitLab API token and export it as an env var
|
||||
export GITLAB_TOKEN=<my-token>
|
||||
|
||||
# Run bootstrap for a private repository using HTTPS token authentication
|
||||
flux bootstrap gitlab --owner=<group> --repository=<repository name> --token-auth
|
||||
|
||||
# Run bootstrap for a private repository using SSH authentication
|
||||
flux bootstrap gitlab --owner=<group> --repository=<repository name>
|
||||
|
||||
# Run bootstrap for a repository path
|
||||
flux bootstrap gitlab --owner=<group> --repository=<repository name> --path=dev-cluster
|
||||
|
||||
# Run bootstrap for a public repository on a personal account
|
||||
flux bootstrap gitlab --owner=<user> --repository=<repository name> --private=false --personal --token-auth
|
||||
|
||||
# Run bootstrap for a private repository hosted on a GitLab server
|
||||
flux bootstrap gitlab --owner=<group> --repository=<repository name> --hostname=<domain> --token-auth
|
||||
|
||||
# Run bootstrap for a an existing repository with a branch named main
|
||||
flux bootstrap gitlab --owner=<organization> --repository=<repository name> --branch=main --token-auth
|
||||
|
||||
# Run bootstrap for a private repository using Deploy Token authentication
|
||||
flux bootstrap gitlab --owner=<group> --repository=<repository name> --deploy-token-auth
|
||||
`,
|
||||
RunE: bootstrapGitLabCmdRun,
|
||||
}
|
||||
|
||||
const (
|
||||
glDefaultPermission = "maintain"
|
||||
glDefaultDomain = "gitlab.com"
|
||||
glTokenEnvVar = "GITLAB_TOKEN"
|
||||
gitlabProjectRegex = `\A[[:alnum:]\x{00A9}-\x{1f9ff}_][[:alnum:]\p{Pd}\x{00A9}-\x{1f9ff}_\.]*\z`
|
||||
)
|
||||
|
||||
type gitlabFlags struct {
|
||||
owner string
|
||||
repository string
|
||||
interval time.Duration
|
||||
personal bool
|
||||
private bool
|
||||
hostname string
|
||||
path flags.SafeRelativePath
|
||||
teams []string
|
||||
readWriteKey bool
|
||||
reconcile bool
|
||||
deployTokenAuth bool
|
||||
}
|
||||
|
||||
var gitlabArgs gitlabFlags
|
||||
|
||||
func init() {
|
||||
bootstrapGitLabCmd.Flags().StringVar(&gitlabArgs.owner, "owner", "", "GitLab user or group name")
|
||||
bootstrapGitLabCmd.Flags().StringVar(&gitlabArgs.repository, "repository", "", "GitLab repository name")
|
||||
bootstrapGitLabCmd.Flags().StringSliceVar(&gitlabArgs.teams, "team", []string{}, "GitLab teams to be given maintainer access (also accepts comma-separated values)")
|
||||
bootstrapGitLabCmd.Flags().BoolVar(&gitlabArgs.personal, "personal", false, "if true, the owner is assumed to be a GitLab user; otherwise a group")
|
||||
bootstrapGitLabCmd.Flags().BoolVar(&gitlabArgs.private, "private", true, "if true, the repository is setup or configured as private")
|
||||
bootstrapGitLabCmd.Flags().DurationVar(&gitlabArgs.interval, "interval", time.Minute, "sync interval")
|
||||
bootstrapGitLabCmd.Flags().StringVar(&gitlabArgs.hostname, "hostname", glDefaultDomain, "GitLab hostname")
|
||||
bootstrapGitLabCmd.Flags().Var(&gitlabArgs.path, "path", "path relative to the repository root, when specified the cluster sync will be scoped to this path")
|
||||
bootstrapGitLabCmd.Flags().BoolVar(&gitlabArgs.readWriteKey, "read-write-key", false, "if true, the deploy key is configured with read/write permissions")
|
||||
bootstrapGitLabCmd.Flags().BoolVar(&gitlabArgs.reconcile, "reconcile", false, "if true, the configured options are also reconciled if the repository already exists")
|
||||
bootstrapGitLabCmd.Flags().BoolVar(&gitlabArgs.deployTokenAuth, "deploy-token-auth", false, "when enabled, a Project Deploy Token is generated and will be used instead of the SSH deploy token")
|
||||
|
||||
bootstrapCmd.AddCommand(bootstrapGitLabCmd)
|
||||
}
|
||||
|
||||
func bootstrapGitLabCmdRun(cmd *cobra.Command, args []string) error {
|
||||
glToken := os.Getenv(glTokenEnvVar)
|
||||
if glToken == "" {
|
||||
var err error
|
||||
glToken, err = readPasswordFromStdin("Please enter your GitLab personal access token (PAT): ")
|
||||
if err != nil {
|
||||
return fmt.Errorf("could not read token: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
if projectNameIsValid, err := regexp.MatchString(gitlabProjectRegex, gitlabArgs.repository); err != nil || !projectNameIsValid {
|
||||
if err == nil {
|
||||
err = fmt.Errorf("%s is an invalid project name for gitlab.\nIt can contain only letters, digits, emojis, '_', '.', dash, space. It must start with letter, digit, emoji or '_'.", gitlabArgs.repository)
|
||||
}
|
||||
return err
|
||||
}
|
||||
|
||||
if bootstrapArgs.tokenAuth && gitlabArgs.deployTokenAuth {
|
||||
return fmt.Errorf("--token-auth and --deploy-token-auth cannot be set both.")
|
||||
}
|
||||
|
||||
if err := bootstrapValidate(); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Manifest base
|
||||
if ver, err := getVersion(bootstrapArgs.version); err != nil {
|
||||
return err
|
||||
} else {
|
||||
bootstrapArgs.version = ver
|
||||
}
|
||||
manifestsBase, err := buildEmbeddedManifestBase()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(manifestsBase)
|
||||
|
||||
var caBundle []byte
|
||||
if bootstrapArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(bootstrapArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
// Build GitLab provider
|
||||
providerCfg := provider.Config{
|
||||
Provider: provider.GitProviderGitLab,
|
||||
Hostname: gitlabArgs.hostname,
|
||||
Token: glToken,
|
||||
CaBundle: caBundle,
|
||||
}
|
||||
// Workaround for: https://github.com/fluxcd/go-git-providers/issues/55
|
||||
if hostname := providerCfg.Hostname; hostname != glDefaultDomain &&
|
||||
!strings.HasPrefix(hostname, "https://") &&
|
||||
!strings.HasPrefix(hostname, "http://") {
|
||||
providerCfg.Hostname = "https://" + providerCfg.Hostname
|
||||
}
|
||||
providerClient, err := provider.BuildGitProvider(providerCfg)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Lazy go-git repository
|
||||
tmpDir, err := manifestgen.MkdirTempAbs("", "flux-bootstrap-")
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create temporary working dir: %w", err)
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
clientOpts := []gogit.ClientOption{gogit.WithDiskStorage(), gogit.WithFallbackToDefaultKnownHosts()}
|
||||
gitClient, err := gogit.NewClient(tmpDir, &git.AuthOptions{
|
||||
Transport: git.HTTPS,
|
||||
Username: gitlabArgs.owner,
|
||||
Password: glToken,
|
||||
CAFile: caBundle,
|
||||
}, clientOpts...)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to create a Git client: %w", err)
|
||||
}
|
||||
|
||||
// Install manifest config
|
||||
installOptions := install.Options{
|
||||
BaseURL: rootArgs.defaults.BaseURL,
|
||||
Version: bootstrapArgs.version,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Components: bootstrapComponents(),
|
||||
Registry: bootstrapArgs.registry,
|
||||
ImagePullSecret: bootstrapArgs.imagePullSecret,
|
||||
WatchAllNamespaces: bootstrapArgs.watchAllNamespaces,
|
||||
NetworkPolicy: bootstrapArgs.networkPolicy,
|
||||
LogLevel: bootstrapArgs.logLevel.String(),
|
||||
NotificationController: rootArgs.defaults.NotificationController,
|
||||
ManifestFile: rootArgs.defaults.ManifestFile,
|
||||
Timeout: rootArgs.timeout,
|
||||
TargetPath: gitlabArgs.path.ToSlash(),
|
||||
ClusterDomain: bootstrapArgs.clusterDomain,
|
||||
TolerationKeys: bootstrapArgs.tolerationKeys,
|
||||
}
|
||||
if customBaseURL := bootstrapArgs.manifestsPath; customBaseURL != "" {
|
||||
installOptions.BaseURL = customBaseURL
|
||||
}
|
||||
|
||||
// Source generation and secret config
|
||||
secretOpts := sourcesecret.Options{
|
||||
Name: bootstrapArgs.secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
TargetPath: gitlabArgs.path.String(),
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
if bootstrapArgs.tokenAuth {
|
||||
secretOpts.Username = "git"
|
||||
secretOpts.Password = glToken
|
||||
secretOpts.CAFile = caBundle
|
||||
} else if gitlabArgs.deployTokenAuth {
|
||||
// the actual deploy token will be reconciled later
|
||||
secretOpts.CAFile = caBundle
|
||||
} else {
|
||||
keypair, err := sourcesecret.LoadKeyPairFromPath(bootstrapArgs.privateKeyFile, gitArgs.password)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
secretOpts.Keypair = keypair
|
||||
secretOpts.PrivateKeyAlgorithm = sourcesecret.PrivateKeyAlgorithm(bootstrapArgs.keyAlgorithm)
|
||||
secretOpts.RSAKeyBits = int(bootstrapArgs.keyRSABits)
|
||||
secretOpts.ECDSACurve = bootstrapArgs.keyECDSACurve.Curve
|
||||
|
||||
secretOpts.SSHHostname = gitlabArgs.hostname
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
secretOpts.SSHHostname = bootstrapArgs.sshHostname
|
||||
}
|
||||
}
|
||||
|
||||
// Sync manifest config
|
||||
syncOpts := sync.Options{
|
||||
Interval: gitlabArgs.interval,
|
||||
Name: *kubeconfigArgs.Namespace,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Branch: bootstrapArgs.branch,
|
||||
Secret: bootstrapArgs.secretName,
|
||||
TargetPath: gitlabArgs.path.ToSlash(),
|
||||
ManifestFile: sync.MakeDefaultOptions().ManifestFile,
|
||||
RecurseSubmodules: bootstrapArgs.recurseSubmodules,
|
||||
}
|
||||
|
||||
entityList, err := bootstrap.LoadEntityListFromPath(bootstrapArgs.gpgKeyRingPath)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Bootstrap config
|
||||
bootstrapOpts := []bootstrap.GitProviderOption{
|
||||
bootstrap.WithProviderRepository(gitlabArgs.owner, gitlabArgs.repository, gitlabArgs.personal),
|
||||
bootstrap.WithBranch(bootstrapArgs.branch),
|
||||
bootstrap.WithBootstrapTransportType("https"),
|
||||
bootstrap.WithSignature(bootstrapArgs.authorName, bootstrapArgs.authorEmail),
|
||||
bootstrap.WithCommitMessageAppendix(bootstrapArgs.commitMessageAppendix),
|
||||
bootstrap.WithProviderTeamPermissions(mapTeamSlice(gitlabArgs.teams, glDefaultPermission)),
|
||||
bootstrap.WithReadWriteKeyPermissions(gitlabArgs.readWriteKey),
|
||||
bootstrap.WithKubeconfig(kubeconfigArgs, kubeclientOptions),
|
||||
bootstrap.WithLogger(logger),
|
||||
bootstrap.WithGitCommitSigning(entityList, bootstrapArgs.gpgPassphrase, bootstrapArgs.gpgKeyID),
|
||||
}
|
||||
if bootstrapArgs.sshHostname != "" {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithSSHHostname(bootstrapArgs.sshHostname))
|
||||
}
|
||||
if bootstrapArgs.tokenAuth || gitlabArgs.deployTokenAuth {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithSyncTransportType("https"))
|
||||
}
|
||||
if gitlabArgs.deployTokenAuth {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithDeployTokenAuth())
|
||||
}
|
||||
if !gitlabArgs.private {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithProviderRepositoryConfig("", "", "public"))
|
||||
}
|
||||
if gitlabArgs.reconcile {
|
||||
bootstrapOpts = append(bootstrapOpts, bootstrap.WithReconcile())
|
||||
}
|
||||
|
||||
// Setup bootstrapper with constructed configs
|
||||
b, err := bootstrap.NewGitProviderBootstrapper(gitClient, providerClient, kubeClient, bootstrapOpts...)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// Run
|
||||
return bootstrap.Run(ctx, b, manifestsBase, installOptions, secretOpts, syncOpts, rootArgs.pollInterval, rootArgs.timeout)
|
||||
}
|
||||
31
cmd/flux/build.go
Normal file
31
cmd/flux/build.go
Normal file
@@ -0,0 +1,31 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var buildCmd = &cobra.Command{
|
||||
Use: "build",
|
||||
Short: "Build a flux resource",
|
||||
Long: `The build command is used to build flux resources.`,
|
||||
}
|
||||
|
||||
func init() {
|
||||
rootCmd.AddCommand(buildCmd)
|
||||
}
|
||||
117
cmd/flux/build_artifact.go
Normal file
117
cmd/flux/build_artifact.go
Normal file
@@ -0,0 +1,117 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"bufio"
|
||||
"bytes"
|
||||
"fmt"
|
||||
"io"
|
||||
"os"
|
||||
"strings"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
oci "github.com/fluxcd/pkg/oci/client"
|
||||
"github.com/fluxcd/pkg/sourceignore"
|
||||
)
|
||||
|
||||
var buildArtifactCmd = &cobra.Command{
|
||||
Use: "artifact",
|
||||
Short: "Build artifact",
|
||||
Long: withPreviewNote(`The build artifact command creates a tgz file with the manifests
|
||||
from the given directory or a single manifest file.`),
|
||||
Example: ` # Build the given manifests directory into an artifact
|
||||
flux build artifact --path ./path/to/local/manifests --output ./path/to/artifact.tgz
|
||||
|
||||
# Build the given single manifest file into an artifact
|
||||
flux build artifact --path ./path/to/local/manifest.yaml --output ./path/to/artifact.tgz
|
||||
|
||||
# List the files bundled in the artifact
|
||||
tar -ztvf ./path/to/artifact.tgz
|
||||
`,
|
||||
RunE: buildArtifactCmdRun,
|
||||
}
|
||||
|
||||
type buildArtifactFlags struct {
|
||||
output string
|
||||
path string
|
||||
ignorePaths []string
|
||||
}
|
||||
|
||||
var excludeOCI = append(strings.Split(sourceignore.ExcludeVCS, ","), strings.Split(sourceignore.ExcludeExt, ",")...)
|
||||
|
||||
var buildArtifactArgs buildArtifactFlags
|
||||
|
||||
func init() {
|
||||
buildArtifactCmd.Flags().StringVarP(&buildArtifactArgs.path, "path", "p", "", "Path to the directory where the Kubernetes manifests are located.")
|
||||
buildArtifactCmd.Flags().StringVarP(&buildArtifactArgs.output, "output", "o", "artifact.tgz", "Path to where the artifact tgz file should be written.")
|
||||
buildArtifactCmd.Flags().StringSliceVar(&buildArtifactArgs.ignorePaths, "ignore-paths", excludeOCI, "set paths to ignore in .gitignore format")
|
||||
|
||||
buildCmd.AddCommand(buildArtifactCmd)
|
||||
}
|
||||
|
||||
func buildArtifactCmdRun(cmd *cobra.Command, args []string) error {
|
||||
if buildArtifactArgs.path == "" {
|
||||
return fmt.Errorf("invalid path %q", buildArtifactArgs.path)
|
||||
}
|
||||
|
||||
path := buildArtifactArgs.path
|
||||
var err error
|
||||
if buildArtifactArgs.path == "-" {
|
||||
path, err = saveReaderToFile(os.Stdin)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
defer os.Remove(path)
|
||||
}
|
||||
|
||||
if _, err := os.Stat(path); err != nil {
|
||||
return fmt.Errorf("invalid path '%s', must point to an existing directory or file", path)
|
||||
}
|
||||
|
||||
logger.Actionf("building artifact from %s", path)
|
||||
|
||||
ociClient := oci.NewClient(oci.DefaultOptions())
|
||||
if err := ociClient.Build(buildArtifactArgs.output, path, buildArtifactArgs.ignorePaths); err != nil {
|
||||
return fmt.Errorf("bulding artifact failed, error: %w", err)
|
||||
}
|
||||
|
||||
logger.Successf("artifact created at %s", buildArtifactArgs.output)
|
||||
return nil
|
||||
}
|
||||
|
||||
func saveReaderToFile(reader io.Reader) (string, error) {
|
||||
b, err := io.ReadAll(bufio.NewReader(reader))
|
||||
if err != nil {
|
||||
return "", err
|
||||
}
|
||||
b = bytes.TrimRight(b, "\r\n")
|
||||
f, err := os.CreateTemp("", "*.yaml")
|
||||
if err != nil {
|
||||
return "", fmt.Errorf("unable to create temp dir for stdin")
|
||||
}
|
||||
|
||||
defer f.Close()
|
||||
|
||||
if _, err := f.Write(b); err != nil {
|
||||
return "", fmt.Errorf("error writing stdin to file: %w", err)
|
||||
}
|
||||
|
||||
return f.Name(), nil
|
||||
}
|
||||
70
cmd/flux/build_artifact_test.go
Normal file
70
cmd/flux/build_artifact_test.go
Normal file
@@ -0,0 +1,70 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"os"
|
||||
"strings"
|
||||
"testing"
|
||||
|
||||
. "github.com/onsi/gomega"
|
||||
)
|
||||
|
||||
func Test_saveReaderToFile(t *testing.T) {
|
||||
g := NewWithT(t)
|
||||
|
||||
testString := `apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: myapp
|
||||
data:
|
||||
foo: bar`
|
||||
|
||||
tests := []struct {
|
||||
name string
|
||||
string string
|
||||
expectErr bool
|
||||
}{
|
||||
{
|
||||
name: "yaml",
|
||||
string: testString,
|
||||
},
|
||||
{
|
||||
name: "yaml with carriage return",
|
||||
string: testString + "\r\n",
|
||||
},
|
||||
}
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
tmpFile, err := saveReaderToFile(strings.NewReader(tt.string))
|
||||
g.Expect(err).To(BeNil())
|
||||
|
||||
t.Cleanup(func() { _ = os.Remove(tmpFile) })
|
||||
|
||||
b, err := os.ReadFile(tmpFile)
|
||||
if tt.expectErr {
|
||||
g.Expect(err).To(Not(BeNil()))
|
||||
return
|
||||
}
|
||||
|
||||
g.Expect(err).To(BeNil())
|
||||
g.Expect(string(b)).To(BeEquivalentTo(testString))
|
||||
})
|
||||
|
||||
}
|
||||
}
|
||||
156
cmd/flux/build_kustomization.go
Normal file
156
cmd/flux/build_kustomization.go
Normal file
@@ -0,0 +1,156 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"os"
|
||||
"os/signal"
|
||||
|
||||
"github.com/fluxcd/pkg/ssa"
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
kustomizev1 "github.com/fluxcd/kustomize-controller/api/v1"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/build"
|
||||
)
|
||||
|
||||
var buildKsCmd = &cobra.Command{
|
||||
Use: "kustomization",
|
||||
Aliases: []string{"ks"},
|
||||
Short: "Build Kustomization",
|
||||
Long: `The build command queries the Kubernetes API and fetches the specified Flux Kustomization.
|
||||
It then uses the fetched in cluster flux kustomization to perform needed transformation on the local kustomization.yaml
|
||||
pointed at by --path. The local kustomization.yaml is generated if it does not exist. Finally it builds the overlays using the local kustomization.yaml, and write the resulting multi-doc YAML to stdout.
|
||||
|
||||
It is possible to specify a Flux kustomization file using --kustomization-file.`,
|
||||
Example: `# Build the local manifests as they were built on the cluster
|
||||
flux build kustomization my-app --path ./path/to/local/manifests
|
||||
|
||||
# Build using a local flux kustomization file
|
||||
flux build kustomization my-app --path ./path/to/local/manifests --kustomization-file ./path/to/local/my-app.yaml
|
||||
|
||||
# Build in dry-run mode without connecting to the cluster.
|
||||
# Note that variable substitutions from Secrets and ConfigMaps are skipped in dry-run mode.
|
||||
flux build kustomization my-app --path ./path/to/local/manifests \
|
||||
--kustomization-file ./path/to/local/my-app.yaml \
|
||||
--dry-run
|
||||
|
||||
# Exclude files by providing a comma separated list of entries that follow the .gitignore pattern fromat.
|
||||
flux build kustomization my-app --path ./path/to/local/manifests \
|
||||
--kustomization-file ./path/to/local/my-app.yaml \
|
||||
--ignore-paths "/to_ignore/**/*.yaml,ignore.yaml"`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(kustomizev1.GroupVersion.WithKind(kustomizev1.KustomizationKind)),
|
||||
RunE: buildKsCmdRun,
|
||||
}
|
||||
|
||||
type buildKsFlags struct {
|
||||
kustomizationFile string
|
||||
path string
|
||||
ignorePaths []string
|
||||
dryRun bool
|
||||
}
|
||||
|
||||
var buildKsArgs buildKsFlags
|
||||
|
||||
func init() {
|
||||
buildKsCmd.Flags().StringVar(&buildKsArgs.path, "path", "", "Path to the manifests location.")
|
||||
buildKsCmd.Flags().StringVar(&buildKsArgs.kustomizationFile, "kustomization-file", "", "Path to the Flux Kustomization YAML file.")
|
||||
buildKsCmd.Flags().StringSliceVar(&buildKsArgs.ignorePaths, "ignore-paths", nil, "set paths to ignore in .gitignore format")
|
||||
buildKsCmd.Flags().BoolVar(&buildKsArgs.dryRun, "dry-run", false, "Dry run mode.")
|
||||
buildCmd.AddCommand(buildKsCmd)
|
||||
}
|
||||
|
||||
func buildKsCmdRun(cmd *cobra.Command, args []string) (err error) {
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("%s name is required", kustomizationType.humanKind)
|
||||
}
|
||||
name := args[0]
|
||||
|
||||
if buildKsArgs.path == "" {
|
||||
return fmt.Errorf("invalid resource path %q", buildKsArgs.path)
|
||||
}
|
||||
|
||||
if fs, err := os.Stat(buildKsArgs.path); err != nil || !fs.IsDir() {
|
||||
return fmt.Errorf("invalid resource path %q", buildKsArgs.path)
|
||||
}
|
||||
|
||||
if buildKsArgs.dryRun && buildKsArgs.kustomizationFile == "" {
|
||||
return fmt.Errorf("dry-run mode requires a kustomization file")
|
||||
}
|
||||
|
||||
if buildKsArgs.kustomizationFile != "" {
|
||||
if fs, err := os.Stat(buildKsArgs.kustomizationFile); os.IsNotExist(err) || fs.IsDir() {
|
||||
return fmt.Errorf("invalid kustomization file %q", buildKsArgs.kustomizationFile)
|
||||
}
|
||||
}
|
||||
|
||||
var builder *build.Builder
|
||||
if buildKsArgs.dryRun {
|
||||
builder, err = build.NewBuilder(name, buildKsArgs.path,
|
||||
build.WithTimeout(rootArgs.timeout),
|
||||
build.WithKustomizationFile(buildKsArgs.kustomizationFile),
|
||||
build.WithDryRun(buildKsArgs.dryRun),
|
||||
build.WithNamespace(*kubeconfigArgs.Namespace),
|
||||
build.WithIgnore(buildKsArgs.ignorePaths),
|
||||
)
|
||||
} else {
|
||||
builder, err = build.NewBuilder(name, buildKsArgs.path,
|
||||
build.WithClientConfig(kubeconfigArgs, kubeclientOptions),
|
||||
build.WithTimeout(rootArgs.timeout),
|
||||
build.WithKustomizationFile(buildKsArgs.kustomizationFile),
|
||||
build.WithIgnore(buildKsArgs.ignorePaths),
|
||||
)
|
||||
}
|
||||
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
// create a signal channel
|
||||
sigc := make(chan os.Signal, 1)
|
||||
signal.Notify(sigc, os.Interrupt)
|
||||
|
||||
errChan := make(chan error)
|
||||
go func() {
|
||||
objects, err := builder.Build()
|
||||
if err != nil {
|
||||
errChan <- err
|
||||
}
|
||||
|
||||
manifests, err := ssa.ObjectsToYAML(objects)
|
||||
if err != nil {
|
||||
errChan <- err
|
||||
}
|
||||
|
||||
cmd.Print(manifests)
|
||||
errChan <- nil
|
||||
}()
|
||||
|
||||
select {
|
||||
case <-sigc:
|
||||
fmt.Println("Build cancelled... exiting.")
|
||||
return builder.Cancel()
|
||||
case err := <-errChan:
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
|
||||
return nil
|
||||
|
||||
}
|
||||
202
cmd/flux/build_kustomization_test.go
Normal file
202
cmd/flux/build_kustomization_test.go
Normal file
@@ -0,0 +1,202 @@
|
||||
//go:build unit
|
||||
// +build unit
|
||||
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"bytes"
|
||||
"os"
|
||||
"testing"
|
||||
"text/template"
|
||||
)
|
||||
|
||||
func setup(t *testing.T, tmpl map[string]string) {
|
||||
t.Helper()
|
||||
testEnv.CreateObjectFile("./testdata/build-kustomization/podinfo-source.yaml", tmpl, t)
|
||||
testEnv.CreateObjectFile("./testdata/build-kustomization/podinfo-kustomization.yaml", tmpl, t)
|
||||
}
|
||||
|
||||
func TestBuildKustomization(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
resultFile string
|
||||
assertFunc string
|
||||
}{
|
||||
{
|
||||
name: "no args",
|
||||
args: "build kustomization podinfo",
|
||||
resultFile: "invalid resource path \"\"",
|
||||
assertFunc: "assertError",
|
||||
},
|
||||
{
|
||||
name: "build podinfo",
|
||||
args: "build kustomization podinfo --path ./testdata/build-kustomization/podinfo",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "build podinfo without service",
|
||||
args: "build kustomization podinfo --path ./testdata/build-kustomization/delete-service",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-without-service-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "build deployment and configmap with var substitution",
|
||||
args: "build kustomization podinfo --path ./testdata/build-kustomization/var-substitution",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-with-var-substitution-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "build ignore",
|
||||
args: "build kustomization podinfo --path ./testdata/build-kustomization/ignore --ignore-paths \"!configmap.yaml,!secret.yaml\"",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-with-ignore-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
}
|
||||
|
||||
tmpl := map[string]string{
|
||||
"fluxns": allocateNamespace("flux-system"),
|
||||
}
|
||||
setup(t, tmpl)
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
var assert assertFunc
|
||||
|
||||
switch tt.assertFunc {
|
||||
case "assertGoldenTemplateFile":
|
||||
assert = assertGoldenTemplateFile(tt.resultFile, tmpl)
|
||||
case "assertError":
|
||||
assert = assertError(tt.resultFile)
|
||||
}
|
||||
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args + " -n " + tmpl["fluxns"],
|
||||
assert: assert,
|
||||
}
|
||||
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
|
||||
func TestBuildLocalKustomization(t *testing.T) {
|
||||
podinfo := `apiVersion: kustomize.toolkit.fluxcd.io/v1
|
||||
kind: Kustomization
|
||||
metadata:
|
||||
name: podinfo
|
||||
namespace: {{ .fluxns }}
|
||||
spec:
|
||||
interval: 5m0s
|
||||
path: ./kustomize
|
||||
force: true
|
||||
prune: true
|
||||
sourceRef:
|
||||
kind: GitRepository
|
||||
name: podinfo
|
||||
targetNamespace: default
|
||||
postBuild:
|
||||
substitute:
|
||||
cluster_env: "prod"
|
||||
cluster_region: "eu-central-1"
|
||||
`
|
||||
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
resultFile string
|
||||
assertFunc string
|
||||
}{
|
||||
{
|
||||
name: "no args",
|
||||
args: "build kustomization podinfo --kustomization-file ./wrongfile/ --path ./testdata/build-kustomization/podinfo",
|
||||
resultFile: "invalid kustomization file \"./wrongfile/\"",
|
||||
assertFunc: "assertError",
|
||||
},
|
||||
{
|
||||
name: "build podinfo",
|
||||
args: "build kustomization podinfo --kustomization-file ./testdata/build-kustomization/podinfo.yaml --path ./testdata/build-kustomization/podinfo",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "build podinfo without service",
|
||||
args: "build kustomization podinfo --kustomization-file ./testdata/build-kustomization/podinfo.yaml --path ./testdata/build-kustomization/delete-service",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-without-service-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "build deployment and configmap with var substitution",
|
||||
args: "build kustomization podinfo --kustomization-file ./testdata/build-kustomization/podinfo.yaml --path ./testdata/build-kustomization/var-substitution",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-with-var-substitution-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "build deployment and configmap with var substitution in dry-run mode",
|
||||
args: "build kustomization podinfo --kustomization-file ./testdata/build-kustomization/podinfo.yaml --path ./testdata/build-kustomization/var-substitution --dry-run",
|
||||
resultFile: "./testdata/build-kustomization/podinfo-with-var-substitution-result.yaml",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
}
|
||||
|
||||
tmpl := map[string]string{
|
||||
"fluxns": allocateNamespace("flux-system"),
|
||||
}
|
||||
setup(t, tmpl)
|
||||
|
||||
testEnv.CreateObjectFile("./testdata/build-kustomization/podinfo-source.yaml", tmpl, t)
|
||||
|
||||
temp, err := template.New("podinfo").Parse(podinfo)
|
||||
if err != nil {
|
||||
t.Fatal(err)
|
||||
}
|
||||
|
||||
var b bytes.Buffer
|
||||
err = temp.Execute(&b, tmpl)
|
||||
if err != nil {
|
||||
t.Fatal(err)
|
||||
}
|
||||
|
||||
err = os.WriteFile("./testdata/build-kustomization/podinfo.yaml", b.Bytes(), 0666)
|
||||
if err != nil {
|
||||
t.Fatal(err)
|
||||
}
|
||||
t.Cleanup(func() { _ = os.Remove("./testdata/build-kustomization/podinfo.yaml") })
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
var assert assertFunc
|
||||
|
||||
switch tt.assertFunc {
|
||||
case "assertGoldenTemplateFile":
|
||||
assert = assertGoldenTemplateFile(tt.resultFile, tmpl)
|
||||
case "assertError":
|
||||
assert = assertError(tt.resultFile)
|
||||
}
|
||||
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args + " -n " + tmpl["fluxns"],
|
||||
assert: assert,
|
||||
}
|
||||
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
255
cmd/flux/check.go
Normal file
255
cmd/flux/check.go
Normal file
@@ -0,0 +1,255 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"os"
|
||||
"time"
|
||||
|
||||
"github.com/Masterminds/semver/v3"
|
||||
"github.com/spf13/cobra"
|
||||
v1 "k8s.io/api/apps/v1"
|
||||
apiextensionsv1 "k8s.io/apiextensions-apiserver/pkg/apis/apiextensions/v1"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
"github.com/fluxcd/pkg/version"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/install"
|
||||
"github.com/fluxcd/flux2/v2/pkg/status"
|
||||
)
|
||||
|
||||
var checkCmd = &cobra.Command{
|
||||
Use: "check",
|
||||
Short: "Check requirements and installation",
|
||||
Long: withPreviewNote(`The check command will perform a series of checks to validate that
|
||||
the local environment is configured correctly and if the installed components are healthy.`),
|
||||
Example: ` # Run pre-installation checks
|
||||
flux check --pre
|
||||
|
||||
# Run installation checks
|
||||
flux check`,
|
||||
RunE: runCheckCmd,
|
||||
}
|
||||
|
||||
type checkFlags struct {
|
||||
pre bool
|
||||
components []string
|
||||
extraComponents []string
|
||||
pollInterval time.Duration
|
||||
}
|
||||
|
||||
var kubernetesConstraints = []string{
|
||||
">=1.24.0-0",
|
||||
}
|
||||
|
||||
var checkArgs checkFlags
|
||||
|
||||
func init() {
|
||||
checkCmd.Flags().BoolVarP(&checkArgs.pre, "pre", "", false,
|
||||
"only run pre-installation checks")
|
||||
checkCmd.Flags().StringSliceVar(&checkArgs.components, "components", rootArgs.defaults.Components,
|
||||
"list of components, accepts comma-separated values")
|
||||
checkCmd.Flags().StringSliceVar(&checkArgs.extraComponents, "components-extra", nil,
|
||||
"list of components in addition to those supplied or defaulted, accepts comma-separated values")
|
||||
checkCmd.Flags().DurationVar(&checkArgs.pollInterval, "poll-interval", 5*time.Second,
|
||||
"how often the health checker should poll the cluster for the latest state of the resources.")
|
||||
rootCmd.AddCommand(checkCmd)
|
||||
}
|
||||
|
||||
func runCheckCmd(cmd *cobra.Command, args []string) error {
|
||||
logger.Actionf("checking prerequisites")
|
||||
checkFailed := false
|
||||
|
||||
fluxCheck()
|
||||
|
||||
if !kubernetesCheck(kubernetesConstraints) {
|
||||
checkFailed = true
|
||||
}
|
||||
|
||||
if checkArgs.pre {
|
||||
if checkFailed {
|
||||
os.Exit(1)
|
||||
}
|
||||
logger.Successf("prerequisites checks passed")
|
||||
return nil
|
||||
}
|
||||
|
||||
logger.Actionf("checking controllers")
|
||||
if !componentsCheck() {
|
||||
checkFailed = true
|
||||
}
|
||||
|
||||
logger.Actionf("checking crds")
|
||||
if !crdsCheck() {
|
||||
checkFailed = true
|
||||
}
|
||||
|
||||
if checkFailed {
|
||||
logger.Failuref("check failed")
|
||||
os.Exit(1)
|
||||
}
|
||||
|
||||
logger.Successf("all checks passed")
|
||||
return nil
|
||||
}
|
||||
|
||||
func fluxCheck() {
|
||||
curSv, err := version.ParseVersion(VERSION)
|
||||
if err != nil {
|
||||
return
|
||||
}
|
||||
// Exclude development builds.
|
||||
if curSv.Prerelease() != "" {
|
||||
return
|
||||
}
|
||||
latest, err := install.GetLatestVersion()
|
||||
if err != nil {
|
||||
return
|
||||
}
|
||||
latestSv, err := version.ParseVersion(latest)
|
||||
if err != nil {
|
||||
return
|
||||
}
|
||||
if latestSv.GreaterThan(curSv) {
|
||||
logger.Failuref("flux %s <%s (new version is available, please upgrade)", curSv, latestSv)
|
||||
}
|
||||
}
|
||||
|
||||
func kubernetesCheck(constraints []string) bool {
|
||||
cfg, err := utils.KubeConfig(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
logger.Failuref("Kubernetes client initialization failed: %s", err.Error())
|
||||
return false
|
||||
}
|
||||
|
||||
clientSet, err := kubernetes.NewForConfig(cfg)
|
||||
if err != nil {
|
||||
logger.Failuref("Kubernetes client initialization failed: %s", err.Error())
|
||||
return false
|
||||
}
|
||||
|
||||
kv, err := clientSet.Discovery().ServerVersion()
|
||||
if err != nil {
|
||||
logger.Failuref("Kubernetes API call failed: %s", err.Error())
|
||||
return false
|
||||
}
|
||||
|
||||
v, err := version.ParseVersion(kv.String())
|
||||
if err != nil {
|
||||
logger.Failuref("Kubernetes version can't be determined")
|
||||
return false
|
||||
}
|
||||
|
||||
var valid bool
|
||||
var vrange string
|
||||
for _, constraint := range constraints {
|
||||
c, _ := semver.NewConstraint(constraint)
|
||||
if c.Check(v) {
|
||||
valid = true
|
||||
vrange = constraint
|
||||
break
|
||||
}
|
||||
}
|
||||
|
||||
if !valid {
|
||||
logger.Failuref("Kubernetes version %s does not match %s", v.Original(), constraints[0])
|
||||
return false
|
||||
}
|
||||
|
||||
logger.Successf("Kubernetes %s %s", v.String(), vrange)
|
||||
return true
|
||||
}
|
||||
|
||||
func componentsCheck() bool {
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeConfig, err := utils.KubeConfig(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return false
|
||||
}
|
||||
|
||||
statusChecker, err := status.NewStatusChecker(kubeConfig, checkArgs.pollInterval, rootArgs.timeout, logger)
|
||||
if err != nil {
|
||||
return false
|
||||
}
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return false
|
||||
}
|
||||
|
||||
ok := true
|
||||
selector := client.MatchingLabels{manifestgen.PartOfLabelKey: manifestgen.PartOfLabelValue}
|
||||
var list v1.DeploymentList
|
||||
ns := *kubeconfigArgs.Namespace
|
||||
if err := kubeClient.List(ctx, &list, client.InNamespace(ns), selector); err == nil {
|
||||
if len(list.Items) == 0 {
|
||||
logger.Failuref("no controllers found in the '%s' namespace with the label selector '%s=%s'",
|
||||
ns, manifestgen.PartOfLabelKey, manifestgen.PartOfLabelValue)
|
||||
return false
|
||||
}
|
||||
|
||||
for _, d := range list.Items {
|
||||
if ref, err := buildComponentObjectRefs(d.Name); err == nil {
|
||||
if err := statusChecker.Assess(ref...); err != nil {
|
||||
ok = false
|
||||
}
|
||||
}
|
||||
for _, c := range d.Spec.Template.Spec.Containers {
|
||||
logger.Actionf(c.Image)
|
||||
}
|
||||
}
|
||||
}
|
||||
return ok
|
||||
}
|
||||
|
||||
func crdsCheck() bool {
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return false
|
||||
}
|
||||
|
||||
ok := true
|
||||
selector := client.MatchingLabels{manifestgen.PartOfLabelKey: manifestgen.PartOfLabelValue}
|
||||
var list apiextensionsv1.CustomResourceDefinitionList
|
||||
if err := kubeClient.List(ctx, &list, client.InNamespace(*kubeconfigArgs.Namespace), selector); err == nil {
|
||||
if len(list.Items) == 0 {
|
||||
logger.Failuref("no crds found with the label selector '%s=%s'",
|
||||
manifestgen.PartOfLabelKey, manifestgen.PartOfLabelValue)
|
||||
return false
|
||||
}
|
||||
|
||||
for _, crd := range list.Items {
|
||||
versions := crd.Status.StoredVersions
|
||||
if len(versions) > 0 {
|
||||
logger.Successf(crd.Name + "/" + versions[len(versions)-1])
|
||||
} else {
|
||||
ok = false
|
||||
logger.Failuref("no stored versions for %s", crd.Name)
|
||||
}
|
||||
}
|
||||
}
|
||||
return ok
|
||||
}
|
||||
53
cmd/flux/check_test.go
Normal file
53
cmd/flux/check_test.go
Normal file
@@ -0,0 +1,53 @@
|
||||
//go:build e2e
|
||||
// +build e2e
|
||||
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"encoding/json"
|
||||
"strings"
|
||||
"testing"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
func TestCheckPre(t *testing.T) {
|
||||
jsonOutput, err := utils.ExecKubectlCommand(context.TODO(), utils.ModeCapture, *kubeconfigArgs.KubeConfig, *kubeconfigArgs.Context, "version", "--output", "json")
|
||||
if err != nil {
|
||||
t.Fatalf("Error running utils.ExecKubectlCommand: %v", err.Error())
|
||||
}
|
||||
|
||||
var versions map[string]interface{}
|
||||
if err := json.Unmarshal([]byte(jsonOutput), &versions); err != nil {
|
||||
t.Fatalf("Error unmarshalling '%s': %v", jsonOutput, err.Error())
|
||||
}
|
||||
|
||||
serverGitVersion := strings.TrimPrefix(
|
||||
versions["serverVersion"].(map[string]interface{})["gitVersion"].(string),
|
||||
"v")
|
||||
|
||||
cmd := cmdTestCase{
|
||||
args: "check --pre",
|
||||
assert: assertGoldenTemplateFile("testdata/check/check_pre.golden", map[string]string{
|
||||
"serverVersion": serverGitVersion,
|
||||
}),
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
}
|
||||
112
cmd/flux/completion.go
Normal file
112
cmd/flux/completion.go
Normal file
@@ -0,0 +1,112 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"strings"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/runtime/schema"
|
||||
"k8s.io/client-go/dynamic"
|
||||
)
|
||||
|
||||
var completionCmd = &cobra.Command{
|
||||
Use: "completion",
|
||||
Short: "Generates completion scripts for various shells",
|
||||
Long: `The completion sub-command generates completion scripts for various shells.`,
|
||||
}
|
||||
|
||||
func init() {
|
||||
rootCmd.AddCommand(completionCmd)
|
||||
}
|
||||
|
||||
func contextsCompletionFunc(cmd *cobra.Command, args []string, toComplete string) ([]string, cobra.ShellCompDirective) {
|
||||
rawConfig, err := kubeconfigArgs.ToRawKubeConfigLoader().RawConfig()
|
||||
if err != nil {
|
||||
return completionError(err)
|
||||
}
|
||||
|
||||
var comps []string
|
||||
|
||||
for name := range rawConfig.Contexts {
|
||||
if strings.HasPrefix(name, toComplete) {
|
||||
comps = append(comps, name)
|
||||
}
|
||||
}
|
||||
|
||||
return comps, cobra.ShellCompDirectiveNoFileComp
|
||||
}
|
||||
|
||||
func resourceNamesCompletionFunc(gvk schema.GroupVersionKind) func(cmd *cobra.Command, args []string, toComplete string) ([]string, cobra.ShellCompDirective) {
|
||||
return func(cmd *cobra.Command, args []string, toComplete string) ([]string, cobra.ShellCompDirective) {
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
cfg, err := utils.KubeConfig(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return completionError(err)
|
||||
}
|
||||
|
||||
mapper, err := kubeconfigArgs.ToRESTMapper()
|
||||
if err != nil {
|
||||
return completionError(err)
|
||||
}
|
||||
|
||||
mapping, err := mapper.RESTMapping(gvk.GroupKind(), gvk.Version)
|
||||
if err != nil {
|
||||
return completionError(err)
|
||||
}
|
||||
|
||||
client, err := dynamic.NewForConfig(cfg)
|
||||
if err != nil {
|
||||
return completionError(err)
|
||||
}
|
||||
|
||||
var dr dynamic.ResourceInterface
|
||||
if mapping.Scope.Name() == meta.RESTScopeNameNamespace {
|
||||
dr = client.Resource(mapping.Resource).Namespace(*kubeconfigArgs.Namespace)
|
||||
} else {
|
||||
dr = client.Resource(mapping.Resource)
|
||||
}
|
||||
|
||||
list, err := dr.List(ctx, metav1.ListOptions{})
|
||||
if err != nil {
|
||||
return completionError(err)
|
||||
}
|
||||
|
||||
var comps []string
|
||||
|
||||
for _, item := range list.Items {
|
||||
name := item.GetName()
|
||||
|
||||
if strings.HasPrefix(name, toComplete) {
|
||||
comps = append(comps, name)
|
||||
}
|
||||
}
|
||||
|
||||
return comps, cobra.ShellCompDirectiveNoFileComp
|
||||
}
|
||||
}
|
||||
|
||||
func completionError(err error) ([]string, cobra.ShellCompDirective) {
|
||||
cobra.CompError(err.Error())
|
||||
return nil, cobra.ShellCompDirectiveError
|
||||
}
|
||||
44
cmd/flux/completion_bash.go
Normal file
44
cmd/flux/completion_bash.go
Normal file
@@ -0,0 +1,44 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var completionBashCmd = &cobra.Command{
|
||||
Use: "bash",
|
||||
Short: "Generates bash completion scripts",
|
||||
Long: `The completion sub-command generates completion scripts for bash.`,
|
||||
Example: `To load completion run
|
||||
|
||||
. <(flux completion bash)
|
||||
|
||||
To configure your bash shell to load completions for each session add to your bashrc
|
||||
|
||||
# ~/.bashrc or ~/.profile
|
||||
command -v flux >/dev/null && . <(flux completion bash)`,
|
||||
Run: func(cmd *cobra.Command, args []string) {
|
||||
rootCmd.GenBashCompletion(os.Stdout)
|
||||
},
|
||||
}
|
||||
|
||||
func init() {
|
||||
completionCmd.AddCommand(completionBashCmd)
|
||||
}
|
||||
41
cmd/flux/completion_fish.go
Normal file
41
cmd/flux/completion_fish.go
Normal file
@@ -0,0 +1,41 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var completionFishCmd = &cobra.Command{
|
||||
Use: "fish",
|
||||
Short: "Generates fish completion scripts",
|
||||
Long: `The completion sub-command generates completion scripts for fish.`,
|
||||
Example: `To configure your fish shell to load completions for each session write this script to your completions dir:
|
||||
|
||||
flux completion fish > ~/.config/fish/completions/flux.fish
|
||||
|
||||
See http://fishshell.com/docs/current/index.html#completion-own for more details`,
|
||||
Run: func(cmd *cobra.Command, args []string) {
|
||||
rootCmd.GenFishCompletion(os.Stdout, true)
|
||||
},
|
||||
}
|
||||
|
||||
func init() {
|
||||
completionCmd.AddCommand(completionFishCmd)
|
||||
}
|
||||
51
cmd/flux/completion_powershell.go
Normal file
51
cmd/flux/completion_powershell.go
Normal file
@@ -0,0 +1,51 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var completionPowerShellCmd = &cobra.Command{
|
||||
Use: "powershell",
|
||||
Short: "Generates powershell completion scripts",
|
||||
Long: `The completion sub-command generates completion scripts for powershell.`,
|
||||
Example: `To load completion run
|
||||
|
||||
. <(flux completion powershell)
|
||||
|
||||
To configure your powershell shell to load completions for each session add to your powershell profile
|
||||
|
||||
Windows:
|
||||
|
||||
cd "$env:USERPROFILE\Documents\WindowsPowerShell\Modules"
|
||||
flux completion powershell >> flux-completion.ps1
|
||||
|
||||
Linux:
|
||||
|
||||
cd "${XDG_CONFIG_HOME:-"$HOME/.config/"}/powershell/modules"
|
||||
flux completion powershell >> flux-completions.ps1`,
|
||||
Run: func(cmd *cobra.Command, args []string) {
|
||||
rootCmd.GenPowerShellCompletion(os.Stdout)
|
||||
},
|
||||
}
|
||||
|
||||
func init() {
|
||||
completionCmd.AddCommand(completionPowerShellCmd)
|
||||
}
|
||||
55
cmd/flux/completion_zsh.go
Normal file
55
cmd/flux/completion_zsh.go
Normal file
@@ -0,0 +1,55 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var completionZshCmd = &cobra.Command{
|
||||
Use: "zsh",
|
||||
Short: "Generates zsh completion scripts",
|
||||
Long: `The completion sub-command generates completion scripts for zsh.`,
|
||||
Example: `To load completion run
|
||||
|
||||
. <(flux completion zsh)
|
||||
|
||||
To configure your zsh shell to load completions for each session add to your zshrc
|
||||
|
||||
# ~/.zshrc or ~/.profile
|
||||
command -v flux >/dev/null && . <(flux completion zsh)
|
||||
|
||||
or write a cached file in one of the completion directories in your ${fpath}:
|
||||
|
||||
echo "${fpath// /\n}" | grep -i completion
|
||||
flux completion zsh > _flux
|
||||
|
||||
mv _flux ~/.oh-my-zsh/completions # oh-my-zsh
|
||||
mv _flux ~/.zprezto/modules/completion/external/src/ # zprezto`,
|
||||
Run: func(cmd *cobra.Command, args []string) {
|
||||
rootCmd.GenZshCompletion(os.Stdout)
|
||||
// Cobra doesn't source zsh completion file, explicitly doing it here
|
||||
fmt.Println("compdef _flux flux")
|
||||
},
|
||||
}
|
||||
|
||||
func init() {
|
||||
completionCmd.AddCommand(completionZshCmd)
|
||||
}
|
||||
170
cmd/flux/create.go
Normal file
170
cmd/flux/create.go
Normal file
@@ -0,0 +1,170 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"regexp"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/validation"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
"sigs.k8s.io/controller-runtime/pkg/controller/controllerutil"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createCmd = &cobra.Command{
|
||||
Use: "create",
|
||||
Short: "Create or update sources and resources",
|
||||
Long: `The create sub-commands generate sources and resources.`,
|
||||
}
|
||||
|
||||
type createFlags struct {
|
||||
interval time.Duration
|
||||
export bool
|
||||
labels []string
|
||||
}
|
||||
|
||||
var createArgs createFlags
|
||||
|
||||
func init() {
|
||||
createCmd.PersistentFlags().DurationVarP(&createArgs.interval, "interval", "", time.Minute, "source sync interval")
|
||||
createCmd.PersistentFlags().BoolVar(&createArgs.export, "export", false, "export in YAML format to stdout")
|
||||
createCmd.PersistentFlags().StringSliceVar(&createArgs.labels, "label", nil,
|
||||
"set labels on the resource (can specify multiple labels with commas: label1=value1,label2=value2)")
|
||||
createCmd.PersistentPreRunE = func(cmd *cobra.Command, args []string) error {
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("name is required")
|
||||
}
|
||||
|
||||
name := args[0]
|
||||
if !validateObjectName(name) {
|
||||
return fmt.Errorf("name '%s' is invalid, it should adhere to standard defined in RFC 1123, the name can only contain alphanumeric characters or '-'", name)
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
rootCmd.AddCommand(createCmd)
|
||||
}
|
||||
|
||||
// upsertable is an interface for values that can be used in `upsert`.
|
||||
type upsertable interface {
|
||||
adapter
|
||||
named
|
||||
}
|
||||
|
||||
// upsert updates or inserts an object. Instead of providing the
|
||||
// object itself, you provide a named (as in Name and Namespace)
|
||||
// template value, and a mutate function which sets the values you
|
||||
// want to update. The mutate function is nullary -- you mutate a
|
||||
// value in the closure, e.g., by doing this:
|
||||
//
|
||||
// var existing Value
|
||||
// existing.Name = name
|
||||
// existing.Namespace = ns
|
||||
// upsert(ctx, client, valueAdapter{&value}, func() error {
|
||||
// value.Spec = onePreparedEarlier
|
||||
// })
|
||||
func (names apiType) upsert(ctx context.Context, kubeClient client.Client, object upsertable, mutate func() error) (types.NamespacedName, error) {
|
||||
nsname := types.NamespacedName{
|
||||
Namespace: object.GetNamespace(),
|
||||
Name: object.GetName(),
|
||||
}
|
||||
|
||||
op, err := controllerutil.CreateOrUpdate(ctx, kubeClient, object.asClientObject(), mutate)
|
||||
if err != nil {
|
||||
return nsname, err
|
||||
}
|
||||
|
||||
switch op {
|
||||
case controllerutil.OperationResultCreated:
|
||||
logger.Successf("%s created", names.kind)
|
||||
case controllerutil.OperationResultUpdated:
|
||||
logger.Successf("%s updated", names.kind)
|
||||
}
|
||||
return nsname, nil
|
||||
}
|
||||
|
||||
type upsertWaitable interface {
|
||||
upsertable
|
||||
statusable
|
||||
}
|
||||
|
||||
// upsertAndWait encodes the pattern of creating or updating a
|
||||
// resource, then waiting for it to reconcile. See the note on
|
||||
// `upsert` for how to work with the `mutate` argument.
|
||||
func (names apiType) upsertAndWait(object upsertWaitable, mutate func() error) error {
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions) // NB globals
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Generatef("generating %s", names.kind)
|
||||
logger.Actionf("applying %s", names.kind)
|
||||
|
||||
namespacedName, err := imageRepositoryType.upsert(ctx, kubeClient, object, mutate)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for %s reconciliation", names.kind)
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isReady(ctx, kubeClient, namespacedName, object)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("%s reconciliation completed", names.kind)
|
||||
return nil
|
||||
}
|
||||
|
||||
func parseLabels() (map[string]string, error) {
|
||||
result := make(map[string]string)
|
||||
for _, label := range createArgs.labels {
|
||||
// validate key value pair
|
||||
parts := strings.Split(label, "=")
|
||||
if len(parts) != 2 {
|
||||
return nil, fmt.Errorf("invalid label format '%s', must be key=value", label)
|
||||
}
|
||||
|
||||
// validate label name
|
||||
if errors := validation.IsQualifiedName(parts[0]); len(errors) > 0 {
|
||||
return nil, fmt.Errorf("invalid label '%s': %v", parts[0], errors)
|
||||
}
|
||||
|
||||
// validate label value
|
||||
if errors := validation.IsValidLabelValue(parts[1]); len(errors) > 0 {
|
||||
return nil, fmt.Errorf("invalid label value '%s': %v", parts[1], errors)
|
||||
}
|
||||
|
||||
result[parts[0]] = parts[1]
|
||||
}
|
||||
|
||||
return result, nil
|
||||
}
|
||||
|
||||
func validateObjectName(name string) bool {
|
||||
r := regexp.MustCompile("^[a-z0-9]([a-z0-9\\-]){0,61}[a-z0-9]$")
|
||||
return r.MatchString(name)
|
||||
}
|
||||
192
cmd/flux/create_alert.go
Normal file
192
cmd/flux/create_alert.go
Normal file
@@ -0,0 +1,192 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
apimeta "k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1"
|
||||
notificationv1b2 "github.com/fluxcd/notification-controller/api/v1beta2"
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createAlertCmd = &cobra.Command{
|
||||
Use: "alert [name]",
|
||||
Short: "Create or update a Alert resource",
|
||||
Long: withPreviewNote(`The create alert command generates a Alert resource.`),
|
||||
Example: ` # Create an Alert for kustomization events
|
||||
flux create alert \
|
||||
--event-severity info \
|
||||
--event-source Kustomization/flux-system \
|
||||
--provider-ref slack \
|
||||
flux-system`,
|
||||
RunE: createAlertCmdRun,
|
||||
}
|
||||
|
||||
type alertFlags struct {
|
||||
providerRef string
|
||||
eventSeverity string
|
||||
eventSources []string
|
||||
}
|
||||
|
||||
var alertArgs alertFlags
|
||||
|
||||
func init() {
|
||||
createAlertCmd.Flags().StringVar(&alertArgs.providerRef, "provider-ref", "", "reference to provider")
|
||||
createAlertCmd.Flags().StringVar(&alertArgs.eventSeverity, "event-severity", "", "severity of events to send alerts for")
|
||||
createAlertCmd.Flags().StringSliceVar(&alertArgs.eventSources, "event-source", []string{}, "sources that should generate alerts (<kind>/<name>), also accepts comma-separated values")
|
||||
createCmd.AddCommand(createAlertCmd)
|
||||
}
|
||||
|
||||
func createAlertCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if alertArgs.providerRef == "" {
|
||||
return fmt.Errorf("provider ref is required")
|
||||
}
|
||||
|
||||
eventSources := []notificationv1.CrossNamespaceObjectReference{}
|
||||
for _, eventSource := range alertArgs.eventSources {
|
||||
kind, name, namespace := utils.ParseObjectKindNameNamespace(eventSource)
|
||||
if kind == "" {
|
||||
return fmt.Errorf("invalid event source '%s', must be in format <kind>/<name>", eventSource)
|
||||
}
|
||||
|
||||
eventSources = append(eventSources, notificationv1.CrossNamespaceObjectReference{
|
||||
Kind: kind,
|
||||
Name: name,
|
||||
Namespace: namespace,
|
||||
})
|
||||
}
|
||||
|
||||
if len(eventSources) == 0 {
|
||||
return fmt.Errorf("at least one event source is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if !createArgs.export {
|
||||
logger.Generatef("generating Alert")
|
||||
}
|
||||
|
||||
alert := notificationv1b2.Alert{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: notificationv1b2.AlertSpec{
|
||||
ProviderRef: meta.LocalObjectReference{
|
||||
Name: alertArgs.providerRef,
|
||||
},
|
||||
EventSeverity: alertArgs.eventSeverity,
|
||||
EventSources: eventSources,
|
||||
Suspend: false,
|
||||
},
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportAlert(&alert))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying Alert")
|
||||
namespacedName, err := upsertAlert(ctx, kubeClient, &alert)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for Alert reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isAlertReady(ctx, kubeClient, namespacedName, &alert)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("Alert %s is ready", name)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertAlert(ctx context.Context, kubeClient client.Client,
|
||||
alert *notificationv1b2.Alert) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: alert.GetNamespace(),
|
||||
Name: alert.GetName(),
|
||||
}
|
||||
|
||||
var existing notificationv1b2.Alert
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, alert); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("Alert created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = alert.Labels
|
||||
existing.Spec = alert.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
alert = &existing
|
||||
logger.Successf("Alert updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isAlertReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, alert *notificationv1b2.Alert) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, alert)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := apimeta.FindStatusCondition(alert.Status.Conditions, meta.ReadyCondition); c != nil {
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
189
cmd/flux/create_alertprovider.go
Normal file
189
cmd/flux/create_alertprovider.go
Normal file
@@ -0,0 +1,189 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
apimeta "k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1beta2"
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createAlertProviderCmd = &cobra.Command{
|
||||
Use: "alert-provider [name]",
|
||||
Short: "Create or update a Provider resource",
|
||||
Long: withPreviewNote(`The create alert-provider command generates a Provider resource.`),
|
||||
Example: ` # Create a Provider for a Slack channel
|
||||
flux create alert-provider slack \
|
||||
--type slack \
|
||||
--channel general \
|
||||
--address https://hooks.slack.com/services/YOUR/SLACK/WEBHOOK \
|
||||
--secret-ref webhook-url
|
||||
|
||||
# Create a Provider for a Github repository
|
||||
flux create alert-provider github-podinfo \
|
||||
--type github \
|
||||
--address https://github.com/stefanprodan/podinfo \
|
||||
--secret-ref github-token`,
|
||||
RunE: createAlertProviderCmdRun,
|
||||
}
|
||||
|
||||
type alertProviderFlags struct {
|
||||
alertType string
|
||||
channel string
|
||||
username string
|
||||
address string
|
||||
secretRef string
|
||||
}
|
||||
|
||||
var alertProviderArgs alertProviderFlags
|
||||
|
||||
func init() {
|
||||
createAlertProviderCmd.Flags().StringVar(&alertProviderArgs.alertType, "type", "", "type of provider")
|
||||
createAlertProviderCmd.Flags().StringVar(&alertProviderArgs.channel, "channel", "", "channel to send messages to in the case of a chat provider")
|
||||
createAlertProviderCmd.Flags().StringVar(&alertProviderArgs.username, "username", "", "bot username used by the provider")
|
||||
createAlertProviderCmd.Flags().StringVar(&alertProviderArgs.address, "address", "", "path to either the git repository, chat provider or webhook")
|
||||
createAlertProviderCmd.Flags().StringVar(&alertProviderArgs.secretRef, "secret-ref", "", "name of secret containing authentication token")
|
||||
createCmd.AddCommand(createAlertProviderCmd)
|
||||
}
|
||||
|
||||
func createAlertProviderCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if alertProviderArgs.alertType == "" {
|
||||
return fmt.Errorf("Provider type is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if !createArgs.export {
|
||||
logger.Generatef("generating Provider")
|
||||
}
|
||||
|
||||
provider := notificationv1.Provider{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: notificationv1.ProviderSpec{
|
||||
Type: alertProviderArgs.alertType,
|
||||
Channel: alertProviderArgs.channel,
|
||||
Username: alertProviderArgs.username,
|
||||
Address: alertProviderArgs.address,
|
||||
},
|
||||
}
|
||||
|
||||
if alertProviderArgs.secretRef != "" {
|
||||
provider.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: alertProviderArgs.secretRef,
|
||||
}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportAlertProvider(&provider))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying Provider")
|
||||
namespacedName, err := upsertAlertProvider(ctx, kubeClient, &provider)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for Provider reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isAlertProviderReady(ctx, kubeClient, namespacedName, &provider)); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Successf("Provider %s is ready", name)
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertAlertProvider(ctx context.Context, kubeClient client.Client,
|
||||
provider *notificationv1.Provider) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: provider.GetNamespace(),
|
||||
Name: provider.GetName(),
|
||||
}
|
||||
|
||||
var existing notificationv1.Provider
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, provider); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("Provider created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = provider.Labels
|
||||
existing.Spec = provider.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
provider = &existing
|
||||
logger.Successf("Provider updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isAlertProviderReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, provider *notificationv1.Provider) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, provider)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := apimeta.FindStatusCondition(provider.Status.Conditions, meta.ReadyCondition); c != nil {
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
374
cmd/flux/create_helmrelease.go
Normal file
374
cmd/flux/create_helmrelease.go
Normal file
@@ -0,0 +1,374 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"encoding/json"
|
||||
"fmt"
|
||||
"os"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
"github.com/fluxcd/pkg/runtime/transform"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
apiextensionsv1 "k8s.io/apiextensions-apiserver/pkg/apis/apiextensions/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
apimeta "k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
"sigs.k8s.io/yaml"
|
||||
|
||||
helmv2 "github.com/fluxcd/helm-controller/api/v2beta1"
|
||||
)
|
||||
|
||||
var createHelmReleaseCmd = &cobra.Command{
|
||||
Use: "helmrelease [name]",
|
||||
Aliases: []string{"hr"},
|
||||
Short: "Create or update a HelmRelease resource",
|
||||
Long: withPreviewNote(`The helmrelease create command generates a HelmRelease resource for a given HelmRepository source.`),
|
||||
Example: ` # Create a HelmRelease with a chart from a HelmRepository source
|
||||
flux create hr podinfo \
|
||||
--interval=10m \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo \
|
||||
--chart-version=">4.0.0"
|
||||
|
||||
# Create a HelmRelease with a chart from a GitRepository source
|
||||
flux create hr podinfo \
|
||||
--interval=10m \
|
||||
--source=GitRepository/podinfo \
|
||||
--chart=./charts/podinfo
|
||||
|
||||
# Create a HelmRelease with a chart from a Bucket source
|
||||
flux create hr podinfo \
|
||||
--interval=10m \
|
||||
--source=Bucket/podinfo \
|
||||
--chart=./charts/podinfo
|
||||
|
||||
# Create a HelmRelease with values from local YAML files
|
||||
flux create hr podinfo \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo \
|
||||
--values=./my-values1.yaml \
|
||||
--values=./my-values2.yaml
|
||||
|
||||
# Create a HelmRelease with values from a Kubernetes secret
|
||||
kubectl -n app create secret generic my-secret-values \
|
||||
--from-file=values.yaml=/path/to/my-secret-values.yaml
|
||||
flux -n app create hr podinfo \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo \
|
||||
--values-from=Secret/my-secret-values
|
||||
|
||||
# Create a HelmRelease with a custom release name
|
||||
flux create hr podinfo \
|
||||
--release-name=podinfo-dev \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo
|
||||
|
||||
# Create a HelmRelease targeting another namespace than the resource
|
||||
flux create hr podinfo \
|
||||
--target-namespace=test \
|
||||
--create-target-namespace=true \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo
|
||||
|
||||
# Create a HelmRelease using a source from a different namespace
|
||||
flux create hr podinfo \
|
||||
--namespace=default \
|
||||
--source=HelmRepository/podinfo.flux-system \
|
||||
--chart=podinfo
|
||||
|
||||
# Create a HelmRelease definition on disk without applying it on the cluster
|
||||
flux create hr podinfo \
|
||||
--source=HelmRepository/podinfo \
|
||||
--chart=podinfo \
|
||||
--values=./values.yaml \
|
||||
--export > podinfo-release.yaml`,
|
||||
RunE: createHelmReleaseCmdRun,
|
||||
}
|
||||
|
||||
type helmReleaseFlags struct {
|
||||
name string
|
||||
source flags.HelmChartSource
|
||||
dependsOn []string
|
||||
chart string
|
||||
chartVersion string
|
||||
targetNamespace string
|
||||
createNamespace bool
|
||||
valuesFiles []string
|
||||
valuesFrom []string
|
||||
saName string
|
||||
crds flags.CRDsPolicy
|
||||
reconcileStrategy string
|
||||
chartInterval time.Duration
|
||||
kubeConfigSecretRef string
|
||||
}
|
||||
|
||||
var helmReleaseArgs helmReleaseFlags
|
||||
|
||||
var supportedHelmReleaseValuesFromKinds = []string{"Secret", "ConfigMap"}
|
||||
|
||||
func init() {
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.name, "release-name", "", "name used for the Helm release, defaults to a composition of '[<target-namespace>-]<HelmRelease-name>'")
|
||||
createHelmReleaseCmd.Flags().Var(&helmReleaseArgs.source, "source", helmReleaseArgs.source.Description())
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.chart, "chart", "", "Helm chart name or path")
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.chartVersion, "chart-version", "", "Helm chart version, accepts a semver range (ignored for charts from GitRepository sources)")
|
||||
createHelmReleaseCmd.Flags().StringSliceVar(&helmReleaseArgs.dependsOn, "depends-on", nil, "HelmReleases that must be ready before this release can be installed, supported formats '<name>' and '<namespace>/<name>'")
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.targetNamespace, "target-namespace", "", "namespace to install this release, defaults to the HelmRelease namespace")
|
||||
createHelmReleaseCmd.Flags().BoolVar(&helmReleaseArgs.createNamespace, "create-target-namespace", false, "create the target namespace if it does not exist")
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.saName, "service-account", "", "the name of the service account to impersonate when reconciling this HelmRelease")
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.reconcileStrategy, "reconcile-strategy", "ChartVersion", "the reconcile strategy for helm chart created by the helm release(accepted values: Revision and ChartRevision)")
|
||||
createHelmReleaseCmd.Flags().DurationVarP(&helmReleaseArgs.chartInterval, "chart-interval", "", 0, "the interval of which to check for new chart versions")
|
||||
createHelmReleaseCmd.Flags().StringSliceVar(&helmReleaseArgs.valuesFiles, "values", nil, "local path to values.yaml files, also accepts comma-separated values")
|
||||
createHelmReleaseCmd.Flags().StringSliceVar(&helmReleaseArgs.valuesFrom, "values-from", nil, "a Kubernetes object reference that contains the values.yaml data key in the format '<kind>/<name>', where kind must be one of: (Secret,ConfigMap)")
|
||||
createHelmReleaseCmd.Flags().Var(&helmReleaseArgs.crds, "crds", helmReleaseArgs.crds.Description())
|
||||
createHelmReleaseCmd.Flags().StringVar(&helmReleaseArgs.kubeConfigSecretRef, "kubeconfig-secret-ref", "", "the name of the Kubernetes Secret that contains a key with the kubeconfig file for connecting to a remote cluster")
|
||||
createCmd.AddCommand(createHelmReleaseCmd)
|
||||
}
|
||||
|
||||
func createHelmReleaseCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if helmReleaseArgs.chart == "" {
|
||||
return fmt.Errorf("chart name or path is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if !createArgs.export {
|
||||
logger.Generatef("generating HelmRelease")
|
||||
}
|
||||
|
||||
if !validateStrategy(helmReleaseArgs.reconcileStrategy) {
|
||||
return fmt.Errorf("'%s' is an invalid reconcile strategy(valid: Revision, ChartVersion)",
|
||||
helmReleaseArgs.reconcileStrategy)
|
||||
}
|
||||
|
||||
helmRelease := helmv2.HelmRelease{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: helmv2.HelmReleaseSpec{
|
||||
ReleaseName: helmReleaseArgs.name,
|
||||
DependsOn: utils.MakeDependsOn(helmReleaseArgs.dependsOn),
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
TargetNamespace: helmReleaseArgs.targetNamespace,
|
||||
|
||||
Chart: helmv2.HelmChartTemplate{
|
||||
Spec: helmv2.HelmChartTemplateSpec{
|
||||
Chart: helmReleaseArgs.chart,
|
||||
Version: helmReleaseArgs.chartVersion,
|
||||
SourceRef: helmv2.CrossNamespaceObjectReference{
|
||||
Kind: helmReleaseArgs.source.Kind,
|
||||
Name: helmReleaseArgs.source.Name,
|
||||
Namespace: helmReleaseArgs.source.Namespace,
|
||||
},
|
||||
ReconcileStrategy: helmReleaseArgs.reconcileStrategy,
|
||||
},
|
||||
},
|
||||
Suspend: false,
|
||||
},
|
||||
}
|
||||
|
||||
if helmReleaseArgs.kubeConfigSecretRef != "" {
|
||||
helmRelease.Spec.KubeConfig = &meta.KubeConfigReference{
|
||||
SecretRef: meta.SecretKeyReference{
|
||||
Name: helmReleaseArgs.kubeConfigSecretRef,
|
||||
},
|
||||
}
|
||||
}
|
||||
|
||||
if helmReleaseArgs.chartInterval != 0 {
|
||||
helmRelease.Spec.Chart.Spec.Interval = &metav1.Duration{
|
||||
Duration: helmReleaseArgs.chartInterval,
|
||||
}
|
||||
}
|
||||
|
||||
if helmReleaseArgs.createNamespace {
|
||||
if helmRelease.Spec.Install == nil {
|
||||
helmRelease.Spec.Install = &helmv2.Install{}
|
||||
}
|
||||
|
||||
helmRelease.Spec.Install.CreateNamespace = helmReleaseArgs.createNamespace
|
||||
}
|
||||
|
||||
if helmReleaseArgs.saName != "" {
|
||||
helmRelease.Spec.ServiceAccountName = helmReleaseArgs.saName
|
||||
}
|
||||
|
||||
if helmReleaseArgs.crds != "" {
|
||||
if helmRelease.Spec.Install == nil {
|
||||
helmRelease.Spec.Install = &helmv2.Install{}
|
||||
}
|
||||
|
||||
helmRelease.Spec.Install.CRDs = helmv2.Create
|
||||
helmRelease.Spec.Upgrade = &helmv2.Upgrade{CRDs: helmv2.CRDsPolicy(helmReleaseArgs.crds.String())}
|
||||
}
|
||||
|
||||
if len(helmReleaseArgs.valuesFiles) > 0 {
|
||||
valuesMap := make(map[string]interface{})
|
||||
for _, v := range helmReleaseArgs.valuesFiles {
|
||||
data, err := os.ReadFile(v)
|
||||
if err != nil {
|
||||
return fmt.Errorf("reading values from %s failed: %w", v, err)
|
||||
}
|
||||
|
||||
jsonBytes, err := yaml.YAMLToJSON(data)
|
||||
if err != nil {
|
||||
return fmt.Errorf("converting values to JSON from %s failed: %w", v, err)
|
||||
}
|
||||
|
||||
jsonMap := make(map[string]interface{})
|
||||
if err := json.Unmarshal(jsonBytes, &jsonMap); err != nil {
|
||||
return fmt.Errorf("unmarshaling values from %s failed: %w", v, err)
|
||||
}
|
||||
|
||||
valuesMap = transform.MergeMaps(valuesMap, jsonMap)
|
||||
}
|
||||
|
||||
jsonRaw, err := json.Marshal(valuesMap)
|
||||
if err != nil {
|
||||
return fmt.Errorf("marshaling values failed: %w", err)
|
||||
}
|
||||
|
||||
helmRelease.Spec.Values = &apiextensionsv1.JSON{Raw: jsonRaw}
|
||||
}
|
||||
|
||||
if len(helmReleaseArgs.valuesFrom) != 0 {
|
||||
values := []helmv2.ValuesReference{}
|
||||
for _, value := range helmReleaseArgs.valuesFrom {
|
||||
sourceKind, sourceName := utils.ParseObjectKindName(value)
|
||||
if sourceKind == "" {
|
||||
return fmt.Errorf("invalid Kubernetes object reference '%s', must be in format <kind>/<name>", value)
|
||||
}
|
||||
cleanSourceKind, ok := utils.ContainsEqualFoldItemString(supportedHelmReleaseValuesFromKinds, sourceKind)
|
||||
if !ok {
|
||||
return fmt.Errorf("reference kind '%s' is not supported, must be one of: %s",
|
||||
sourceKind, strings.Join(supportedHelmReleaseValuesFromKinds, ", "))
|
||||
}
|
||||
|
||||
values = append(values, helmv2.ValuesReference{
|
||||
Name: sourceName,
|
||||
Kind: cleanSourceKind,
|
||||
})
|
||||
}
|
||||
helmRelease.Spec.ValuesFrom = values
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportHelmRelease(&helmRelease))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying HelmRelease")
|
||||
namespacedName, err := upsertHelmRelease(ctx, kubeClient, &helmRelease)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for HelmRelease reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isHelmReleaseReady(ctx, kubeClient, namespacedName, &helmRelease)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("HelmRelease %s is ready", name)
|
||||
|
||||
logger.Successf("applied revision %s", helmRelease.Status.LastAppliedRevision)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertHelmRelease(ctx context.Context, kubeClient client.Client,
|
||||
helmRelease *helmv2.HelmRelease) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: helmRelease.GetNamespace(),
|
||||
Name: helmRelease.GetName(),
|
||||
}
|
||||
|
||||
var existing helmv2.HelmRelease
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, helmRelease); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("HelmRelease created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = helmRelease.Labels
|
||||
existing.Spec = helmRelease.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
helmRelease = &existing
|
||||
logger.Successf("HelmRelease updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isHelmReleaseReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, helmRelease *helmv2.HelmRelease) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, helmRelease)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
// Confirm the state we are observing is for the current generation
|
||||
if helmRelease.Generation != helmRelease.Status.ObservedGeneration {
|
||||
return false, nil
|
||||
}
|
||||
|
||||
return apimeta.IsStatusConditionTrue(helmRelease.Status.Conditions, meta.ReadyCondition), nil
|
||||
}
|
||||
}
|
||||
|
||||
func validateStrategy(input string) bool {
|
||||
allowedStrategy := []string{"Revision", "ChartVersion"}
|
||||
|
||||
for _, strategy := range allowedStrategy {
|
||||
if strategy == input {
|
||||
return true
|
||||
}
|
||||
}
|
||||
|
||||
return false
|
||||
}
|
||||
33
cmd/flux/create_image.go
Normal file
33
cmd/flux/create_image.go
Normal file
@@ -0,0 +1,33 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var createImageCmd = &cobra.Command{
|
||||
Use: "image",
|
||||
Short: "Create or update resources dealing with image automation",
|
||||
Long: `The create image sub-commands work with image automation objects;
|
||||
that is, object controlling updates to git based on e.g., new container images
|
||||
being available.`,
|
||||
}
|
||||
|
||||
func init() {
|
||||
createCmd.AddCommand(createImageCmd)
|
||||
}
|
||||
260
cmd/flux/create_image_policy.go
Normal file
260
cmd/flux/create_image_policy.go
Normal file
@@ -0,0 +1,260 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"regexp/syntax"
|
||||
"strings"
|
||||
"unicode"
|
||||
"unicode/utf8"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
|
||||
imagev1 "github.com/fluxcd/image-reflector-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
var createImagePolicyCmd = &cobra.Command{
|
||||
Use: "policy [name]",
|
||||
Short: "Create or update an ImagePolicy object",
|
||||
Long: withPreviewNote(`The create image policy command generates an ImagePolicy resource.
|
||||
An ImagePolicy object calculates a "latest image" given an image
|
||||
repository and a policy, e.g., semver.
|
||||
|
||||
The image that sorts highest according to the policy is recorded in
|
||||
the status of the object.`),
|
||||
Example: ` # Create an ImagePolicy to select the latest stable release
|
||||
flux create image policy podinfo \
|
||||
--image-ref=podinfo \
|
||||
--select-semver=">=1.0.0"
|
||||
|
||||
# Create an ImagePolicy to select the latest main branch build tagged as "${GIT_BRANCH}-${GIT_SHA:0:7}-$(date +%s)"
|
||||
flux create image policy podinfo \
|
||||
--image-ref=podinfo \
|
||||
--select-numeric=asc \
|
||||
--filter-regex='^main-[a-f0-9]+-(?P<ts>[0-9]+)' \
|
||||
--filter-extract='$ts'`,
|
||||
RunE: createImagePolicyRun}
|
||||
|
||||
type imagePolicyFlags struct {
|
||||
imageRef string
|
||||
semver string
|
||||
alpha string
|
||||
numeric string
|
||||
filterRegex string
|
||||
filterExtract string
|
||||
filterNumerical string
|
||||
}
|
||||
|
||||
var imagePolicyArgs = imagePolicyFlags{}
|
||||
|
||||
func init() {
|
||||
flags := createImagePolicyCmd.Flags()
|
||||
flags.StringVar(&imagePolicyArgs.imageRef, "image-ref", "", "the name of an image repository object")
|
||||
flags.StringVar(&imagePolicyArgs.semver, "select-semver", "", "a semver range to apply to tags; e.g., '1.x'")
|
||||
flags.StringVar(&imagePolicyArgs.alpha, "select-alpha", "", "use alphabetical sorting to select image; either \"asc\" meaning select the last, or \"desc\" meaning select the first")
|
||||
flags.StringVar(&imagePolicyArgs.numeric, "select-numeric", "", "use numeric sorting to select image; either \"asc\" meaning select the last, or \"desc\" meaning select the first")
|
||||
flags.StringVar(&imagePolicyArgs.filterRegex, "filter-regex", "", "regular expression pattern used to filter the image tags")
|
||||
flags.StringVar(&imagePolicyArgs.filterExtract, "filter-extract", "", "replacement pattern (using capture groups from --filter-regex) to use for sorting")
|
||||
|
||||
createImageCmd.AddCommand(createImagePolicyCmd)
|
||||
}
|
||||
|
||||
// getObservedGeneration is implemented here, since it's not
|
||||
// (presently) needed elsewhere.
|
||||
func (obj imagePolicyAdapter) getObservedGeneration() int64 {
|
||||
return obj.ImagePolicy.Status.ObservedGeneration
|
||||
}
|
||||
|
||||
func createImagePolicyRun(cmd *cobra.Command, args []string) error {
|
||||
objectName := args[0]
|
||||
|
||||
if imagePolicyArgs.imageRef == "" {
|
||||
return fmt.Errorf("the name of an ImageRepository in the namespace is required (--image-ref)")
|
||||
}
|
||||
|
||||
labels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
var policy = imagev1.ImagePolicy{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: objectName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: labels,
|
||||
},
|
||||
Spec: imagev1.ImagePolicySpec{
|
||||
ImageRepositoryRef: meta.NamespacedObjectReference{
|
||||
Name: imagePolicyArgs.imageRef,
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
switch {
|
||||
case imagePolicyArgs.semver != "" && imagePolicyArgs.alpha != "":
|
||||
case imagePolicyArgs.semver != "" && imagePolicyArgs.numeric != "":
|
||||
case imagePolicyArgs.alpha != "" && imagePolicyArgs.numeric != "":
|
||||
return fmt.Errorf("only one of --select-semver, --select-alpha or --select-numeric can be specified")
|
||||
case imagePolicyArgs.semver != "":
|
||||
policy.Spec.Policy.SemVer = &imagev1.SemVerPolicy{
|
||||
Range: imagePolicyArgs.semver,
|
||||
}
|
||||
case imagePolicyArgs.alpha != "":
|
||||
if imagePolicyArgs.alpha != "desc" && imagePolicyArgs.alpha != "asc" {
|
||||
return fmt.Errorf("--select-alpha must be one of [\"asc\", \"desc\"]")
|
||||
}
|
||||
policy.Spec.Policy.Alphabetical = &imagev1.AlphabeticalPolicy{
|
||||
Order: imagePolicyArgs.alpha,
|
||||
}
|
||||
case imagePolicyArgs.numeric != "":
|
||||
if imagePolicyArgs.numeric != "desc" && imagePolicyArgs.numeric != "asc" {
|
||||
return fmt.Errorf("--select-numeric must be one of [\"asc\", \"desc\"]")
|
||||
}
|
||||
policy.Spec.Policy.Numerical = &imagev1.NumericalPolicy{
|
||||
Order: imagePolicyArgs.numeric,
|
||||
}
|
||||
default:
|
||||
return fmt.Errorf("a policy must be provided with either --select-semver or --select-alpha")
|
||||
}
|
||||
|
||||
if imagePolicyArgs.filterRegex != "" {
|
||||
exp, err := syntax.Parse(imagePolicyArgs.filterRegex, syntax.Perl)
|
||||
if err != nil {
|
||||
return fmt.Errorf("--filter-regex is an invalid regex pattern")
|
||||
}
|
||||
policy.Spec.FilterTags = &imagev1.TagFilter{
|
||||
Pattern: imagePolicyArgs.filterRegex,
|
||||
}
|
||||
|
||||
if imagePolicyArgs.filterExtract != "" {
|
||||
if err := validateExtractStr(imagePolicyArgs.filterExtract, exp.CapNames()); err != nil {
|
||||
return err
|
||||
}
|
||||
policy.Spec.FilterTags.Extract = imagePolicyArgs.filterExtract
|
||||
}
|
||||
} else if imagePolicyArgs.filterExtract != "" {
|
||||
return fmt.Errorf("cannot specify --filter-extract without specifying --filter-regex")
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportImagePolicy(&policy))
|
||||
}
|
||||
|
||||
var existing imagev1.ImagePolicy
|
||||
copyName(&existing, &policy)
|
||||
err = imagePolicyType.upsertAndWait(imagePolicyAdapter{&existing}, func() error {
|
||||
existing.Spec = policy.Spec
|
||||
existing.SetLabels(policy.Labels)
|
||||
return nil
|
||||
})
|
||||
return err
|
||||
}
|
||||
|
||||
// Performs a dry-run of the extract function in Regexp to validate the template
|
||||
func validateExtractStr(template string, capNames []string) error {
|
||||
for len(template) > 0 {
|
||||
i := strings.Index(template, "$")
|
||||
if i < 0 {
|
||||
return nil
|
||||
}
|
||||
template = template[i:]
|
||||
if len(template) > 1 && template[1] == '$' {
|
||||
template = template[2:]
|
||||
continue
|
||||
}
|
||||
name, num, rest, ok := extract(template)
|
||||
if !ok {
|
||||
// Malformed extract string, assume user didn't want this
|
||||
template = template[1:]
|
||||
return fmt.Errorf("--filter-extract is malformed")
|
||||
}
|
||||
template = rest
|
||||
if num >= 0 {
|
||||
// we won't worry about numbers as we can't validate these
|
||||
continue
|
||||
} else {
|
||||
found := false
|
||||
for _, capName := range capNames {
|
||||
if name == capName {
|
||||
found = true
|
||||
}
|
||||
}
|
||||
if !found {
|
||||
return fmt.Errorf("capture group $%s used in --filter-extract not found in --filter-regex", name)
|
||||
}
|
||||
}
|
||||
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
// extract method from the regexp package
|
||||
// returns the name or number of the value prepended by $
|
||||
func extract(str string) (name string, num int, rest string, ok bool) {
|
||||
if len(str) < 2 || str[0] != '$' {
|
||||
return
|
||||
}
|
||||
brace := false
|
||||
if str[1] == '{' {
|
||||
brace = true
|
||||
str = str[2:]
|
||||
} else {
|
||||
str = str[1:]
|
||||
}
|
||||
i := 0
|
||||
for i < len(str) {
|
||||
rune, size := utf8.DecodeRuneInString(str[i:])
|
||||
if !unicode.IsLetter(rune) && !unicode.IsDigit(rune) && rune != '_' {
|
||||
break
|
||||
}
|
||||
i += size
|
||||
}
|
||||
if i == 0 {
|
||||
// empty name is not okay
|
||||
return
|
||||
}
|
||||
name = str[:i]
|
||||
if brace {
|
||||
if i >= len(str) || str[i] != '}' {
|
||||
// missing closing brace
|
||||
return
|
||||
}
|
||||
i++
|
||||
}
|
||||
|
||||
// Parse number.
|
||||
num = 0
|
||||
for i := 0; i < len(name); i++ {
|
||||
if name[i] < '0' || '9' < name[i] || num >= 1e8 {
|
||||
num = -1
|
||||
break
|
||||
}
|
||||
num = num*10 + int(name[i]) - '0'
|
||||
}
|
||||
// Disallow leading zeros.
|
||||
if name[0] == '0' && len(name) > 1 {
|
||||
num = -1
|
||||
}
|
||||
|
||||
rest = str[i:]
|
||||
ok = true
|
||||
return
|
||||
}
|
||||
139
cmd/flux/create_image_repository.go
Normal file
139
cmd/flux/create_image_repository.go
Normal file
@@ -0,0 +1,139 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"time"
|
||||
|
||||
"github.com/google/go-containerregistry/pkg/name"
|
||||
"github.com/spf13/cobra"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
|
||||
imagev1 "github.com/fluxcd/image-reflector-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
var createImageRepositoryCmd = &cobra.Command{
|
||||
Use: "repository [name]",
|
||||
Short: "Create or update an ImageRepository object",
|
||||
Long: withPreviewNote(`The create image repository command generates an ImageRepository resource.
|
||||
An ImageRepository object specifies an image repository to scan.`),
|
||||
Example: ` # Create an ImageRepository object to scan the alpine image repository:
|
||||
flux create image repository alpine-repo --image alpine --interval 20m
|
||||
|
||||
# Create an image repository that uses an image pull secret (assumed to
|
||||
# have been created already):
|
||||
flux create image repository myapp-repo \
|
||||
--secret-ref image-pull \
|
||||
--image ghcr.io/example.com/myapp --interval 5m
|
||||
|
||||
# Create a TLS secret for a local image registry using a self-signed
|
||||
# host certificate, and use it to scan an image. ca.pem is a file
|
||||
# containing the CA certificate used to sign the host certificate.
|
||||
flux create secret tls local-registry-cert --ca-file ./ca.pem
|
||||
flux create image repository app-repo \
|
||||
--cert-secret-ref local-registry-cert \
|
||||
--image local-registry:5000/app --interval 5m
|
||||
|
||||
# Create a TLS secret with a client certificate and key, and use it
|
||||
# to scan a private image registry.
|
||||
flux create secret tls client-cert \
|
||||
--cert-file client.crt --key-file client.key
|
||||
flux create image repository app-repo \
|
||||
--cert-secret-ref client-cert \
|
||||
--image registry.example.com/private/app --interval 5m`,
|
||||
RunE: createImageRepositoryRun,
|
||||
}
|
||||
|
||||
type imageRepoFlags struct {
|
||||
image string
|
||||
secretRef string
|
||||
certSecretRef string
|
||||
timeout time.Duration
|
||||
}
|
||||
|
||||
var imageRepoArgs = imageRepoFlags{}
|
||||
|
||||
func init() {
|
||||
flags := createImageRepositoryCmd.Flags()
|
||||
flags.StringVar(&imageRepoArgs.image, "image", "", "the image repository to scan; e.g., library/alpine")
|
||||
flags.StringVar(&imageRepoArgs.secretRef, "secret-ref", "", "the name of a docker-registry secret to use for credentials")
|
||||
flags.StringVar(&imageRepoArgs.certSecretRef, "cert-ref", "", "the name of a secret to use for TLS certificates")
|
||||
// NB there is already a --timeout in the global flags, for
|
||||
// controlling timeout on operations while e.g., creating objects.
|
||||
flags.DurationVar(&imageRepoArgs.timeout, "scan-timeout", 0, "a timeout for scanning; this defaults to the interval if not set")
|
||||
|
||||
createImageCmd.AddCommand(createImageRepositoryCmd)
|
||||
}
|
||||
|
||||
func createImageRepositoryRun(cmd *cobra.Command, args []string) error {
|
||||
objectName := args[0]
|
||||
|
||||
if imageRepoArgs.image == "" {
|
||||
return fmt.Errorf("an image repository (--image) is required")
|
||||
}
|
||||
|
||||
if _, err := name.NewRepository(imageRepoArgs.image); err != nil {
|
||||
return fmt.Errorf("unable to parse image value: %w", err)
|
||||
}
|
||||
|
||||
labels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
var repo = imagev1.ImageRepository{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: objectName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: labels,
|
||||
},
|
||||
Spec: imagev1.ImageRepositorySpec{
|
||||
Image: imageRepoArgs.image,
|
||||
Interval: metav1.Duration{Duration: createArgs.interval},
|
||||
},
|
||||
}
|
||||
if imageRepoArgs.timeout != 0 {
|
||||
repo.Spec.Timeout = &metav1.Duration{Duration: imageRepoArgs.timeout}
|
||||
}
|
||||
if imageRepoArgs.secretRef != "" {
|
||||
repo.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: imageRepoArgs.secretRef,
|
||||
}
|
||||
}
|
||||
if imageRepoArgs.certSecretRef != "" {
|
||||
repo.Spec.CertSecretRef = &meta.LocalObjectReference{
|
||||
Name: imageRepoArgs.certSecretRef,
|
||||
}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportImageRepository(&repo))
|
||||
}
|
||||
|
||||
// a temp value for use with the rest
|
||||
var existing imagev1.ImageRepository
|
||||
copyName(&existing, &repo)
|
||||
err = imageRepositoryType.upsertAndWait(imageRepositoryAdapter{&existing}, func() error {
|
||||
existing.Spec = repo.Spec
|
||||
existing.Labels = repo.Labels
|
||||
return nil
|
||||
})
|
||||
return err
|
||||
}
|
||||
178
cmd/flux/create_image_update.go
Normal file
178
cmd/flux/create_image_update.go
Normal file
@@ -0,0 +1,178 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
|
||||
autov1 "github.com/fluxcd/image-automation-controller/api/v1beta1"
|
||||
sourcev1 "github.com/fluxcd/source-controller/api/v1"
|
||||
)
|
||||
|
||||
var createImageUpdateCmd = &cobra.Command{
|
||||
Use: "update [name]",
|
||||
Short: "Create or update an ImageUpdateAutomation object",
|
||||
Long: withPreviewNote(`The create image update command generates an ImageUpdateAutomation resource.
|
||||
An ImageUpdateAutomation object specifies an automated update to images
|
||||
mentioned in YAMLs in a git repository.`),
|
||||
Example: ` # Configure image updates for the main repository created by flux bootstrap
|
||||
flux create image update flux-system \
|
||||
--git-repo-ref=flux-system \
|
||||
--git-repo-path="./clusters/my-cluster" \
|
||||
--checkout-branch=main \
|
||||
--author-name=flux \
|
||||
--author-email=flux@example.com \
|
||||
--commit-template="{{range .Updated.Images}}{{println .}}{{end}}"
|
||||
|
||||
# Configure image updates to push changes to a different branch, if the branch doesn't exists it will be created
|
||||
flux create image update flux-system \
|
||||
--git-repo-ref=flux-system \
|
||||
--git-repo-path="./clusters/my-cluster" \
|
||||
--checkout-branch=main \
|
||||
--push-branch=image-updates \
|
||||
--author-name=flux \
|
||||
--author-email=flux@example.com \
|
||||
--commit-template="{{range .Updated.Images}}{{println .}}{{end}}"
|
||||
|
||||
# Configure image updates for a Git repository in a different namespace
|
||||
flux create image update apps \
|
||||
--namespace=apps \
|
||||
--git-repo-ref=flux-system \
|
||||
--git-repo-namespace=flux-system \
|
||||
--git-repo-path="./clusters/my-cluster" \
|
||||
--checkout-branch=main \
|
||||
--push-branch=image-updates \
|
||||
--author-name=flux \
|
||||
--author-email=flux@example.com \
|
||||
--commit-template="{{range .Updated.Images}}{{println .}}{{end}}"
|
||||
`,
|
||||
RunE: createImageUpdateRun,
|
||||
}
|
||||
|
||||
type imageUpdateFlags struct {
|
||||
gitRepoName string
|
||||
gitRepoNamespace string
|
||||
gitRepoPath string
|
||||
checkoutBranch string
|
||||
pushBranch string
|
||||
commitTemplate string
|
||||
authorName string
|
||||
authorEmail string
|
||||
}
|
||||
|
||||
var imageUpdateArgs = imageUpdateFlags{}
|
||||
|
||||
func init() {
|
||||
flags := createImageUpdateCmd.Flags()
|
||||
flags.StringVar(&imageUpdateArgs.gitRepoName, "git-repo-ref", "", "the name of a GitRepository resource with details of the upstream Git repository")
|
||||
flags.StringVar(&imageUpdateArgs.gitRepoNamespace, "git-repo-namespace", "", "the namespace of the GitRepository resource, defaults to the ImageUpdateAutomation namespace")
|
||||
flags.StringVar(&imageUpdateArgs.gitRepoPath, "git-repo-path", "", "path to the directory containing the manifests to be updated, defaults to the repository root")
|
||||
flags.StringVar(&imageUpdateArgs.checkoutBranch, "checkout-branch", "", "the branch to checkout")
|
||||
flags.StringVar(&imageUpdateArgs.pushBranch, "push-branch", "", "the branch to push commits to, defaults to the checkout branch if not specified")
|
||||
flags.StringVar(&imageUpdateArgs.commitTemplate, "commit-template", "", "a template for commit messages")
|
||||
flags.StringVar(&imageUpdateArgs.authorName, "author-name", "", "the name to use for commit author")
|
||||
flags.StringVar(&imageUpdateArgs.authorEmail, "author-email", "", "the email to use for commit author")
|
||||
|
||||
createImageCmd.AddCommand(createImageUpdateCmd)
|
||||
}
|
||||
|
||||
func createImageUpdateRun(cmd *cobra.Command, args []string) error {
|
||||
objectName := args[0]
|
||||
|
||||
if imageUpdateArgs.gitRepoName == "" {
|
||||
return fmt.Errorf("a reference to a GitRepository is required (--git-repo-ref)")
|
||||
}
|
||||
|
||||
if imageUpdateArgs.checkoutBranch == "" {
|
||||
return fmt.Errorf("the Git repository branch is required (--checkout-branch)")
|
||||
}
|
||||
|
||||
if imageUpdateArgs.authorName == "" {
|
||||
return fmt.Errorf("the author name is required (--author-name)")
|
||||
}
|
||||
|
||||
if imageUpdateArgs.authorEmail == "" {
|
||||
return fmt.Errorf("the author email is required (--author-email)")
|
||||
}
|
||||
|
||||
labels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
var update = autov1.ImageUpdateAutomation{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: objectName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: labels,
|
||||
},
|
||||
Spec: autov1.ImageUpdateAutomationSpec{
|
||||
SourceRef: autov1.CrossNamespaceSourceReference{
|
||||
Kind: sourcev1.GitRepositoryKind,
|
||||
Name: imageUpdateArgs.gitRepoName,
|
||||
Namespace: imageUpdateArgs.gitRepoNamespace,
|
||||
},
|
||||
|
||||
GitSpec: &autov1.GitSpec{
|
||||
Checkout: &autov1.GitCheckoutSpec{
|
||||
Reference: sourcev1.GitRepositoryRef{
|
||||
Branch: imageUpdateArgs.checkoutBranch,
|
||||
},
|
||||
},
|
||||
Commit: autov1.CommitSpec{
|
||||
Author: autov1.CommitUser{
|
||||
Name: imageUpdateArgs.authorName,
|
||||
Email: imageUpdateArgs.authorEmail,
|
||||
},
|
||||
MessageTemplate: imageUpdateArgs.commitTemplate,
|
||||
},
|
||||
},
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
if imageUpdateArgs.pushBranch != "" {
|
||||
update.Spec.GitSpec.Push = &autov1.PushSpec{
|
||||
Branch: imageUpdateArgs.pushBranch,
|
||||
}
|
||||
}
|
||||
|
||||
if imageUpdateArgs.gitRepoPath != "" {
|
||||
update.Spec.Update = &autov1.UpdateStrategy{
|
||||
Path: imageUpdateArgs.gitRepoPath,
|
||||
Strategy: autov1.UpdateStrategySetters,
|
||||
}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportImageUpdate(&update))
|
||||
}
|
||||
|
||||
var existing autov1.ImageUpdateAutomation
|
||||
copyName(&existing, &update)
|
||||
err = imageUpdateAutomationType.upsertAndWait(imageUpdateAutomationAdapter{&existing}, func() error {
|
||||
existing.Spec = update.Spec
|
||||
existing.Labels = update.Labels
|
||||
return nil
|
||||
})
|
||||
return err
|
||||
}
|
||||
330
cmd/flux/create_kustomization.go
Normal file
330
cmd/flux/create_kustomization.go
Normal file
@@ -0,0 +1,330 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
apimeta "k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
helmv2 "github.com/fluxcd/helm-controller/api/v2beta1"
|
||||
kustomizev1 "github.com/fluxcd/kustomize-controller/api/v1"
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createKsCmd = &cobra.Command{
|
||||
Use: "kustomization [name]",
|
||||
Aliases: []string{"ks"},
|
||||
Short: "Create or update a Kustomization resource",
|
||||
Long: `The create command generates a Kustomization resource for a given source.`,
|
||||
Example: ` # Create a Kustomization resource from a source at a given path
|
||||
flux create kustomization kyverno \
|
||||
--source=GitRepository/kyverno \
|
||||
--path="./config/release" \
|
||||
--prune=true \
|
||||
--interval=60m \
|
||||
--wait=true \
|
||||
--health-check-timeout=3m
|
||||
|
||||
# Create a Kustomization resource that depends on the previous one
|
||||
flux create kustomization kyverno-policies \
|
||||
--depends-on=kyverno \
|
||||
--source=GitRepository/kyverno-policies \
|
||||
--path="./policies/flux" \
|
||||
--prune=true \
|
||||
--interval=5m
|
||||
|
||||
# Create a Kustomization using a source from a different namespace
|
||||
flux create kustomization podinfo \
|
||||
--namespace=default \
|
||||
--source=GitRepository/podinfo.flux-system \
|
||||
--path="./kustomize" \
|
||||
--prune=true \
|
||||
--interval=5m
|
||||
|
||||
# Create a Kustomization resource that references an OCIRepository
|
||||
flux create kustomization podinfo \
|
||||
--source=OCIRepository/podinfo \
|
||||
--target-namespace=default \
|
||||
--prune=true \
|
||||
--interval=5m
|
||||
|
||||
# Create a Kustomization resource that references a Bucket
|
||||
flux create kustomization secrets \
|
||||
--source=Bucket/secrets \
|
||||
--prune=true \
|
||||
--interval=5m`,
|
||||
RunE: createKsCmdRun,
|
||||
}
|
||||
|
||||
type kustomizationFlags struct {
|
||||
source flags.KustomizationSource
|
||||
path flags.SafeRelativePath
|
||||
prune bool
|
||||
dependsOn []string
|
||||
validation string
|
||||
healthCheck []string
|
||||
healthTimeout time.Duration
|
||||
saName string
|
||||
decryptionProvider flags.DecryptionProvider
|
||||
decryptionSecret string
|
||||
targetNamespace string
|
||||
wait bool
|
||||
kubeConfigSecretRef string
|
||||
retryInterval time.Duration
|
||||
}
|
||||
|
||||
var kustomizationArgs = NewKustomizationFlags()
|
||||
|
||||
func init() {
|
||||
createKsCmd.Flags().Var(&kustomizationArgs.source, "source", kustomizationArgs.source.Description())
|
||||
createKsCmd.Flags().Var(&kustomizationArgs.path, "path", "path to the directory containing a kustomization.yaml file")
|
||||
createKsCmd.Flags().BoolVar(&kustomizationArgs.prune, "prune", false, "enable garbage collection")
|
||||
createKsCmd.Flags().BoolVar(&kustomizationArgs.wait, "wait", false, "enable health checking of all the applied resources")
|
||||
createKsCmd.Flags().StringSliceVar(&kustomizationArgs.healthCheck, "health-check", nil, "workload to be included in the health assessment, in the format '<kind>/<name>.<namespace>'")
|
||||
createKsCmd.Flags().DurationVar(&kustomizationArgs.healthTimeout, "health-check-timeout", 2*time.Minute, "timeout of health checking operations")
|
||||
createKsCmd.Flags().StringVar(&kustomizationArgs.validation, "validation", "", "validate the manifests before applying them on the cluster, can be 'client' or 'server'")
|
||||
createKsCmd.Flags().StringSliceVar(&kustomizationArgs.dependsOn, "depends-on", nil, "Kustomization that must be ready before this Kustomization can be applied, supported formats '<name>' and '<namespace>/<name>', also accepts comma-separated values")
|
||||
createKsCmd.Flags().StringVar(&kustomizationArgs.saName, "service-account", "", "the name of the service account to impersonate when reconciling this Kustomization")
|
||||
createKsCmd.Flags().Var(&kustomizationArgs.decryptionProvider, "decryption-provider", kustomizationArgs.decryptionProvider.Description())
|
||||
createKsCmd.Flags().StringVar(&kustomizationArgs.decryptionSecret, "decryption-secret", "", "set the Kubernetes secret name that contains the OpenPGP private keys used for sops decryption")
|
||||
createKsCmd.Flags().StringVar(&kustomizationArgs.targetNamespace, "target-namespace", "", "overrides the namespace of all Kustomization objects reconciled by this Kustomization")
|
||||
createKsCmd.Flags().StringVar(&kustomizationArgs.kubeConfigSecretRef, "kubeconfig-secret-ref", "", "the name of the Kubernetes Secret that contains a key with the kubeconfig file for connecting to a remote cluster")
|
||||
createKsCmd.Flags().MarkDeprecated("validation", "this arg is no longer used, all resources are validated using server-side apply dry-run")
|
||||
createKsCmd.Flags().DurationVar(&kustomizationArgs.retryInterval, "retry-interval", 0, "the interval at which to retry a previously failed reconciliation")
|
||||
|
||||
createCmd.AddCommand(createKsCmd)
|
||||
}
|
||||
|
||||
func NewKustomizationFlags() kustomizationFlags {
|
||||
return kustomizationFlags{
|
||||
path: "./",
|
||||
}
|
||||
}
|
||||
|
||||
func createKsCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if kustomizationArgs.path == "" {
|
||||
return fmt.Errorf("path is required")
|
||||
}
|
||||
if !strings.HasPrefix(kustomizationArgs.path.String(), "./") {
|
||||
return fmt.Errorf("path must begin with ./")
|
||||
}
|
||||
|
||||
if !createArgs.export {
|
||||
logger.Generatef("generating Kustomization")
|
||||
}
|
||||
|
||||
kslabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
kustomization := kustomizev1.Kustomization{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: kslabels,
|
||||
},
|
||||
Spec: kustomizev1.KustomizationSpec{
|
||||
DependsOn: utils.MakeDependsOn(kustomizationArgs.dependsOn),
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
Path: kustomizationArgs.path.ToSlash(),
|
||||
Prune: kustomizationArgs.prune,
|
||||
SourceRef: kustomizev1.CrossNamespaceSourceReference{
|
||||
Kind: kustomizationArgs.source.Kind,
|
||||
Name: kustomizationArgs.source.Name,
|
||||
Namespace: kustomizationArgs.source.Namespace,
|
||||
},
|
||||
Suspend: false,
|
||||
TargetNamespace: kustomizationArgs.targetNamespace,
|
||||
},
|
||||
}
|
||||
|
||||
if kustomizationArgs.kubeConfigSecretRef != "" {
|
||||
kustomization.Spec.KubeConfig = &meta.KubeConfigReference{
|
||||
SecretRef: meta.SecretKeyReference{
|
||||
Name: kustomizationArgs.kubeConfigSecretRef,
|
||||
},
|
||||
}
|
||||
}
|
||||
|
||||
if len(kustomizationArgs.healthCheck) > 0 && !kustomizationArgs.wait {
|
||||
healthChecks := make([]meta.NamespacedObjectKindReference, 0)
|
||||
for _, w := range kustomizationArgs.healthCheck {
|
||||
kindObj := strings.Split(w, "/")
|
||||
if len(kindObj) != 2 {
|
||||
return fmt.Errorf("invalid health check '%s' must be in the format 'kind/name.namespace' %v", w, kindObj)
|
||||
}
|
||||
kind := kindObj[0]
|
||||
|
||||
//TODO: (stefan) extend this list with all the kstatus builtin kinds
|
||||
kinds := map[string]bool{
|
||||
"Deployment": true,
|
||||
"DaemonSet": true,
|
||||
"StatefulSet": true,
|
||||
helmv2.HelmReleaseKind: true,
|
||||
}
|
||||
if !kinds[kind] {
|
||||
return fmt.Errorf("invalid health check kind '%s' can be HelmRelease, Deployment, DaemonSet or StatefulSet", kind)
|
||||
}
|
||||
nameNs := strings.Split(kindObj[1], ".")
|
||||
if len(nameNs) != 2 {
|
||||
return fmt.Errorf("invalid health check '%s' must be in the format 'kind/name.namespace'", w)
|
||||
}
|
||||
|
||||
check := meta.NamespacedObjectKindReference{
|
||||
Kind: kind,
|
||||
Name: nameNs[0],
|
||||
Namespace: nameNs[1],
|
||||
}
|
||||
|
||||
if kind == helmv2.HelmReleaseKind {
|
||||
check.APIVersion = helmv2.GroupVersion.String()
|
||||
}
|
||||
healthChecks = append(healthChecks, check)
|
||||
}
|
||||
kustomization.Spec.HealthChecks = healthChecks
|
||||
kustomization.Spec.Timeout = &metav1.Duration{
|
||||
Duration: kustomizationArgs.healthTimeout,
|
||||
}
|
||||
}
|
||||
|
||||
if kustomizationArgs.wait {
|
||||
kustomization.Spec.Wait = true
|
||||
kustomization.Spec.Timeout = &metav1.Duration{
|
||||
Duration: kustomizationArgs.healthTimeout,
|
||||
}
|
||||
}
|
||||
|
||||
if kustomizationArgs.saName != "" {
|
||||
kustomization.Spec.ServiceAccountName = kustomizationArgs.saName
|
||||
}
|
||||
|
||||
if kustomizationArgs.decryptionProvider != "" {
|
||||
kustomization.Spec.Decryption = &kustomizev1.Decryption{
|
||||
Provider: kustomizationArgs.decryptionProvider.String(),
|
||||
}
|
||||
|
||||
if kustomizationArgs.decryptionSecret != "" {
|
||||
kustomization.Spec.Decryption.SecretRef = &meta.LocalObjectReference{Name: kustomizationArgs.decryptionSecret}
|
||||
}
|
||||
}
|
||||
|
||||
if kustomizationArgs.retryInterval > 0 {
|
||||
kustomization.Spec.RetryInterval = &metav1.Duration{Duration: kustomizationArgs.retryInterval}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportKs(&kustomization))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying Kustomization")
|
||||
namespacedName, err := upsertKustomization(ctx, kubeClient, &kustomization)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for Kustomization reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isKustomizationReady(ctx, kubeClient, namespacedName, &kustomization)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("Kustomization %s is ready", name)
|
||||
|
||||
logger.Successf("applied revision %s", kustomization.Status.LastAppliedRevision)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertKustomization(ctx context.Context, kubeClient client.Client,
|
||||
kustomization *kustomizev1.Kustomization) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: kustomization.GetNamespace(),
|
||||
Name: kustomization.GetName(),
|
||||
}
|
||||
|
||||
var existing kustomizev1.Kustomization
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, kustomization); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("Kustomization created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = kustomization.Labels
|
||||
existing.Spec = kustomization.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
kustomization = &existing
|
||||
logger.Successf("Kustomization updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isKustomizationReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, kustomization *kustomizev1.Kustomization) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, kustomization)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
// Confirm the state we are observing is for the current generation
|
||||
if kustomization.Generation != kustomization.Status.ObservedGeneration {
|
||||
return false, nil
|
||||
}
|
||||
|
||||
if c := apimeta.FindStatusCondition(kustomization.Status.Conditions, meta.ReadyCondition); c != nil {
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
201
cmd/flux/create_receiver.go
Normal file
201
cmd/flux/create_receiver.go
Normal file
@@ -0,0 +1,201 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
apimeta "k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1"
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createReceiverCmd = &cobra.Command{
|
||||
Use: "receiver [name]",
|
||||
Short: "Create or update a Receiver resource",
|
||||
Long: `The create receiver command generates a Receiver resource.`,
|
||||
Example: ` # Create a Receiver
|
||||
flux create receiver github-receiver \
|
||||
--type github \
|
||||
--event ping \
|
||||
--event push \
|
||||
--secret-ref webhook-token \
|
||||
--resource GitRepository/webapp \
|
||||
--resource HelmRepository/webapp`,
|
||||
RunE: createReceiverCmdRun,
|
||||
}
|
||||
|
||||
type receiverFlags struct {
|
||||
receiverType string
|
||||
secretRef string
|
||||
events []string
|
||||
resources []string
|
||||
}
|
||||
|
||||
var receiverArgs receiverFlags
|
||||
|
||||
func init() {
|
||||
createReceiverCmd.Flags().StringVar(&receiverArgs.receiverType, "type", "", "")
|
||||
createReceiverCmd.Flags().StringVar(&receiverArgs.secretRef, "secret-ref", "", "")
|
||||
createReceiverCmd.Flags().StringSliceVar(&receiverArgs.events, "event", []string{}, "also accepts comma-separated values")
|
||||
createReceiverCmd.Flags().StringSliceVar(&receiverArgs.resources, "resource", []string{}, "also accepts comma-separated values")
|
||||
createCmd.AddCommand(createReceiverCmd)
|
||||
}
|
||||
|
||||
func createReceiverCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if receiverArgs.receiverType == "" {
|
||||
return fmt.Errorf("Receiver type is required")
|
||||
}
|
||||
|
||||
if receiverArgs.secretRef == "" {
|
||||
return fmt.Errorf("secret ref is required")
|
||||
}
|
||||
|
||||
resources := []notificationv1.CrossNamespaceObjectReference{}
|
||||
for _, resource := range receiverArgs.resources {
|
||||
kind, name := utils.ParseObjectKindName(resource)
|
||||
if kind == "" {
|
||||
return fmt.Errorf("invalid event source '%s', must be in format <kind>/<name>", resource)
|
||||
}
|
||||
|
||||
resources = append(resources, notificationv1.CrossNamespaceObjectReference{
|
||||
Kind: kind,
|
||||
Name: name,
|
||||
})
|
||||
}
|
||||
|
||||
if len(resources) == 0 {
|
||||
return fmt.Errorf("atleast one resource is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if !createArgs.export {
|
||||
logger.Generatef("generating Receiver")
|
||||
}
|
||||
|
||||
receiver := notificationv1.Receiver{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: notificationv1.ReceiverSpec{
|
||||
Type: receiverArgs.receiverType,
|
||||
Events: receiverArgs.events,
|
||||
Resources: resources,
|
||||
SecretRef: meta.LocalObjectReference{
|
||||
Name: receiverArgs.secretRef,
|
||||
},
|
||||
Suspend: false,
|
||||
},
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportReceiver(&receiver))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying Receiver")
|
||||
namespacedName, err := upsertReceiver(ctx, kubeClient, &receiver)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for Receiver reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isReceiverReady(ctx, kubeClient, namespacedName, &receiver)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("Receiver %s is ready", name)
|
||||
|
||||
logger.Successf("generated webhook URL %s", receiver.Status.WebhookPath)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertReceiver(ctx context.Context, kubeClient client.Client,
|
||||
receiver *notificationv1.Receiver) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: receiver.GetNamespace(),
|
||||
Name: receiver.GetName(),
|
||||
}
|
||||
|
||||
var existing notificationv1.Receiver
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, receiver); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("Receiver created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = receiver.Labels
|
||||
existing.Spec = receiver.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
receiver = &existing
|
||||
logger.Successf("Receiver updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isReceiverReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, receiver *notificationv1.Receiver) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, receiver)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := apimeta.FindStatusCondition(receiver.Status.Conditions, meta.ReadyCondition); c != nil {
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
63
cmd/flux/create_secret.go
Normal file
63
cmd/flux/create_secret.go
Normal file
@@ -0,0 +1,63 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
)
|
||||
|
||||
var createSecretCmd = &cobra.Command{
|
||||
Use: "secret",
|
||||
Short: "Create or update Kubernetes secrets",
|
||||
Long: `The create source sub-commands generate Kubernetes secrets specific to Flux.`,
|
||||
}
|
||||
|
||||
func init() {
|
||||
createCmd.AddCommand(createSecretCmd)
|
||||
}
|
||||
|
||||
func upsertSecret(ctx context.Context, kubeClient client.Client, secret corev1.Secret) error {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: secret.GetNamespace(),
|
||||
Name: secret.GetName(),
|
||||
}
|
||||
|
||||
var existing corev1.Secret
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, &secret); err != nil {
|
||||
return err
|
||||
} else {
|
||||
return nil
|
||||
}
|
||||
}
|
||||
return err
|
||||
}
|
||||
|
||||
existing.StringData = secret.StringData
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return err
|
||||
}
|
||||
return nil
|
||||
}
|
||||
205
cmd/flux/create_secret_git.go
Normal file
205
cmd/flux/create_secret_git.go
Normal file
@@ -0,0 +1,205 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"crypto/elliptic"
|
||||
"fmt"
|
||||
"net/url"
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"sigs.k8s.io/yaml"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
)
|
||||
|
||||
var createSecretGitCmd = &cobra.Command{
|
||||
Use: "git [name]",
|
||||
Short: "Create or update a Kubernetes secret for Git authentication",
|
||||
Long: `The create secret git command generates a Kubernetes secret with Git credentials.
|
||||
For Git over SSH, the host and SSH keys are automatically generated and stored
|
||||
in the secret.
|
||||
For Git over HTTP/S, the provided basic authentication credentials or bearer
|
||||
authentication token are stored in the secret.`,
|
||||
Example: ` # Create a Git SSH authentication secret using an ECDSA P-521 curve public key
|
||||
|
||||
flux create secret git podinfo-auth \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--ssh-key-algorithm=ecdsa \
|
||||
--ssh-ecdsa-curve=p521
|
||||
|
||||
# Create a Git SSH authentication secret with a passwordless private key from file
|
||||
# The public SSH host key will still be gathered from the host
|
||||
flux create secret git podinfo-auth \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--private-key-file=./private.key
|
||||
|
||||
# Create a Git SSH authentication secret with a passworded private key from file
|
||||
# The public SSH host key will still be gathered from the host
|
||||
flux create secret git podinfo-auth \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--private-key-file=./private.key \
|
||||
--password=<password>
|
||||
|
||||
# Create a secret for a Git repository using basic authentication
|
||||
flux create secret git podinfo-auth \
|
||||
--url=https://github.com/stefanprodan/podinfo \
|
||||
--username=username \
|
||||
--password=password
|
||||
|
||||
# Create a Git SSH secret on disk
|
||||
flux create secret git podinfo-auth \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--export > podinfo-auth.yaml
|
||||
|
||||
# Print the deploy key
|
||||
yq eval '.stringData."identity.pub"' podinfo-auth.yaml
|
||||
|
||||
# Encrypt the secret on disk with Mozilla SOPS
|
||||
sops --encrypt --encrypted-regex '^(data|stringData)$' \
|
||||
--in-place podinfo-auth.yaml`,
|
||||
RunE: createSecretGitCmdRun,
|
||||
}
|
||||
|
||||
type secretGitFlags struct {
|
||||
url string
|
||||
username string
|
||||
password string
|
||||
keyAlgorithm flags.PublicKeyAlgorithm
|
||||
rsaBits flags.RSAKeyBits
|
||||
ecdsaCurve flags.ECDSACurve
|
||||
caFile string
|
||||
privateKeyFile string
|
||||
bearerToken string
|
||||
}
|
||||
|
||||
var secretGitArgs = NewSecretGitFlags()
|
||||
|
||||
func init() {
|
||||
createSecretGitCmd.Flags().StringVar(&secretGitArgs.url, "url", "", "git address, e.g. ssh://git@host/org/repository")
|
||||
createSecretGitCmd.Flags().StringVarP(&secretGitArgs.username, "username", "u", "", "basic authentication username")
|
||||
createSecretGitCmd.Flags().StringVarP(&secretGitArgs.password, "password", "p", "", "basic authentication password")
|
||||
createSecretGitCmd.Flags().Var(&secretGitArgs.keyAlgorithm, "ssh-key-algorithm", secretGitArgs.keyAlgorithm.Description())
|
||||
createSecretGitCmd.Flags().Var(&secretGitArgs.rsaBits, "ssh-rsa-bits", secretGitArgs.rsaBits.Description())
|
||||
createSecretGitCmd.Flags().Var(&secretGitArgs.ecdsaCurve, "ssh-ecdsa-curve", secretGitArgs.ecdsaCurve.Description())
|
||||
createSecretGitCmd.Flags().StringVar(&secretGitArgs.caFile, "ca-file", "", "path to TLS CA file used for validating self-signed certificates")
|
||||
createSecretGitCmd.Flags().StringVar(&secretGitArgs.privateKeyFile, "private-key-file", "", "path to a passwordless private key file used for authenticating to the Git SSH server")
|
||||
createSecretGitCmd.Flags().StringVar(&secretGitArgs.bearerToken, "bearer-token", "", "bearer authentication token")
|
||||
|
||||
createSecretCmd.AddCommand(createSecretGitCmd)
|
||||
}
|
||||
|
||||
func NewSecretGitFlags() secretGitFlags {
|
||||
return secretGitFlags{
|
||||
keyAlgorithm: flags.PublicKeyAlgorithm(sourcesecret.ECDSAPrivateKeyAlgorithm),
|
||||
rsaBits: 2048,
|
||||
ecdsaCurve: flags.ECDSACurve{Curve: elliptic.P384()},
|
||||
}
|
||||
}
|
||||
|
||||
func createSecretGitCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
if secretGitArgs.url == "" {
|
||||
return fmt.Errorf("url is required")
|
||||
}
|
||||
|
||||
u, err := url.Parse(secretGitArgs.url)
|
||||
if err != nil {
|
||||
return fmt.Errorf("git URL parse failed: %w", err)
|
||||
}
|
||||
|
||||
labels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
opts := sourcesecret.Options{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: labels,
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
switch u.Scheme {
|
||||
case "ssh":
|
||||
keypair, err := sourcesecret.LoadKeyPairFromPath(secretGitArgs.privateKeyFile, secretGitArgs.password)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
opts.Keypair = keypair
|
||||
opts.SSHHostname = u.Host
|
||||
opts.PrivateKeyAlgorithm = sourcesecret.PrivateKeyAlgorithm(secretGitArgs.keyAlgorithm)
|
||||
opts.RSAKeyBits = int(secretGitArgs.rsaBits)
|
||||
opts.ECDSACurve = secretGitArgs.ecdsaCurve.Curve
|
||||
opts.Password = secretGitArgs.password
|
||||
case "http", "https":
|
||||
if (secretGitArgs.username == "" || secretGitArgs.password == "") && secretGitArgs.bearerToken == "" {
|
||||
return fmt.Errorf("for Git over HTTP/S the username and password, or a bearer token is required")
|
||||
}
|
||||
opts.Username = secretGitArgs.username
|
||||
opts.Password = secretGitArgs.password
|
||||
opts.BearerToken = secretGitArgs.bearerToken
|
||||
if secretGitArgs.username != "" && secretGitArgs.password != "" && secretGitArgs.bearerToken != "" {
|
||||
return fmt.Errorf("user credentials and bearer token cannot be used together")
|
||||
}
|
||||
if secretGitArgs.caFile != "" {
|
||||
caBundle, err := os.ReadFile(secretGitArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
opts.CAFile = caBundle
|
||||
}
|
||||
default:
|
||||
return fmt.Errorf("git URL scheme '%s' not supported, can be: ssh, http and https", u.Scheme)
|
||||
}
|
||||
|
||||
secret, err := sourcesecret.Generate(opts)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
rootCmd.Println(secret.Content)
|
||||
return nil
|
||||
}
|
||||
|
||||
var s corev1.Secret
|
||||
if err := yaml.Unmarshal([]byte(secret.Content), &s); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if ppk, ok := s.StringData[sourcesecret.PublicKeySecretKey]; ok {
|
||||
logger.Generatef("deploy key: %s", ppk)
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
if err := upsertSecret(ctx, kubeClient, s); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Actionf("git secret '%s' created in '%s' namespace", name, *kubeconfigArgs.Namespace)
|
||||
|
||||
return nil
|
||||
}
|
||||
54
cmd/flux/create_secret_git_test.go
Normal file
54
cmd/flux/create_secret_git_test.go
Normal file
@@ -0,0 +1,54 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestCreateGitSecret(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
assert assertFunc
|
||||
}{
|
||||
{
|
||||
name: "no args",
|
||||
args: "create secret git",
|
||||
assert: assertError("name is required"),
|
||||
},
|
||||
{
|
||||
name: "basic secret",
|
||||
args: "create secret git podinfo-auth --url=https://github.com/stefanprodan/podinfo --username=my-username --password=my-password --namespace=my-namespace --export",
|
||||
assert: assertGoldenFile("./testdata/create_secret/git/secret-git-basic.yaml"),
|
||||
},
|
||||
{
|
||||
name: "ssh key",
|
||||
args: "create secret git podinfo-auth --url=ssh://git@github.com/stefanprodan/podinfo --private-key-file=./testdata/create_secret/git/ecdsa.private --namespace=my-namespace --export",
|
||||
assert: assertGoldenFile("testdata/create_secret/git/git-ssh-secret.yaml"),
|
||||
},
|
||||
{
|
||||
name: "ssh key with password",
|
||||
args: "create secret git podinfo-auth --url=ssh://git@github.com/stefanprodan/podinfo --private-key-file=./testdata/create_secret/git/ecdsa-password.private --password=password --namespace=my-namespace --export",
|
||||
assert: assertGoldenFile("testdata/create_secret/git/git-ssh-secret-password.yaml"),
|
||||
},
|
||||
{
|
||||
name: "git authentication with bearer token",
|
||||
args: "create secret git bearer-token-auth --url=https://github.com/stefanprodan/podinfo --bearer-token=ghp_baR2qnFF0O41WlucePL3udt2N9vVZS4R0hAS --namespace=my-namespace --export",
|
||||
assert: assertGoldenFile("testdata/create_secret/git/git-bearer-token.yaml"),
|
||||
},
|
||||
{
|
||||
name: "git authentication with basic auth and bearer token",
|
||||
args: "create secret git podinfo-auth --url=https://github.com/stefanprodan/podinfo --username=aaa --password=zzzz --bearer-token=aaaa --namespace=my-namespace --export",
|
||||
assert: assertError("user credentials and bearer token cannot be used together"),
|
||||
},
|
||||
}
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args,
|
||||
assert: tt.assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
134
cmd/flux/create_secret_helm.go
Normal file
134
cmd/flux/create_secret_helm.go
Normal file
@@ -0,0 +1,134 @@
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"sigs.k8s.io/yaml"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
)
|
||||
|
||||
var createSecretHelmCmd = &cobra.Command{
|
||||
Use: "helm [name]",
|
||||
Short: "Create or update a Kubernetes secret for Helm repository authentication",
|
||||
Long: withPreviewNote(`The create secret helm command generates a Kubernetes secret with basic authentication credentials.`),
|
||||
Example: ` # Create a Helm authentication secret on disk and encrypt it with Mozilla SOPS
|
||||
flux create secret helm repo-auth \
|
||||
--namespace=my-namespace \
|
||||
--username=my-username \
|
||||
--password=my-password \
|
||||
--export > repo-auth.yaml
|
||||
|
||||
sops --encrypt --encrypted-regex '^(data|stringData)$' \
|
||||
--in-place repo-auth.yaml
|
||||
|
||||
# Create a Helm authentication secret using a custom TLS cert
|
||||
flux create secret helm repo-auth \
|
||||
--username=username \
|
||||
--password=password \
|
||||
--cert-file=./cert.crt \
|
||||
--key-file=./key.crt \
|
||||
--ca-file=./ca.crt`,
|
||||
RunE: createSecretHelmCmdRun,
|
||||
}
|
||||
|
||||
type secretHelmFlags struct {
|
||||
username string
|
||||
password string
|
||||
secretTLSFlags
|
||||
}
|
||||
|
||||
var secretHelmArgs secretHelmFlags
|
||||
|
||||
func init() {
|
||||
createSecretHelmCmd.Flags().StringVarP(&secretHelmArgs.username, "username", "u", "", "basic authentication username")
|
||||
createSecretHelmCmd.Flags().StringVarP(&secretHelmArgs.password, "password", "p", "", "basic authentication password")
|
||||
initSecretTLSFlags(createSecretHelmCmd.Flags(), &secretHelmArgs.secretTLSFlags)
|
||||
createSecretCmd.AddCommand(createSecretHelmCmd)
|
||||
}
|
||||
|
||||
func createSecretHelmCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
labels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
caBundle := []byte{}
|
||||
if secretHelmArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(secretHelmArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
var certFile, keyFile []byte
|
||||
if secretHelmArgs.certFile != "" && secretHelmArgs.keyFile != "" {
|
||||
if certFile, err = os.ReadFile(secretHelmArgs.certFile); err != nil {
|
||||
return fmt.Errorf("failed to read cert file: %w", err)
|
||||
}
|
||||
if keyFile, err = os.ReadFile(secretHelmArgs.keyFile); err != nil {
|
||||
return fmt.Errorf("failed to read key file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
opts := sourcesecret.Options{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: labels,
|
||||
Username: secretHelmArgs.username,
|
||||
Password: secretHelmArgs.password,
|
||||
CAFile: caBundle,
|
||||
CertFile: certFile,
|
||||
KeyFile: keyFile,
|
||||
}
|
||||
secret, err := sourcesecret.Generate(opts)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
rootCmd.Println(secret.Content)
|
||||
return nil
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
var s corev1.Secret
|
||||
if err := yaml.Unmarshal([]byte(secret.Content), &s); err != nil {
|
||||
return err
|
||||
}
|
||||
if err := upsertSecret(ctx, kubeClient, s); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("helm secret '%s' created in '%s' namespace", name, *kubeconfigArgs.Namespace)
|
||||
return nil
|
||||
}
|
||||
47
cmd/flux/create_secret_helm_test.go
Normal file
47
cmd/flux/create_secret_helm_test.go
Normal file
@@ -0,0 +1,47 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestCreateHelmSecret(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
assert assertFunc
|
||||
}{
|
||||
{
|
||||
args: "create secret helm",
|
||||
assert: assertError("name is required"),
|
||||
},
|
||||
{
|
||||
args: "create secret helm helm-secret --username=my-username --password=my-password --namespace=my-namespace --export",
|
||||
assert: assertGoldenFile("testdata/create_secret/helm/secret-helm.yaml"),
|
||||
},
|
||||
}
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args,
|
||||
assert: tt.assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
121
cmd/flux/create_secret_oci.go
Normal file
121
cmd/flux/create_secret_oci.go
Normal file
@@ -0,0 +1,121 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
"github.com/google/go-containerregistry/pkg/name"
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"sigs.k8s.io/yaml"
|
||||
)
|
||||
|
||||
var createSecretOCICmd = &cobra.Command{
|
||||
Use: "oci [name]",
|
||||
Short: "Create or update a Kubernetes image pull secret",
|
||||
Long: withPreviewNote(`The create secret oci command generates a Kubernetes secret that can be used for OCIRepository authentication`),
|
||||
Example: ` # Create an OCI authentication secret on disk and encrypt it with Mozilla SOPS
|
||||
flux create secret oci podinfo-auth \
|
||||
--url=ghcr.io \
|
||||
--username=username \
|
||||
--password=password \
|
||||
--export > repo-auth.yaml
|
||||
|
||||
sops --encrypt --encrypted-regex '^(data|stringData)$' \
|
||||
--in-place repo-auth.yaml
|
||||
`,
|
||||
RunE: createSecretOCICmdRun,
|
||||
}
|
||||
|
||||
type secretOCIFlags struct {
|
||||
url string
|
||||
password string
|
||||
username string
|
||||
}
|
||||
|
||||
var secretOCIArgs = secretOCIFlags{}
|
||||
|
||||
func init() {
|
||||
createSecretOCICmd.Flags().StringVar(&secretOCIArgs.url, "url", "", "oci repository address e.g ghcr.io/stefanprodan/charts")
|
||||
createSecretOCICmd.Flags().StringVarP(&secretOCIArgs.username, "username", "u", "", "basic authentication username")
|
||||
createSecretOCICmd.Flags().StringVarP(&secretOCIArgs.password, "password", "p", "", "basic authentication password")
|
||||
|
||||
createSecretCmd.AddCommand(createSecretOCICmd)
|
||||
}
|
||||
|
||||
func createSecretOCICmdRun(cmd *cobra.Command, args []string) error {
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("name is required")
|
||||
}
|
||||
|
||||
secretName := args[0]
|
||||
|
||||
if secretOCIArgs.url == "" {
|
||||
return fmt.Errorf("--url is required")
|
||||
}
|
||||
|
||||
if secretOCIArgs.username == "" {
|
||||
return fmt.Errorf("--username is required")
|
||||
}
|
||||
|
||||
if secretOCIArgs.password == "" {
|
||||
return fmt.Errorf("--password is required")
|
||||
}
|
||||
|
||||
if _, err := name.ParseReference(secretOCIArgs.url); err != nil {
|
||||
return fmt.Errorf("error parsing url: '%s'", err)
|
||||
}
|
||||
|
||||
opts := sourcesecret.Options{
|
||||
Name: secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Registry: secretOCIArgs.url,
|
||||
Password: secretOCIArgs.password,
|
||||
Username: secretOCIArgs.username,
|
||||
}
|
||||
|
||||
secret, err := sourcesecret.Generate(opts)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
rootCmd.Println(secret.Content)
|
||||
return nil
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
var s corev1.Secret
|
||||
if err := yaml.Unmarshal([]byte(secret.Content), &s); err != nil {
|
||||
return err
|
||||
}
|
||||
if err := upsertSecret(ctx, kubeClient, s); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("oci secret '%s' created in '%s' namespace", secretName, *kubeconfigArgs.Namespace)
|
||||
return nil
|
||||
}
|
||||
51
cmd/flux/create_secret_oci_test.go
Normal file
51
cmd/flux/create_secret_oci_test.go
Normal file
@@ -0,0 +1,51 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestCreateSecretOCI(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
assert assertFunc
|
||||
}{
|
||||
{
|
||||
args: "create secret oci",
|
||||
assert: assertError("name is required"),
|
||||
},
|
||||
{
|
||||
args: "create secret oci ghcr",
|
||||
assert: assertError("--url is required"),
|
||||
},
|
||||
{
|
||||
args: "create secret oci ghcr --namespace=my-namespace --url ghcr.io --username stefanprodan --password=password --export",
|
||||
assert: assertGoldenFile("testdata/create_secret/oci/create-secret.yaml"),
|
||||
},
|
||||
}
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args,
|
||||
assert: tt.assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
131
cmd/flux/create_secret_tls.go
Normal file
131
cmd/flux/create_secret_tls.go
Normal file
@@ -0,0 +1,131 @@
|
||||
/*
|
||||
Copyright 2020, 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"os"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"github.com/spf13/pflag"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"sigs.k8s.io/yaml"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
)
|
||||
|
||||
var createSecretTLSCmd = &cobra.Command{
|
||||
Use: "tls [name]",
|
||||
Short: "Create or update a Kubernetes secret with TLS certificates",
|
||||
Long: withPreviewNote(`The create secret tls command generates a Kubernetes secret with certificates for use with TLS.`),
|
||||
Example: ` # Create a TLS secret on disk and encrypt it with Mozilla SOPS.
|
||||
# Files are expected to be PEM-encoded.
|
||||
flux create secret tls certs \
|
||||
--namespace=my-namespace \
|
||||
--cert-file=./client.crt \
|
||||
--key-file=./client.key \
|
||||
--export > certs.yaml
|
||||
|
||||
sops --encrypt --encrypted-regex '^(data|stringData)$' \
|
||||
--in-place certs.yaml`,
|
||||
RunE: createSecretTLSCmdRun,
|
||||
}
|
||||
|
||||
type secretTLSFlags struct {
|
||||
certFile string
|
||||
keyFile string
|
||||
caFile string
|
||||
}
|
||||
|
||||
var secretTLSArgs secretTLSFlags
|
||||
|
||||
func initSecretTLSFlags(flags *pflag.FlagSet, args *secretTLSFlags) {
|
||||
flags.StringVar(&args.certFile, "cert-file", "", "TLS authentication cert file path")
|
||||
flags.StringVar(&args.keyFile, "key-file", "", "TLS authentication key file path")
|
||||
flags.StringVar(&args.caFile, "ca-file", "", "TLS authentication CA file path")
|
||||
}
|
||||
|
||||
func init() {
|
||||
flags := createSecretTLSCmd.Flags()
|
||||
initSecretTLSFlags(flags, &secretTLSArgs)
|
||||
createSecretCmd.AddCommand(createSecretTLSCmd)
|
||||
}
|
||||
|
||||
func createSecretTLSCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
labels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
caBundle := []byte{}
|
||||
if secretTLSArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(secretTLSArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
var certFile, keyFile []byte
|
||||
if secretTLSArgs.certFile != "" && secretTLSArgs.keyFile != "" {
|
||||
if certFile, err = os.ReadFile(secretTLSArgs.certFile); err != nil {
|
||||
return fmt.Errorf("failed to read cert file: %w", err)
|
||||
}
|
||||
if keyFile, err = os.ReadFile(secretTLSArgs.keyFile); err != nil {
|
||||
return fmt.Errorf("failed to read key file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
opts := sourcesecret.Options{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: labels,
|
||||
CAFile: caBundle,
|
||||
CertFile: certFile,
|
||||
KeyFile: keyFile,
|
||||
}
|
||||
secret, err := sourcesecret.Generate(opts)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
rootCmd.Print(secret.Content)
|
||||
return nil
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
var s corev1.Secret
|
||||
if err := yaml.Unmarshal([]byte(secret.Content), &s); err != nil {
|
||||
return err
|
||||
}
|
||||
if err := upsertSecret(ctx, kubeClient, s); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("tls secret '%s' created in '%s' namespace", name, *kubeconfigArgs.Namespace)
|
||||
return nil
|
||||
}
|
||||
31
cmd/flux/create_secret_tls_test.go
Normal file
31
cmd/flux/create_secret_tls_test.go
Normal file
@@ -0,0 +1,31 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestCreateTlsSecretNoArgs(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
assert assertFunc
|
||||
}{
|
||||
{
|
||||
args: "create secret tls",
|
||||
assert: assertError("name is required"),
|
||||
},
|
||||
{
|
||||
args: "create secret tls certs --namespace=my-namespace --cert-file=./testdata/create_secret/tls/test-cert.pem --key-file=./testdata/create_secret/tls/test-key.pem --export",
|
||||
assert: assertGoldenFile("testdata/create_secret/tls/secret-tls.yaml"),
|
||||
},
|
||||
}
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args,
|
||||
assert: tt.assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
41
cmd/flux/create_source.go
Normal file
41
cmd/flux/create_source.go
Normal file
@@ -0,0 +1,41 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"time"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var createSourceCmd = &cobra.Command{
|
||||
Use: "source",
|
||||
Short: "Create or update sources",
|
||||
Long: `The create source sub-commands generate sources.`,
|
||||
}
|
||||
|
||||
type createSourceFlags struct {
|
||||
fetchTimeout time.Duration
|
||||
}
|
||||
|
||||
var createSourceArgs createSourceFlags
|
||||
|
||||
func init() {
|
||||
createSourceCmd.PersistentFlags().DurationVar(&createSourceArgs.fetchTimeout, "fetch-timeout", createSourceArgs.fetchTimeout,
|
||||
"set a timeout for fetch operations performed by source-controller (e.g. 'git clone' or 'helm repo update')")
|
||||
createCmd.AddCommand(createSourceCmd)
|
||||
}
|
||||
276
cmd/flux/create_source_bucket.go
Normal file
276
cmd/flux/create_source_bucket.go
Normal file
@@ -0,0 +1,276 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"os"
|
||||
"strings"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
"github.com/fluxcd/pkg/runtime/conditions"
|
||||
|
||||
sourcev1 "github.com/fluxcd/source-controller/api/v1beta2"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createSourceBucketCmd = &cobra.Command{
|
||||
Use: "bucket [name]",
|
||||
Short: "Create or update a Bucket source",
|
||||
Long: withPreviewNote(`The create source bucket command generates a Bucket resource and waits for it to be downloaded.
|
||||
For Buckets with static authentication, the credentials are stored in a Kubernetes secret.`),
|
||||
Example: ` # Create a source for a Bucket using static authentication
|
||||
flux create source bucket podinfo \
|
||||
--bucket-name=podinfo \
|
||||
--endpoint=minio.minio.svc.cluster.local:9000 \
|
||||
--insecure=true \
|
||||
--access-key=myaccesskey \
|
||||
--secret-key=mysecretkey \
|
||||
--interval=10m
|
||||
|
||||
# Create a source for an Amazon S3 Bucket using IAM authentication
|
||||
flux create source bucket podinfo \
|
||||
--bucket-name=podinfo \
|
||||
--provider=aws \
|
||||
--endpoint=s3.amazonaws.com \
|
||||
--region=us-east-1 \
|
||||
--interval=10m`,
|
||||
RunE: createSourceBucketCmdRun,
|
||||
}
|
||||
|
||||
type sourceBucketFlags struct {
|
||||
name string
|
||||
provider flags.SourceBucketProvider
|
||||
endpoint string
|
||||
accessKey string
|
||||
secretKey string
|
||||
region string
|
||||
insecure bool
|
||||
secretRef string
|
||||
ignorePaths []string
|
||||
}
|
||||
|
||||
var sourceBucketArgs = newSourceBucketFlags()
|
||||
|
||||
func init() {
|
||||
createSourceBucketCmd.Flags().Var(&sourceBucketArgs.provider, "provider", sourceBucketArgs.provider.Description())
|
||||
createSourceBucketCmd.Flags().StringVar(&sourceBucketArgs.name, "bucket-name", "", "the bucket name")
|
||||
createSourceBucketCmd.Flags().StringVar(&sourceBucketArgs.endpoint, "endpoint", "", "the bucket endpoint address")
|
||||
createSourceBucketCmd.Flags().StringVar(&sourceBucketArgs.accessKey, "access-key", "", "the bucket access key")
|
||||
createSourceBucketCmd.Flags().StringVar(&sourceBucketArgs.secretKey, "secret-key", "", "the bucket secret key")
|
||||
createSourceBucketCmd.Flags().StringVar(&sourceBucketArgs.region, "region", "", "the bucket region")
|
||||
createSourceBucketCmd.Flags().BoolVar(&sourceBucketArgs.insecure, "insecure", false, "for when connecting to a non-TLS S3 HTTP endpoint")
|
||||
createSourceBucketCmd.Flags().StringVar(&sourceBucketArgs.secretRef, "secret-ref", "", "the name of an existing secret containing credentials")
|
||||
createSourceBucketCmd.Flags().StringSliceVar(&sourceBucketArgs.ignorePaths, "ignore-paths", nil, "set paths to ignore in bucket resource (can specify multiple paths with commas: path1,path2)")
|
||||
|
||||
createSourceCmd.AddCommand(createSourceBucketCmd)
|
||||
}
|
||||
|
||||
func newSourceBucketFlags() sourceBucketFlags {
|
||||
return sourceBucketFlags{
|
||||
provider: flags.SourceBucketProvider(sourcev1.GenericBucketProvider),
|
||||
}
|
||||
}
|
||||
|
||||
func createSourceBucketCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if sourceBucketArgs.name == "" {
|
||||
return fmt.Errorf("bucket-name is required")
|
||||
}
|
||||
|
||||
if sourceBucketArgs.endpoint == "" {
|
||||
return fmt.Errorf("endpoint is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
tmpDir, err := os.MkdirTemp("", name)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
var ignorePaths *string
|
||||
if len(sourceBucketArgs.ignorePaths) > 0 {
|
||||
ignorePathsStr := strings.Join(sourceBucketArgs.ignorePaths, "\n")
|
||||
ignorePaths = &ignorePathsStr
|
||||
}
|
||||
|
||||
bucket := &sourcev1.Bucket{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: sourcev1.BucketSpec{
|
||||
BucketName: sourceBucketArgs.name,
|
||||
Provider: sourceBucketArgs.provider.String(),
|
||||
Insecure: sourceBucketArgs.insecure,
|
||||
Endpoint: sourceBucketArgs.endpoint,
|
||||
Region: sourceBucketArgs.region,
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
Ignore: ignorePaths,
|
||||
},
|
||||
}
|
||||
|
||||
if createSourceArgs.fetchTimeout > 0 {
|
||||
bucket.Spec.Timeout = &metav1.Duration{Duration: createSourceArgs.fetchTimeout}
|
||||
}
|
||||
|
||||
if sourceBucketArgs.secretRef != "" {
|
||||
bucket.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: sourceBucketArgs.secretRef,
|
||||
}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportBucket(bucket))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Generatef("generating Bucket source")
|
||||
|
||||
if sourceBucketArgs.secretRef == "" {
|
||||
secretName := fmt.Sprintf("bucket-%s", name)
|
||||
|
||||
secret := corev1.Secret{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
StringData: map[string]string{},
|
||||
}
|
||||
|
||||
if sourceBucketArgs.accessKey != "" && sourceBucketArgs.secretKey != "" {
|
||||
secret.StringData["accesskey"] = sourceBucketArgs.accessKey
|
||||
secret.StringData["secretkey"] = sourceBucketArgs.secretKey
|
||||
}
|
||||
|
||||
if len(secret.StringData) > 0 {
|
||||
logger.Actionf("applying secret with the bucket credentials")
|
||||
if err := upsertSecret(ctx, kubeClient, secret); err != nil {
|
||||
return err
|
||||
}
|
||||
bucket.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: secretName,
|
||||
}
|
||||
logger.Successf("authentication configured")
|
||||
}
|
||||
}
|
||||
|
||||
logger.Actionf("applying Bucket source")
|
||||
namespacedName, err := upsertBucket(ctx, kubeClient, bucket)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for Bucket source reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isBucketReady(ctx, kubeClient, namespacedName, bucket)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("Bucket source reconciliation completed")
|
||||
|
||||
if bucket.Status.Artifact == nil {
|
||||
return fmt.Errorf("Bucket source reconciliation but no artifact was found")
|
||||
}
|
||||
logger.Successf("fetched revision: %s", bucket.Status.Artifact.Revision)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertBucket(ctx context.Context, kubeClient client.Client,
|
||||
bucket *sourcev1.Bucket) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: bucket.GetNamespace(),
|
||||
Name: bucket.GetName(),
|
||||
}
|
||||
|
||||
var existing sourcev1.Bucket
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, bucket); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("Bucket source created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = bucket.Labels
|
||||
existing.Spec = bucket.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
bucket = &existing
|
||||
logger.Successf("Bucket source updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isBucketReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, bucket *sourcev1.Bucket) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, bucket)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := conditions.Get(bucket, meta.ReadyCondition); c != nil {
|
||||
// Confirm the Ready condition we are observing is for the
|
||||
// current generation
|
||||
if c.ObservedGeneration != bucket.GetGeneration() {
|
||||
return false, nil
|
||||
}
|
||||
|
||||
// Further check the Status
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
397
cmd/flux/create_source_git.go
Normal file
397
cmd/flux/create_source_git.go
Normal file
@@ -0,0 +1,397 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"crypto/elliptic"
|
||||
"fmt"
|
||||
"net/url"
|
||||
"os"
|
||||
"strings"
|
||||
|
||||
"github.com/manifoldco/promptui"
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
"sigs.k8s.io/yaml"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
"github.com/fluxcd/pkg/runtime/conditions"
|
||||
|
||||
sourcev1 "github.com/fluxcd/source-controller/api/v1"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
)
|
||||
|
||||
type sourceGitFlags struct {
|
||||
url string
|
||||
branch string
|
||||
tag string
|
||||
semver string
|
||||
refName string
|
||||
commit string
|
||||
username string
|
||||
password string
|
||||
keyAlgorithm flags.PublicKeyAlgorithm
|
||||
keyRSABits flags.RSAKeyBits
|
||||
keyECDSACurve flags.ECDSACurve
|
||||
secretRef string
|
||||
caFile string
|
||||
privateKeyFile string
|
||||
recurseSubmodules bool
|
||||
silent bool
|
||||
ignorePaths []string
|
||||
}
|
||||
|
||||
var createSourceGitCmd = &cobra.Command{
|
||||
Use: "git [name]",
|
||||
Short: "Create or update a GitRepository source",
|
||||
Long: `The create source git command generates a GitRepository resource and waits for it to sync.
|
||||
For Git over SSH, host and SSH keys are automatically generated and stored in a Kubernetes secret.
|
||||
For private Git repositories, the basic authentication credentials are stored in a Kubernetes secret.`,
|
||||
Example: ` # Create a source from a public Git repository master branch
|
||||
flux create source git podinfo \
|
||||
--url=https://github.com/stefanprodan/podinfo \
|
||||
--branch=master
|
||||
|
||||
# Create a source for a Git repository pinned to specific git tag
|
||||
flux create source git podinfo \
|
||||
--url=https://github.com/stefanprodan/podinfo \
|
||||
--tag="3.2.3"
|
||||
|
||||
# Create a source from a public Git repository tag that matches a semver range
|
||||
flux create source git podinfo \
|
||||
--url=https://github.com/stefanprodan/podinfo \
|
||||
--tag-semver=">=3.2.0 <3.3.0"
|
||||
|
||||
# Create a source for a Git repository using SSH authentication
|
||||
flux create source git podinfo \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--branch=master
|
||||
|
||||
# Create a source for a Git repository using SSH authentication and an
|
||||
# ECDSA P-521 curve public key
|
||||
flux create source git podinfo \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--branch=master \
|
||||
--ssh-key-algorithm=ecdsa \
|
||||
--ssh-ecdsa-curve=p521
|
||||
|
||||
# Create a source for a Git repository using SSH authentication and a
|
||||
# passwordless private key from file
|
||||
# The public SSH host key will still be gathered from the host
|
||||
flux create source git podinfo \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--branch=master \
|
||||
--private-key-file=./private.key
|
||||
|
||||
# Create a source for a Git repository using SSH authentication and a
|
||||
# private key with a password from file
|
||||
# The public SSH host key will still be gathered from the host
|
||||
flux create source git podinfo \
|
||||
--url=ssh://git@github.com/stefanprodan/podinfo \
|
||||
--branch=master \
|
||||
--private-key-file=./private.key \
|
||||
--password=<password>
|
||||
|
||||
# Create a source for a Git repository using basic authentication
|
||||
flux create source git podinfo \
|
||||
--url=https://github.com/stefanprodan/podinfo \
|
||||
--branch=master \
|
||||
--username=username \
|
||||
--password=password`,
|
||||
RunE: createSourceGitCmdRun,
|
||||
}
|
||||
|
||||
var sourceGitArgs = newSourceGitFlags()
|
||||
|
||||
func init() {
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.url, "url", "", "git address, e.g. ssh://git@host/org/repository")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.branch, "branch", "", "git branch")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.tag, "tag", "", "git tag")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.semver, "tag-semver", "", "git tag semver range")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.refName, "ref-name", "", " git reference name")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.commit, "commit", "", "git commit")
|
||||
createSourceGitCmd.Flags().StringVarP(&sourceGitArgs.username, "username", "u", "", "basic authentication username")
|
||||
createSourceGitCmd.Flags().StringVarP(&sourceGitArgs.password, "password", "p", "", "basic authentication password")
|
||||
createSourceGitCmd.Flags().Var(&sourceGitArgs.keyAlgorithm, "ssh-key-algorithm", sourceGitArgs.keyAlgorithm.Description())
|
||||
createSourceGitCmd.Flags().Var(&sourceGitArgs.keyRSABits, "ssh-rsa-bits", sourceGitArgs.keyRSABits.Description())
|
||||
createSourceGitCmd.Flags().Var(&sourceGitArgs.keyECDSACurve, "ssh-ecdsa-curve", sourceGitArgs.keyECDSACurve.Description())
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.secretRef, "secret-ref", "", "the name of an existing secret containing SSH or basic credentials")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.caFile, "ca-file", "", "path to TLS CA file used for validating self-signed certificates")
|
||||
createSourceGitCmd.Flags().StringVar(&sourceGitArgs.privateKeyFile, "private-key-file", "", "path to a passwordless private key file used for authenticating to the Git SSH server")
|
||||
createSourceGitCmd.Flags().BoolVar(&sourceGitArgs.recurseSubmodules, "recurse-submodules", false,
|
||||
"when enabled, configures the GitRepository source to initialize and include Git submodules in the artifact it produces")
|
||||
createSourceGitCmd.Flags().BoolVarP(&sourceGitArgs.silent, "silent", "s", false, "assumes the deploy key is already setup, skips confirmation")
|
||||
createSourceGitCmd.Flags().StringSliceVar(&sourceGitArgs.ignorePaths, "ignore-paths", nil, "set paths to ignore in git resource (can specify multiple paths with commas: path1,path2)")
|
||||
|
||||
createSourceCmd.AddCommand(createSourceGitCmd)
|
||||
}
|
||||
|
||||
func newSourceGitFlags() sourceGitFlags {
|
||||
return sourceGitFlags{
|
||||
keyAlgorithm: flags.PublicKeyAlgorithm(sourcesecret.ECDSAPrivateKeyAlgorithm),
|
||||
keyRSABits: 2048,
|
||||
keyECDSACurve: flags.ECDSACurve{Curve: elliptic.P384()},
|
||||
}
|
||||
}
|
||||
|
||||
func createSourceGitCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if sourceGitArgs.url == "" {
|
||||
return fmt.Errorf("url is required")
|
||||
}
|
||||
|
||||
u, err := url.Parse(sourceGitArgs.url)
|
||||
if err != nil {
|
||||
return fmt.Errorf("git URL parse failed: %w", err)
|
||||
}
|
||||
if u.Scheme != "ssh" && u.Scheme != "http" && u.Scheme != "https" {
|
||||
return fmt.Errorf("git URL scheme '%s' not supported, can be: ssh, http and https", u.Scheme)
|
||||
}
|
||||
|
||||
if sourceGitArgs.branch == "" && sourceGitArgs.tag == "" && sourceGitArgs.semver == "" && sourceGitArgs.commit == "" && sourceGitArgs.refName == "" {
|
||||
return fmt.Errorf("a Git ref is required, use one of the following: --branch, --tag, --commit, --ref-name or --tag-semver")
|
||||
}
|
||||
|
||||
if sourceGitArgs.caFile != "" && u.Scheme == "ssh" {
|
||||
return fmt.Errorf("specifying a CA file is not supported for Git over SSH")
|
||||
}
|
||||
|
||||
tmpDir, err := os.MkdirTemp("", name)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
var ignorePaths *string
|
||||
if len(sourceGitArgs.ignorePaths) > 0 {
|
||||
ignorePathsStr := strings.Join(sourceGitArgs.ignorePaths, "\n")
|
||||
ignorePaths = &ignorePathsStr
|
||||
}
|
||||
|
||||
gitRepository := sourcev1.GitRepository{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: sourcev1.GitRepositorySpec{
|
||||
URL: sourceGitArgs.url,
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
RecurseSubmodules: sourceGitArgs.recurseSubmodules,
|
||||
Reference: &sourcev1.GitRepositoryRef{},
|
||||
Ignore: ignorePaths,
|
||||
},
|
||||
}
|
||||
|
||||
if createSourceArgs.fetchTimeout > 0 {
|
||||
gitRepository.Spec.Timeout = &metav1.Duration{Duration: createSourceArgs.fetchTimeout}
|
||||
}
|
||||
|
||||
if sourceGitArgs.commit != "" {
|
||||
gitRepository.Spec.Reference.Commit = sourceGitArgs.commit
|
||||
gitRepository.Spec.Reference.Branch = sourceGitArgs.branch
|
||||
} else if sourceGitArgs.refName != "" {
|
||||
gitRepository.Spec.Reference.Name = sourceGitArgs.refName
|
||||
} else if sourceGitArgs.semver != "" {
|
||||
gitRepository.Spec.Reference.SemVer = sourceGitArgs.semver
|
||||
} else if sourceGitArgs.tag != "" {
|
||||
gitRepository.Spec.Reference.Tag = sourceGitArgs.tag
|
||||
} else {
|
||||
gitRepository.Spec.Reference.Branch = sourceGitArgs.branch
|
||||
}
|
||||
|
||||
if sourceGitArgs.secretRef != "" {
|
||||
gitRepository.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: sourceGitArgs.secretRef,
|
||||
}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportGit(&gitRepository))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Generatef("generating GitRepository source")
|
||||
if sourceGitArgs.secretRef == "" {
|
||||
secretOpts := sourcesecret.Options{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
switch u.Scheme {
|
||||
case "ssh":
|
||||
keypair, err := sourcesecret.LoadKeyPairFromPath(sourceGitArgs.privateKeyFile, sourceGitArgs.password)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
secretOpts.Keypair = keypair
|
||||
secretOpts.SSHHostname = u.Host
|
||||
secretOpts.PrivateKeyAlgorithm = sourcesecret.PrivateKeyAlgorithm(sourceGitArgs.keyAlgorithm)
|
||||
secretOpts.RSAKeyBits = int(sourceGitArgs.keyRSABits)
|
||||
secretOpts.ECDSACurve = sourceGitArgs.keyECDSACurve.Curve
|
||||
secretOpts.Password = sourceGitArgs.password
|
||||
case "https":
|
||||
if sourceGitArgs.caFile != "" {
|
||||
caBundle, err := os.ReadFile(sourceGitArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
secretOpts.CAFile = caBundle
|
||||
}
|
||||
secretOpts.Username = sourceGitArgs.username
|
||||
secretOpts.Password = sourceGitArgs.password
|
||||
case "http":
|
||||
logger.Warningf("insecure configuration: credentials configured for an HTTP URL")
|
||||
secretOpts.Username = sourceGitArgs.username
|
||||
secretOpts.Password = sourceGitArgs.password
|
||||
}
|
||||
secret, err := sourcesecret.Generate(secretOpts)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
var s corev1.Secret
|
||||
if err = yaml.Unmarshal([]byte(secret.Content), &s); err != nil {
|
||||
return err
|
||||
}
|
||||
if len(s.StringData) > 0 {
|
||||
if hk, ok := s.StringData[sourcesecret.KnownHostsSecretKey]; ok {
|
||||
logger.Successf("collected public key from SSH server:\n%s", hk)
|
||||
}
|
||||
if ppk, ok := s.StringData[sourcesecret.PublicKeySecretKey]; ok {
|
||||
logger.Generatef("deploy key: %s", ppk)
|
||||
if !sourceGitArgs.silent {
|
||||
prompt := promptui.Prompt{
|
||||
Label: "Have you added the deploy key to your repository",
|
||||
IsConfirm: true,
|
||||
}
|
||||
if _, err := prompt.Run(); err != nil {
|
||||
return fmt.Errorf("aborting")
|
||||
}
|
||||
}
|
||||
}
|
||||
logger.Actionf("applying secret with repository credentials")
|
||||
if err := upsertSecret(ctx, kubeClient, s); err != nil {
|
||||
return err
|
||||
}
|
||||
gitRepository.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: s.Name,
|
||||
}
|
||||
logger.Successf("authentication configured")
|
||||
}
|
||||
}
|
||||
|
||||
logger.Actionf("applying GitRepository source")
|
||||
namespacedName, err := upsertGitRepository(ctx, kubeClient, &gitRepository)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for GitRepository source reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isGitRepositoryReady(ctx, kubeClient, namespacedName, &gitRepository)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("GitRepository source reconciliation completed")
|
||||
|
||||
if gitRepository.Status.Artifact == nil {
|
||||
return fmt.Errorf("GitRepository source reconciliation completed but no artifact was found")
|
||||
}
|
||||
logger.Successf("fetched revision: %s", gitRepository.Status.Artifact.Revision)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertGitRepository(ctx context.Context, kubeClient client.Client,
|
||||
gitRepository *sourcev1.GitRepository) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: gitRepository.GetNamespace(),
|
||||
Name: gitRepository.GetName(),
|
||||
}
|
||||
|
||||
var existing sourcev1.GitRepository
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, gitRepository); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("GitRepository source created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = gitRepository.Labels
|
||||
existing.Spec = gitRepository.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
gitRepository = &existing
|
||||
logger.Successf("GitRepository source updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isGitRepositoryReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, gitRepository *sourcev1.GitRepository) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, gitRepository)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := conditions.Get(gitRepository, meta.ReadyCondition); c != nil {
|
||||
// Confirm the Ready condition we are observing is for the
|
||||
// current generation
|
||||
if c.ObservedGeneration != gitRepository.GetGeneration() {
|
||||
return false, nil
|
||||
}
|
||||
|
||||
// Further check the Status
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
235
cmd/flux/create_source_git_test.go
Normal file
235
cmd/flux/create_source_git_test.go
Normal file
@@ -0,0 +1,235 @@
|
||||
//go:build unit
|
||||
// +build unit
|
||||
|
||||
/*
|
||||
Copyright 2021 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"testing"
|
||||
"time"
|
||||
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
apimeta "k8s.io/apimachinery/pkg/api/meta"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
sourcev1 "github.com/fluxcd/source-controller/api/v1"
|
||||
)
|
||||
|
||||
var pollInterval = 50 * time.Millisecond
|
||||
var testTimeout = 10 * time.Second
|
||||
|
||||
// Update the GitRepository once created to exercise test specific behavior
|
||||
type reconcileFunc func(repo *sourcev1.GitRepository)
|
||||
|
||||
// reconciler waits for an object to be created, then invokes a test supplied
|
||||
// function to mutate that object, simulating a controller.
|
||||
// Test should invoke run() to run the background reconciler task which
|
||||
// polls to wait for the object to exist before applying the update function.
|
||||
// Any errors from the reconciler are asserted on test completion.
|
||||
type reconciler struct {
|
||||
client client.Client
|
||||
name types.NamespacedName
|
||||
reconcile reconcileFunc
|
||||
}
|
||||
|
||||
// Start the background task that waits for the object to exist then applies
|
||||
// the update function.
|
||||
func (r *reconciler) run(t *testing.T) {
|
||||
result := make(chan error)
|
||||
go func() {
|
||||
defer close(result)
|
||||
err := wait.PollImmediate(
|
||||
pollInterval,
|
||||
testTimeout,
|
||||
r.conditionFunc)
|
||||
result <- err
|
||||
}()
|
||||
t.Cleanup(func() {
|
||||
if err := <-result; err != nil {
|
||||
t.Errorf("Failure from test reconciler: '%v':", err.Error())
|
||||
}
|
||||
})
|
||||
}
|
||||
|
||||
// A ConditionFunction that waits for the named GitRepository to be created,
|
||||
// then sets the ready condition to true.
|
||||
func (r *reconciler) conditionFunc() (bool, error) {
|
||||
var repo sourcev1.GitRepository
|
||||
if err := r.client.Get(context.Background(), r.name, &repo); err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
return false, nil // Keep polling until object is created
|
||||
}
|
||||
return true, err
|
||||
}
|
||||
r.reconcile(&repo)
|
||||
err := r.client.Status().Update(context.Background(), &repo)
|
||||
return true, err
|
||||
}
|
||||
|
||||
func TestCreateSourceGitExport(t *testing.T) {
|
||||
var command = "create source git podinfo --url=https://github.com/stefanprodan/podinfo --branch=master --ignore-paths .cosign,non-existent-dir/ -n default --interval 1m --export --timeout=" + testTimeout.String()
|
||||
|
||||
cases := []struct {
|
||||
name string
|
||||
args string
|
||||
assert assertFunc
|
||||
}{
|
||||
{
|
||||
"ExportSucceeded",
|
||||
command,
|
||||
assertGoldenFile("testdata/create_source_git/export.golden"),
|
||||
},
|
||||
{
|
||||
name: "no args",
|
||||
args: "create secret git",
|
||||
assert: assertError("name is required"),
|
||||
},
|
||||
{
|
||||
name: "source with commit",
|
||||
args: "create source git podinfo --namespace=flux-system --url=https://github.com/stefanprodan/podinfo --commit=c88a2f41 --interval=1m0s --export",
|
||||
assert: assertGoldenFile("./testdata/create_source_git/source-git-commit.yaml"),
|
||||
},
|
||||
{
|
||||
name: "source with ref name",
|
||||
args: "create source git podinfo --namespace=flux-system --url=https://github.com/stefanprodan/podinfo --ref-name=refs/heads/main --interval=1m0s --export",
|
||||
assert: assertGoldenFile("testdata/create_source_git/source-git-refname.yaml"),
|
||||
},
|
||||
{
|
||||
name: "source with branch name and commit",
|
||||
args: "create source git podinfo --namespace=flux-system --url=https://github.com/stefanprodan/podinfo --branch=main --commit=c88a2f41 --interval=1m0s --export",
|
||||
assert: assertGoldenFile("testdata/create_source_git/source-git-branch-commit.yaml"),
|
||||
},
|
||||
{
|
||||
name: "source with semver",
|
||||
args: "create source git podinfo --namespace=flux-system --url=https://github.com/stefanprodan/podinfo --tag-semver=v1.01 --interval=1m0s --export",
|
||||
assert: assertGoldenFile("testdata/create_source_git/source-git-semver.yaml"),
|
||||
},
|
||||
{
|
||||
name: "source with git tag",
|
||||
args: "create source git podinfo --namespace=flux-system --url=https://github.com/stefanprodan/podinfo --tag=test --interval=1m0s --export",
|
||||
assert: assertGoldenFile("testdata/create_source_git/source-git-tag.yaml"),
|
||||
},
|
||||
{
|
||||
name: "source with git branch",
|
||||
args: "create source git podinfo --namespace=flux-system --url=https://github.com/stefanprodan/podinfo --branch=test --interval=1m0s --export",
|
||||
assert: assertGoldenFile("testdata/create_source_git/source-git-branch.yaml"),
|
||||
},
|
||||
}
|
||||
for _, tc := range cases {
|
||||
t.Run(tc.name, func(t *testing.T) {
|
||||
cmd := cmdTestCase{
|
||||
args: tc.args,
|
||||
assert: tc.assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
|
||||
func TestCreateSourceGit(t *testing.T) {
|
||||
// Default command used for multiple tests
|
||||
var command = "create source git podinfo --url=https://github.com/stefanprodan/podinfo --branch=master --timeout=" + testTimeout.String()
|
||||
|
||||
cases := []struct {
|
||||
name string
|
||||
args string
|
||||
assert assertFunc
|
||||
reconcile reconcileFunc
|
||||
}{
|
||||
{
|
||||
"NoArgs",
|
||||
"create source git",
|
||||
assertError("name is required"),
|
||||
nil,
|
||||
}, {
|
||||
"Succeeded",
|
||||
command,
|
||||
assertGoldenFile("testdata/create_source_git/success.golden"),
|
||||
func(repo *sourcev1.GitRepository) {
|
||||
newCondition := metav1.Condition{
|
||||
Type: meta.ReadyCondition,
|
||||
Status: metav1.ConditionTrue,
|
||||
Reason: sourcev1.GitOperationSucceedReason,
|
||||
Message: "succeeded message",
|
||||
ObservedGeneration: repo.GetGeneration(),
|
||||
}
|
||||
apimeta.SetStatusCondition(&repo.Status.Conditions, newCondition)
|
||||
repo.Status.Artifact = &sourcev1.Artifact{
|
||||
Path: "some-path",
|
||||
Revision: "v1",
|
||||
LastUpdateTime: metav1.Time{
|
||||
Time: time.Now(),
|
||||
},
|
||||
}
|
||||
},
|
||||
}, {
|
||||
"Failed",
|
||||
command,
|
||||
assertError("failed message"),
|
||||
func(repo *sourcev1.GitRepository) {
|
||||
newCondition := metav1.Condition{
|
||||
Type: meta.ReadyCondition,
|
||||
Status: metav1.ConditionFalse,
|
||||
Reason: sourcev1.URLInvalidReason,
|
||||
Message: "failed message",
|
||||
ObservedGeneration: repo.GetGeneration(),
|
||||
}
|
||||
apimeta.SetStatusCondition(&repo.Status.Conditions, newCondition)
|
||||
},
|
||||
}, {
|
||||
"NoArtifact",
|
||||
command,
|
||||
assertError("GitRepository source reconciliation completed but no artifact was found"),
|
||||
func(repo *sourcev1.GitRepository) {
|
||||
// Updated with no artifact
|
||||
newCondition := metav1.Condition{
|
||||
Type: meta.ReadyCondition,
|
||||
Status: metav1.ConditionTrue,
|
||||
Reason: sourcev1.GitOperationSucceedReason,
|
||||
Message: "succeeded message",
|
||||
ObservedGeneration: repo.GetGeneration(),
|
||||
}
|
||||
apimeta.SetStatusCondition(&repo.Status.Conditions, newCondition)
|
||||
},
|
||||
},
|
||||
}
|
||||
for _, tc := range cases {
|
||||
t.Run(tc.name, func(t *testing.T) {
|
||||
ns := allocateNamespace("podinfo")
|
||||
setupTestNamespace(ns, t)
|
||||
if tc.reconcile != nil {
|
||||
r := reconciler{
|
||||
client: testEnv.client,
|
||||
name: types.NamespacedName{Namespace: ns, Name: "podinfo"},
|
||||
reconcile: tc.reconcile,
|
||||
}
|
||||
r.run(t)
|
||||
}
|
||||
cmd := cmdTestCase{
|
||||
args: tc.args + " -n=" + ns,
|
||||
assert: tc.assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
308
cmd/flux/create_source_helm.go
Normal file
308
cmd/flux/create_source_helm.go
Normal file
@@ -0,0 +1,308 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"net/url"
|
||||
"os"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
"github.com/fluxcd/pkg/runtime/conditions"
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
"sigs.k8s.io/yaml"
|
||||
|
||||
sourcev1 "github.com/fluxcd/source-controller/api/v1beta2"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/fluxcd/flux2/v2/pkg/manifestgen/sourcesecret"
|
||||
)
|
||||
|
||||
var createSourceHelmCmd = &cobra.Command{
|
||||
Use: "helm [name]",
|
||||
Short: "Create or update a HelmRepository source",
|
||||
Long: withPreviewNote(`The create source helm command generates a HelmRepository resource and waits for it to fetch the index.
|
||||
For private Helm repositories, the basic authentication credentials are stored in a Kubernetes secret.`),
|
||||
Example: ` # Create a source for an HTTPS public Helm repository
|
||||
flux create source helm podinfo \
|
||||
--url=https://stefanprodan.github.io/podinfo \
|
||||
--interval=10m
|
||||
|
||||
# Create a source for an HTTPS Helm repository using basic authentication
|
||||
flux create source helm podinfo \
|
||||
--url=https://stefanprodan.github.io/podinfo \
|
||||
--username=username \
|
||||
--password=password
|
||||
|
||||
# Create a source for an HTTPS Helm repository using TLS authentication
|
||||
flux create source helm podinfo \
|
||||
--url=https://stefanprodan.github.io/podinfo \
|
||||
--cert-file=./cert.crt \
|
||||
--key-file=./key.crt \
|
||||
--ca-file=./ca.crt
|
||||
|
||||
# Create a source for an OCI Helm repository
|
||||
flux create source helm podinfo \
|
||||
--url=oci://ghcr.io/stefanprodan/charts/podinfo \
|
||||
--username=username \
|
||||
--password=password
|
||||
|
||||
# Create a source for an OCI Helm repository using an existing secret with basic auth or dockerconfig credentials
|
||||
flux create source helm podinfo \
|
||||
--url=oci://ghcr.io/stefanprodan/charts/podinfo \
|
||||
--secret-ref=docker-config`,
|
||||
RunE: createSourceHelmCmdRun,
|
||||
}
|
||||
|
||||
type sourceHelmFlags struct {
|
||||
url string
|
||||
username string
|
||||
password string
|
||||
certFile string
|
||||
keyFile string
|
||||
caFile string
|
||||
secretRef string
|
||||
ociProvider string
|
||||
passCredentials bool
|
||||
}
|
||||
|
||||
var sourceHelmArgs sourceHelmFlags
|
||||
|
||||
func init() {
|
||||
createSourceHelmCmd.Flags().StringVar(&sourceHelmArgs.url, "url", "", "Helm repository address")
|
||||
createSourceHelmCmd.Flags().StringVarP(&sourceHelmArgs.username, "username", "u", "", "basic authentication username")
|
||||
createSourceHelmCmd.Flags().StringVarP(&sourceHelmArgs.password, "password", "p", "", "basic authentication password")
|
||||
createSourceHelmCmd.Flags().StringVar(&sourceHelmArgs.certFile, "cert-file", "", "TLS authentication cert file path")
|
||||
createSourceHelmCmd.Flags().StringVar(&sourceHelmArgs.keyFile, "key-file", "", "TLS authentication key file path")
|
||||
createSourceHelmCmd.Flags().StringVar(&sourceHelmArgs.caFile, "ca-file", "", "TLS authentication CA file path")
|
||||
createSourceHelmCmd.Flags().StringVarP(&sourceHelmArgs.secretRef, "secret-ref", "", "", "the name of an existing secret containing TLS, basic auth or docker-config credentials")
|
||||
createSourceHelmCmd.Flags().StringVar(&sourceHelmArgs.ociProvider, "oci-provider", "", "OCI provider for authentication")
|
||||
createSourceHelmCmd.Flags().BoolVarP(&sourceHelmArgs.passCredentials, "pass-credentials", "", false, "pass credentials to all domains")
|
||||
|
||||
createSourceCmd.AddCommand(createSourceHelmCmd)
|
||||
}
|
||||
|
||||
func createSourceHelmCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if sourceHelmArgs.url == "" {
|
||||
return fmt.Errorf("url is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
tmpDir, err := os.MkdirTemp("", name)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer os.RemoveAll(tmpDir)
|
||||
|
||||
if _, err := url.Parse(sourceHelmArgs.url); err != nil {
|
||||
return fmt.Errorf("url parse failed: %w", err)
|
||||
}
|
||||
|
||||
helmRepository := &sourcev1.HelmRepository{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: sourcev1.HelmRepositorySpec{
|
||||
URL: sourceHelmArgs.url,
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
url, err := url.Parse(sourceHelmArgs.url)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to parse URL: %w", err)
|
||||
}
|
||||
if url.Scheme == sourcev1.HelmRepositoryTypeOCI {
|
||||
helmRepository.Spec.Type = sourcev1.HelmRepositoryTypeOCI
|
||||
helmRepository.Spec.Provider = sourceHelmArgs.ociProvider
|
||||
}
|
||||
|
||||
if createSourceArgs.fetchTimeout > 0 {
|
||||
helmRepository.Spec.Timeout = &metav1.Duration{Duration: createSourceArgs.fetchTimeout}
|
||||
}
|
||||
|
||||
if sourceHelmArgs.secretRef != "" {
|
||||
helmRepository.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: sourceHelmArgs.secretRef,
|
||||
}
|
||||
helmRepository.Spec.PassCredentials = sourceHelmArgs.passCredentials
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportHelmRepository(helmRepository))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
caBundle := []byte{}
|
||||
if sourceHelmArgs.caFile != "" {
|
||||
var err error
|
||||
caBundle, err = os.ReadFile(sourceHelmArgs.caFile)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to read TLS CA file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
var certFile, keyFile []byte
|
||||
if sourceHelmArgs.certFile != "" && sourceHelmArgs.keyFile != "" {
|
||||
if certFile, err = os.ReadFile(sourceHelmArgs.certFile); err != nil {
|
||||
return fmt.Errorf("failed to read cert file: %w", err)
|
||||
}
|
||||
if keyFile, err = os.ReadFile(sourceHelmArgs.keyFile); err != nil {
|
||||
return fmt.Errorf("failed to read key file: %w", err)
|
||||
}
|
||||
}
|
||||
|
||||
logger.Generatef("generating HelmRepository source")
|
||||
if sourceHelmArgs.secretRef == "" {
|
||||
secretName := fmt.Sprintf("helm-%s", name)
|
||||
secretOpts := sourcesecret.Options{
|
||||
Name: secretName,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Username: sourceHelmArgs.username,
|
||||
Password: sourceHelmArgs.password,
|
||||
CAFile: caBundle,
|
||||
CertFile: certFile,
|
||||
KeyFile: keyFile,
|
||||
ManifestFile: sourcesecret.MakeDefaultOptions().ManifestFile,
|
||||
}
|
||||
secret, err := sourcesecret.Generate(secretOpts)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
var s corev1.Secret
|
||||
if err = yaml.Unmarshal([]byte(secret.Content), &s); err != nil {
|
||||
return err
|
||||
}
|
||||
if len(s.StringData) > 0 {
|
||||
logger.Actionf("applying secret with repository credentials")
|
||||
if err := upsertSecret(ctx, kubeClient, s); err != nil {
|
||||
return err
|
||||
}
|
||||
helmRepository.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: secretName,
|
||||
}
|
||||
helmRepository.Spec.PassCredentials = sourceHelmArgs.passCredentials
|
||||
logger.Successf("authentication configured")
|
||||
}
|
||||
}
|
||||
|
||||
logger.Actionf("applying HelmRepository source")
|
||||
namespacedName, err := upsertHelmRepository(ctx, kubeClient, helmRepository)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for HelmRepository source reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isHelmRepositoryReady(ctx, kubeClient, namespacedName, helmRepository)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("HelmRepository source reconciliation completed")
|
||||
|
||||
if helmRepository.Spec.Type == sourcev1.HelmRepositoryTypeOCI {
|
||||
// OCI repos don't expose any artifact so we just return early here
|
||||
return nil
|
||||
}
|
||||
|
||||
if helmRepository.Status.Artifact == nil {
|
||||
return fmt.Errorf("HelmRepository source reconciliation completed but no artifact was found")
|
||||
}
|
||||
logger.Successf("fetched revision: %s", helmRepository.Status.Artifact.Revision)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertHelmRepository(ctx context.Context, kubeClient client.Client,
|
||||
helmRepository *sourcev1.HelmRepository) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: helmRepository.GetNamespace(),
|
||||
Name: helmRepository.GetName(),
|
||||
}
|
||||
|
||||
var existing sourcev1.HelmRepository
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, helmRepository); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("source created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = helmRepository.Labels
|
||||
existing.Spec = helmRepository.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
helmRepository = &existing
|
||||
logger.Successf("source updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isHelmRepositoryReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, helmRepository *sourcev1.HelmRepository) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, helmRepository)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := conditions.Get(helmRepository, meta.ReadyCondition); c != nil {
|
||||
// Confirm the Ready condition we are observing is for the
|
||||
// current generation
|
||||
if c.ObservedGeneration != helmRepository.GetGeneration() {
|
||||
return false, nil
|
||||
}
|
||||
|
||||
// Further check the Status
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
81
cmd/flux/create_source_helm_test.go
Normal file
81
cmd/flux/create_source_helm_test.go
Normal file
@@ -0,0 +1,81 @@
|
||||
//go:build unit
|
||||
// +build unit
|
||||
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestCreateSourceHelm(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
resultFile string
|
||||
assertFunc string
|
||||
}{
|
||||
{
|
||||
name: "no args",
|
||||
args: "create source helm",
|
||||
resultFile: "name is required",
|
||||
assertFunc: "assertError",
|
||||
},
|
||||
{
|
||||
name: "OCI repo",
|
||||
args: "create source helm podinfo --url=oci://ghcr.io/stefanprodan/charts/podinfo --interval 5m --export",
|
||||
resultFile: "./testdata/create_source_helm/oci.golden",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "OCI repo with Secret ref",
|
||||
args: "create source helm podinfo --url=oci://ghcr.io/stefanprodan/charts/podinfo --interval 5m --secret-ref=creds --export",
|
||||
resultFile: "./testdata/create_source_helm/oci-with-secret.golden",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
{
|
||||
name: "HTTPS repo",
|
||||
args: "create source helm podinfo --url=https://stefanprodan.github.io/charts/podinfo --interval 5m --export",
|
||||
resultFile: "./testdata/create_source_helm/https.golden",
|
||||
assertFunc: "assertGoldenTemplateFile",
|
||||
},
|
||||
}
|
||||
|
||||
tmpl := map[string]string{
|
||||
"fluxns": allocateNamespace("flux-system"),
|
||||
}
|
||||
setup(t, tmpl)
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
var assert assertFunc
|
||||
switch tt.assertFunc {
|
||||
case "assertGoldenTemplateFile":
|
||||
assert = assertGoldenTemplateFile(tt.resultFile, tmpl)
|
||||
case "assertError":
|
||||
assert = assertError(tt.resultFile)
|
||||
}
|
||||
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args + " -n " + tmpl["fluxns"],
|
||||
assert: assert,
|
||||
}
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
247
cmd/flux/create_source_oci.go
Normal file
247
cmd/flux/create_source_oci.go
Normal file
@@ -0,0 +1,247 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"strings"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
|
||||
"github.com/fluxcd/pkg/apis/meta"
|
||||
"github.com/fluxcd/pkg/runtime/conditions"
|
||||
|
||||
sourcev1 "github.com/fluxcd/source-controller/api/v1beta2"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/flags"
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var createSourceOCIRepositoryCmd = &cobra.Command{
|
||||
Use: "oci [name]",
|
||||
Short: "Create or update an OCIRepository",
|
||||
Long: withPreviewNote(`The create source oci command generates an OCIRepository resource and waits for it to be ready.`),
|
||||
Example: ` # Create an OCIRepository for a public container image
|
||||
flux create source oci podinfo \
|
||||
--url=oci://ghcr.io/stefanprodan/manifests/podinfo \
|
||||
--tag=6.1.6 \
|
||||
--interval=10m
|
||||
`,
|
||||
RunE: createSourceOCIRepositoryCmdRun,
|
||||
}
|
||||
|
||||
type sourceOCIRepositoryFlags struct {
|
||||
url string
|
||||
tag string
|
||||
semver string
|
||||
digest string
|
||||
secretRef string
|
||||
serviceAccount string
|
||||
certSecretRef string
|
||||
ignorePaths []string
|
||||
provider flags.SourceOCIProvider
|
||||
insecure bool
|
||||
}
|
||||
|
||||
var sourceOCIRepositoryArgs = newSourceOCIFlags()
|
||||
|
||||
func newSourceOCIFlags() sourceOCIRepositoryFlags {
|
||||
return sourceOCIRepositoryFlags{
|
||||
provider: flags.SourceOCIProvider(sourcev1.GenericOCIProvider),
|
||||
}
|
||||
}
|
||||
|
||||
func init() {
|
||||
createSourceOCIRepositoryCmd.Flags().Var(&sourceOCIRepositoryArgs.provider, "provider", sourceOCIRepositoryArgs.provider.Description())
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.url, "url", "", "the OCI repository URL")
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.tag, "tag", "", "the OCI artifact tag")
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.semver, "tag-semver", "", "the OCI artifact tag semver range")
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.digest, "digest", "", "the OCI artifact digest")
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.secretRef, "secret-ref", "", "the name of the Kubernetes image pull secret (type 'kubernetes.io/dockerconfigjson')")
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.serviceAccount, "service-account", "", "the name of the Kubernetes service account that refers to an image pull secret")
|
||||
createSourceOCIRepositoryCmd.Flags().StringVar(&sourceOCIRepositoryArgs.certSecretRef, "cert-ref", "", "the name of a secret to use for TLS certificates")
|
||||
createSourceOCIRepositoryCmd.Flags().StringSliceVar(&sourceOCIRepositoryArgs.ignorePaths, "ignore-paths", nil, "set paths to ignore resources (can specify multiple paths with commas: path1,path2)")
|
||||
createSourceOCIRepositoryCmd.Flags().BoolVar(&sourceOCIRepositoryArgs.insecure, "insecure", false, "for when connecting to a non-TLS registries over plain HTTP")
|
||||
|
||||
createSourceCmd.AddCommand(createSourceOCIRepositoryCmd)
|
||||
}
|
||||
|
||||
func createSourceOCIRepositoryCmdRun(cmd *cobra.Command, args []string) error {
|
||||
name := args[0]
|
||||
|
||||
if sourceOCIRepositoryArgs.url == "" {
|
||||
return fmt.Errorf("url is required")
|
||||
}
|
||||
|
||||
if sourceOCIRepositoryArgs.semver == "" && sourceOCIRepositoryArgs.tag == "" && sourceOCIRepositoryArgs.digest == "" {
|
||||
return fmt.Errorf("--tag, --tag-semver or --digest is required")
|
||||
}
|
||||
|
||||
sourceLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
var ignorePaths *string
|
||||
if len(sourceOCIRepositoryArgs.ignorePaths) > 0 {
|
||||
ignorePathsStr := strings.Join(sourceOCIRepositoryArgs.ignorePaths, "\n")
|
||||
ignorePaths = &ignorePathsStr
|
||||
}
|
||||
|
||||
repository := &sourcev1.OCIRepository{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: name,
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Labels: sourceLabels,
|
||||
},
|
||||
Spec: sourcev1.OCIRepositorySpec{
|
||||
Provider: sourceOCIRepositoryArgs.provider.String(),
|
||||
URL: sourceOCIRepositoryArgs.url,
|
||||
Insecure: sourceOCIRepositoryArgs.insecure,
|
||||
Interval: metav1.Duration{
|
||||
Duration: createArgs.interval,
|
||||
},
|
||||
Reference: &sourcev1.OCIRepositoryRef{},
|
||||
Ignore: ignorePaths,
|
||||
},
|
||||
}
|
||||
|
||||
if digest := sourceOCIRepositoryArgs.digest; digest != "" {
|
||||
repository.Spec.Reference.Digest = digest
|
||||
}
|
||||
if semver := sourceOCIRepositoryArgs.semver; semver != "" {
|
||||
repository.Spec.Reference.SemVer = semver
|
||||
}
|
||||
if tag := sourceOCIRepositoryArgs.tag; tag != "" {
|
||||
repository.Spec.Reference.Tag = tag
|
||||
}
|
||||
|
||||
if createSourceArgs.fetchTimeout > 0 {
|
||||
repository.Spec.Timeout = &metav1.Duration{Duration: createSourceArgs.fetchTimeout}
|
||||
}
|
||||
|
||||
if saName := sourceOCIRepositoryArgs.serviceAccount; saName != "" {
|
||||
repository.Spec.ServiceAccountName = saName
|
||||
}
|
||||
|
||||
if secretName := sourceOCIRepositoryArgs.secretRef; secretName != "" {
|
||||
repository.Spec.SecretRef = &meta.LocalObjectReference{
|
||||
Name: secretName,
|
||||
}
|
||||
}
|
||||
|
||||
if secretName := sourceOCIRepositoryArgs.certSecretRef; secretName != "" {
|
||||
repository.Spec.CertSecretRef = &meta.LocalObjectReference{
|
||||
Name: secretName,
|
||||
}
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
return printExport(exportOCIRepository(repository))
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying OCIRepository")
|
||||
namespacedName, err := upsertOCIRepository(ctx, kubeClient, repository)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Waitingf("waiting for OCIRepository reconciliation")
|
||||
if err := wait.PollImmediate(rootArgs.pollInterval, rootArgs.timeout,
|
||||
isOCIRepositoryReady(ctx, kubeClient, namespacedName, repository)); err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("OCIRepository reconciliation completed")
|
||||
|
||||
if repository.Status.Artifact == nil {
|
||||
return fmt.Errorf("no artifact was found")
|
||||
}
|
||||
logger.Successf("fetched revision: %s", repository.Status.Artifact.Revision)
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertOCIRepository(ctx context.Context, kubeClient client.Client,
|
||||
ociRepository *sourcev1.OCIRepository) (types.NamespacedName, error) {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: ociRepository.GetNamespace(),
|
||||
Name: ociRepository.GetName(),
|
||||
}
|
||||
|
||||
var existing sourcev1.OCIRepository
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, ociRepository); err != nil {
|
||||
return namespacedName, err
|
||||
} else {
|
||||
logger.Successf("OCIRepository created")
|
||||
return namespacedName, nil
|
||||
}
|
||||
}
|
||||
return namespacedName, err
|
||||
}
|
||||
|
||||
existing.Labels = ociRepository.Labels
|
||||
existing.Spec = ociRepository.Spec
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return namespacedName, err
|
||||
}
|
||||
ociRepository = &existing
|
||||
logger.Successf("OCIRepository updated")
|
||||
return namespacedName, nil
|
||||
}
|
||||
|
||||
func isOCIRepositoryReady(ctx context.Context, kubeClient client.Client,
|
||||
namespacedName types.NamespacedName, ociRepository *sourcev1.OCIRepository) wait.ConditionFunc {
|
||||
return func() (bool, error) {
|
||||
err := kubeClient.Get(ctx, namespacedName, ociRepository)
|
||||
if err != nil {
|
||||
return false, err
|
||||
}
|
||||
|
||||
if c := conditions.Get(ociRepository, meta.ReadyCondition); c != nil {
|
||||
// Confirm the Ready condition we are observing is for the
|
||||
// current generation
|
||||
if c.ObservedGeneration != ociRepository.GetGeneration() {
|
||||
return false, nil
|
||||
}
|
||||
|
||||
// Further check the Status
|
||||
switch c.Status {
|
||||
case metav1.ConditionTrue:
|
||||
return true, nil
|
||||
case metav1.ConditionFalse:
|
||||
return false, fmt.Errorf(c.Message)
|
||||
}
|
||||
}
|
||||
return false, nil
|
||||
}
|
||||
}
|
||||
61
cmd/flux/create_source_oci_test.go
Normal file
61
cmd/flux/create_source_oci_test.go
Normal file
@@ -0,0 +1,61 @@
|
||||
/*
|
||||
Copyright 2022 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestCreateSourceOCI(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
args string
|
||||
assertFunc assertFunc
|
||||
}{
|
||||
{
|
||||
name: "NoArgs",
|
||||
args: "create source oci",
|
||||
assertFunc: assertError("name is required"),
|
||||
},
|
||||
{
|
||||
name: "NoURL",
|
||||
args: "create source oci podinfo",
|
||||
assertFunc: assertError("url is required"),
|
||||
},
|
||||
{
|
||||
name: "export manifest",
|
||||
args: "create source oci podinfo --url=oci://ghcr.io/stefanprodan/manifests/podinfo --tag=6.3.5 --interval 10m --export",
|
||||
assertFunc: assertGoldenFile("./testdata/oci/export.golden"),
|
||||
},
|
||||
{
|
||||
name: "export manifest with secret",
|
||||
args: "create source oci podinfo --url=oci://ghcr.io/stefanprodan/manifests/podinfo --tag=6.3.5 --interval 10m --secret-ref=creds --export",
|
||||
assertFunc: assertGoldenFile("./testdata/oci/export_with_secret.golden"),
|
||||
},
|
||||
}
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
cmd := cmdTestCase{
|
||||
args: tt.args,
|
||||
assert: tt.assertFunc,
|
||||
}
|
||||
|
||||
cmd.runTestCmd(t)
|
||||
})
|
||||
}
|
||||
}
|
||||
316
cmd/flux/create_tenant.go
Normal file
316
cmd/flux/create_tenant.go
Normal file
@@ -0,0 +1,316 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"bytes"
|
||||
"context"
|
||||
"fmt"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
"github.com/spf13/cobra"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
rbacv1 "k8s.io/api/rbac/v1"
|
||||
"k8s.io/apimachinery/pkg/api/equality"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
"k8s.io/apimachinery/pkg/util/validation"
|
||||
"sigs.k8s.io/controller-runtime/pkg/client"
|
||||
"sigs.k8s.io/yaml"
|
||||
)
|
||||
|
||||
var createTenantCmd = &cobra.Command{
|
||||
Use: "tenant",
|
||||
Short: "Create or update a tenant",
|
||||
Long: withPreviewNote(`The create tenant command generates namespaces, service accounts and role bindings to limit the
|
||||
reconcilers scope to the tenant namespaces.`),
|
||||
Example: ` # Create a tenant with access to a namespace
|
||||
flux create tenant dev-team \
|
||||
--with-namespace=frontend \
|
||||
--label=environment=dev
|
||||
|
||||
# Generate tenant namespaces and role bindings in YAML format
|
||||
flux create tenant dev-team \
|
||||
--with-namespace=frontend \
|
||||
--with-namespace=backend \
|
||||
--export > dev-team.yaml`,
|
||||
RunE: createTenantCmdRun,
|
||||
}
|
||||
|
||||
const (
|
||||
tenantLabel = "toolkit.fluxcd.io/tenant"
|
||||
)
|
||||
|
||||
type tenantFlags struct {
|
||||
namespaces []string
|
||||
clusterRole string
|
||||
}
|
||||
|
||||
var tenantArgs tenantFlags
|
||||
|
||||
func init() {
|
||||
createTenantCmd.Flags().StringSliceVar(&tenantArgs.namespaces, "with-namespace", nil, "namespace belonging to this tenant")
|
||||
createTenantCmd.Flags().StringVar(&tenantArgs.clusterRole, "cluster-role", "cluster-admin", "cluster role of the tenant role binding")
|
||||
createCmd.AddCommand(createTenantCmd)
|
||||
}
|
||||
|
||||
func createTenantCmdRun(cmd *cobra.Command, args []string) error {
|
||||
tenant := args[0]
|
||||
if err := validation.IsQualifiedName(tenant); len(err) > 0 {
|
||||
return fmt.Errorf("invalid tenant name '%s': %v", tenant, err)
|
||||
}
|
||||
|
||||
if tenantArgs.clusterRole == "" {
|
||||
return fmt.Errorf("cluster-role is required")
|
||||
}
|
||||
|
||||
if tenantArgs.namespaces == nil {
|
||||
return fmt.Errorf("with-namespace is required")
|
||||
}
|
||||
|
||||
var namespaces []corev1.Namespace
|
||||
var accounts []corev1.ServiceAccount
|
||||
var roleBindings []rbacv1.RoleBinding
|
||||
|
||||
for _, ns := range tenantArgs.namespaces {
|
||||
if err := validation.IsQualifiedName(ns); len(err) > 0 {
|
||||
return fmt.Errorf("invalid namespace '%s': %v", ns, err)
|
||||
}
|
||||
|
||||
objLabels, err := parseLabels()
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
objLabels[tenantLabel] = tenant
|
||||
|
||||
namespace := corev1.Namespace{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: ns,
|
||||
Labels: objLabels,
|
||||
},
|
||||
}
|
||||
namespaces = append(namespaces, namespace)
|
||||
|
||||
account := corev1.ServiceAccount{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: tenant,
|
||||
Namespace: ns,
|
||||
Labels: objLabels,
|
||||
},
|
||||
}
|
||||
|
||||
accounts = append(accounts, account)
|
||||
|
||||
roleBinding := rbacv1.RoleBinding{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: fmt.Sprintf("%s-reconciler", tenant),
|
||||
Namespace: ns,
|
||||
Labels: objLabels,
|
||||
},
|
||||
Subjects: []rbacv1.Subject{
|
||||
{
|
||||
APIGroup: "rbac.authorization.k8s.io",
|
||||
Kind: "User",
|
||||
Name: fmt.Sprintf("gotk:%s:reconciler", ns),
|
||||
},
|
||||
{
|
||||
Kind: "ServiceAccount",
|
||||
Name: tenant,
|
||||
Namespace: ns,
|
||||
},
|
||||
},
|
||||
RoleRef: rbacv1.RoleRef{
|
||||
APIGroup: "rbac.authorization.k8s.io",
|
||||
Kind: "ClusterRole",
|
||||
Name: tenantArgs.clusterRole,
|
||||
},
|
||||
}
|
||||
roleBindings = append(roleBindings, roleBinding)
|
||||
}
|
||||
|
||||
if createArgs.export {
|
||||
for i := range tenantArgs.namespaces {
|
||||
if err := exportTenant(namespaces[i], accounts[i], roleBindings[i]); err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
for i := range tenantArgs.namespaces {
|
||||
logger.Actionf("applying namespace %s", namespaces[i].Name)
|
||||
if err := upsertNamespace(ctx, kubeClient, namespaces[i]); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying service account %s", accounts[i].Name)
|
||||
if err := upsertServiceAccount(ctx, kubeClient, accounts[i]); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
logger.Actionf("applying role binding %s", roleBindings[i].Name)
|
||||
if err := upsertRoleBinding(ctx, kubeClient, roleBindings[i]); err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
|
||||
logger.Successf("tenant setup completed")
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertNamespace(ctx context.Context, kubeClient client.Client, namespace corev1.Namespace) error {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: namespace.GetNamespace(),
|
||||
Name: namespace.GetName(),
|
||||
}
|
||||
|
||||
var existing corev1.Namespace
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, &namespace); err != nil {
|
||||
return err
|
||||
} else {
|
||||
return nil
|
||||
}
|
||||
}
|
||||
return err
|
||||
}
|
||||
|
||||
if !equality.Semantic.DeepDerivative(namespace.Labels, existing.Labels) {
|
||||
existing.Labels = namespace.Labels
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertServiceAccount(ctx context.Context, kubeClient client.Client, account corev1.ServiceAccount) error {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: account.GetNamespace(),
|
||||
Name: account.GetName(),
|
||||
}
|
||||
|
||||
var existing corev1.ServiceAccount
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, &account); err != nil {
|
||||
return err
|
||||
} else {
|
||||
return nil
|
||||
}
|
||||
}
|
||||
return err
|
||||
}
|
||||
|
||||
if !equality.Semantic.DeepDerivative(account.Labels, existing.Labels) {
|
||||
existing.Labels = account.Labels
|
||||
if err := kubeClient.Update(ctx, &existing); err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func upsertRoleBinding(ctx context.Context, kubeClient client.Client, roleBinding rbacv1.RoleBinding) error {
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: roleBinding.GetNamespace(),
|
||||
Name: roleBinding.GetName(),
|
||||
}
|
||||
|
||||
var existing rbacv1.RoleBinding
|
||||
err := kubeClient.Get(ctx, namespacedName, &existing)
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if err := kubeClient.Create(ctx, &roleBinding); err != nil {
|
||||
return err
|
||||
} else {
|
||||
return nil
|
||||
}
|
||||
}
|
||||
return err
|
||||
}
|
||||
|
||||
if !equality.Semantic.DeepDerivative(roleBinding.Subjects, existing.Subjects) ||
|
||||
!equality.Semantic.DeepDerivative(roleBinding.RoleRef, existing.RoleRef) ||
|
||||
!equality.Semantic.DeepDerivative(roleBinding.Labels, existing.Labels) {
|
||||
if err := kubeClient.Delete(ctx, &existing); err != nil {
|
||||
return err
|
||||
}
|
||||
if err := kubeClient.Create(ctx, &roleBinding); err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func exportTenant(namespace corev1.Namespace, account corev1.ServiceAccount, roleBinding rbacv1.RoleBinding) error {
|
||||
namespace.TypeMeta = metav1.TypeMeta{
|
||||
APIVersion: "v1",
|
||||
Kind: "Namespace",
|
||||
}
|
||||
data, err := yaml.Marshal(namespace)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
fmt.Println("---")
|
||||
data = bytes.Replace(data, []byte("spec: {}\n"), []byte(""), 1)
|
||||
fmt.Println(resourceToString(data))
|
||||
|
||||
account.TypeMeta = metav1.TypeMeta{
|
||||
APIVersion: "v1",
|
||||
Kind: "ServiceAccount",
|
||||
}
|
||||
data, err = yaml.Marshal(account)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
fmt.Println("---")
|
||||
data = bytes.Replace(data, []byte("spec: {}\n"), []byte(""), 1)
|
||||
fmt.Println(resourceToString(data))
|
||||
|
||||
roleBinding.TypeMeta = metav1.TypeMeta{
|
||||
APIVersion: "rbac.authorization.k8s.io/v1",
|
||||
Kind: "RoleBinding",
|
||||
}
|
||||
data, err = yaml.Marshal(roleBinding)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
fmt.Println("---")
|
||||
fmt.Println(resourceToString(data))
|
||||
|
||||
return nil
|
||||
}
|
||||
55
cmd/flux/create_test.go
Normal file
55
cmd/flux/create_test.go
Normal file
@@ -0,0 +1,55 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"testing"
|
||||
|
||||
"k8s.io/apimachinery/pkg/util/rand"
|
||||
)
|
||||
|
||||
func Test_validateObjectName(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
valid bool
|
||||
}{
|
||||
{
|
||||
name: "flux-system",
|
||||
valid: true,
|
||||
},
|
||||
{
|
||||
name: "-flux-system",
|
||||
valid: false,
|
||||
},
|
||||
{
|
||||
name: "-flux-system-",
|
||||
valid: false,
|
||||
},
|
||||
{
|
||||
name: "third.first",
|
||||
valid: false,
|
||||
},
|
||||
{
|
||||
name: "THirdfirst",
|
||||
valid: false,
|
||||
},
|
||||
{
|
||||
name: "THirdfirst",
|
||||
valid: false,
|
||||
},
|
||||
{
|
||||
name: rand.String(63),
|
||||
valid: true,
|
||||
},
|
||||
{
|
||||
name: rand.String(64),
|
||||
valid: false,
|
||||
},
|
||||
}
|
||||
|
||||
for _, tt := range tests {
|
||||
valid := validateObjectName(tt.name)
|
||||
if valid != tt.valid {
|
||||
t.Errorf("expected name %q to return %t for validateObjectName func but got %t",
|
||||
tt.name, tt.valid, valid)
|
||||
}
|
||||
}
|
||||
}
|
||||
96
cmd/flux/delete.go
Normal file
96
cmd/flux/delete.go
Normal file
@@ -0,0 +1,96 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
|
||||
"github.com/manifoldco/promptui"
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
|
||||
"github.com/fluxcd/flux2/v2/internal/utils"
|
||||
)
|
||||
|
||||
var deleteCmd = &cobra.Command{
|
||||
Use: "delete",
|
||||
Short: "Delete sources and resources",
|
||||
Long: `The delete sub-commands delete sources and resources.`,
|
||||
}
|
||||
|
||||
type deleteFlags struct {
|
||||
silent bool
|
||||
}
|
||||
|
||||
var deleteArgs deleteFlags
|
||||
|
||||
func init() {
|
||||
deleteCmd.PersistentFlags().BoolVarP(&deleteArgs.silent, "silent", "s", false,
|
||||
"delete resource without asking for confirmation")
|
||||
|
||||
rootCmd.AddCommand(deleteCmd)
|
||||
}
|
||||
|
||||
type deleteCommand struct {
|
||||
apiType
|
||||
object adapter // for getting the value, and later deleting it
|
||||
}
|
||||
|
||||
func (del deleteCommand) run(cmd *cobra.Command, args []string) error {
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("%s name is required", del.humanKind)
|
||||
}
|
||||
name := args[0]
|
||||
|
||||
ctx, cancel := context.WithTimeout(context.Background(), rootArgs.timeout)
|
||||
defer cancel()
|
||||
|
||||
kubeClient, err := utils.KubeClient(kubeconfigArgs, kubeclientOptions)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
namespacedName := types.NamespacedName{
|
||||
Namespace: *kubeconfigArgs.Namespace,
|
||||
Name: name,
|
||||
}
|
||||
|
||||
err = kubeClient.Get(ctx, namespacedName, del.object.asClientObject())
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
if !deleteArgs.silent {
|
||||
prompt := promptui.Prompt{
|
||||
Label: "Are you sure you want to delete this " + del.humanKind,
|
||||
IsConfirm: true,
|
||||
}
|
||||
if _, err := prompt.Run(); err != nil {
|
||||
return fmt.Errorf("aborting")
|
||||
}
|
||||
}
|
||||
|
||||
logger.Actionf("deleting %s %s in %s namespace", del.humanKind, name, *kubeconfigArgs.Namespace)
|
||||
err = kubeClient.Delete(ctx, del.object.asClientObject())
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
logger.Successf("%s deleted", del.humanKind)
|
||||
|
||||
return nil
|
||||
}
|
||||
40
cmd/flux/delete_alert.go
Normal file
40
cmd/flux/delete_alert.go
Normal file
@@ -0,0 +1,40 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
var deleteAlertCmd = &cobra.Command{
|
||||
Use: "alert [name]",
|
||||
Short: "Delete a Alert resource",
|
||||
Long: withPreviewNote("The delete alert command removes the given Alert from the cluster."),
|
||||
Example: ` # Delete an Alert and the Kubernetes resources created by it
|
||||
flux delete alert main`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(notificationv1.GroupVersion.WithKind(notificationv1.AlertKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: alertType,
|
||||
object: universalAdapter{¬ificationv1.Alert{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteCmd.AddCommand(deleteAlertCmd)
|
||||
}
|
||||
40
cmd/flux/delete_alertprovider.go
Normal file
40
cmd/flux/delete_alertprovider.go
Normal file
@@ -0,0 +1,40 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
notificationv1 "github.com/fluxcd/notification-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
var deleteAlertProviderCmd = &cobra.Command{
|
||||
Use: "alert-provider [name]",
|
||||
Short: "Delete a Provider resource",
|
||||
Long: withPreviewNote("The delete alert-provider command removes the given Provider from the cluster."),
|
||||
Example: ` # Delete a Provider and the Kubernetes resources created by it
|
||||
flux delete alert-provider slack`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(notificationv1.GroupVersion.WithKind(notificationv1.ProviderKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: alertProviderType,
|
||||
object: universalAdapter{¬ificationv1.Provider{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteCmd.AddCommand(deleteAlertProviderCmd)
|
||||
}
|
||||
41
cmd/flux/delete_helmrelease.go
Normal file
41
cmd/flux/delete_helmrelease.go
Normal file
@@ -0,0 +1,41 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
helmv2 "github.com/fluxcd/helm-controller/api/v2beta1"
|
||||
)
|
||||
|
||||
var deleteHelmReleaseCmd = &cobra.Command{
|
||||
Use: "helmrelease [name]",
|
||||
Aliases: []string{"hr"},
|
||||
Short: "Delete a HelmRelease resource",
|
||||
Long: withPreviewNote("The delete helmrelease command removes the given HelmRelease from the cluster."),
|
||||
Example: ` # Delete a Helm release and the Kubernetes resources created by it
|
||||
flux delete hr podinfo`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(helmv2.GroupVersion.WithKind(helmv2.HelmReleaseKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: helmReleaseType,
|
||||
object: universalAdapter{&helmv2.HelmRelease{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteCmd.AddCommand(deleteHelmReleaseCmd)
|
||||
}
|
||||
31
cmd/flux/delete_image.go
Normal file
31
cmd/flux/delete_image.go
Normal file
@@ -0,0 +1,31 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
|
||||
var deleteImageCmd = &cobra.Command{
|
||||
Use: "image",
|
||||
Short: "Delete image automation objects",
|
||||
Long: `The delete image sub-commands delete image automation objects.`,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteCmd.AddCommand(deleteImageCmd)
|
||||
}
|
||||
40
cmd/flux/delete_image_policy.go
Normal file
40
cmd/flux/delete_image_policy.go
Normal file
@@ -0,0 +1,40 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
imagev1 "github.com/fluxcd/image-reflector-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
var deleteImagePolicyCmd = &cobra.Command{
|
||||
Use: "policy [name]",
|
||||
Short: "Delete an ImagePolicy object",
|
||||
Long: withPreviewNote(`The delete image policy command deletes the given ImagePolicy from the cluster.`),
|
||||
Example: ` # Delete an image policy
|
||||
flux delete image policy alpine3.x`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(imagev1.GroupVersion.WithKind(imagev1.ImagePolicyKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: imagePolicyType,
|
||||
object: universalAdapter{&imagev1.ImagePolicy{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteImageCmd.AddCommand(deleteImagePolicyCmd)
|
||||
}
|
||||
40
cmd/flux/delete_image_repository.go
Normal file
40
cmd/flux/delete_image_repository.go
Normal file
@@ -0,0 +1,40 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
imagev1 "github.com/fluxcd/image-reflector-controller/api/v1beta2"
|
||||
)
|
||||
|
||||
var deleteImageRepositoryCmd = &cobra.Command{
|
||||
Use: "repository [name]",
|
||||
Short: "Delete an ImageRepository object",
|
||||
Long: withPreviewNote("The delete image repository command deletes the given ImageRepository from the cluster."),
|
||||
Example: ` # Delete an image repository
|
||||
flux delete image repository alpine`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(imagev1.GroupVersion.WithKind(imagev1.ImageRepositoryKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: imageRepositoryType,
|
||||
object: universalAdapter{&imagev1.ImageRepository{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteImageCmd.AddCommand(deleteImageRepositoryCmd)
|
||||
}
|
||||
40
cmd/flux/delete_image_update.go
Normal file
40
cmd/flux/delete_image_update.go
Normal file
@@ -0,0 +1,40 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
autov1 "github.com/fluxcd/image-automation-controller/api/v1beta1"
|
||||
)
|
||||
|
||||
var deleteImageUpdateCmd = &cobra.Command{
|
||||
Use: "update [name]",
|
||||
Short: "Delete an ImageUpdateAutomation object",
|
||||
Long: withPreviewNote(`The delete image update command deletes the given ImageUpdateAutomation from the cluster.`),
|
||||
Example: ` # Delete an image update automation
|
||||
flux delete image update latest-images`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(autov1.GroupVersion.WithKind(autov1.ImageUpdateAutomationKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: imageUpdateAutomationType,
|
||||
object: universalAdapter{&autov1.ImageUpdateAutomation{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteImageCmd.AddCommand(deleteImageUpdateCmd)
|
||||
}
|
||||
41
cmd/flux/delete_kustomization.go
Normal file
41
cmd/flux/delete_kustomization.go
Normal file
@@ -0,0 +1,41 @@
|
||||
/*
|
||||
Copyright 2020 The Flux authors
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
*/
|
||||
|
||||
package main
|
||||
|
||||
import (
|
||||
"github.com/spf13/cobra"
|
||||
|
||||
kustomizev1 "github.com/fluxcd/kustomize-controller/api/v1"
|
||||
)
|
||||
|
||||
var deleteKsCmd = &cobra.Command{
|
||||
Use: "kustomization [name]",
|
||||
Aliases: []string{"ks"},
|
||||
Short: "Delete a Kustomization resource",
|
||||
Long: `The delete kustomization command deletes the given Kustomization from the cluster.`,
|
||||
Example: ` # Delete a kustomization and the Kubernetes resources created by it when prune is enabled
|
||||
flux delete kustomization podinfo`,
|
||||
ValidArgsFunction: resourceNamesCompletionFunc(kustomizev1.GroupVersion.WithKind(kustomizev1.KustomizationKind)),
|
||||
RunE: deleteCommand{
|
||||
apiType: kustomizationType,
|
||||
object: universalAdapter{&kustomizev1.Kustomization{}},
|
||||
}.run,
|
||||
}
|
||||
|
||||
func init() {
|
||||
deleteCmd.AddCommand(deleteKsCmd)
|
||||
}
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user